嗯,用户让我帮忙总结一篇文章的内容,控制在100个字以内,而且不需要用“文章内容总结”这样的开头。我得先仔细阅读这篇文章,理解它的主要观点。 文章讲的是AirSnitch攻击,这是一种新型的攻击技术,可以绕过Wi-Fi加密和客户端隔离机制。这些攻击利用了协议和基础设施之间的安全漏洞,影响了WPA2和WPA3-Enterprise等标准。主要影响包括企业数据泄露、敏感凭证暴露以及后端系统被攻击的风险。 接下来,我需要将这些关键点浓缩到100字以内。首先提到AirSnitch攻击,然后说明它们如何绕过加密和隔离机制,接着指出影响的范围和潜在风险。最后,可能还要提到缓解措施或建议。 确保语言简洁明了,不使用复杂的术语,让读者一目了然。检查字数是否在限制内,并调整句子结构以优化表达。 </think> AirSnitch攻击揭示了Wi-Fi加密和客户端隔离机制的漏洞,可绕过WPA2/WPA3-Enterprise保护,导致企业数据泄露风险增加。 2026-4-22 10:0:22 Author: unit42.paloaltonetworks.com(查看原文) 阅读量:18 收藏
Executive Summary
Enterprises have long trusted Wi-Fi encryption and client isolation to secure their wireless infrastructure. However, we conducted research presented at the NDSS Symposium 2026 that reveals that these safeguards can be breached by a novel set of attack techniques that we call AirSnitch. These techniques exploit subtle security issues in protocol-infrastructure interactions to undermine the security guarantees offered by standard protocols like WPA2 and WPA3-Enterprise.
Due to the widespread adoption of these protocols, the impact is industry-wide, affecting Wi-Fi devices from several major vendors. Major operating systems, including Android, macOS, iOS, Windows and Ubuntu Linux, also rely on these protocols.
WPA2 and WPA3-Enterprise protocols authenticate and encrypt most global IEEE 802.11 wireless traffic. They act as the primary cryptographic barrier for legacy cleartext application-layer protocols (e.g., DNS, HTTP), preventing unauthorized packet interception at the data link layer (Layer 2) of the OSI model.
However, AirSnitch breaks this barrier. Unlike more commonly known threats, AirSnitch focuses on exploiting the wireless infrastructure itself rather than just client devices, fundamentally shifting our assumptions of wireless security. By subverting how networks handle low-level states (e.g., the MAC address table), attackers can break client isolation to intercept traffic or inject packets, completely bypassing Wi-Fi encryption.
This creates a critical risk to enterprise data confidentiality, potentially exposing sensitive credentials and backend systems to both malicious insiders and external over-the-air attackers. These security issues exist within the core logic of how Wi-Fi handles data. As a result, they represent a fundamental security gap that undermines protections across all Wi-Fi encryption standards, from the original WEP algorithm to modern WPA2/3 protection. This security gap stems from two primary factors: some attacks, such as Port Stealing, exploit fundamental Wi-Fi design errors that are difficult or impossible to patch within the existing protocol standards, necessitating the conservative treatment of these protocols as inherently insecure. Additionally, other exploits, like Gateway Bouncing, rely on diverse, organization-specific network configurations, making universal vendor testing and coordinated responsible disclosure impractical. Therefore, these findings are being released publicly to accelerate threat mitigation and security improvement across all impacted enterprises.
Importantly, AirSnitch also serves as a foundational building block for more sophisticated higher-layer attacks. By compromising the integrity of the lower protocol layers, an attacker can launch complex exploits against the upper protocol layers that were previously thought to be shielded by WPA.
Our research on AirSnitch leads us to urge the Wi-Fi industry to adopt rigorous, standardized security for complex modern Wi-Fi networks.
To counter these pervasive risks within individual organizations, security professionals must move beyond the assumption that WPA2/3-Enterprise provides robust protection. This article provides a concise overview of the attack mechanisms and offers actionable mitigation steps. Key defense steps include implementing robust network segmentation, enhancing spoofing prevention and updating firewall configurations to protect the integrity of both wired and wireless enterprise environments.
