In a previous post about the adjacencies to the MDR market, I laid out a framework 2026-5-11 13:41:0 Author: raffy.ch(查看原文) 阅读量:2 收藏
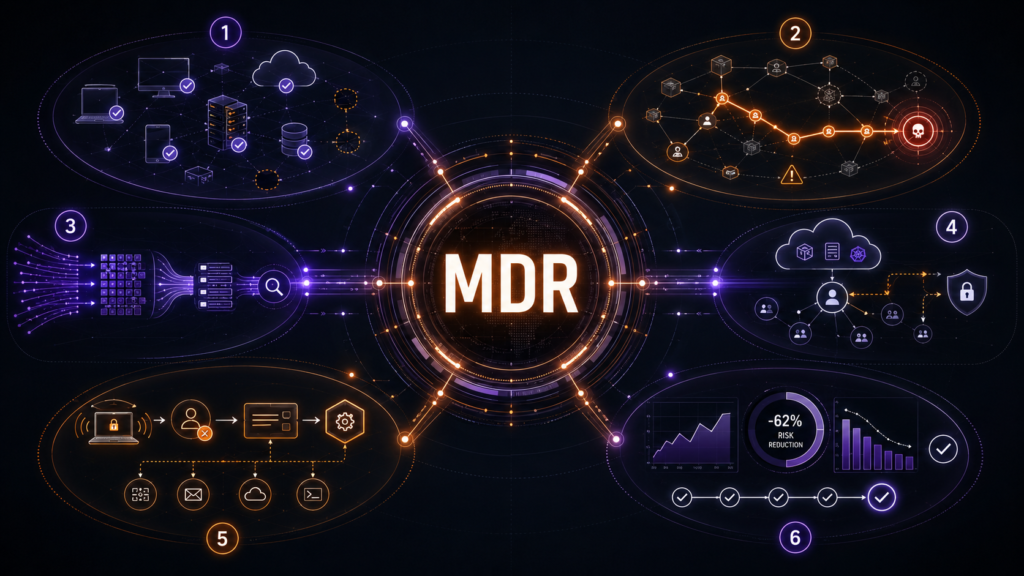
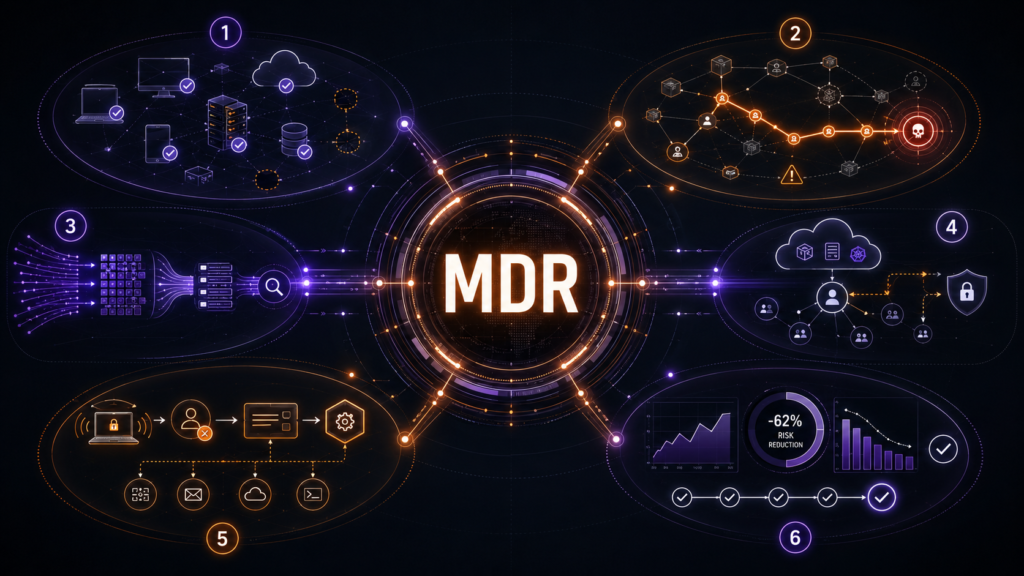
In a previous post about the adjacencies to the MDR market, I laid out a framework for how MDR needs to evolve beyond alert triage. The basic idea was that future MDR should not just be “EDR alerts plus analysts.” It should become the control plane for cybersecurity operations and cyber risk reduction.
This post goes one level deeper. If MDR is going to become that control plane, what capabilities actually need to sit closest to the operating loop? The strongest extensions are the ones that help MDR understand what exists, what is exposed, what telemetry is missing, what response should happen, and whether risk actually went down.
