The financial services ecosystem in India is undergoing rapid digital transformation, and fintec 2026-5-2 04:52:43 Author: securityboulevard.com(查看原文) 阅读量:32 收藏
The financial services ecosystem in India is undergoing rapid digital transformation, and fintech organizations sit at the center of this evolution. With increasing cyber threats targeting digital payments, lending platforms, and financial data, regulatory oversight has intensified. The Reserve Bank of India mandates a strong RBI cybersecurity framework that fintechs must follow to ensure resilience, trust, and compliance.
NBFCs and Indian banks are navigating an increasingly hostile threat landscape in 2025. Cyberattacks on the BFSI sector are rising by nearly 25% year over year, with potential losses reaching ₹50,000 crore annually.
In this environment, the RBI Cybersecurity Compliance Checklist serves as a critical safeguard, strengthening operations, VAPT processes, and Zero Trust frameworks to defend against threats like ransomware and deepfake-driven attacks. This blog provides a data-backed roadmap aligned with the latest RBI regulations, helping organizations implement compliance effectively and turn it into a strategic advantage rather than just a mandate.
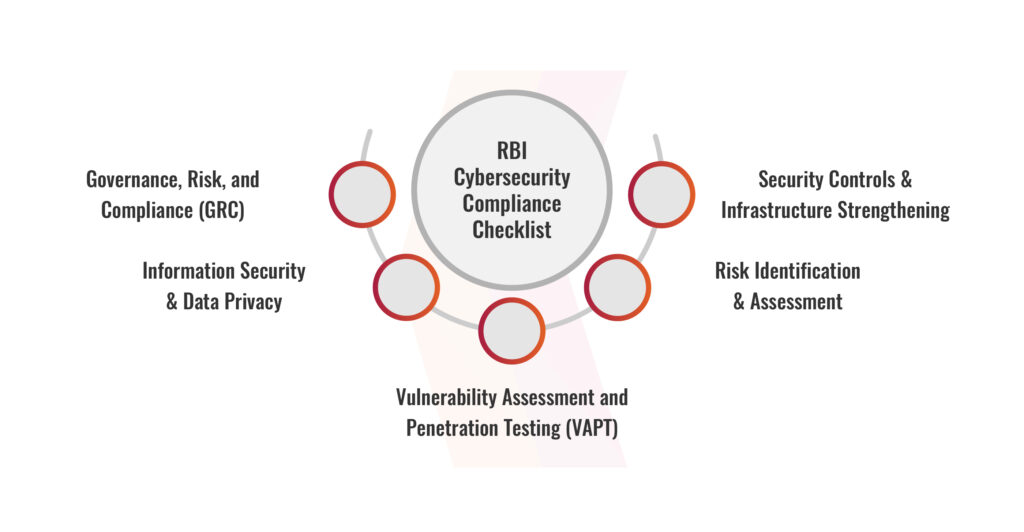
RBI Cybersecurity Compliance Checklist
The RBI cybersecurity framework checklist provides a structured framework for organizations to strengthen their security posture and ensure regulatory compliance. It outlines essential controls across governance, risk management, and technical security. Adhering to these guidelines helps organizations mitigate cyber risks and maintain operational resilience.
Security Controls & Infrastructure Strengthening
Infrastructure Hardening Testing assesses the security posture of critical systems, networks, and applications to ensure alignment with established security baselines. This includes evaluating the effectiveness of network segmentation, endpoint protection mechanisms, server hardening practices, and application-level security configurations. Access Control Testing focuses on validating identity and access management mechanisms, including authentication processes, user permissions, and privilege governance.
Vulnerability Management Testing evaluates an organization’s capability to detect, prioritize, and remediate security vulnerabilities across systems and applications. This involves evaluating vulnerability scanning, patching, and how insights inform risk-based decisions.
Governance, Risk, and Compliance (GRC)
Organizations must demonstrate that their cybersecurity policies are formally approved by the board and regularly updated to align with evolving business strategies and risk appetite. Assess cybersecurity governance, including the CISO’s authority and how cyber risk integrates into enterprise risk management.
Organizations must comply with RBI guidelines, industry standards, and applicable legal requirements. This involves validating internal audit mechanisms, external assessments, and continuous monitoring practices to maintain a consistent state of compliance.
Risk management testing ensures organizations can identify, assess, and respond to cyber risks effectively using a structured approach. This includes evaluating threat modeling approaches, vulnerability management processes, and risk quantification frameworks that support informed and strategic decision-making.
Information Security & Data Privacy
Data Protection ensures that teams keep sensitive data secure at all times, whether they store, share, or process it. Within the RBI cybersecurity framework, it evaluates encryption strength, key management reliability, and secure data-handling practices to protect critical information. Data Classification and Handling Validation examines how effectively an organization understands and manages its data landscape.
Privacy Compliance Testing ensures that security efforts align with regulatory expectations under RBI cybersecurity framework, including mandates. It assesses consent management, data rights protection, and cross-border transfers to ensure compliance and build trust.
