Cyber supply-chain attacks did not originate with computers. They are part of a much old 2026-5-13 12:42:16 Author: krypt3ia.wordpress.com(查看原文) 阅读量:5 收藏
Cyber supply-chain attacks did not originate with computers. They are part of a much older strategic logic rooted in warfare, trade, logistics, and trust manipulation. Across history, adversaries repeatedly discovered that directly attacking a fortified target is often less effective than compromising the systems, suppliers, intermediaries, or dependencies that sustain it. The modern cyber supply-chain attack is therefore best understood not as a new phenomenon, but as the digital evolution of an ancient operational principle: compromise what the target already trusts, depends upon, or routinely accepts into its environment.
In pre-industrial warfare, supply-chain compromise often took physical form. Armies poisoned wells, contaminated food stores, sabotaged weapons shipments, infiltrated merchant caravans, or introduced defective materiel into enemy logistics chains. During the Peloponnesian Wars, Roman campaigns, and later medieval conflicts, control of roads, grain supplies, blacksmithing, and shipping networks often mattered more than battlefield engagements themselves. A castle could withstand assault for months, but if the food supplier was corrupted or the river poisoned upstream, the fortress became vulnerable without a direct breach. The strategic pattern already existed: attack the dependency, not merely the defended perimeter.
As global trade expanded during the colonial and industrial eras, supply-chain attacks became increasingly sophisticated. Empires targeted shipping routes, insurance systems, manufacturing inputs, and industrial suppliers. Sabotage during the First and Second World Wars demonstrated the enormous power of indirect compromise. Intelligence services infiltrated factories, inserted defective components into military production, manipulated fuel supplies, tampered with rail logistics, and conducted covert operations against industrial infrastructure. One of the most important lessons of twentieth-century warfare was that industrial capacity itself was a strategic weapon. Destroying or corrupting the production chain could have greater operational impact than destroying frontline forces.
Cold War intelligence services refined these concepts further. Soviet and Western intelligence agencies both recognized that supply systems created opportunities for covert penetration. The famous Farewell Dossier operation of the early 1980s reportedly involved manipulated industrial control software and sabotaged technology transfers targeting Soviet infrastructure acquisition programs. Whether every public detail of the incident is historically accurate remains debated, but the strategic concept became central to modern cyber doctrine: corrupt technology before the adversary deploys it.
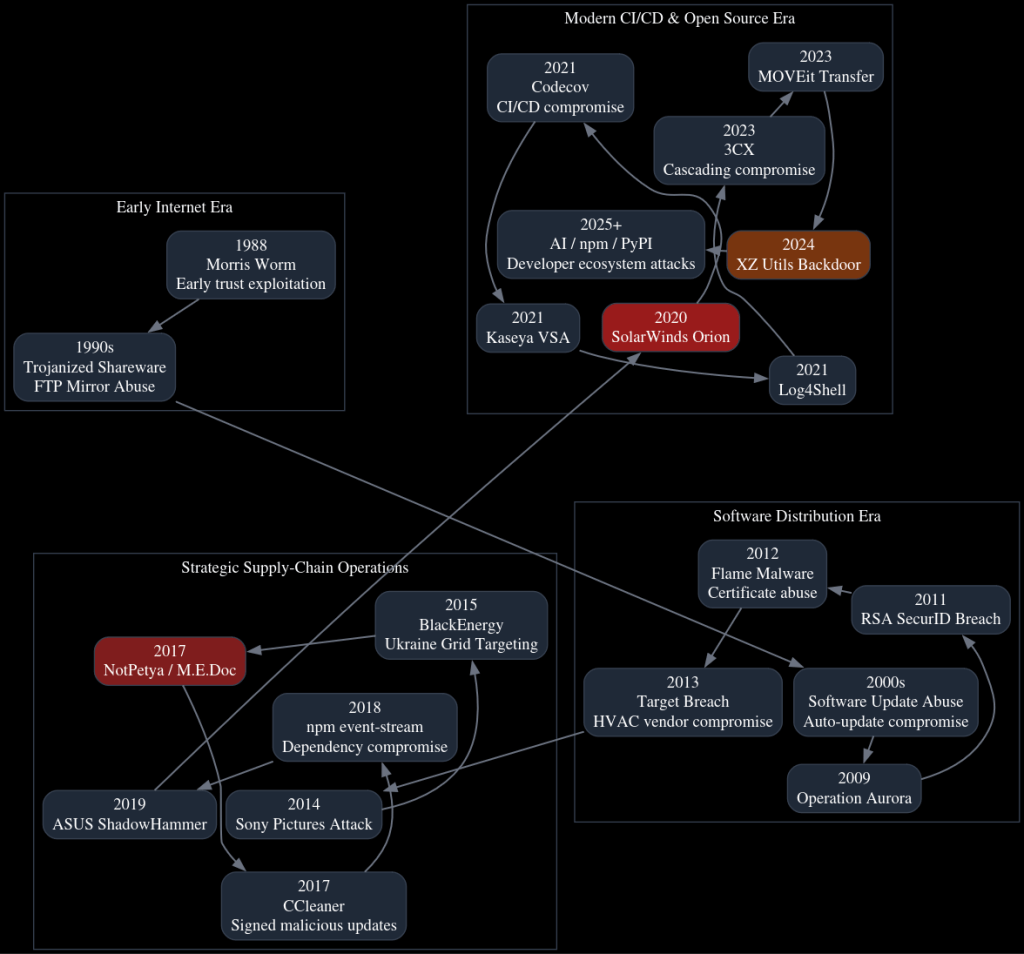
