嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要用“文章内容总结”之类的开头。我得先仔细阅读这篇文章,抓住主要信息。 文章主要讲的是英国国家网络安全中心(NCSC)警告称,与中国有关的黑客利用劫持的消费设备构建代理网络,隐藏他们的活动以逃避检测。这些设备包括路由器、摄像头、录像机和NAS系统。他们通过这些设备进行攻击,掩盖身份。 文章还提到这些网络被用于整个网络攻击链,从侦察到数据窃取。这种模式低成本、灵活且难以追踪。防御者面临“IOC灭绝”,因为威胁指标很快消失。NCSC和合作伙伴提供了指导,建议组织绘制和基准边缘设备流量,使用动态威胁过滤,并实施多因素认证等措施。 最后提到了一个名为Raptor Train的大型僵尸网络,由Flax Typhoon APT组织控制,自2020年以来感染了超过20万台设备。 总结时需要涵盖:中国关联的威胁行为者、利用消费设备构建代理网络、隐藏活动、逃避检测、僵尸网络如Raptor Train以及防御建议。 </think> 英国国家网络安全中心警告称,与中国有关的黑客利用劫持的消费设备构建代理网络,隐藏活动以逃避检测。这些网络由路由器、摄像头等设备组成,用于掩盖身份并进行攻击。该模式低成本且灵活,使防御面临挑战。 2026-4-24 06:58:13 Author: securityaffairs.com(查看原文) 阅读量:15 收藏
China-linked threat actors use consumer device botnets to evade detection, warn UK and partners

UK National Cyber Security Centre (NCSC) warns China-linked hackers use hijacked devices as proxy networks to hide activity and evade detection.
UK National Cyber Security Centre (NCSC) and global partners warn that China-linked threat actors now rely on large proxy networks built of hacked consumer devices. Groups control routers, cameras, video recorders, and NAS systems to route attacks and mask their identity. This shift replaces smaller, dedicated infrastructure with vast botnets that help them blend into normal traffic and avoid detection.
China-nexus cyber actors use these botnets across the full Cyber Kill Chain, from reconnaissance to data theft. This model gives them a low-cost, flexible, and deniable setup that they can quickly reshape, making static IP blocklists far less effective.
“Covert networks enable China-nexus actors to launch cyber attacks against UK organisations, stealing sensitive data and potentially disrupting critical services.
Because the covert networks are constantly refreshed and share nodes across multiple threat groups, defenders face “IOC extinction” – indicators of compromise disappear as quickly as they are discovered.” reads the advisory. “Consequently, organisations that rely solely on static defences risk being bypassed, while those that adopt adaptive, intelligence driven measures can better mitigate the risk.”
National Cyber Security Centre and partners, including the Cyber League, released guidance to counter covert network threats. They advise organisations of all sizes to map and baseline traffic from edge devices, especially VPN and remote access connections. They also recommend using dynamic threat feed filtering that includes indicators of compromised infrastructure to improve detection and reduce exposure to hidden attack networks.
“Potential victims should implement two-factor authentication for remote access and, where possible, apply zero trust controls, IP allow lists, and machine certificate verification.” continues the advisory. “Larger or high-risk entities should consider active hunting of suspicious SOHO/IOT traffic, geographic profiling, and machine learning based anomaly detection.”
National Cyber Security Centre explains that China-linked covert networks keep evolving, with new and updated infrastructures appearing regularly due to countermeasures, exploits, and technical changes.
“The number of covert networks used by China-nexus cyber actors is large, with new networks regularly developed and deployed.” reads the joint advisory. “The existing covert networks change too, either because of defensive or legal action, or simply as a result of software updates and new exploits being used to target different technologies for incorporation into the network.”
