Countless, easily-configurable malware families give rise, unfortunately 2020-10-19 23:35:41 Author: www.vmray.com(查看原文) 阅读量:296 收藏
Countless, easily-configurable malware families give rise, unfortunately, to countless malware samples. Fortunately for researchers, these different samples share functionality and the family can be discerned by looking for similarities, patterns, and heuristics contained within the code. It’s easy to figure out the child when you know what the parent looks like.
There are many ways to achieve obfuscation but the simplest form is to use already existing packers, which are also offered as malware products. To better sell their products, threat actors enrich them with additional features including sandbox evasion, or much simpler features like persistence.
In this Malware Analysis Spotlight, we highlight the execution of a packed Ave_Maria sample. Ave_Maria is an advanced information stealer whose first documented appearance occurred near the end of 2018. This packed sample version of Ave_Maria was first seen this month according to VirusTotal. It is typically distributed via malicious email campaigns and is capable of credential theft and bypassing User Access Control (UAC).
In this sample, the packer is written in .Net and unpacks Ave_Maria and a UAC bypass. Both parts, packer and Ave_Maria, gains persistence as we see in the following.
Analysis of the Execution Chain
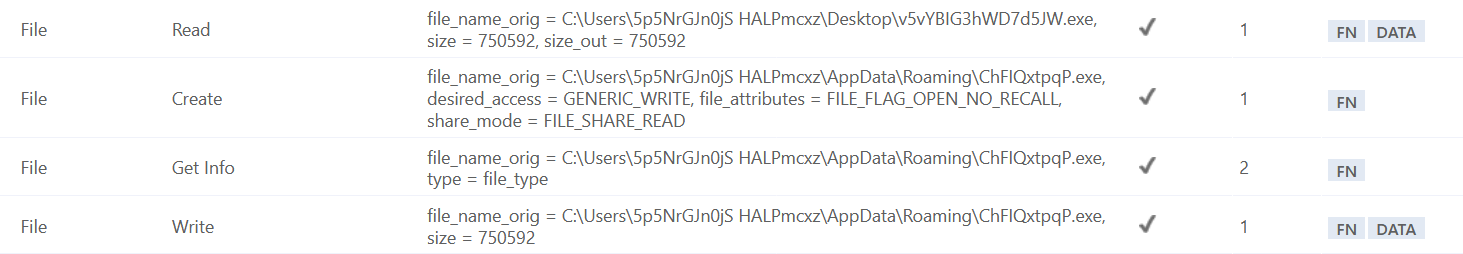
The execution starts with a .NET binary (packer) that carries the actual payload inside its resources. In the beginning, it makes sure to copy itself to a less obvious location the %APPDATA% directory.
The loader creates a This is one of the two methods used for persistence observed during the infection process.
It then creates a new process of itself in a suspended state. The encoded payload is a string that is read into an array, reversed and base64 decoded. The actual Ave_Maria stealer is then unpacked into the newly created process. To be more specific two executables are injected. The first one, the stealer payload, is injected at address 0x400000. Following that, the UAC bypass, which is further described by Morphisec, is injected at the address 0x54e000 (Figure 4).
After the loader is finished unpacking, the execution is passed to the injected stealer payload by resuming its thread.
VMRay Analyzer is monitoring all injection attempts and provides the possibility to access the injected data. In this case, it’s already the unpacked payload that is being injected which saves time during analysis.
In addition to the achieved persistence with schtasks.exe, a well-known startup registry key HKCU\Software\Microsoft\Windows\CurrentVersion\Run (Figure 5).
authors try to target security researchers by directly referencing their names in the binary. This is also the case with Ave_Maria which directly references a well-known researcher in the security community (Figure 6). However, we can use this to our advantage. It’s a good indicator to detect further malicious samples.
After the above-mentioned execution chain, Ave_Maria starts its main purpose: the stealing of credentials targeting multiple applications (Figure 7).
Conclusion
As one can see from the above analysis, Ave_Maria can be a challenge to de-obfuscate but the use of VMRay Analyzer eases the pursuit and increases understanding of the sample’s execution chain. Analyzer allows users to extract important runtime information faster without dealing with multiple obfuscation layers or debugging the sample manually.
IOCs
如有侵权请联系:admin#unsafe.sh