The rise of computing and networked systems merely transformed the medium through which supply-chain compromise occurred. In the early internet era of the 1980s and 1990s, trust was largely implicit. Universities, research institutions, hobbyist bulletin board systems, and early software communities operated on assumptions of cooperative behavior. Software was exchanged through FTP servers, floppy disks, CD-ROMs, email attachments, and bulletin board downloads with minimal integrity validation. Attackers quickly recognized that compromising widely distributed software or inserting malicious code into trusted distribution points allowed them to scale access far beyond direct intrusion attempts.
Early malware and Trojanized software represented primitive forms of cyber supply-chain compromise. Attackers embedded malicious code into pirated software, cracked utilities, shareware packages, and mirrored downloads. Users trusted the source because it appeared familiar or community-approved. The Morris Worm in 1988 was not technically a supply-chain attack in the modern sense, but it revealed how interconnected trusted systems could rapidly propagate compromise across a networked ecosystem. The lesson was foundational: trust relationships create attack surfaces.
By the late 1990s and early 2000s, the software ecosystem had centralized around commercial vendors and automated updates. This changed the economics of compromise dramatically. Instead of infecting individual victims one at a time, attackers could compromise the vendor itself and inherit downstream trust automatically. Software update systems became particularly attractive because organizations intentionally configured defenses to permit them. Firewalls, antivirus exclusions, administrative privileges, and scheduled execution policies often granted update mechanisms implicit trust.
This era marked the transition from opportunistic abuse into strategic software supply-chain operations. Attackers increasingly targeted software vendors, code-signing infrastructure, and distribution systems. The objective was no longer simply malware distribution, but stealthy persistence through trusted software relationships. Security products, network management tools, accounting platforms, and remote administration software became especially valuable targets because they operated deep inside enterprise environments with elevated privileges.
By the 2010s, cyber supply-chain attacks matured into major intelligence and military instruments. The 2013 Target breach demonstrated how third-party access relationships could become intrusion vectors when attackers compromised an HVAC vendor to pivot into the retailer’s payment environment. The attack revealed that vendor trust relationships effectively extended the enterprise perimeter outward into the broader commercial ecosystem.
The 2017 NotPetya operation represented a historic escalation. Russian military intelligence operators compromised the Ukrainian M.E.Doc accounting software platform and used legitimate software updates to distribute destructive malware. Although initially focused on Ukraine, the interconnected nature of global business networks caused the malware to spread internationally, disrupting shipping, logistics, pharmaceuticals, and manufacturing worldwide. NotPetya transformed supply-chain compromise from an espionage technique into a strategic cyber weapon capable of systemic economic disruption.
