Sn1per Community Edition is an automated scanner that can be used during a penetration test to enumerate and scan for vulnerabilities. Sn1per Professional is Xero Security's premium reporting addon for Professional Penetration Testers, Bug Bounty Researchers and Corporate Security teams to manage large environments and pentest scopes.
Professional reporting interface
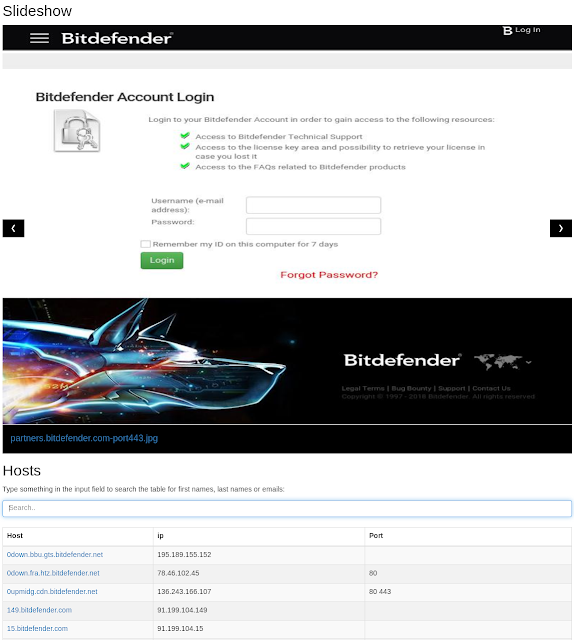
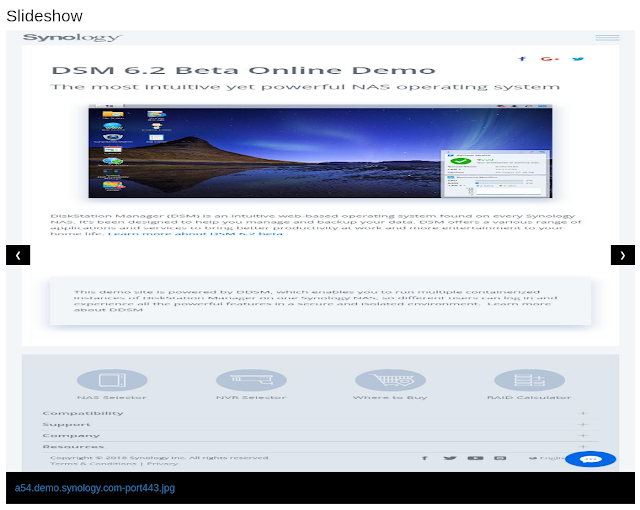
Slideshow for all gathered screenshots
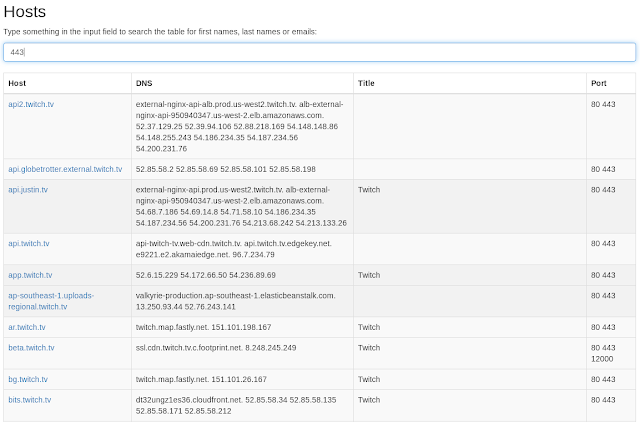
Searchable and sortable DNS, IP and open port database
Categorized host reports
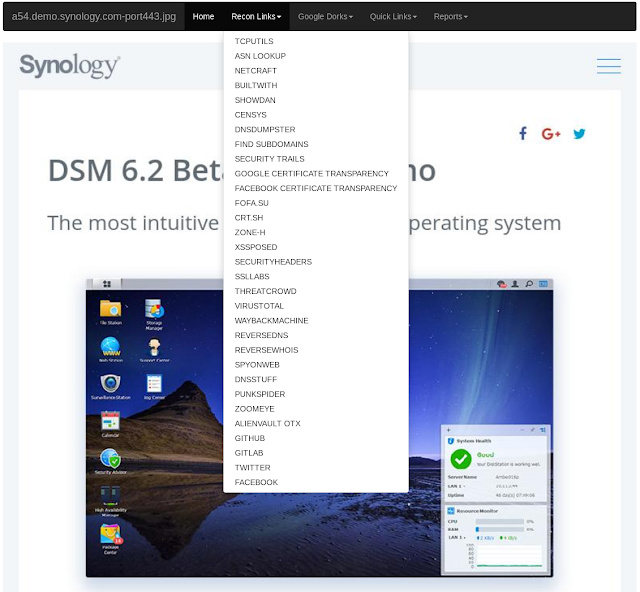
Quick links to online recon tools and Google hacking queries
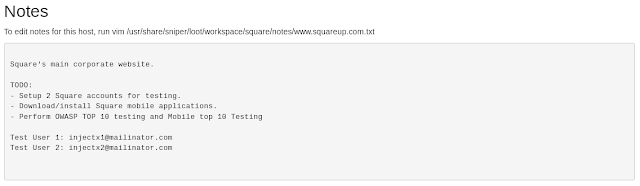
Personalized notes field for each host
SN1PER COMMUNITY FEATURES:
- Automatically collects basic recon (ie. whois, ping, DNS, etc.)
- Automatically launches Google hacking queries against a target domain
- Automatically enumerates open ports via NMap port scanning
- Automatically brute forces sub-domains, gathers DNS info and checks for zone transfers
- Automatically checks for sub-domain hijacking
- Automatically runs targeted NMap scripts against open ports
- Automatically runs targeted Metasploit scan and exploit modules
- Automatically scans all web applications for common vulnerabilities
- Automatically brute forces ALL open services
- Automatically test for anonymous FTP access
- Automatically runs WPScan, Arachni and Nikto for all web services
- Automatically enumerates NFS shares
- Automatically test for anonymous LDAP access
- Automatically enumerate SSL/TLS ciphers, protocols and vulnerabilities
- Automatically enumerate SNMP community strings, services and users
- Automatically list SMB users and shares, check for NULL sessions and exploit MS08-067
