
2021-07-22 03:10:40 Author: www.nowsecure.com(查看原文) 阅读量:139 收藏
Android 12 is currently in beta with an expected release date of September. While Google is working to stabilize the newest version of the Android mobile operating system, mobile app developers can begin strategizing new feature implementations. Just as we previously examined Android 11 security and privacy features, this article covers Android 12 changes to security and privacy and how they will impact mobile app developers.
According to Google’s feature change list, there are nearly 20 notable changes or new features to security and privacy for Android 12. Some Android 12 updates below will address whether they affect apps specifically targeting Android 12, all apps running on Android 12, or are brand new features entirely. All in all, while we can’t discuss every line of code that changed (although that would be fun), we attempt to address the majority of changes with a quick summary of the impact.
Updates to Apps Targeting Android 12 and Higher
- Motion sensors are rate-limited: To protect users and their precise location and device data, the rate of sensor data refresh on the device will be throttled and limited. Developers will need to declare permission to gain a higher rate of data refresh through
HIGH_SAMPLING_RATE_SENSORSconsent.
- Modern SameSite cookies in WebView: SameSite is an attribute of the Set-Cookie HTTP response header. It can hold three different values: Lax, Strict, and None. With Android updates, any WebView that does not specify the SameSite attribute will default to Lax. Therefore, third-party site sub-requests will not obtain cookies. Only the origin site the user is navigating to will receive them. This feature will help against unintended cross-site sharing.
- ADB backup restriction: App data will now be excluded from any other system data when the command, adb backup, is performed. This command’s new default behavior helps mitigate issues related to app data privacy.
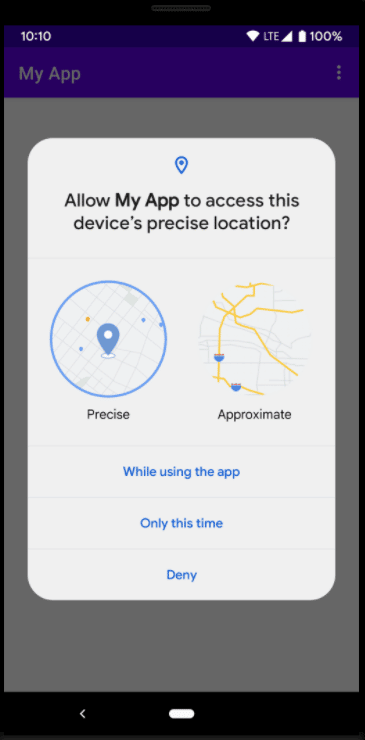
- Approximate location: Developers must be aware that users now have the option in Android 12 to allow an app only to obtain an approximate location of their device, regardless of whether the developer requests
ACCESS_FINE_LOCATIONruntime permission.
- App hibernation: In a solid win for security and privacy, app hibernation is in full effect now and builds upon Android 11. Android 12 will place apps in a hibernation state if users do not interact with them for a few months. User-granted permissions will be auto-reset for safety.
- Data access auditing: This update is a welcome, nice-to-have feature for developers that allow for easier auditing of data access in a codebase. Developers can create attribution tags in their manifest file, pointing to specific parts of their app that require data access, such as photos, for example.
<manifest ...>
<!-- The value of "android:tag" must be a literal string, and the
value of "android:label" must be a resource. The value of
"android:label" should be user-readable. -->
<attribution android:tag="sharePhotos"
android:label="@string/share_photos_attribution_label" />
...
</manifest>
- Safer component exporting: Developers targeting Android 12 must declare the android:exported attribute if any activities, services, or broadcast receivers use intent filters.
- Pending intents mutability: Pending intents, essentially actions that other applications can perform later on behalf of another app, will need to be declared as mutable or immutable using PendingIntent.FLAG_MUTABLE or
PendingIntent.FLAG_IMMUTABLE.
- Unsafe intent launches: To provide better platform security and app security development for Android, version 12 will offer a debugging feature that warns developers if their app performs an unsafe launch of an intent.
- Notification trampoline restrictions: Most mobile users are familiar with tapping on a notification or a button within a notification, and launching to an app or resulting page, hence the name notification trampoline. With the next Android OS, developers cannot call startActivity() from service or broadcast receivers. Google is veering away from 3rd party or intermediate sources to launch the activity and instead focusing on the developer to activate it. You will now see the following in Logcat if a notification trampoline results from your app starting an activity from a service or broadcast receiver:
“Indirect notification activity start (trampoline) from PACKAGE_NAME, \
this should be avoided for performance reasons.”
Updates to All Apps Running Android 12
- Untrusted touch events are blocked: Developers and users alike will feel more at ease knowing that if an overlay obscures the view of an app to the user in some fashion, Android 12 will prohibit any receiving touch events to said app. The only exceptions to this will be accessibility windows or if the overlay window is within the app itself that presented it.
- Apps can’t close system dialogs: Google is giving the user more control in this update. Apps will not be able to close temporary system dialogs moving forward. The user will need to perform this action.
- Permission package visibility: A list of installed apps on an Android device is considered personal and sensitive user data. Therefore, when an app queries for information about other apps on the device, the OS will filter information by default and offer a limited visibility scope.
