
好的,我现在需要帮用户总结这篇文章的内容。用户的要求是用中文,控制在一百个字以内,不需要特定的开头,直接写描述。 首先,我仔细阅读了文章。文章主要讲的是Marimo这个开源Python笔记本平台被黑客利用了一个关键漏洞。这个漏洞是在公开披露后10小时内被利用的,允许远程代码执行,没有身份验证。漏洞编号是CVE-2026-39987,评分为9.3分。 接下来,研究人员提到攻击者迅速创建了利用工具,并开始窃取敏感信息。Marimo是一个数据科学家常用的工具,用户量很大。漏洞是由于WebSocket端点没有正确验证身份导致的。 文章还提到Marimo在4月8日披露了这个漏洞,并在几天后发布了修复版本0.23.0。攻击者在披露后的短时间内就开始活动,窃取凭证和SSH密钥。 最后,建议用户升级到新版本,并采取其他安全措施。 现在我需要把这些信息浓缩到100字以内。要突出关键点:Marimo平台、远程代码执行漏洞、迅速被利用、影响范围、修复建议。 可能的结构:Marimo平台被黑客攻击,利用了关键漏洞,在披露后很快被利用,导致敏感信息泄露。建议升级和限制访问。 检查一下字数是否符合要求。确保信息准确且简洁。 </think> Marimo开源Python笔记本平台曝出关键漏洞CVE-2026-39987,允许未认证远程代码执行。该漏洞在披露10小时内即被利用,攻击者窃取敏感信息并提取凭证。建议用户升级至最新版本并限制访问以缓解风险。 2026-4-12 14:31:39 Author: www.bleepingcomputer.com(查看原文) 阅读量:13 收藏

Hackers started exploiting a critical vulnerability in the Marimo open-source reactive Python notebook platform just 10 hours after its public disclosure.
The flaw allows remote code execution without authentication in Marimo versions 0.20.4 and earlier. It tracked as CVE-2026-39987 and GitHub assessed it with a critical score of 9.3 out of 10.
According to researchers at cloud-security company Sysdig, attackers created an exploit from the information in the developer's advisory and immediately started using it in attacks that exfiltrated sensitive information.
Marimo is an open-source Python notebook environment, typically used by data scientists, ML/AI practitioners, researchers, and developers building data apps or dashboards. It is a fairly popular project, with 20,000 GitHub stars and 1,000 forks.
CVE-2026-39987 is caused by the WebSocket endpoint ‘/terminal/ws’ exposing an interactive terminal without proper authentication checks, allowing connections from any unauthenticated client.
This gives direct access to a full interactive shell, running with the same privileges as the Marimo process.
Marimo disclosed the flaw on April 8 and yesterday released version 0.23.0 to address it. The developers noted that the flaw affects users who deployed Marimo as an editable notebook, and those who expose Marimo to a shared network using --host 0.0.0.0 while in edit mode.
Exploitation in the wild
Within the first 12 hours after the vulnerability details were disclosed, 125 IP addresses began reconnaissance activity, according to Sysdig.
Less than 10 hours after the disclosure, the researchers observed the first exploitation attempt in a credential theft operation.
The attacker first validated the vulnerability by connecting to the /terminal/ws endpoint and executing a short scripted sequence to confirm remote command execution, disconnecting within seconds.
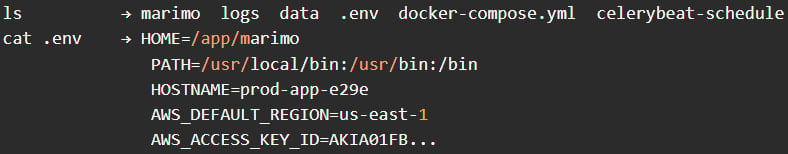
Shortly after, they reconnected and began manual reconnaissance, issuing basic commands such as pwd, whoami, and ls to understand the environment, followed by directory navigation attempts and checks for SSH-related locations.
Next, the attacker focused on credential harvesting, immediately targeting the .env file and extracting environment variables, including cloud credentials and application secrets. They then attempted to read additional files in the working directory and continued probing for SSH keys.
Source: Sysdig
The entire credential access phase was completed in less than three minutes, notes a Sysdig report this week.
Roughly an hour later, the attacker returned for a second exploitation session using the same exploit sequence.
The researchers say that behind the attack appears to be a “methodical operator” with a hands-on approach, rather than automated scripts, focusing on high-value objectives such as stealing .env credentials and SSH keys.
The attackers did not attempt to install persistence, deploy cryptominers, or backdoors, suggesting a quick, stealthy operation.
Marimo users are recommended to upgrade to version 0.23.0 immediately, monitor WebSocket connections to ‘/terminal/ws,’ restrict external access via a firewall, and rotate all exposed secrets.
If upgrading is not possible, an effective mitigation is to block or disable access to the ‘/terminal/ws’ endpoint entirely.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

