Palo Alto Networks PAN-OS Remote Code Execution | Critical Remote Access RiskA critical b 2026-5-15 17:12:21 Author: horizon3.ai(查看原文) 阅读量:7 收藏
Palo Alto Networks PAN-OS Remote Code Execution | Critical Remote Access Risk
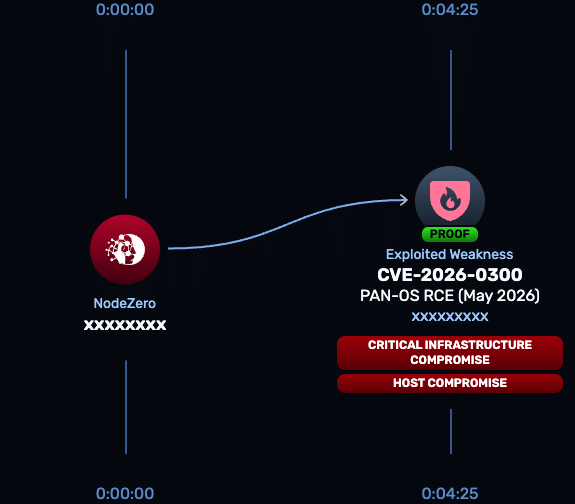
A critical buffer overflow vulnerability has been identified in Palo Alto Networks PAN-OS in the User-ID captive portal functionality that could lead to remote code execution. Tracked as CVE-2026-0300 and rated CVSS 9.3, the flaw stems from improper bounds handling that results in an out-of-bounds write when the service processes specially crafted network packets, potentially leading to remote code execution.
Technical Details
CVE-2026-0300 is a buffer overflow vulnerability in Palo Alto Networks PAN-OS. The flaw stems from improper bounds handling that results in an out-of-bounds write when the service processes specially crafted network packets. Exploitation requires no authentication, no user interaction, and only network reachability to the affected portal
Once access is obtained, attackers can:
- Intercept and decrypt traffic to steal credentials and sensitive data.
- Harvest stored VPN keys, certificates, and administrator credentials.
- Modify firewall configuration to disable logging and establish persistence.
- Pivot laterally into trusted internal segments and crown-jewel systems.
- Stage ransomware or espionage operations from a high-trust device.
This is a high-impact vulnerability due to PAN-OS’s central role as the security boundary in enterprise and government networks. A single compromise can cascade across all traffic, credentials, and internal systems the firewall is trusted to protect.ise can cascade across all managed domains and services.
NodeZero® Proactive Security Platform — Rapid Response
A NodeZero Rapid Response test has been developed to safely validate whether this authentication bypass can be exploited in your environment. The test executes real attack techniques without causing damage, giving teams immediate clarity on exposure.
- Run the Rapid Response test: Launch from the NodeZero platform to determine if unauthorized access is possible
- Patch immediately: Upgrade to a fixed version based on your PAN-OS release tier
- Re-run the test: Confirm the vulnerability is no longer exploitable after remediation
Affected versions & patch
Affected
Affected PAN-OS versions on PA-Series and VM-Series firewalls prior to the patched releases are vulnerable when the User-ID Authentication Portal (Captive Portal) is enabled.
Patch
Patch Palo Alto Networks has released fixes across multiple PAN-OS branches. Upgrade to one of the following or later, matching the branch your firewall is on:
- PAN-OS 12.1: 12.1.4-h5 or 12.1.7
- PAN-OS 11.2: 11.2.4-h17, 11.2.7-h13, 11.2.10-h6, or 11.2.12
- PAN-OS 11.1: 11.1.4-h33, 11.1.6-h32, 11.1.7-h6, 11.1.10-h25, 11.1.13-h5, or 11.1.15
- PAN-OS 10.2: 10.2.7-h34, 10.2.10-h36, 10.2.13-h21, 10.2.16-h7, or 10.2.18-h6
If patching cannot be performed immediately, restrict User-ID Authentication Portal access to trusted internal zones only, disable the portal where it is not required, and apply the Palo Alto Threat Prevention signature available for PAN-OS 11.1 and above.