- Bouncy Castle implementation removed: This update includes removing many deprecated BouncyCastle cryptographic algorithm operations in favor of Conscrypt implementations. This removal also includes deprecated AES algorithms.
- Clipboard access notifications: A toast message will notify users if they are using an app that attempts to access ClipData from a different app, which is done through an app calling the method, getPrimaryClip().
- Microphone and camera toggles: A significant update to privacy for users pertains to microphone audio and camera video feed. In Android’s Quick Settings, a user can enable or disable camera and microphone access with a click of a button. This setting is global and will impact all apps on the device.
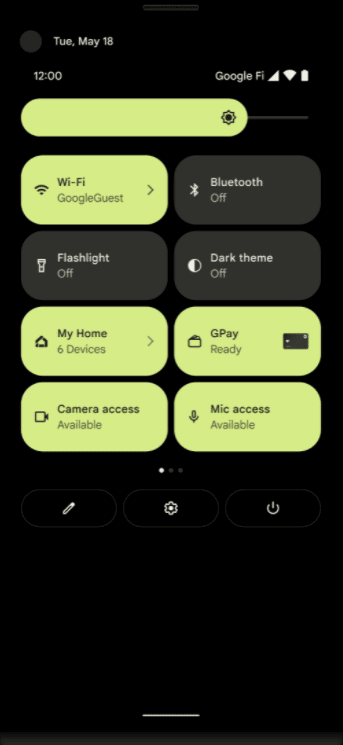
- Microphone and camera indicators: Adding on top of the feature mentioned above related to toggling the microphone and camera, the user will now see an icon in the status bar when an app accesses the microphone or camera on devices running Android 12.
New Android 12 Features
- Hide application overlay windows: Certainly a positive step in the right direction, Android 12 gives developers the ability to hide overlay windows when a user is interacting with their app.
- Device properties attestation: If developers want to verify device properties in attestation certificates, any app targeting Android 12 can use the method, setDevicePropertiesAttestationIncluded().
- App digest API: Brand new API that will allow querying of an app’s checksum straight from the platform. This API helps when you want to verify the integrity of app packages installed.
- Secure lockscreen notification actions: Developers will gain an additional flag,
setAuthenticationRequired, toNotification.Action.Builder. This flag, when set to true, will force an authentication request on a locked device.
Notification n1 = new Notification.Builder(context, NotificationListenerVerifierActivity.TAG)
...
.addAction(new Notification.Action.Builder(R.drawable.ic_stat_charlie,
context.getString(R.string.action_test_title), makeBroadcastIntent(context))
// Make sure this notification action will always request authentication when
// invoked from a lock screen
.setAuthenticationRequired(true).build())
.build();
- Known signers permission protection flag: A new attribute, knownCerts, is introduced for signature-level permissions, allowing a developer to refer to an array resource containing the digests of known signing certificates when using the knownSigner protection flag. This feature will create efficiency for the system in granting permission to a requesting app if any signer in the app’s signing lineage matches one declared in this new attribute.
- Bluetooth permissions: Significant Bluetooth permissions are coming our way to Android 12, introducing
BLUETOOTH_SCAN, BLUETOOTH_ADVERTISE, andBLUETOOTH_CONNECT. These help developers locate and maintain Bluetooth connections without needing the device’s location, essentially decoupling privacy issues from Bluetooth for good.
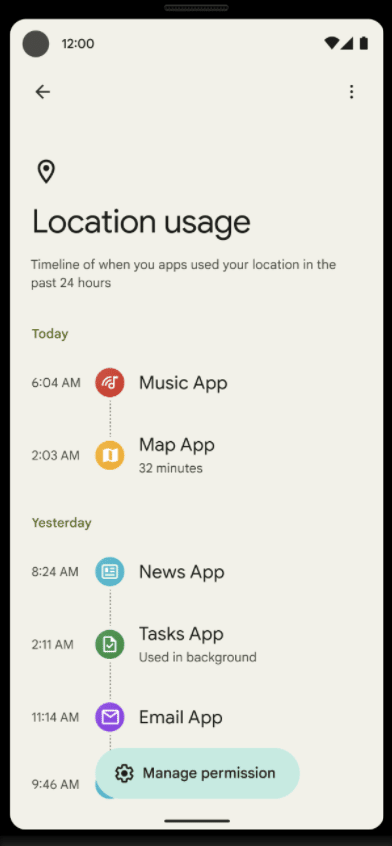
- Privacy Dashboard: Easily one of the most visual updates for users regarding privacy is the new privacy dashboard. This dashboard will appear in system settings on devices running Android 12. Any app accessing location, microphone, or camera information will be on full blast to the user. The dashboard will display the apps in a timeline fashion to see when the actions occurred.
- Permission group lookup: This is a straight-forward update in allowing developers to query the system to detect how platform-provided permissions are organized into groups. Permissions on Android are something to never be assumed as these help support user privacy by protecting access to restricted data and access.
In Summary
This year is driving forward the focus on security and privacy in the mobile app space in a big way. Google and Apple are emphasizing secure development practices to make devices and apps safer. Likewise, NowSecure stays up to date with mobile operating system changes and offers training to help mobile app developers embrace a secure by design philosophy to create secure mobile apps.
How to Deliver an Innovative, Secure Mobile App
如有侵权请联系:admin#unsafe.sh