
好的,我现在需要帮助用户总结一篇关于软件供应链中毒的文章,控制在100字以内,并且不需要特定的开头。首先,我得通读整篇文章,抓住主要内容。 文章主要讨论了“Artifact Poisoning”,也就是软件供应链中的中毒威胁。它解释了这种攻击是如何通过污染构建块(如二进制文件、库、容器镜像等)来侵入应用的。攻击者利用了企业对内部和第三方组件的信任,导致恶意代码在系统中传播而不被察觉。 接下来,文章分析了这种威胁的风险因素:盲目信任、快速传播、传统安全措施的盲区以及长期存在的可能性。还提到了常见的攻击技术,比如打字错误欺骗和破坏构建管道。最后,文章给出了预防措施,如加强完整性控制、保护存储库访问、控制依赖关系以及采用零信任方法。 现在,我需要将这些要点浓缩到100字以内。重点包括:软件供应链中的中毒威胁、攻击方式、风险因素以及预防措施。 可能的结构是:描述威胁是什么,如何运作,带来的风险,以及如何防范。 最终总结应简洁明了,涵盖关键点。 </think> 软件供应链中的“Artifact Poisoning”是一种通过污染构建块(如二进制文件、库等)侵入应用的威胁。攻击者利用企业对内部和第三方组件的信任,在开发或部署过程中注入恶意代码。这种攻击能快速传播且长期隐藏,传统安全措施难以检测。企业需加强完整性控制、保护存储库访问并采用零信任方法以防范风险。 2026-4-28 06:9:18 Author: securityboulevard.com(查看原文) 阅读量:8 收藏
Software supply chains have quietly become one of the most critical and most vulnerable foundations of modern enterprises. Today, applications are no longer monolithic systems built entirely in-house. Instead, they are complex assemblies of open-source libraries, third-party packages, container images, APIs, and pre-built binaries pulled from multiple repositories. This interconnected ecosystem has dramatically improved speed, innovation, and scalability. But it has also introduced a risky assumption: that every component pulled into the development pipeline can be trusted. This is exactly where artifact poisoning emerges as a powerful and often invisible threat.
Rather than attacking systems directly, attackers are now targeting the building blocks of software itself. By compromising artifacts, the packaged outputs and dependencies used in development, they can infiltrate applications at scale, bypass traditional defenses, and persist undetected.
Gist on Artifact Poisoning
This is the process of injecting malicious code into software artifacts, such as binaries, libraries, packages, or container images, that are stored in repositories and consumed during development or deployment.
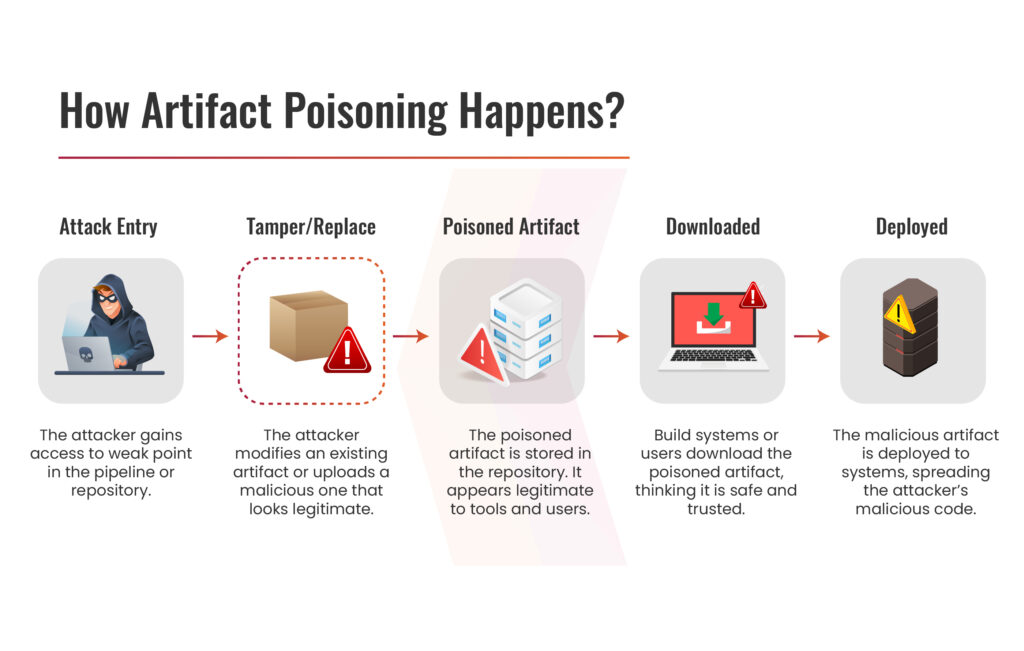
These artifacts are foundational elements of modern applications. Developers rarely build everything from scratch; instead, they pull pre-built components from internal or public repositories. When attackers poison these artifacts, they effectively weaponize trust.
