好的,我现在需要帮用户总结一篇关于APT28使用PRISMEX恶意软件的文章,控制在100字以内。首先,我得通读文章,抓住主要信息。 文章提到APT28(又名Fancy Bear等)针对乌克兰及其盟友发起了钓鱼攻击,使用了新的PRISMEX恶意软件。攻击手法包括隐写术和COM劫持,目标是国防系统和援助基础设施。他们利用了CVE-2026-21509等漏洞,快速武器化新披露的漏洞。PRISMEX组件包括Dropper、Loader、Implant,基于Covenant框架,实现无文件攻击和加密C&C通信。 攻击链从钓鱼邮件开始,主题涉及军事训练、天气警报或武器走私。附件中的RTF文件利用CVE-2026-21509漏洞,连接到WebDAV服务器下载恶意LNK文件。LNK文件可能进一步利用CVE-2026-21513绕过浏览器保护。PRISMEX组件使用隐写术、COM劫持和云服务进行C&C通信。 目标包括乌克兰政府、国防、紧急服务和水文气象部门,以及波兰、罗马尼亚等支持军事援助的国家。研究人员将活动归因于APT28,基于工具、基础设施和行为的一致性。 总结时要涵盖APT28的目标、使用的恶意软件及其技术特点,以及攻击的影响范围。控制在100字以内,直接描述内容。 </think> 俄罗斯关联的APT28组织利用新型恶意软件PRISMEX对乌克兰及其盟友发起网络攻击,采用隐写术和COM劫持等高级隐蔽技术实施间谍活动和指挥控制操作。该组织针对国防系统和援助基础设施展开长期间谍行动,并迅速利用新披露的漏洞(如CVE-2026-21509)进行攻击。 2026-4-8 20:23:8 Author: securityaffairs.com(查看原文) 阅读量:14 收藏
Russia-linked APT28 uses PRISMEX to infiltrate Ukraine and allied infrastructure with advanced tactics

APT28 targets Ukraine and allies with PRISMEX malware, using stealthy techniques for espionage and command-and-control.
Russia-linked group APT28 (aka UAC-0001, aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, and STRONTIUM) is running a spear-phishing campaign against Ukraine and its allies, deploying a new malware suite called PRISMEX. Active since September 2025, the campaign uses advanced stealth techniques like steganography and COM hijacking, and targets defense systems and aid infrastructure to support long-running espionage operations.
The Russian cyber espionage group remains highly aggressive, quickly weaponizing newly disclosed flaws like CVE-2026-21509 to target government, military, and critical infrastructure in Central and Eastern Europe. Its latest campaign uses the PRISMEX malware suite, combining a dropper, loader, and implant based on the Covenant framework to enable stealthy, fileless attacks and encrypted command-and-control.
The operation shows advanced preparation and links to past activity, focusing on Ukraine’s defense supply chain, including allies, transport, and aid networks. Researchers believe this marks an evolution of the NotDoor ecosystem, expanding capabilities for rapid exploitation and long-term espionage.
Attack chain starts with spear-phishing emails themed around military training, weather alerts, or weapon smuggling. Victims who open the attached RTF file trigger exploitation of CVE-2026-21509, which bypasses security controls and forces the system to connect to an attacker-controlled WebDAV server. This automatically retrieves and executes a malicious LNK file without further user interaction.
The LNK file may then exploit CVE-2026-21513 to bypass browser protections and execute code silently, downloading additional payloads. This suggests a possible two-stage attack chain designed for stealth and reliability.
“TrendAI™ Research has tracked Pawn Storm’s activities across three distinct but interconnected campaigns, each building upon its previous infrastructure and tooling.” reads the report published by Trend Micro. “The timeline of this campaign indicates advanced knowledge of multiple vulnerabilities:
- CVE-2026-21509: Domain registration for WebDAV servers began on January 12, 2026, exactly two weeks prior to the public disclosure on January 26.
- CVE-2026-21513: The LNK exploit sample appeared on VirusTotal on January 30, 2026, while Microsoft’s patch was not released until February 10, 2026. This 11-day gap confirms zero-day exploitation in the wild.
This pattern suggests Pawn Storm had access to vulnerability details ahead of public disclosure.”
From there, the infection can follow different paths, including deployment of the PRISMEX malware suite. PRISMEX components, such as PrismexSheet, PrismexDrop, PrismexLoader, and PrismexStager, use techniques like steganography, COM hijacking, and abuse of cloud services for command-and-control. These methods enable fileless execution, persistence, and evasion of modern security tools, allowing attackers to maintain long-term access and conduct espionage operations.