If you think you might have been compromised or have an urgent matter, contact the Unit 42 Incident Response team.
| Related Unit 42 Topics | Network Security, MitM |
The AirSnitch Threats: A New Security Paradigm
For years, the standard Wi-Fi threat model focused on an attacker targeting a single device or a specific network segment (e.g., basic service set identifier (BSSID)/service set identifier (SSID)). AirSnitch attacks challenge this assumption with a more multifaceted approach. These attacks:
- Operate across different wireless network segments (basic service set (BSS))
- Engage multiple access points (APs)
- Can collude with malicious remote servers.
AirSnitch attacks exploit security issues across Wi-Fi encryption, switching and routing layers. These attacks manipulate underlying network states such as interface port (OSI Layer 1) mappings, to bypass Wi-Fi client isolation and encryption.
Unlike previous styles of attacks (e.g., address resolution protocol (ARP) poisoning), AirSnitch works at even lower networking layers and restores meddler-in-the-middle (MitM) capabilities in current Wi-Fi networks. This effectively breaks the security perimeter that enterprises rely on, making even a properly configured WPA2/3-Enterprise network vulnerable to insider and outsider threats.
The threat model in AirSnitch differs from a typical Wi-Fi threat model, where a wireless attacker tries to compromise a single SSID/BSSID. AirSnitch takes into consideration all possible sources of attacks, and even how different attackers cooperate to inject or leak wireless traffic protected by WPA2/3.
As shown in Figure 1, an attacker can:
- Deliver frames directly over the air to the victim (①)
- Attempt to inject packets to the victim through the same AP (②)
- From within the network (③)
- Through a different AP (④)
- Launch attacks from the internet (⑤)
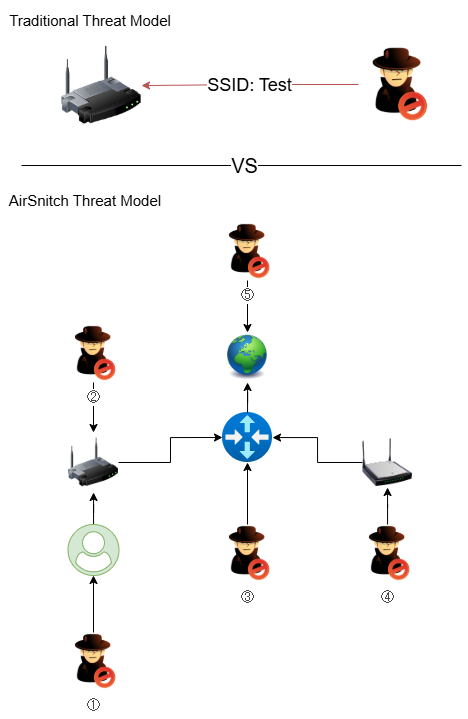
AirSnitch is the first public research to propose all five attack channels.
The Anatomy of AirSnitch Attacks: Starting With Wi-Fi Fundamentals
AirSnitch attacks circumvent standard Wi-Fi security by exploiting weaknesses in the interplay between encryption, switching and routing layers, despite WPA2/3 encryption being designed to secure over-the-air traffic. Below, we begin by analyzing Wi-Fi fundamentals to demonstrate how WPA2/3 can be broken.
Injecting and Decrypting Packets by Misusing Shared Keys
In the classic WPA four-way handshake, a client blends AP and client randomness (i.e., nonces exchanged over the air) with the Pairwise Master Key (PMK) to derive the unicast session's Pairwise Transient Key (PTK). In WPA2-Personal, the client PMK is derived from the Wi-Fi passphrase. Thus, for WPA2-Personal networks, possession of a shared passphrase (common in public settings like restaurants and coffee shops) allows a meddler-on-the-side attacker to derive session keys, just as legitimate clients do. This allows an attacker to passively decrypt and inject traffic, breaking client isolation.
Due to the Dragonfly handshake added right before the four-way handshake, meddler-on-the-side attacks are no longer effective for the WPA3-Personal protocol. However, if attackers know the WPA3 passphrase, they can still set up a fake or cloned WPA3-Personal AP and then lure clients to this cloned AP. This would allow them to bypass client isolation on real APs to capture victim traffic. These attack methods reveal that keeping WPA2/3-Personal passphrases confidential is key to enforcing Wi-Fi client isolation.