Once compromised artifacts are integrated into applications, the malicious code propagates silently across systems, environments, and even organizations.
This is what makes artifact poisoning uniquely risky; it doesn’t break trust, it abuses it.
Why is Artifact Poisoning a Threat to Enterprise Supply Chain?
This is not just another supply chain vulnerability; it represents a strategic risk that directly impacts how modern enterprises build, deploy, and scale software. Its true risk lies in its ability to exploit trust, scale rapidly, and remain undetected within critical systems. Below are the key reasons why this has become a high-priority concern for enterprises:
- Blind Trust in Software Components
Enterprises rely heavily on internal repositories, third-party vendors, and open-source ecosystems to accelerate development. Over time, this dependency creates a trust-first culture, where components are consumed with minimal verification.
This implicit trust becomes a major vulnerability. Attackers can inject malicious code into seemingly legitimate artifacts, knowing they are unlikely to be deeply inspected. The risk is compounded by transitive dependencies, where a single trusted package may include multiple indirect components that are never validated.
As a result, organizations unknowingly build applications on top of unverified and potentially compromised building blocks, making artifact poisoning an effective entry point into enterprise environments.
- Rapid and Widespread Propagation
Artifact poisoning is inherently scalable. A single compromised artifact can be reused across multiple applications, teams, and environments, creating a multiplier effect that amplifies the impact of the attack.
In large enterprises, shared libraries and reusable components are common across microservices architectures. This means one poisoned artifact can simultaneously affect development, testing, and production systems.
CI/CD pipelines further accelerate this spread. Automated workflows continuously fetch and deploy artifacts, often without revalidation. This allows malicious components to propagate at machine speed, making containment and remediation significantly more complex once the attack is in motion.
- Gaps in Conventional Security Visibility
Traditional security approaches are not designed to detect threats embedded within software artifacts. Most controls focus on network activity, endpoint protection, or runtime behavior, leaving a critical visibility gap in the early stages of the software lifecycle.
This type of supply chain attack occurs during dependency resolution, artifact storage, or build processes, areas that often lack strong monitoring and validation mechanisms. Since the malicious code is packaged within legitimate artifacts, it blends seamlessly into expected behavior.
This lack of visibility makes it difficult for organizations to trace the origin of compromised components or identify when the attack was introduced, allowing poisoned artifacts to move undetected across the supply chain.
- Long-Term Persistence Through Trusted Channels
One of the riskiest aspects of artifact poisoning is its ability to provide attackers with persistent and recurring access.
By embedding backdoors within trusted artifacts, attackers ensure their code is executed repeatedly whenever the application runs. Even after patching or system rebuilds, the same compromised artifact can be reintroduced through automated pipelines, effectively restoring the attacker’s foothold.
Additionally, artifact versioning and caching mechanisms can unintentionally preserve malicious versions. This allows attackers to maintain access over extended periods while remaining under the radar, making artifact poisoning a long-term strategic threat rather than a one-time incident.
If you want to know more about supply chain attacks, read the blog on Why Supply Chain Attacks Are The Biggest Threat To Businesses?
Join our weekly newsletter and stay updated
Common Techniques Used in Artifact Poisoning
Artifact poisoning attacks are rarely random; they are carefully designed to exploit weaknesses in dependency management, developer behavior, and pipeline security. Below are some of the most common techniques attackers use, along with deeper insight into how they work and why they are effective:
- Typosquatting-Based Infiltration
Typosquatting leverages small human errors to introduce malicious artifacts. Attackers register package names that closely resemble popular or commonly used libraries, relying on minor spelling mistakes or visual similarities.
In fast-moving development environments, such errors are easy to overlook. A developer installing a dependency with a slight typo may unknowingly introduce a compromised package into the application.
These malicious packages are often designed to appear functional while embedding hidden behavior, such as credential harvesting or system reconnaissance. Because the package name looks familiar, it often bypasses manual review, allowing the poisoned artifact to integrate seamlessly into the codebase.