Timeline
- May 5, 2026 – Palo Alto Networks Security Advisory published, disclosing the vulnerability and fixes
- May 5, 2026 – H3 begins rapid response assessment
- May 6, 2026 – Added to CISA KEV
- May 15, 2026 – Exploit added to n0
References
Read about other CVEs
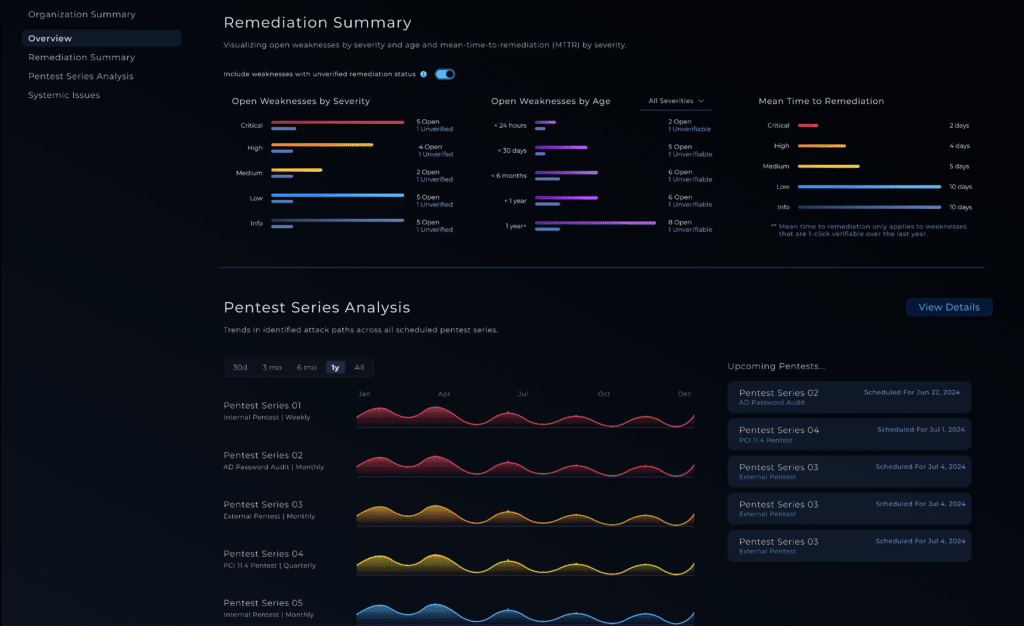
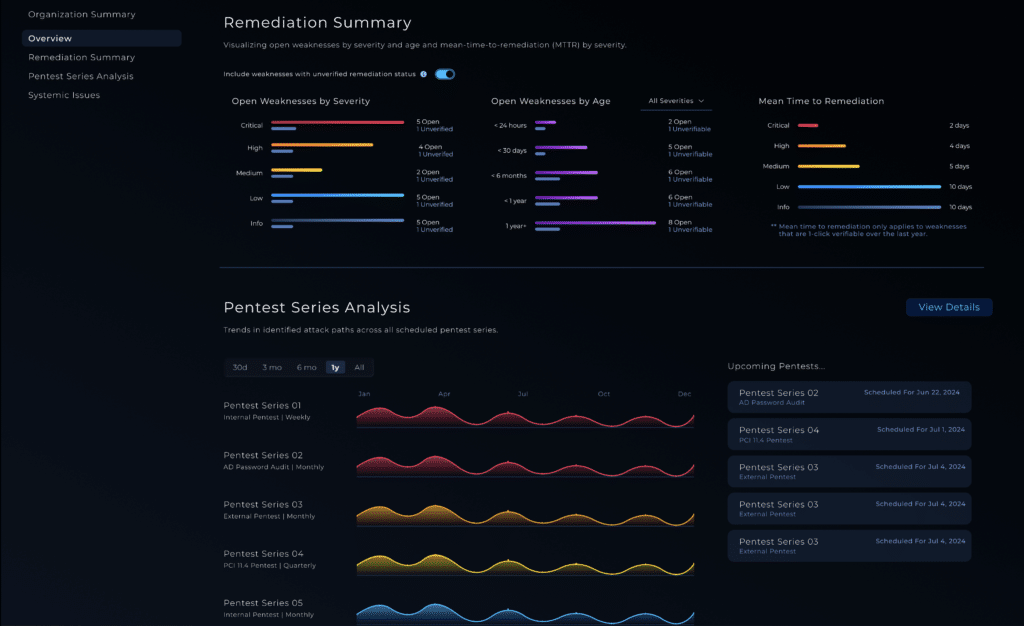
NodeZero® Platform
Implement a continuous find, fix, and verify loop with NodeZero
The NodeZero® platform empowers your organization to reduce your security risks by autonomously finding exploitable weaknesses in your network, giving you detailed guidance around how to priortize and fix them, and having you immediately verify that your fixes are effective.
Recognized By
如有侵权请联系:admin#unsafe.sh