The WPA four-way handshake also distributes the AP Group Temporal Key (GTK) to clients under the same BSSID, according to the Wi-Fi standard. The purpose of distributing GTK is to enable broadcast/multicast communications. However, we found that even for WPA2/WPA3-Enterprise networks, an insider attacker can misuse the shared GTK to wrap unicast IP traffic inside broadcast/multicast frames encrypted with the GTK. This enables an attacker to inject packets directly to victims, bypassing client isolation on target enterprise APs.
To better illustrate this, Figure 2 shows that, as a symmetric key, GTK is always shared between WPA clients and the AP. It is also distributed to clients during the classical WPA four-way handshake. Normally, client operating systems are responsible for managing this GTK. Normal applications won’t (and shouldn’t) know this shared GTK.
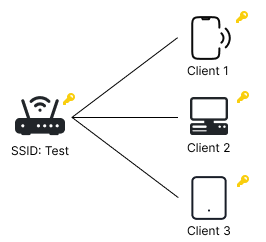
However, the publicly available AirSnitch tool intentionally extracts this GTK by modifying the internal workings of wpa_supplicant, an open-source Wi-Fi client. As a result, a malicious client can bypass OS restrictions and obtain GTKs. After this, the attacker can spoof broadcast/multicast frames like APs do, by encrypting spoofed frames with GTK.
While some security-aware implementations enforce per-client GTKs to prevent shared GTKs and maximize isolation, certain Wi-Fi standard handshakes (group key, FT, FILS, WNM-Sleep) still expose the real GTK. Moreover, Integrity GTKs (IGTKs, another shared group key for management purposes) are never randomized. This enables an attacker to choose a GTK for a victim to use, also enabling packet injections. For a more in-depth analysis of these techniques within the Wi-Fi standard, you can refer to our academic publication.
The Broader Context of Wi-Fi Client Isolation
To further understand how AirSnitch bypasses client isolation, it's important to grasp the broader context of Wi-Fi client isolation. Client isolation is a set of mechanisms designed to block direct communication between clients on the same Wi-Fi network. However, client isolation is not a standardized feature of the IEEE 802.11 standards, leading to unclear security guarantees.
Our research identifies four typical, yet often flawed, mechanisms used for client isolation:
- Wi-Fi encryption protocols (e.g., WEP, TKIP, CCMP, GCMP) are intended to prevent decryption of other clients' over-the-air traffic. For example, Wi-Fi encryption protocols prevent one mobile client from directly monitoring another's cleartext wireless traffic over the air. Such encryption also protects important unencrypted protocols, including HTTP and DNS.
- Intra-BSSID isolation drops frames that are sent directly between clients on the same BSSID. In most AP configurations and the open-source hostapd Wi-Fi daemon, this is referred to as ap_isolate=1.
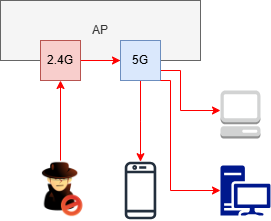
- Inter-BSSID isolation blocks traffic between clients on different BSSIDs within the same network. For instance, ideally, a 2.4GHz BSSID of a Wi-Fi AP should not connect internally to a 5GHz BSSID on the same AP to provide robust client isolation. However, our research shows this is often not the case.
- Guest network configurations assign untrusted clients to separate, restricted SSIDs, forcing them to use guest credentials to connect. However, these often fail to provide complete isolation. For example, many enterprises often deploy guest SSIDs with no encryption at all (i.e., Open System authentication), or weak encryption (i.e., passphrase authentication), along with WPA2/3-Enterprise for privileged employees. We show that those guest SSIDs, without sound client isolation, might allow attackers to harm privileged employees’ WPA2/3-Enterprise connections.
The core issue is that many vendors only implement a subset of these mechanisms, or they implement them incorrectly. For example, isolation might be enforced at the MAC layer (OSI Layer 2, with ap_isolate=1) but not the IP layer (OSI Layer 3), creating a bypass with “Gateway Bouncing” as we illustrate below.