- Automatically exploit vulnerable JBoss, Java RMI and Tomcat servers
- Automatically tests for open X11 servers
- Auto-pwn added for Metasploitable, ShellShock, MS08-067, Default Tomcat Creds
- Performs high level enumeration of multiple hosts and subnets
- Automatically integrates with Metasploit Pro, MSFConsole and Zenmap for reporting
- Automatically gathers screenshots of all web sites
- Create individual workspaces to store all scan output
AUTO-PWN:
- Drupal Drupalgedon2 RCE CVE-2018-7600
- GPON Router RCE CVE-2018-10561
- Apache Struts 2 RCE CVE-2017-5638
- Apache Struts 2 RCE CVE-2017-9805
- Apache Jakarta RCE CVE-2017-5638
- Shellshock GNU Bash RCE CVE-2014-6271
- HeartBleed OpenSSL Detection CVE-2014-0160
- Default Apache Tomcat Creds CVE-2009-3843
- MS Windows SMB RCE MS08-067
- Webmin File Disclosure CVE-2006-3392
- Anonymous FTP Access
- PHPMyAdmin Backdoor RCE
- PHPMyAdmin Auth Bypass
- JBoss Java De-Serialization RCE's
KALI LINUX INSTALL:
./install.shDOCKER INSTALL:
Credits: @menzow
Docker Install: https://github.com/menzow/sn1per-docker
Docker Build: https://hub.docker.com/r/menzo/sn1per-docker/builds/bqez3h7hwfun4odgd2axvn4/
Example usage:
$ docker pull menzo/sn1per-docker
$ docker run --rm -ti menzo/sn1per-docker sniper menzo.ioUSAGE:
[*] NORMAL MODE
sniper -t|--target <TARGET>
[*] NORMAL MODE + OSINT + RECON
sniper -t|--target <TARGET> -o|--osint -re|--recon
[*] STEALTH MODE + OSINT + RECON
sniper -t|--target <TARGET> -m|--mode stealth -o|--osint -re|--recon
[*] DISCOVER MODE
sniper -t|--target <CIDR> -m|--mode discover -w|--workspace <WORSPACE_ALIAS>
[*] SCAN ONLY SPECIFIC PORT
sniper -t|--target <TARGET> -m port -p|--port <portnum>
[*] FULLPORTONLY SCAN MODE
sniper -t|--target <TARGET> -fp|--fullportonly
[*] PORT SCAN MODE
sniper -t|--target <TARGET> -m|--mode port -p|--port <PORT_NUM>
[*] WEB MODE - PORT 80 + 443 ONLY!
