Pwn2Own Berlin 2026, Day Two: $385,750 more, Microsoft Exchange falls, and the runnin 2026-5-15 21:53:56 Author: securityaffairs.com(查看原文) 阅读量:12 收藏
Pwn2Own Berlin 2026, Day Two: $385,750 more, Microsoft Exchange falls, and the running total crosses $900K

Day two of Pwn2Own Berlin 2026 saw $385,750 earned for 15 zero-days, bringing the total to $908,750 and 39 vulnerabilities over two days.
During the second day of Pwn2Own Berlin 2026, security researchers earned $385,750 after successfully demonstrating 15 unique zero-day vulnerabilities affecting products such as Windows 11, Microsoft Exchange, and Red Hat Enterprise Linux for Workstations. Combined with the first day of the competition, total rewards have reached $908,750 for 39 unique vulnerabilities discovered across two days, with another day of hacking still remaining.
Going into day two, DEVCORE held a commanding lead built almost entirely on Orange Tsai’s four-logic-bug Edge sandbox escape from the previous day.
Microsoft Exchange and Windows 11 were successfully exploited during the second day of Pwn2Own Berlin 2026. Researcher Siyeon Wi demonstrated a Windows 11 privilege escalation flaw caused by an integer overflow bug, earning $7,500. Multiple successful attacks against fully patched Windows 11 systems across two days highlighted the presence of serious real-world vulnerabilities in widely used software.
Ben Koo of Team DDOS had a clean win on Red Hat Enterprise Linux for Workstations, leveraging a use-after-free bug to escalate privileges and earning $10,000.
AI-focused attacks continued during Pwn2Own Berlin 2026 as researcher Byung Young Yi targeted LiteLLM. His exploit matched a vulnerability already demonstrated earlier in the competition, resulting in a collision rather than a new zero-day. He still earned $17,750 and partial Master of Pwn points, highlighting the intense scrutiny researchers placed on LiteLLM throughout the event.
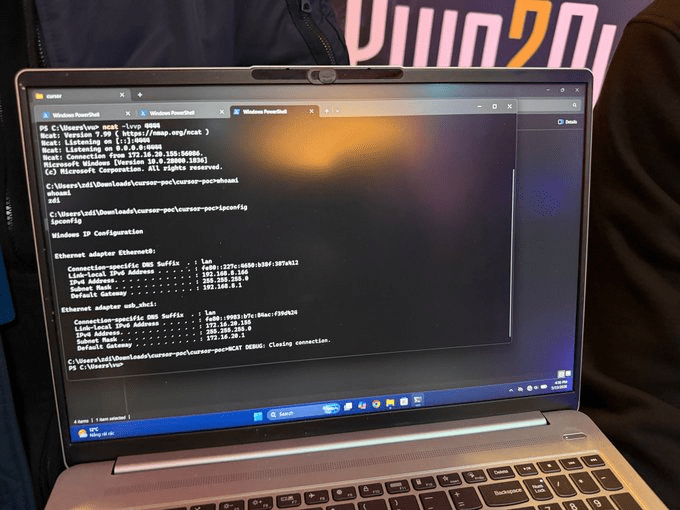
Le Duc Anh Vu of Viettel Cyber Security successfully exploited Cursor, earning $30,000 and 3 Master of Pwn points in a full Pwn2Own win.
Compass Security successfully exploited the AI-powered code editor Cursor during Pwn2Own Berlin 2026, earning $15,000. The attack, alongside earlier exploits targeting OpenAI Codex, highlights growing security risks across AI-assisted developer tools and infrastructure.
Some exploits failed at Pwn2Own Berlin 2026, including Safari and SharePoint attempts that did not work within the time limit. Researchers still showed strong effort, but live conditions and strict timing made reliable exploitation difficult even for well-prepared teams targeting fully patched systems.
DEVCORE leads Pwn2Own Berlin 2026 with 40.5 points and $405,000, but the competition is still open with one day remaining and high-value targets like Firefox and AI systems still ahead. A single successful exploit could change the rankings.
Across two days, researchers demonstrated 39 unique zero-days across widely used software, including operating systems, AI tools, and enterprise platforms, all running fully patched versions. The results highlight how skilled attackers can still find weaknesses even in mature systems. Vendors now have 90 days to patch the vulnerabilities disclosed during the event, turning live exploitation into coordinated disclosure instead of real-world attacks.
Pwn2Own Berlin 2026 day one saw 22 entries and 24 zero-days across major software, with researchers earning $523,000 in total rewards.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Pwn2Own Berlin 2026)
如有侵权请联系:admin#unsafe.sh