The same year, the CCleaner compromise demonstrated the danger of poisoned trusted software updates signed with legitimate certificates. Users installed malware willingly because the software appeared authentic. Shortly afterward, the event-stream npm compromise exposed a different dimension of supply-chain risk: the fragility of open-source trust relationships. Instead of compromising a corporation directly, attackers manipulated maintainer trust and dependency inheritance inside the open-source ecosystem itself. Modern software, assembled from thousands of interconnected packages, proved vulnerable not only to technical compromise but to social engineering and governance manipulation.
The SolarWinds Orion compromise in 2020 represented perhaps the apex of modern cyber supply-chain espionage. By infiltrating the build environment of a trusted network-management platform, Russian intelligence operators embedded malicious code directly into software updates distributed to governments, defense contractors, and critical enterprises. The operation demonstrated extraordinary operational patience and sophistication. The attackers did not merely exploit software; they weaponized institutional trust itself. Organizations installed the malicious updates because doing so was part of standard security and operational procedure.
Following SolarWinds, attackers increasingly shifted toward CI/CD pipelines, cloud identity systems, package repositories, and developer tooling. The Codecov breach showed that compromising software-development pipelines could expose authentication secrets, cloud credentials, and deployment tokens at enormous scale. The Kaseya VSA ransomware incident illustrated how managed service providers could function as force multipliers for downstream compromise. The 3CX compromise later demonstrated cascading supply-chain attacks, where one compromised supplier became the mechanism to compromise another software provider.
The 2024 XZ Utils backdoor incident revealed yet another evolutionary step: long-term social infiltration of open-source ecosystems. The attacker appeared to spend years building trust within the maintainer community before introducing a highly sophisticated backdoor into a core Linux compression library. This incident was historically significant because it blurred the boundary between technical compromise and human intelligence tradecraft. The maintainer ecosystem itself became the target.
Today, supply-chain attacks have expanded beyond software into cloud platforms, AI development ecosystems, identity providers, and infrastructure-as-code environments. Modern attackers increasingly target GitHub accounts, package registries such as npm and PyPI, cloud API tokens, CI/CD systems, container repositories, and machine-learning tooling. The objective is no longer merely malware distribution. Instead, attackers seek persistent influence over the mechanisms by which software, infrastructure, and digital trust are created and maintained.
The continuity across centuries is striking. Whether poisoning grain in antiquity, sabotaging industrial machinery during world wars, manipulating technology transfers during the Cold War, or backdooring open-source packages today, the strategic principle remains fundamentally unchanged. Supply-chain attacks succeed because they exploit the efficiencies of trust. Human systems—military, commercial, industrial, or digital—must rely on intermediaries, dependencies, and distributed production chains to function at scale. Those same efficiencies create pathways for covert compromise.
What has changed in the cyber era is velocity, reach, and systemic dependency. Ancient sabotage might affect a city or army. Modern digital supply-chain compromise can affect governments, hospitals, financial systems, cloud platforms, telecommunications providers, and global logistics simultaneously. The attack surface is no longer merely physical infrastructure or software distribution; it is the entire architecture of modern interconnected trust.
Early internet era: trust without verification
The early internet was built around academic trust, shared code, mailing lists, FTP mirrors, and weak authentication. The Morris worm in 1988 was not a supply-chain attack in the modern sense, but it exposed the same structural weakness: trusted, interconnected systems could propagate harm quickly when assumptions failed. It exploited Unix weaknesses, including sendmail behavior and weak passwords, and slowed parts of the early internet. (SentinelOne)
During the 1990s and early 2000s, the supply-chain problem was still immature but visible in three forms: Trojanized freeware/shareware, infected removable media, and compromised download sites. Attackers did not yet need to compromise CI/CD systems because most software delivery lacked integrity controls. Trust was social, not cryptographic.
2000s: software distribution becomes the attack surface
As enterprises standardized around commercial software, centralized patching, and remote management tools, attackers began recognizing that the update channel itself was a privileged pathway. Signed software, vendor-hosted downloads, and automatic updates became high-value delivery mechanisms.
