
嗯,用户让我用中文总结这篇文章,控制在一百个字以内,而且不需要特定的开头。首先,我需要通读整篇文章,抓住主要信息。 文章讲的是美国网络安全和基础设施安全局(CISA)警告说,一个严重的Apache ActiveMQ漏洞CVE-2026-34197被积极利用。这个漏洞存在了13年,最近被修复。攻击者可以利用它执行任意代码。CISA要求联邦机构在两周内修补漏洞,并建议私营部门也尽快处理。 接下来,我需要把这些要点浓缩到100字以内。要确保包括:CISA警告、漏洞名称、存在时间、攻击方式、修复情况、影响范围以及建议措施。 可能会这样组织句子:CISA警告称,Apache ActiveMQ的严重漏洞CVE-2026-34197被积极利用。该漏洞未被检测13年,允许认证攻击者执行任意代码。CISA要求联邦机构两周内修补,并建议私营部门优先处理。 检查一下字数是否在限制内,并且没有使用不需要的开头。 </think> CISA警告Apache ActiveMQ严重漏洞CVE-2026-34197被积极利用。该漏洞未被检测13年,允许认证攻击者执行任意代码。CISA要求联邦机构两周内修补,并建议私营部门优先处理。 2026-4-17 09:46:58 Author: www.bleepingcomputer.com(查看原文) 阅读量:32 收藏
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned on Thursday that a high-severity Apache ActiveMQ vulnerability patched earlier this month is now actively exploited in attacks.
Apache ActiveMQ is the most popular open-source Java-based message broker for asynchronous communication between applications.
Tracked as CVE-2026-34197, the security flaw has gone undetected for 13 years and was discovered by Horizon3 researcher Naveen Sunkavally using the Claude AI assistant.
Sunkavally explained that the vulnerability stems from improper input validation, which allows authenticated threat actors to execute arbitrary code via injection attacks. The Apache maintainers patched the vulnerability on March 30in ActiveMQ Classic versions 6.2.3 and 5.19.4.
"We recommend organizations running ActiveMQ treat this as a high priority, as ActiveMQ has been a repeated target for real-world attackers, and methods for exploitation and post-exploitation of ActiveMQ are well-known," Horizon3 warned.
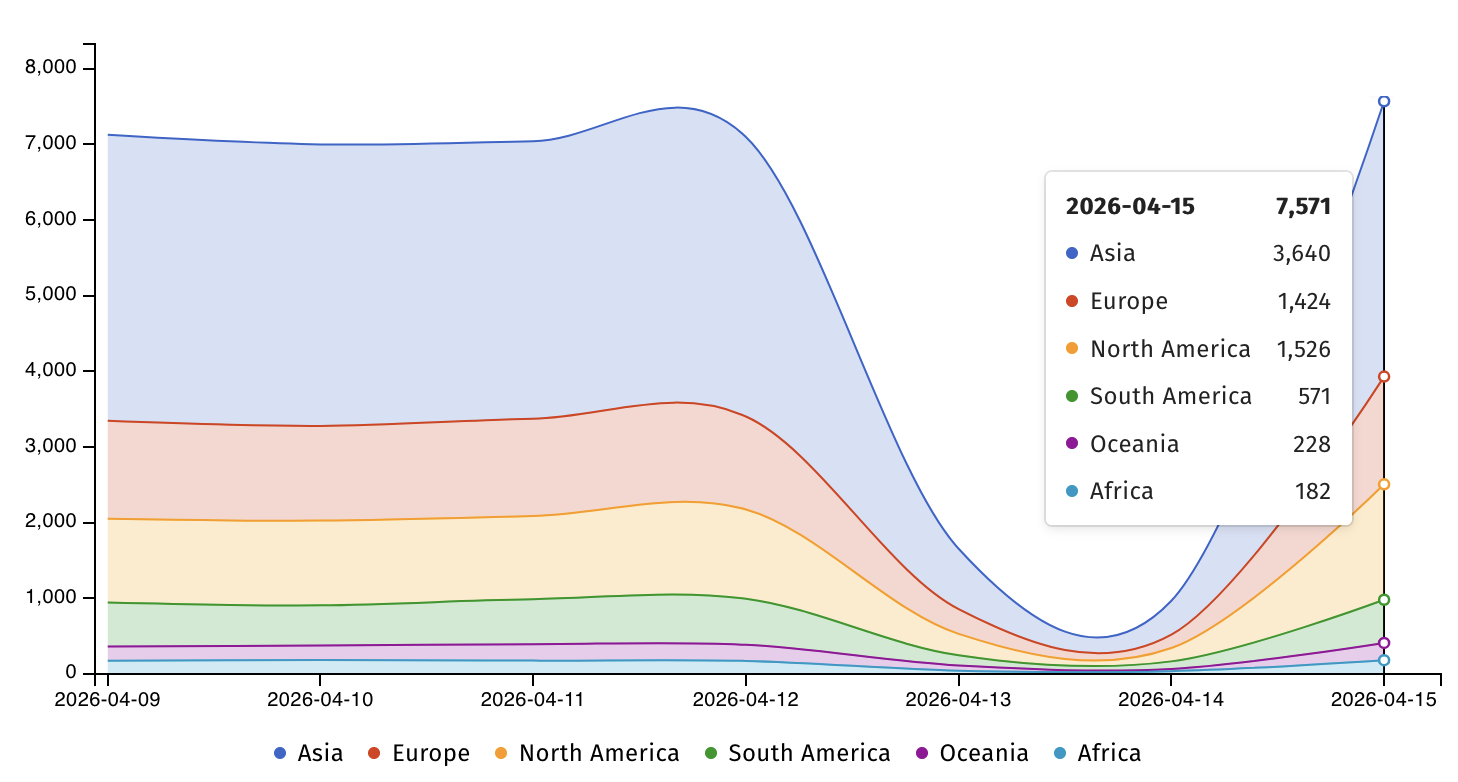
Threat monitoring service ShadowServer is currently tracking more than 7,500 Apache ActiveMQ servers exposed online.
On Thursday, CISA added CVE-2026-34197 to its Known Exploited Vulnerabilities (KEV) Catalog and ordered Federal Civilian Executive Branch (FCEB) agencies to patch ActiveMQ servers within two weeks, by April 30, as mandated by Binding Operational Directive (BOD) 22-01.
Horizon3 researchers said that signs of exploitation can be found by analyzing the ActiveMQ broker logs and recommended looking for suspicious broker connections that use the brokerConfig=xbean:http:// query parameter and the internal transport protocol VM.
"This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," the cybersecurity agency warned.
"Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable."
It also urged private-sector defenders to prioritize patching for CVE-2026-35616 and to secure their organizations' networks as soon as possible, even though BOD 22-01 applies only to U.S. federal agencies.
Previously, CISA tagged two other Apache ActiveMQ vulnerabilities as exploited in the wild, tracked as CVE-2023-46604 and CVE-2016-3088, with the former targeted by the TellYouThePass ransomware gang as a zero-day flaw.
99% of What Mythos Found Is Still Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what's exploitable, proves controls hold, and closes the remediation loop.
如有侵权请联系:admin#unsafe.sh