One Step Further: Dissection of Selected Novel MitM Primitives in AirSnitch
AirSnitch introduces several novel MitM primitives that exploit the often incomplete client isolation. We illustrate three of them:
- Gateway bouncing
- Port stealing
- Broadcast reflection
Gateway Bouncing
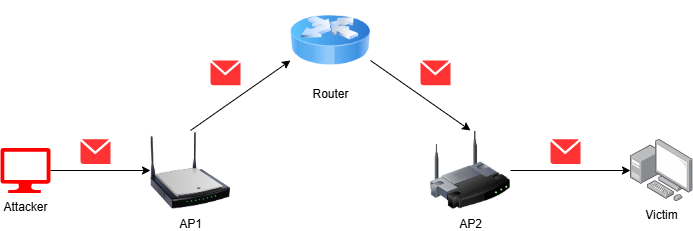
Attacks can use gateway bouncing to exploit the failure to enforce isolation at the IP layer in home and enterprise networks. An attacker sends a packet with the victim's Layer 3 IP address as the destination but uses the network gateway's MAC address as the Layer 2 destination. The AP accepts and forwards the packet to the gateway, which then routes it to the victim. This process effectively bypasses Layer 2 isolation, such as ap_isolate=1 in hostapd on Wi-Fi APs.
As shown in Figure 3, even with ap_isolate=1 enabled on both AP1 and AP2, AP1 forwards the injected packet because it sees the router as the Layer 2 destination. The router then identifies the packet's IP destination address on the AP2 side and bounces the packet to AP2, ultimately reaching the victim.
Port Stealing
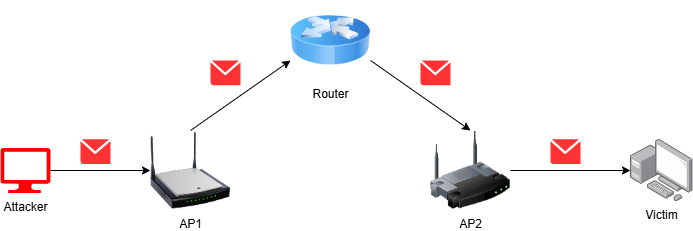
An attacker can use port stealing to spoof a victim's MAC address toward a different BSSID of the same AP (see Figure 4 below), or toward a separate AP within the same wireless/wired infrastructure.
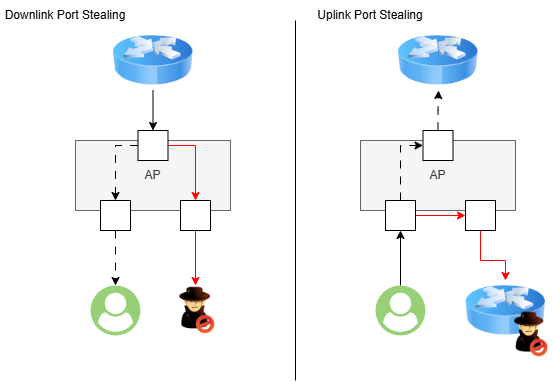
The network's internal switches or APs will then mistakenly update their forwarding tables (i.e., Layer 1 interface port-to-MAC-address mappings), associating the victim's MAC address with the BSSID the attacker is exploiting. As a result, all traffic meant for the victim is redirected to the attacker's device and encrypted with the attacker's session key (i.e., PTK). This is also effective for hijacking uplink traffic by spoofing the MAC address of the gateway itself toward the wireless AP.
- Importantly, without inter-BSSID isolation on a target AP, an attacker can spoof the gateway MAC address on a different BSSID. This allows them to intercept the first RADIUS/UDP authentication packet generated by the victim’s AP daemon. This allows an attacker to brute force and learn the victim's BSSID’s RADIUS secret, further compromising enterprise Wi-Fi security.
- Wi-Fi port stealing compromises Wi-Fi security at a networking layer below ARP, operating between the physical layer (Layer 1) and the data link layer (Layer 2). This means that all unencrypted networking protocols carried by Wi-Fi, such as ARP, DNS, TCP and HTTP, can fall victim to Wi-Fi port stealing. Even encrypted protocols like TLS can expose IP addresses through port stealing.
Broadcast Reflection
Broadcast reflection is a subtle injection method that bypasses the need for an attacker to know or predict the GTK. The attacker crafts a Wi-Fi frame that looks like a broadcast but contains a unicast IP layer payload for the victim. Upon receiving the broadcast frame, the AP re-encrypts it with the GTK associated with the victim's BSSID and broadcasts it to all clients, including the victim. This allows the attacker to inject traffic from a completely separate BSSID, without knowing the GTK for a target BSSID (see Figure 5 below).