This period established the critical supply-chain principle: compromising the vendor can be more efficient than compromising each target individually. Security tools, management agents, accounting software, and remote administration products became especially attractive because they often run with elevated privileges and broad network access.
2010s: supply-chain attacks become strategic
NotPetya / M.E.Doc — destructive supply-chain warfare
The 2017 NotPetya incident is the canonical destructive supply-chain attack. Russian-linked Sandworm operators used the Ukrainian M.E.Doc accounting software update mechanism to distribute malware that masqueraded as ransomware but functioned as a wiper. It spread globally, causing major operational damage beyond Ukraine. (MITRE ATT&CK)
Strategic significance: NotPetya showed that a regional software supplier could become a global blast-radius amplifier. The victimology was determined not only by targeting intent but by dependency geography.
CCleaner — trusted utility as intrusion vehicle
In 2017, attackers compromised legitimate signed CCleaner builds distributed from official channels. Avast later reported that compromised versions were released in August 2017 and remediated in September 2017. (blog.avast.com)
Strategic significance: CCleaner demonstrated that code signing alone is insufficient if the build or release process is compromised. A malicious binary can still be “legitimate” from the user’s perspective.
event-stream / npm — maintainer trust exploitation
In 2018, the event-stream npm incident showed how open-source maintainer trust could be weaponized. A malicious maintainer gained control of a popular package dependency and inserted code targeting cryptocurrency wallet users. npm confirmed that a malicious package entered the event-stream dependency chain and removed the affected packages. (blog.npmjs.org)
Strategic significance: The attack shifted attention from vendor compromise to ecosystem compromise: maintainers, dependency graphs, package ownership, and transitive trust.
2020–2021: enterprise-scale supply-chain compromise
SolarWinds Orion — strategic espionage through software updates
The SolarWinds compromise remains the defining state-backed software supply-chain espionage case. Attackers inserted a backdoor into Orion software updates, affecting a broad customer base that included government and enterprise networks. CISA issued emergency directives and follow-on guidance for the incident. (CISA)
Strategic significance: SolarWinds proved that trusted network-management software is an ideal espionage platform: privileged, widely deployed, allowlisted, and connected to sensitive environments.
Codecov — CI/CD secrets as the real target
In 2021, Codecov disclosed that an attacker modified its Bash Uploader script after obtaining credentials from an error in Codecov’s Docker image creation process. The altered script enabled theft of CI/CD environment variables and secrets. (Codecov)
Strategic significance: Codecov moved the center of gravity from endpoint compromise to pipeline compromise. CI/CD systems became intelligence targets because they contain cloud keys, signing credentials, tokens, and deployment access.
Kaseya VSA — MSP tooling as ransomware distribution
In July 2021, REvil exploited Kaseya VSA to push ransomware through managed service provider infrastructure. U.S. government reporting noted that Kaseya was already patching the VSA vulnerability and that there was no evidence of malicious changes to the VSA codebase. (DNI)
Strategic significance: Kaseya showed that supply-chain attacks do not require poisoned code. Exploiting a trusted management platform can produce the same downstream effect.
2022–2024: cascading, open-source, and managed-file-transfer risk
3CX — cascading supply-chain compromise
In 2023, Mandiant attributed the 3CX software supply-chain attack to UNC4736, assessed with high confidence as North Korea-nexus activity. Mandiant reported that the 3CX compromise was initiated through a prior compromise of another software supply chain, creating a cascading attack model. (Google Cloud)
Strategic significance: 3CX demonstrated supply-chain-on-supply-chain compromise: one poisoned dependency or software product becomes the entry point to poison another.
MOVEit Transfer — mass exploitation of a data-transfer dependency
In 2023, CL0P exploited CVE-2023-34362 in MOVEit Transfer, a managed file-transfer platform used by many organizations to move sensitive data. CISA and FBI issued a joint advisory on the exploitation. (CISA)
Strategic significance: MOVEit was not a classic poisoned-update case. It was supply-chain risk through common third-party infrastructure: one product flaw exposed many downstream organizations.
