
好的,我现在需要帮用户总结一篇文章,控制在100字以内。首先,我得通读整篇文章,抓住主要观点。 文章主要讨论的是现代网络应用的安全问题,特别是浏览器层的供应链风险。传统安全工具如SAST、DAST、WAF等无法覆盖浏览器中的第三方脚本执行情况,导致攻击者有机可乘。 接下来,我需要找出关键点:浏览器层的漏洞、第三方依赖的风险、传统工具的不足以及监管压力。然后,将这些点浓缩成简洁的句子。 还要注意不要使用“文章内容总结”这样的开头,直接描述内容。最后检查字数,确保在100字以内。 </think> 现代网络应用的安全风险集中在浏览器层的第三方依赖和供应链漏洞上。传统安全工具无法覆盖浏览器中动态执行的代码,导致攻击者通过妥协第三方脚本或数据窃取等方式入侵。企业需加强浏览器层的实时监控和数据流分析,以应对日益严格的监管要求和供应链风险。 2026-4-16 04:18:58 Author: securityboulevard.com(查看原文) 阅读量:17 收藏
Right now, code is executing in your users’ browsers that your WAF has never inspected, your DAST never tested, and your pen testers never touched. It’s not a gap in your tools, it’s a gap in where those tools look. And attackers have already found it.
● SAST and DAST to secure code
● EASM to identify exposed assets
● WAFs and bot mitigation to protect applications
● Regular penetration testing to validate risk
These controls have done their job well. But the application has moved. More of it now runs in the browser, shaped by a constantly changing ecosystem of third and fourth-party dependencies that these tools were never designed to see.
In many environments, this browser layer remains largely unmeasured. That is where web supply chain risk lives, and it is the front line security teams can no longer afford to ignore.
The Expansion of the Attack Surface
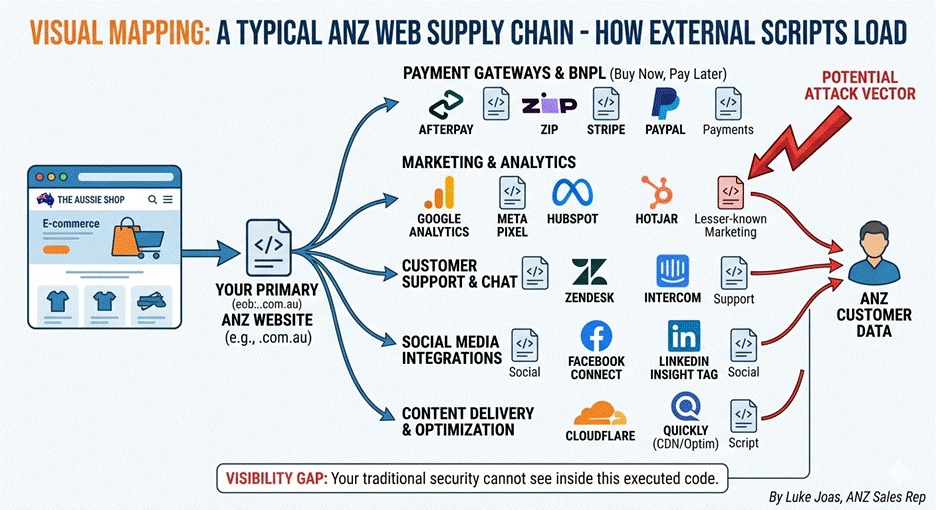
To support modern development and release cycles, applications rely heavily on a network of third and fourth-party technologies. Each introduces code that executes directly in the user’s browser, code the organisation did not write and often cannot see. Reflectiz research across 4,700 websites found that 64% of third-party applications access sensitive data without a clear business justification. Common examples include:
● Tag managers and marketing platforms
● Analytics and tracking technologies
● Embedded services and integrations
● Payment providers (e.g., Afterpay, Zip, Stripe)
The problem is not the vendors themselves, it is the lack of visibility into what they are actually doing at runtime.
Where Traditional Visibility Breaks Down
Most organisations have a clear view of what they build and deploy, but far less understanding of what actually executes in a real user session.
| Control | What it Sees | The “Browser Gap” (What it Misses) |
| SAST & DAST | First-party source code. | Runtime behavior of third-party scripts. |
| EASM | External IP assets and domains. | In-browser data interactions and data skimming. |
| WAF | Incoming traffic patterns. | Malicious logic running inside the browser. |
| Pen-Testing | A point-in-time snapshot. | Real-time changes in the third-party ecosystem. |
These controls operate outside the browser layer. The result is a gap between known vendors and actual runtime dependencies, and that is exactly where web supply chain risk sits.
The Rise of Web Supply Chain Risk in ANZ
This gap is becoming more critical as attackers move away from hardened infrastructure toward:
● Third-party script compromise
● Dependency hijacking
● Data exfiltration through browser-executed code
This is not theoretical. High-profile web skimming attacks, including incidents affecting major airlines, ticketing platforms, and retail brands globally, followed exactly this pattern: attackers compromised a trusted third-party script, injected malicious code into payment flows, and exfiltrated card data for months before detection. Traditional controls generated no alerts, because the attack never touched the infrastructure those controls monitor.
The Regulatory Stake
In Australia, the stakes have never been higher. The OAIC is increasingly focusing on how data is collected and handled in the browser. As outlined in Reflectiz’s analysis, misconfigured trackers can expose sensitive user data, with potential penalties reaching up to AUD $50 million or more.
Organisations are now strictly accountable for:
- What data is collected in the browser.
- Whether that aligns with user consent.
- Exactly where that data is being sent.
From Visibility to Context: The Next Phase of Attack Surface Management
Knowing what assets you have is no longer enough. The question security teams need to answer is: what are those assets doing? For web applications, that question cannot be answered from outside the browser. It requires continuous observation of what scripts are executing, what data they are touching, and where that data is going, in real user sessions, not synthetic scans.
This is the gap that Continuous Threat Exposure Management (CTEM) frameworks are designed to close, and the browser is where that gap is most acute for organisations operating modern web applications.
Bringing the Browser into Scope
ANZ organisations are already navigating this. Village Roadshow needed visibility across hundreds of client-side scripts to demonstrate PCI DSS compliance, a requirement that cannot be met by server-side tools alone. Lion faced the challenge of managing browser-side risk across a complex, distributed environment spanning multiple brands and teams. In both cases, the answer started with getting visibility into what was actually running in the browser.
To manage the web supply chain in practice, you must be able to:
● Continuously observe script execution across key user journeys.
● Identify when script behaviour changes in meaningful ways.
● Map data flows across third and fourth-party dependencies.
Final Thought
Modern web applications run on a shadow supply chain, dozens of third and fourth-party scripts executing in real user sessions, largely invisible to conventional security controls. The organisations that close this gap will not just reduce risk; they will be better positioned to meet the compliance and privacy obligations that regulators are increasingly enforcing. The ones that don’t are operating with an unknown variable at the heart of their application risk. It’s time to bring the browser into scope.

Luke Joas leads ANZ for Reflectiz, helping Australian and New Zealand enterprises secure their web supply chains and stay ahead of evolving privacy regulations. Reflectiz recently opened its Sydney office at Level 13, 333 George Street. Luke welcomes a conversation — reach him at [email protected].
The post Web Supply Chain Risk in ANZ: Why the Browser is the New Front Line appeared first on Reflectiz.
*** This is a Security Bloggers Network syndicated blog from Cybersecurity Blog: News, Insights and Research – Reflectiz authored by Luke Joas. Read the original post at: https://www.reflectiz.com/blog/supply-chain-anz/
如有侵权请联系:admin#unsafe.sh