Our full paper also introduces other techniques that facilitate the manipulation of low-level port states within the target Wi-Fi network. As a result, an attacker can actively decrypt WPA2/3-Enterprise traffic and become a MitM, intercepting bi-directional traffic (i.e., both to and from a Wi-Fi client).
Putting It Together: Chaining Primitives, Executing Cross-AP Attacks and Enabling Higher-Layer Attacks
A key insight of our AirSnitch research is its demonstration of combining different attack primitives into MitM attack chains. For example, an attacker might first use port stealing to intercept downlink traffic meant for a victim, and then apply GTK misuse to directly inject those stolen frames over the air to the victim.
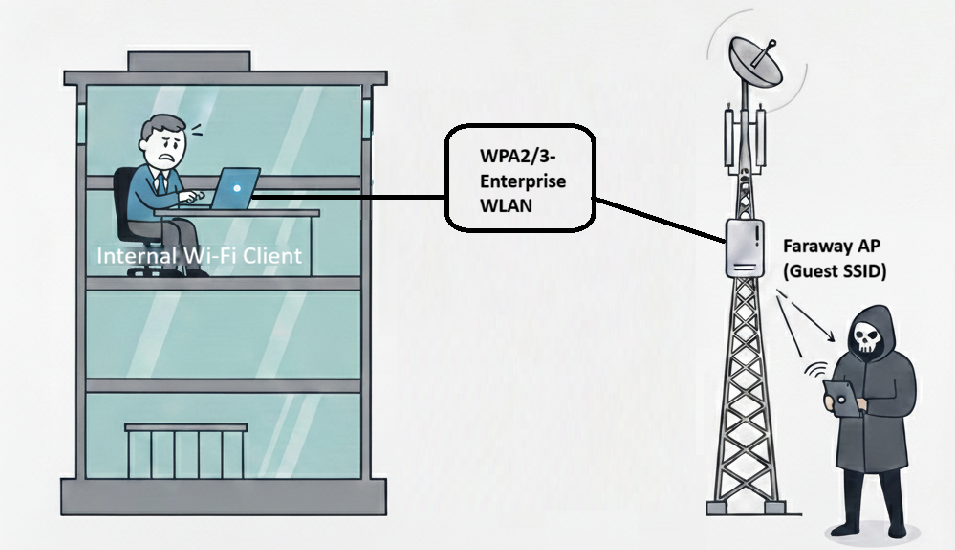
Our research even reveals the possibility of cross-AP attacks. In this scenario, the attacker targets a Wi-Fi AP located at a different physical location than the victim to leak traffic belonging to the victim. This escalates the threat beyond traditional local attacks, as it breaks the assumption that physically separate APs provide effective isolation.
By hijacking MAC-to-port mappings at the distribution switch level (i.e., internal wired switches of enterprise networks), an attacker can manipulate traffic across AP boundaries even if those APs are broadcasting different network names (SSIDs). For example, Figure 6 shows that without strict isolation, an attacker could exploit a faraway AP’s guest SSID to steal WPA2/3-Enterprise traffic belonging to a client located inside an office building.
Once an attacker establishes a bi-directional MitM through these methods, they can facilitate higher-layer attacks that were previously thought impractical in isolated networks. These possibilities include:
- Rogue enterprise APs: In enterprise settings, attackers can steal RADIUS packets to brute force RADIUS authentication passphrases, eventually setting up rogue enterprise access points to harvest secret data.
- Traffic decryption: Attackers can exploit vulnerabilities in unpatched Datagram TLS (DTLS) implementations to decrypt HTTPS connections and compromise sensitive user data. Wi-Fi port stealing also serves as a powerful primitive to more sophisticated attacks, such as traffic analysis.
- Address poisoning: By decrypting Wi-Fi, an adversary can perform DNS or DHCP poisoning, modifying gateway addresses or poisoning ARP caches to maintain long-term control over the victim's traffic.
How to Mitigate the AirSnitch Attacks for Enterprise Wi-Fi Networks
To protect against AirSnitch attacks, enterprises must move beyond simple, vendor-specific client isolation settings and adopt a more holistic security approach.
