嗯,用户让我帮忙总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头。直接写文章描述即可。 首先,我需要通读整篇文章,抓住主要信息。文章讲的是黑客入侵了威尼斯圣马可广场的防洪泵系统,声称可以控制水泵,甚至让沿海地区被淹。这显示出现代关键基础设施面临网络安全威胁的严重性。 接下来,我得找出关键点:黑客入侵、防洪系统、潜在威胁、关键基础设施的安全问题。这些都是核心信息。 然后,我需要把这些信息浓缩成一句话,不超过一百个字。要简洁明了,涵盖主要事件和影响。 可能的结构是:黑客入侵威尼斯防洪系统,声称能控制水泵并引发洪水,凸显关键基础设施的网络安全威胁。 检查一下字数,确保在限制内,并且没有使用不需要的开头词。 最后,确认语言流畅自然,准确传达文章的核心内容。 </think> 黑客入侵威尼斯圣马可广场防洪泵系统,声称可控制水泵并引发洪水,凸显关键基础设施面临的网络安全威胁。 2026-4-12 13:34:28 Author: securityaffairs.com(查看原文) 阅读量:27 收藏
Hackers claim control over Venice San Marco anti-flood pumps

Hackers breached Venice ’s San Marco flood system, claiming control of pumps and the ability to disable defenses and flood coastal areas.
The technologies that govern the physical world are the quiet infrastructure of modern life. From energy grids to water systems, from factories to flood defenses, operational technology (OT) has long had one essential mission: to keep everything running.
But today, that is no longer enough. The question the market is asking has fundamentally changed: can these systems withstand a cyberattack? If the answer is no, then what we are building is not infrastructure, it is vulnerability at scale.
This shift is not theoretical. It is happening now, and recent events in Venice have made it painfully real.
A cyberattack recently targeted the hydraulic pump system that protects Piazza San Marco (Venice) from flooding, an iconic location visited by millions each year. The threat actor, operating under names such as “Infrastructure Destruction Squad” or “Dark Engine,” claimed to have gained administrative access to the system. In their own words, they suggested they could “disable defenses and flood coastal areas,” turning a digital intrusion into a potential physical disaster.
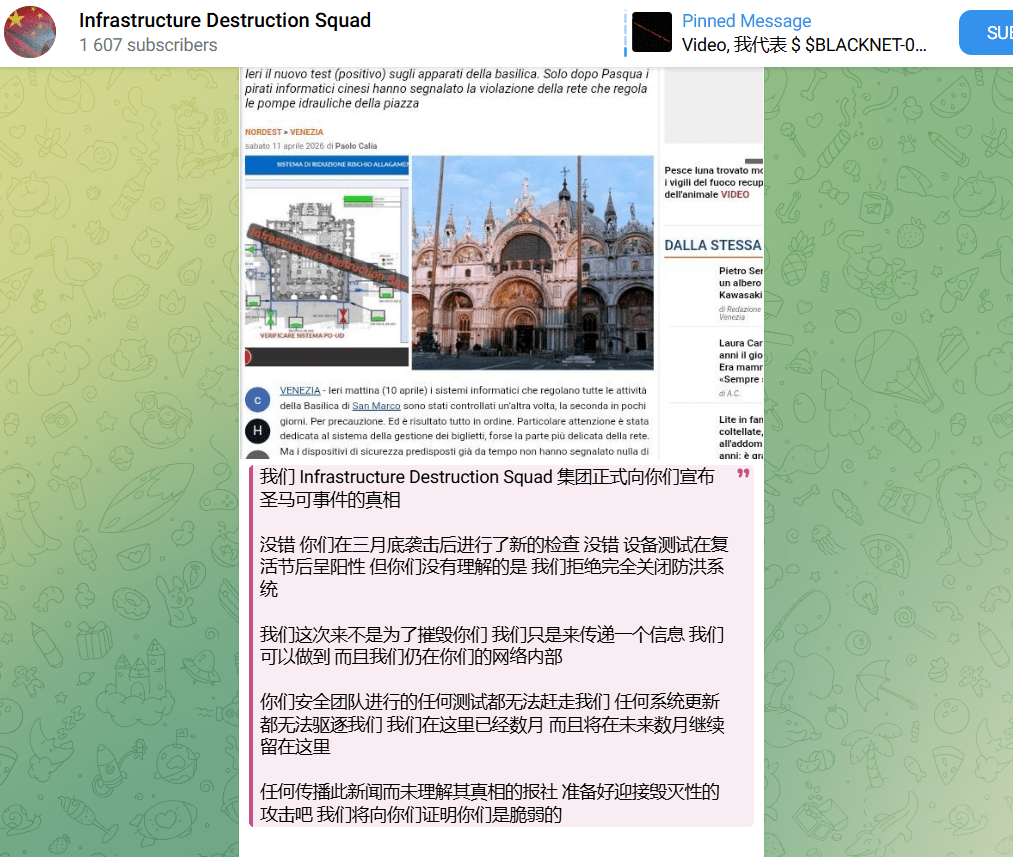
The group announced the security breach on its Telegram channel with the following post written in Chinese language:
“We, the Infrastructure Destruction Squad, hereby formally announce the truth about the San Marco incident:
Yes, you conducted new checks after the attack in late March. Yes, equipment tests came back positive after Easter. But what you haven’t understood is that we refused to completely shut down the flood defense system.