XZ Utils backdoor — near-miss against Linux trust infrastructure
In 2024, malicious code was discovered in XZ Utils versions 5.6.0 and 5.6.1. CISA warned that the malicious code could allow unauthorized access to affected systems, and NVD described complex obfuscation in upstream tarballs affecting the build process. (CISA)
Strategic significance: XZ was a watershed case for open-source governance. The attack appeared to target the human layer of maintainership as much as the code layer: patient trust-building, release manipulation, and highly selective activation conditions.
2025–today: developer ecosystems and AI-adjacent supply chains
Recent campaigns increasingly target npm, PyPI, GitHub repositories, CI/CD credentials, cloud API keys, and AI developer tooling. Reporting in 2026 described “Mini Shai-Hulud” activity affecting PyPI and npm ecosystems, including packages associated with AI developer workflows and credential theft from GitHub, cloud, and CI/CD environments. (Tom’s Hardware)
This marks the current phase: the attacker is no longer merely poisoning software for end users. They are compromising the systems that produce software, train models, deploy cloud workloads, and automate enterprise development.
Attack-pattern evolution
| Era | Dominant trust target | Typical technique | Strategic effect |
|---|---|---|---|
| 1980s–1990s | Shared systems, public code, FTP/software mirrors | Worms, Trojanized downloads, infected media | Opportunistic spread |
| 2000s | Vendor downloads, update channels | Compromised installers, weak signing, poisoned updates | Broad user compromise |
| 2010s | Software vendors, package ecosystems | Signed malware, malicious dependencies, maintainer takeover | Scaled intrusion and sabotage |
| 2020–2021 | Build systems, MSP tools, CI/CD | Build compromise, token theft, remote-management abuse | Enterprise and government penetration |
| 2022–2024 | Open source, transfer platforms, chained suppliers | Dependency compromise, mass exploitation, cascading compromise | Systemic blast radius |
| 2025–2026 | Developer identity, cloud, AI tooling | Package worms, token theft, repo abuse, CI/CD propagation | Self-replicating ecosystem compromise |
Core TTPs
The recurring techniques are:
- Compromise of build or release infrastructure — SolarWinds, CCleaner, XZ.
- Malicious dependency insertion — event-stream, npm/PyPI campaigns.
- Maintainer or developer account compromise — open-source package poisoning.
- MSP/RMM abuse — Kaseya-style downstream deployment.
- CI/CD secret theft — Codecov-style environment-variable exfiltration.
- Common third-party platform exploitation — MOVEit-style mass data theft.
- Cascading supply-chain compromise — 3CX, where one supplier compromise enables another.
- Code-signing and update-channel abuse — legitimate trust signals used to deliver malicious payloads.
Strategic assessment
Supply-chain attacks are attractive because they invert the defender’s trust model. Instead of bypassing defenses directly, the attacker rides through approved software, trusted vendors, signed binaries, routine updates, or sanctioned automation. This makes detection difficult because the malicious activity often begins from a trusted identity, trusted binary, trusted host, or trusted workflow.
The most dangerous modern pattern is the convergence of three layers:
Software supply chain + identity supply chain + cloud supply chain.
Once attackers steal developer tokens, CI/CD secrets, signing keys, or cloud credentials, they can move from one compromised package or vendor into many downstream environments. The blast radius is no longer defined by malware propagation alone; it is defined by dependency graphs, SaaS integrations, automation rights, and identity trust.
Defensive implications
Effective defense now requires C-SCRM, not just endpoint security. Minimum viable controls include SBOMs, signed and reproducible builds, hardened CI/CD, least-privilege tokens, short-lived credentials, MFA for maintainers, package provenance, dependency pinning, behavioral monitoring of build systems, and vendor-risk telemetry.
NIST SP 800-161 Rev. 1 frames this as a multilevel discipline: organizations must identify, assess, and mitigate cybersecurity risks across products, services, suppliers, and enterprise risk processes. (NIST Computer Security Resource Center)
The practical bottom line: supply-chain security is now a core national-security, enterprise-risk, and software-engineering problem. The attacker’s target is no longer just the victim network. It is the victim’s trust fabric.
如有侵权请联系:admin#unsafe.sh