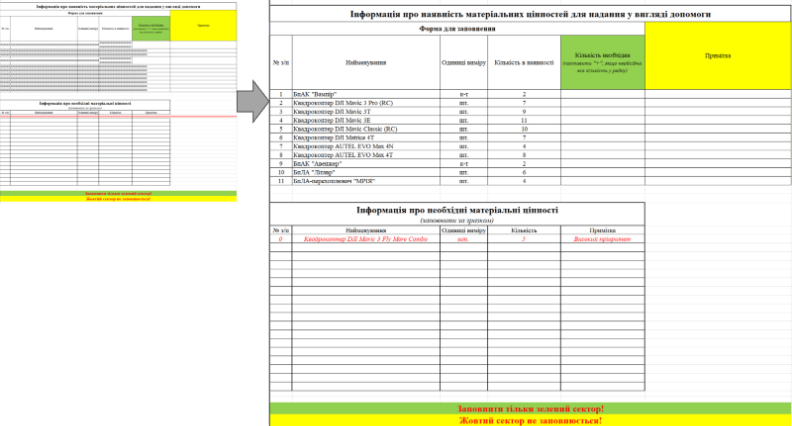
The researchers detailed decoy documents and targeting, such as a malicious Excel files showing realistic decoy content once macros are enabled, including Ukrainian drone inventories, supplier price lists, and military logistics forms.

These themes clearly target Ukrainian drone units and logistics staff. The upload data suggests victims across key regions like Kyiv and Kharkiv, indicating a focus on both frontline and command structures.
PrismexDrop is a native dropper that prepares the system by decrypting payloads, dropping files, and ensuring persistence via COM hijacking and a scheduled task that restarts explorer.exe. This allows the malware to run within a trusted process, improving stealth and reliability.
PrismexLoader is a loader that acts as a proxy DLL, executing malicious code while mimicking legitimate system behavior. It uses a custom “Bit Plane Round Robin” steganography method to extract hidden payloads from images, spreading data across the file to evade detection. The payload is then executed entirely in memory using .NET runtime loading, leaving minimal traces on disk.
The final component, PrismexStager, connects to command-and-control servers via Filen.io cloud services. This helps attackers blend malicious traffic with normal encrypted communications, making detection harder while enabling data exfiltration and remote control.
“The payload extracted from the image is the Covenant Grunt Stager, which we have internally tracked as PrismexStager. This is a .NET assembly responsible for C&C and executing further tasks from the Covenant framework. It is heavily obfuscated with randomized function names to hinder static analysis. ” states the report. “The malware abuses the legitimate end-to-end encrypted cloud storage service Filen.io for C&C communications. By leveraging this trusted service, the malicious traffic blends in with normal encrypted web traffic, effectively bypassing reputation-based filtering and firewall rules.”
The campaign shows a clear strategy: disrupt Ukraine’s supply chain and operational planning, while extending access to NATO-linked logistics. Targets include the Ukrainian government, defense, emergency services, and hydrometeorology, critical for drone and artillery operations, as well as hubs in Poland, Romania, Slovakia, and others supporting military aid flows.
TrendAI attributes the activity to the APT28 group with high confidence, based on consistent tools, infrastructure, and behavior. Unique elements like the custom steganography method, MiniDoor/NotDoor malware lineage, use of Covenant, and COM hijacking reinforce this link, along with reused infrastructure and rapid exploitation of vulnerabilities.
The operation reflects a shift toward tactical disruption rather than pure espionage. By targeting weather data, transport networks, and aid organizations, attackers aim to map and potentially sabotage support to Ukraine. The presence of destructive capabilities alongside espionage tools highlights the dual-use nature of the campaign, enabling both intelligence gathering and potential disruptive attacks aligned with military objectives.
“The technical links between the PRISMEX components and previous campaigns demonstrate the threat actor’s continuous development cycle and modular approach to capability building. Organizations in the targeted geographic and industry sectors should consider themselves at elevated risk and implement the countermeasures detailed above immediately. ” concludes the report. “The use of newly disclosed vulnerabilities and legitimate cloud services makes detection challenging. Defenders must adopt an “assume breach” mentality and focus on behavioral anomalies rather than just static indicators. ”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, APT28)
如有侵权请联系:admin#unsafe.sh