sniper -t|--target <TARGET> -m|--mode web
[*] HTTP WEB PORT MODE
sniper -t|--target <TARGET> -m|--mode webporthttp -p|--port <port>
[*] HTTPS WEB PORT MODE
sniper -t|--target <TARGET> -m|--mode webporthttps -p|--port <port>
[*] ENABLE BRUTEFORCE
sniper -t|--target <TARGET> -b|--bruteforce
[*] AIRSTRIKE MODE
sniper -f|--file /full/path/to/targets.txt -m|--mode airstrike
[*] NUKE MODE WITH TARGET LIST, BRUTEFORCE ENABLED, FULLPORTSCAN ENABLED, OSINT ENABLED, RECON ENABLED, WORKSPACE & LOOT ENABLED
sniper -f--file /full/path/to/targets.txt -m|--mode nuke -w|--workspace <WORKSPACE_ALIAS>
[*] ENABLE LOOT IMPORTING INTO METASPLOIT
sniper -t|--target <TARGET>
[*] LOOT REIMPORT FUNCTION
sniper -w <WORKSPACE_ALIAS> --reimport
[*] UPDATE SNIPER
sniper -u|--updateMODES:
- NORMAL: Performs basic scan of targets and open ports using both active and passive checks for optimal performance.
- STEALTH: Quickly enumerate single targets using mostly non-intrusive scans to avoid WAF/IPS blocking.
- AIRSTRIKE: Quickly enumerates open ports/services on multiple hosts and performs basic fingerprinting. To use, specify the full location of the file which contains all hosts, IPs that need to be scanned and run ./sn1per /full/path/to/targets.txt airstrike to begin scanning.
- NUKE: Launch full audit of multiple hosts specified in text file of choice. Usage example: ./sniper /pentest/loot/targets.txt nuke.
- DISCOVER: Parses all hosts on a subnet/CIDR (ie. 192.168.0.0/16) and initiates a sniper scan against each host. Useful for internal network scans.
- PORT: Scans a specific port for vulnerabilities. Reporting is not currently available in this mode.
- FULLPORTONLY: Performs a full detailed port scan and saves results to XML.
- WEB: Adds full automatic web application scans to the results (port 80/tcp & 443/tcp only). Ideal for web applications but may increase scan time significantly.
- WEBPORTHTTP: Launches a full HTTP web application scan against a specific host and port.
- WEBPORTHTTPS: Launches a full HTTPS web application scan against a specific host and port.
- UPDATE: Checks for updates and upgrades all components used by sniper.
- REIMPORT: Reimport all workspace files into Metasploit and reproduce all reports.
- RELOAD: Reload the master workspace report.
SAMPLE REPORT:
https://gist.github.com/1N3/8214ec2da2c91691bcbc