Risk Identification & Assessment
Financial institutions must conduct comprehensive cyber risk assessments that go beyond surface-level evaluations. This includes identifying and classifying critical assets based on sensitivity, mapping potential threat vectors, and performing detailed vulnerability assessments. Teams then translate these insights into structured mitigation strategies supported by well-defined policies and controls. At the governance level, CISOs play a pivotal role, operating independently of the IT function and reporting directly to risk leadership, ensuring that cybersecurity remains a strategic priority aligned with enterprise risk management.
Vulnerability Assessment and Penetration Testing (VAPT)
Mandatory VAPT must be conducted annually, covering applications, APIs, and infrastructure, and must address vulnerabilities aligned with the OWASP Top 10 and ensure proper remediation validation. Additionally, testing should be performed more frequently after any major system changes. Organizations should adopt continuous vulnerability management through automated scanning, structured patching, and risk-based prioritization to continuously identify and mitigate security risks.
Is your organization ready to strengthen its defenses? Connect with us to confidently navigate the RBI cybersecurity framework.
Book Your Free Cybersecurity Consultation Today!
Why is RBI Cybersecurity Framework Important for Fintech Organizations?
- Regulatory Penalties and License Suspension: Non-compliance with guidelines issued by the Reserve Bank of India can lead to heavy financial penalties, operational restrictions, or even suspension of licenses. This can directly halt business operations and impact long-term sustainability.
- Loss of Partnerships with Banks/NBFCs: Fintechs rely heavily on partnerships with regulated entities. Failure to comply with the RBI cybersecurity framework can result in termination of partnerships, limiting access to critical banking infrastructure and financial networks.
- Reputational Damage and Customer Distrust: Security lapses or regulatory actions can severely damage brand credibility. In the fintech space, where trust is a key differentiator, even a single incident can lead to customer churn and reduced market confidence.
- Increased Risk of Cyberattacks: Non-compliance often indicates weak security controls, making organizations easy targets for hackers. This increases exposure to data breaches, ransomware, and financial fraud.
- Impact on Financial Stability and Data Protection: Fintech platforms handle sensitive financial data. Any compromise can disrupt financial transactions and expose customer information, leading to legal liabilities and regulatory scrutiny.
Join our weekly newsletter and stay updated
Common Compliance Gaps Observed
Organizations often fall short in the following areas under the RBI cybersecurity framework, which can weaken their overall security posture and audit readiness:
- Delayed Incident Reporting: Many fintechs fail to report cybersecurity incidents within the stipulated timelines defined by the Reserve Bank of India. Delays not only violate regulatory requirements but also hinder timely response and containment, increasing the impact of breaches.
- Weak Access Control Mechanisms: Inadequate implementation of Identity and Access Management (IAM), lack of multi-factor authentication (MFA), and excessive privileged access often lead to unauthorized system access and insider threats.
- Lack of Network Segmentation: Flat network architectures without proper segmentation make it easier for attackers to move laterally across systems. This significantly increases the blast radius of a cyberattack.
- Insufficient Logging and Monitoring: Lack of centralized logging and weak monitoring reduces visibility, delaying threat detection and response.
- Irregular VAPT and Patch Management: Organizations often conduct Vulnerability Assessment and Penetration Testing (VAPT) as a one-time activity rather than an ongoing process. Delayed patching leaves known vulnerabilities exploitable.
Conclusion
Compliance with guidelines issued by the Reserve Bank of India is fundamental for fintech organizations operating in today’s high-risk digital environment. The RBI cybersecurity framework not only ensures regulatory alignment but also strengthens overall cyber resilience, safeguarding sensitive financial data and critical business operations. Organizations should treat compliance as an ongoing discipline, proactively strengthening resilience against evolving threats and regulations through strong security and audit readiness.
Ultimately, fintechs that embed cybersecurity into their core strategy gain more than compliance; they build trust, enhance operational stability, and secure a sustainable competitive advantage in India’s rapidly expanding digital financial ecosystem.
FAQs
- What is the role of IS (RBI) Audit in compliance?
IS (RBI) Audit is a structured assessment that evaluates an organization’s IT governance, cybersecurity controls, and regulatory compliance. It helps identify gaps in security practices and ensures alignment with RBI guidelines.
- How often should VAPT be conducted under RBI guidelines?
Vulnerability Assessment and Penetration Testing (VAPT) should be conducted at least annually and after any major system changes. It ensures that vulnerabilities are identified and remediated before they can be exploited.
- What happens if a fintech company fails RBI compliance?
Non-compliance can result in regulatory penalties, suspension of operations, reputational damage, loss of partnerships with banks/NBFCs, and increased regulatory scrutiny.
The post RBI Cybersecurity Compliance Checklist for Fintech Organizations appeared first on Kratikal Blogs.
*** This is a Security Bloggers Network syndicated blog from Kratikal Blogs authored by Shikha Dhingra. Read the original post at: https://kratikal.com/blog/rbi-cybersecurity-compliance-checklist-for-fintech-organizations/
如有侵权请联系:admin#unsafe.sh