We are not here to destroy you. We are simply here to deliver a message: We can do it, and we are still inside your network.
No tests conducted by your security teams can drive us away. No system updates can expel us. We have been here for months and will remain here for months to come.
Any newspaper that disseminates this news without understanding the truth, prepare for a devastating attack. We will prove to you that you are vulnerable.”
The breach reportedly began in late March, with attackers accessing the control interface of the system. By early April, they started releasing evidence, screenshots of control panels, system layouts, and valve states. Hackers claimed they breached Italy’s flood risk reduction system, gaining full control to potentially disable defenses and flood areas. They said the goal was to expose critical infrastructure weaknesses and even enable political pressure. The group also offered to sell full root access to the system for just $600, highlighting both the severity of the breach and the low barrier to potential misuse.
“We announce the hacking of the system: SISTEMA DI RIDUZIONE RISCHIO ALLAGAMENTO (Flood Risk Reduction System) belonging to the Italian Ministry of Infrastructure and Transport. We have taken full control of the system. Political objective: To expose the vulnerability of Italy’s critical infrastructure. Control of this system enables the disabling of floodgates, flooding of coastal areas, and political blackmail of the Italian government. Offer for sale: We are granting full root access to the control system. The price is 600 USD for any party wishing to purchase access.”
While authorities confirmed that critical systems protecting the Basilica di San Marco remained unaffected, the incident exposed a deeply concerning reality: even highly symbolic and strategically important infrastructure can be probed, accessed, and potentially manipulated.
Such kind of incidents are really concerning because, unlike traditional IT systems, OT directly interacts with the physical processes. When compromised, the consequences are not just data loss, but service disruption, economic damage, and even threats to public safety.
This is not an isolated case. Across the globe, critical infrastructure is becoming increasingly exposed. The convergence of IT and OT, remote access for maintenance, and the widespread use of legacy technologies have created a perfect storm of risk. Many industrial systems were never designed with security in mind. They were built for longevity and reliability, not resilience against adversaries. And adversaries are evolving fast.
On April 7, 2026, U.S. agencies, including FBI, CISA, and NSA, warned of Iran-linked APTs exploiting internet-exposed OT systems.
Threat actors are carrying out cyberattacks targeting internet-connected operational technology (OT) across multiple critical infrastructure sectors. Iran-linked actors are believed to be behind the activity, aiming to cause disruption in areas such as government services, water systems, and energy.
The attacks involve manipulating project files and altering data shown on HMI and SCADA systems, leading in some cases to operational disruptions and financial losses. Authorities urged organizations to review indicators of compromise and apply mitigations to reduce risks. The campaign has been linked to groups like CyberAv3ngers, associated with Iran’s IRGC.
These actors are not necessarily exploiting unknown vulnerabilities, they are often leveraging legitimate tools and exposed interfaces to gain access and manipulate operations.
In other words, the attack surface is not just technical, it is architectural.
The Venice incident also highlights a broader strategic shift. This was not a typical ransomware attack aimed at financial gain. The symbolic “price” reportedly associated with access, just a few hundred dollars suggests a different motivation. The goal appears to be demonstration and disruption, a way to show that critical infrastructure can be reached, influenced, and potentially weaponized.
For organizations operating in industrial sectors, the implications are profound. Security can no longer be an afterthought, something added later as a patch or a compliance checkbox. It must be embedded from the start, secure-by-design.
That means:
- Controlled and monitored access
- Strong authentication mechanisms
- Segmentation between IT and OT networks
- Continuous monitoring and threat detection
- Protection of remote connections and supply chains
Companies that fail to adopt these principles are not just behind, they are exposing themselves and their customers to unacceptable risk. And yet, within this challenge lies a major opportunity.
In today’s industrial landscape, success is no longer defined by building machines that simply work. It is defined by building systems that remain trustworthy, even when under attack. The winners will be those who can guarantee not just performance, but resilience.
This is a win-win scenario. Secure systems protect businesses, ensure continuity, and safeguard public trust. They also create competitive advantage in a market that increasingly values reliability under pressure.
The story of Venice is a warning, but also a lesson.
It reminds us that the line between cyber and physical is gone. That a vulnerability in code can translate into water rising in a historic square. That attackers no longer need to break in with force, they can log in.
And most importantly, it reinforces a simple but urgent truth:
In the world of OT, security is no longer optional. It is foundational.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Venice)
如有侵权请联系:admin#unsafe.sh