Asset And Control Coverage
This is the starting point. MDR cannot protect an environment it does not understand, so the provider needs to know:
- What exists?
- What is unmanaged?
- What lacks EDR coverage?
- What lacks vulnerability scanning?
- What logs are missing?
- Which assets are business-critical?
- Which controls are present, absent, or failing?
Asset context turns MDR from generic alert review into prioritized operations. An alert on a test machine is not the same as an alert on a domain controller, cloud control-plane asset, payment system, build server, or executive endpoint. An exposed vulnerability on an internet-facing revenue system is not the same as the same CVE on a low-value internal host.
The future MDR has to understand this context automatically in a dynamic envirionment.
Exposure And CTEM
This is probably the most important adjacency. Classic MDR waits for something to fire. Exposure management asks what can be attacked before the alert exists.
The future MDR should know:
- What is exploitable?
- What is internet-facing?
- What is business-critical?
- What is currently being targeted?
- What attack paths exist?
- What should be fixed first?
- Which exposures actually got closed?
This is what moves MDR from reactive monitoring to proactive risk reduction. The important distinction is that this cannot just be scanner reporting. Vulnerability management becomes an MDR extension only when it is tied to exploitability, asset criticality, identity paths, observed threat activity, and actual remediation workflow.
SIEM And Data Quality
MDR is only as good as the data it can use. That makes SIEM operations and data quality core to the future model, even if the MDR provider does not own the SIEM product.
The provider should know:
- Are the right logs ingested?
- Are important sources missing?
- Are fields normalized?
- Are detections using the right data?
- Is retention sufficient?
- Is query performance good enough for investigation?
- Is SIEM cost being optimized?
This becomes more important as AI changes the interface to the SOC. If AI becomes the primary user of security data, the SIEM UI may matter less, but the quality, structure, accessibility, and completeness of the data matter more.
Cloud And Identity Posture
Modern attack paths increasingly run through identity, SaaS, cloud entitlements, workload permissions, and configuration mistakes. That means cloud and identity posture are not optional context for serious MDR.
The future MDR should understand:
- Who can access what?
- Which identities are overprivileged?
- Which accounts are risky or stale?
- Which cloud paths create attack chains?
- Which workloads are exposed?
- Which posture issues make detection or containment harder?
Without this context, MDR sees too little. It may detect a suspicious event, but miss the path that made the event possible.
Response Orchestration
The MDR has to respond faster than human-speed response, but safely. The system should be able to:
- Isolate an endpoint
- Disable or step-up an identity
- Block an indicator
- Remove malicious artifacts
- Open and route tickets
- Trigger patching or remediation workflows
- Escalate to IR
- Prove that the action happened
The word “safely” matters. MDR automation cannot become a blind SOAR playbook that breaks production. The provider needs policy, approvals, rollback paths, asset criticality, business context, and evidence that the response improved the situation.
What The Future MDR Should Prove
The old MDR output was an investigated alert. The future MDR output should be a safer environment. That changes the questions the service should answer:
- What percentage of critical assets are covered by EDR, vulnerability scanning, identity telemetry, cloud telemetry, and relevant logs?
- Which high-risk exposures were removed this month?
- Which attack paths were closed?
- Which detections improved because missing telemetry was fixed?
- Which response actions were automated safely?
- Which risks were accepted by the business?
- Which risks were remediated?
- Did measurable exposure go down?
This is the reporting layer that matters. Not activity reporting. Not “we reviewed this many alerts.” Not a dashboard that proves the provider was busy.
The stronger MDR report says: here is what exists, here is what is exposed, here is what we saw, here is what we did, here is what changed, and here is the risk that remains.
The Market Implication
The MDR market will split between alert-centric providers and control-plane providers. Alert-centric MDR can still be useful. Many buyers still need 24/7 investigation, escalation, and containment. But that model will be pressured by platform vendors, automation, and buyer expectations for more context.
The more defensible MDR provider will move upstream and downstream at the same time. Upstream, it owns asset context, control coverage, telemetry quality, exposure prioritization, cloud posture, and identity posture. Downstream, it owns containment, remediation orchestration, incident response, validation, and outcome reporting.
That is the future MDR control plane. The category may keep the same name, but the job changes from outsourced alert handling to command central for cyber risk reduction.
I will follow up on this with another MDR post to explore some topics a bit more, such as:
- The product aspect of the MDR service business
- The MDR symbiotic relationship with SIEM
- AI changing the MDR platform architecture
- Detection having to move into automated response
Stay tuned …
No comments yet.
如有侵权请联系:admin#unsafe.sh