We suggest a simple security checklist before introducing more specialized solutions:
- Does your enterprise strictly separate guest SSIDs from WPA2/3-Enterprise SSIDs on Wi-Fi APs?
- Does your enterprise ever use firewall policies in core networks to provide network isolation between guest Wi-Fi and WPA2/3-Enterprise, and block attacks including gateway bouncing?
- Does your enterprise use weak RADIUS passphrases on Wi-Fi APs?
- Does your enterprise update endpoint operating systems to newer, patched versions?
- Does your enterprise use robust, secure virtual private network (VPN) solutions for even intranet access?
- Does your enterprise harbor legacy or orphaned APs that remain physically uplinked to the core network despite being phased out of active management?
Our AirSnitch research also suggests more specialized solutions to nullify the attacks:
- Improve network isolation with virtual local area networks (VLANs). Implement VLANs to logically separate network segments. Placing untrusted BSSIDs (e.g., guest networks) in their own VLAN prevents an attacker from launching port-stealing attacks to redirect traffic from a trusted network.
- Implement spoofing prevention.
- MAC spoofing: Configure APs to prevent a single MAC address from being used on multiple BSSIDs simultaneously. This feature, seen on certain devices, directly prevents the cross-BSSID port-stealing attacks.
- IP spoofing: Enable IP spoofing prevention to block traffic where the source IP address does not belong to the sender. This defense can stop gateway bouncing by preventing the attacker from injecting packets that appear to originate from an external server.
- Enhance group key security. You can stop GTK misuse attacks by configuring APs to use per-client randomized GTKs. The Passpoint (Hotspot 2.0) specification includes a mechanism called downstream group-addressed forwarding (DGAF), which allows access points to control or disable forwarding of multicast/broadcast traffic to clients. This is important because such traffic typically relies on a shared group key (GTK), that could introduce potential attack vectors. By disabling downstream group-addressed forwarding, APs can prevent these risks and, in some implementations, convert essential group traffic into unicast transmissions per client. Examine whether your enterprise APs support these options.
- Adopt device-to-device encryption. For better security, use a protocol like MACsec (IEEE 802.1AE). MACsec establishes secure, end-to-end encryption at the link layer between devices. This ensures that even if an attacker manages to intercept traffic, they cannot read or tamper with it. At most, they can cause a denial of service. This option is available on Linux distributions like Ubuntu.
Conclusion
The AirSnitch attacks illustrate a fundamental fact about modern Wi-Fi networks. Client isolation, as currently implemented, is an inconsistent and unreliable defense.
The lack of standardization has led to ad hoc and incomplete solutions that fail to protect against sophisticated insider and outsider threats. By exploiting security issues across the encryption, switching and routing layers, an attacker can achieve a full MitM position, even in enterprise-grade networks. Our research on AirSnitch leads us to urge the Wi-Fi industry to adopt rigorous, standardized security for complex modern Wi-Fi networks.
If you think you may have been compromised or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
- North America: Toll Free: +1 (866) 486-4842 (866.4.UNIT42)
- UK: +44.20.3743.3660
- Europe and Middle East: +31.20.299.3130
- Asia: +65.6983.8730
- Japan: +81.50.1790.0200
- Australia: +61.2.4062.7950
- India: 000 800 050 45107
- South Korea: +82.080.467.8774
Palo Alto Networks has shared these findings with our fellow Cyber Threat Alliance (CTA) members. CTA members use this intelligence to rapidly deploy protections to their customers and to systematically disrupt malicious cyber actors. Learn more about the Cyber Threat Alliance.
Indicators of Compromise
- Unexpected changes in MAC address-to-port mappings within the AP's forwarding table
- Detection of an attacker device with a spoofed MAC address of a legitimate client or gateway
- High volume of multicast/broadcast frames containing unexpected unicast payloads, especially from internal Wi-Fi clients
- Unexpected re-negotiation of session keys or GTK updates outside of standard periodic intervals
Additional Resources
- AirSnitch: Demystifying and Breaking Client Isolation in Wi-Fi Networks - Network and Distributed System Security (NDSS) Symposium
如有侵权请联系:admin#unsafe.sh