This month’s Patch Tuesday remedies 137 security vulnerabilities, including 31 marked critical by Microsoft, with no zero-days actively exploited in the wild.
Microsoft defines a zero-day as “a flaw in software for which no official patch or security update is available yet.” This month, Microsoft has not observed any included vulnerability being exploited in production environments.
Still, this release is far from low-risk. A large chunk of the critical bugs allow remote code execution (RCE) across Windows services, Office, Azure, SharePoint, and graphics components. That means attackers who trick a user into opening a malicious document or lure them into connecting to a malicious service could gain full control of a system.
Two vulnerabilities to prioritize
From that list, we selected two that look like they could cause some trouble.
First is CVE-2026-40361, which has a CVSS score of 8.4 out of 10. It’s described as a critical use-after-free vulnerability in Microsoft Word that could allow an attacker to execute code locally on the affected system.
Use-after-free is a class of vulnerability caused by incorrect use of dynamic memory during a program’s operation. If, after freeing a memory location, a program does not clear the pointer to that memory, an attacker may be able to use the error to manipulate the program.
So, if an attacker convinces a user to open a malicious Word document, or even previews the file, they could execute arbitrary code with the privileges of the current user. That’s often enough to install malware, steal credentials, or move laterally through a network.
Second is CVE-2026-35421 (CVSS score 7.8 out of 10). This is a critical heap-based buffer overflow in Windows Graphics Device Interface (GDI). A buffer overflow occurs when an area of memory within a software application reaches its address boundary and writes into an adjacent memory region. Microsoft notes:
“For this vulnerability to be exploited, a user would need to open or otherwise process a specially crafted Enhanced Metafile (EMF) file using Microsoft Paint. This action is necessary to trigger the affected graphics functionality in the Windows component.”

Real-time protection. Zero effort.
How to apply fixes and check if you’re protected
These updates fix security problems and keep your Windows PC protected. Here’s how to make sure you’re up to date:
1. Open Settings
- Click the Start button (the Windows logo at the bottom left of your screen).
- Click on Settings (it looks like a little gear).
2. Go to Windows Update
- In the Settings window, select Windows Update (usually at the bottom of the menu on the left).
3. Check for updates
- Click the button that says Check for updates.
- Windows will search for the latest Patch Tuesday updates.
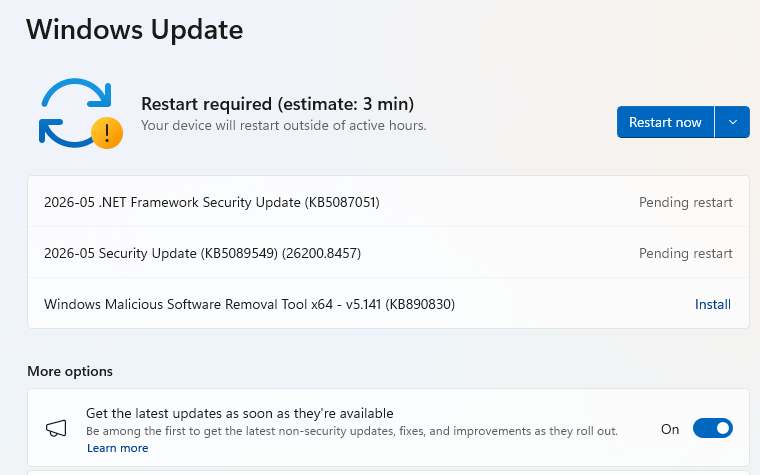
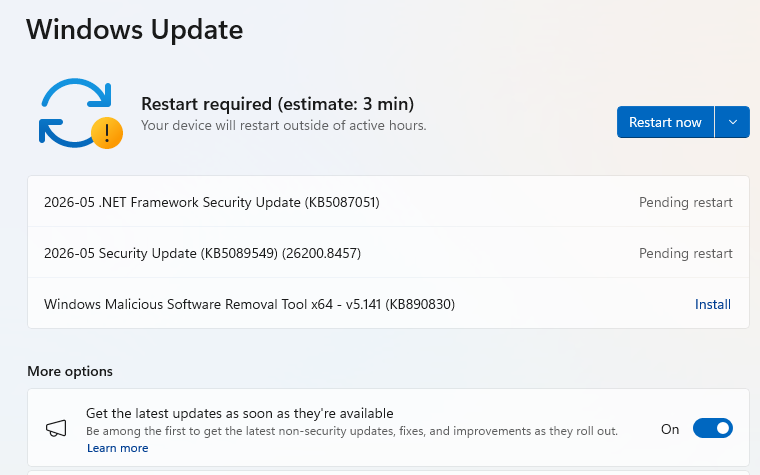
- If you have selected to get the latest updates as soon as they’re available, you may see this under More options.
- In which case you may see a Restart required message. Restart your system and the update will complete.
- If not, continue with the steps below.
4. Download and Install If updates are found, they’ll start downloading automatically. Once complete, you’ll see a button that says Install or Restart now.
- Click Install if needed and follow any prompts. Your computer will usually need a restart to finish the update. If it does, click Restart now.
5. Double-check you’re up to date
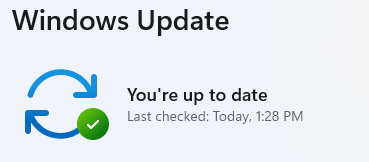
- After restarting, go back to Windows Update and check again. If it says You’re up to date, you’re all set!
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.