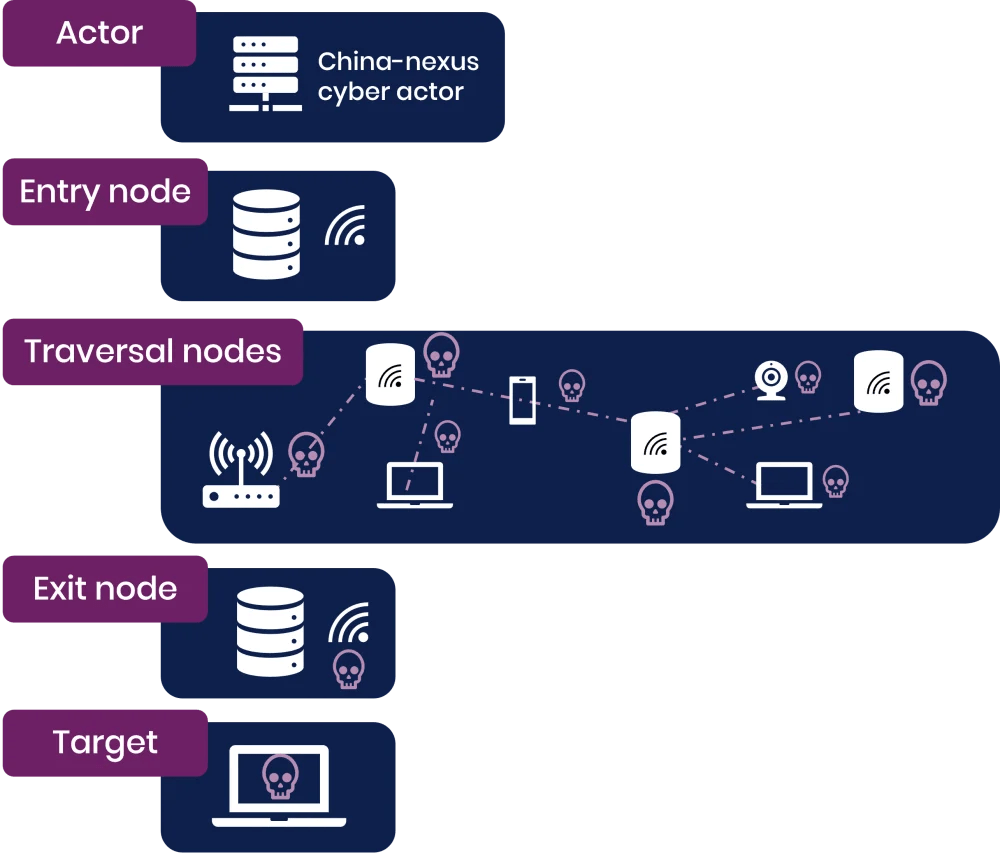
Because these networks change so often, full technical descriptions quickly become outdated and offer limited value for defenders. Still, most share a common structure: an operator enters through an on-ramp or entry node, then routes traffic across multiple compromised devices acting as traversal nodes, before exiting through an exit node that often sits near the target’s region. Understanding this basic flow helps defenders identify where they sit in the chain and improve detection and response strategies against these dynamic proxy-based networks.
NCSC provides tailored guidance to defend against covert networks built from compromised devices. It explains that defending these attacks requires layered strategies based on an organisation’s size and risk level, and it does not eliminate all risk.
All organisations should map internet-facing assets, baseline normal traffic, especially VPN and remote connections, and use dynamic threat feeds that include covert infrastructure indicators. They should also deploy multi-factor authentication and consider tools like the Cyber Action Toolkit and Cyber Essentials.
Higher-risk organisations should strengthen controls with IP allow lists, geographic and behavioural filtering, zero trust models, SSL machine certificates, and reduced internet exposure. They should also explore anomaly detection using machine learning.
The largest or most exposed organisations should actively hunt for signs of covert networks, track known infrastructure using threat intelligence, analyse NetFlow data, and integrate dynamic blocklists and alerts. For critical sectors, the Cyber Assessment Framework supports advanced defensive maturity.
Federal Bureau of Investigation reports describe large China-linked botnets, such as Raptor Train, used for state-aligned cyber activity. In September 2024, researchers from Lumen’s Black Lotus Labs discovered the Raptor Train botnet, composed of small office/home office (SOHO) and IoT devices. The experts believe the botnet is controlled by the China-linked APT group Flax Typhoon (also called Ethereal Panda or RedJuliett). The botnet has been active since at least May 2020, reaching its peak with 60,000 compromised devices in June 2023.
Since May 2020, over 200,000 devices, including SOHO routers, NVR/DVR devices, NAS servers, and IP cameras, have been compromised and added to the Raptor Train botnet, making it one of the largest China-linked IoT botnets discovered.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, China)
如有侵权请联系:admin#unsafe.sh