- Unauthorized Repository Manipulation
Internal artifact repositories are considered trusted hubs for software components, making them prime targets for attackers. One of the most common entry points into these systems is credential stuffing, a technique where attackers use previously leaked username-password combinations (often from unrelated breaches) to gain unauthorized access.
Because many users reuse credentials across platforms, attackers can automate login attempts against repository platforms using large datasets of compromised credentials. If multi-factor authentication (MFA) is not enforced or access controls are weak, even a single successful login can provide direct access to critical repositories.
- Build Pipeline Compromise
Instead of targeting stored artifacts, attackers may focus on the build infrastructure itself. By compromising CI/CD pipelines, they can inject malicious code during the artifact creation phase.
This approach is particularly effective because the resulting artifact is generated within a trusted environment. It carries valid metadata, follows standard processes, and often passes security checks, making the malicious code extremely difficult to identify.
Attackers may exploit insecure pipeline configurations, vulnerable plugins, or exposed credentials to gain access. Once inside, they can alter build scripts or introduce hidden payloads that persist across deployments.
How can Artifact Poisoning be Prevented?
Preventing artifact poisoning requires more than a single control; it demands a defense-in-depth approach across the entire software supply chain. Since attackers exploit trust, automation, and weak validation, organizations must shift toward a “verify everything” mindset. Below are the most effective strategies to mitigate artifact poisoning risks in enterprise environments:
- Enforce Strong Artifact Integrity Controls
The first line of defense is ensuring that every artifact is authentic and untampered.
- Implement cryptographic signing for all artifacts
- Verify digital signatures before consumption in pipelines
- Use checksum/hash validation to detect unauthorized changes
This ensures that even if an attacker attempts to replace or modify an artifact, the system can immediately detect inconsistencies.
- Secure Access to Artifact Repositories
Since repositories are prime targets, controlling access is critical.
- Enforce role-based access control (RBAC) with least privilege
- Enable multi-factor authentication (MFA) for all users
- Monitor login activity for anomalies (e.g., unusual locations, repeated failures)
- Regularly audit permissions and remove inactive accounts
This significantly reduces the risk of unauthorized access through techniques like credential stuffing.
- Control and Validate Dependencies
Dependencies are one of the most common entry points for artifact poisoning.
- Use internal, curated repositories instead of direct public downloads
- Implement allowlists for approved packages and versions
- Regularly audit and update dependencies
- Prevent dependency confusion by enforcing strict source prioritization
This reduces the risk of pulling malicious or unintended components into your environment.
- Adopt a Zero Trust Approach for Artifacts
Trust should never be assumed, even for internal components.
- Treat every artifact as untrusted until verified
- Continuously validate artifacts at every stage (build, storage, deployment)
- Avoid implicit trust based on source or history
This mindset directly counters the core principle exploited in this type of supply chain attack.
Book Your Free Cybersecurity Consultation Today!
Conclusion
Artifact poisoning is a reminder that the modern software supply chain is built on layers of trust that can be silently exploited if left unverified. As enterprises continue to rely on open-source components, automated pipelines, and shared repositories, the attack surface expands beyond traditional security boundaries. What makes this type of attack particularly risky is its ability to embed itself within trusted workflows, scale rapidly across environments, and persist undetected for long periods.
To effectively defend against this threat, organizations must move beyond reactive security measures and adopt a proactive, zero-trust approach, where every artifact is validated, every dependency is scrutinized, and every stage of the development lifecycle is secured. In an ecosystem where software is assembled rather than built, ensuring the integrity of each component is no longer optional; it is essential for maintaining resilience and trust.
FAQs
- Can artifact poisoning impact production systems directly?
Yes, poisoned artifacts can reach production through automated deployment pipelines.
- How does artifact poisoning remain undetected?
It hides within trusted components and mimics legitimate application behavior.
- What role do CI/CD pipelines play in artifact poisoning?
They can unknowingly distribute compromised artifacts across environments.
- Are open-source dependencies a major risk factor?
Yes, heavy reliance on open-source increases exposure to poisoned components.
The post Artifact Poisoning: A Silent Threat to Enterprise Software Supply Chains appeared first on Kratikal Blogs.
*** This is a Security Bloggers Network syndicated blog from Kratikal Blogs authored by Shikha Dhingra. Read the original post at: https://kratikal.com/blog/artifact-poisoning-a-threat-to-enterprise-software-supply-chains/
如有侵权请联系:admin#unsafe.sh