好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住主要观点。 文章主要讲的是住宅代理对IP信誉系统的影响。研究人员发现,这些代理被用于恶意流量,导致防御系统难以区分攻击者和合法用户。数据来自GreyNoise的分析,涉及40亿次恶意会话,其中39%来自家庭网络,但78%未被信誉系统识别。 接下来,我需要提取关键点:住宅代理短暂、频繁更换,导致难以追踪;攻击者利用这些特性隐藏身份;大部分IP活跃时间不到一个月;涉及683个ISP;主要来自中国、印度和巴西;使用时间和人类作息一致;流量来自物联网僵尸网络和受感染电脑;防御建议转向行为分析。 现在,我要把这些信息浓缩到100字以内。确保涵盖主要问题、数据来源、关键比例和解决方案建议。同时,避免使用“这篇文章”这样的开头。 最后,组织语言,确保流畅简洁。检查字数是否符合要求,并调整句子结构以优化表达。 </think> 住宅代理被用于恶意流量,导致IP信誉系统难以区分攻击者与合法用户。研究人员发现这些代理短暂、频繁更换且涉及大量ISP,使防御系统难以追踪。大部分住宅IP活跃时间不足一个月,主要来自中国、印度和巴西,并与人类作息模式一致。GreyNoise建议转向行为分析以应对这一挑战。 2026-4-2 15:30:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:17 收藏

Researchers warn that residential proxies used to route malicious traffic are a big problem for IP reputation systems, as there is no clear distinction between attackers and legitimate users.
This occurs because residential proxies are too short-lived, uninvolved, or systematically rotated, preventing defense systems from cataloging them in time.
Cybersecurity intelligence platform GreyNoise determined this after examining a massive dataset of 4 billion malicious sessions targeting the edge over a three-month period.
Roughly 39% of those sessions appear to originate from home networks, most certainly part of residential proxies, but 78% of them are invisible to reputation feeds.
“The data reveals a pattern that challenges a core assumption of network defense: that you can tell attackers from legitimate users by where the traffic comes from,” explains GreyNoise.
According to the company, most residential IPs are used once or twice, and then vanish, with attackers rotating them with others, keeping the pace at a level that reputation systems will not flag them.
About 89.7% of residential IPs are active in malicious operations for under a month, with only 8.7% lasting 2 months, and 1.6% persisting for 3 months.
Those that are kept alive for longer seem to carry a specialization according to the researchers, being SSH-focused and using Linux TCP stacks.
Source: GreyNoise
Diversity is another factor that complicates flagging and blocking, as GreyNoise’s data shows the residential IPs participating in attacks belong to 683 internet service providers.
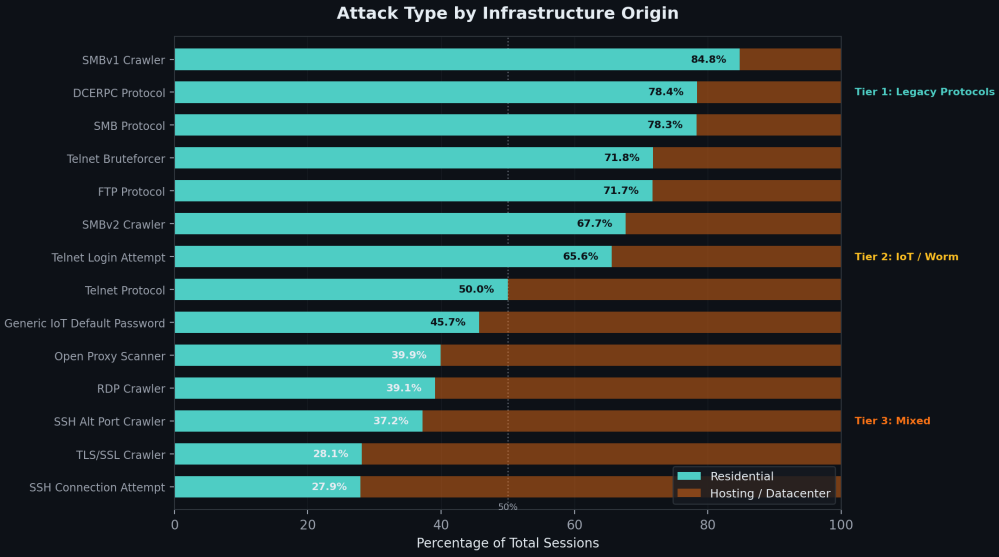
Another reason for their stealthiness is that they are primarily used for network scanning and reconnaissance, with only 0.1% involved in actual exploits, the researchers say.
A small percentage (1.3%) targeted enterprise VPN login pages, while some limited cases also involved residential IPs to path traversal and credential stuffing attempts.
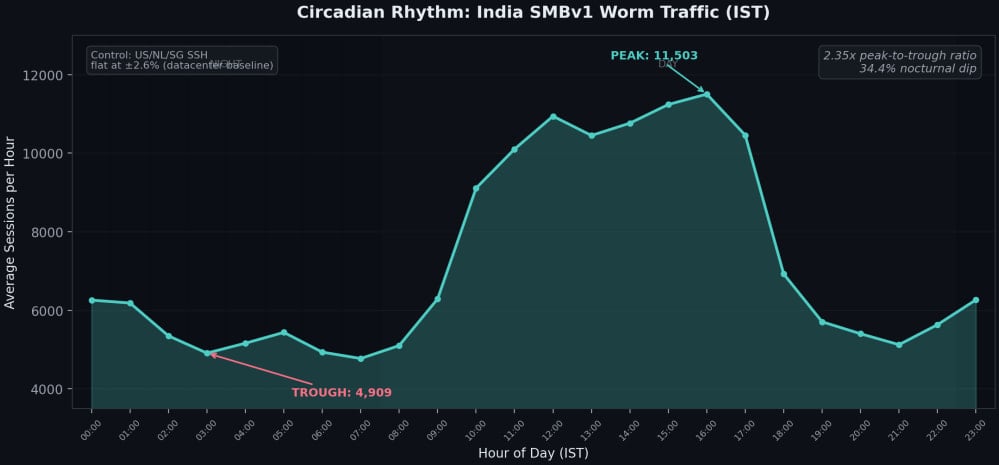
Regarding the source of the residential proxies, GreyNoise says China, India, and Brazil are major contributors, with traffic from the IPs following human sleep patterns, dropping by a third at night, when most people power off their devices.
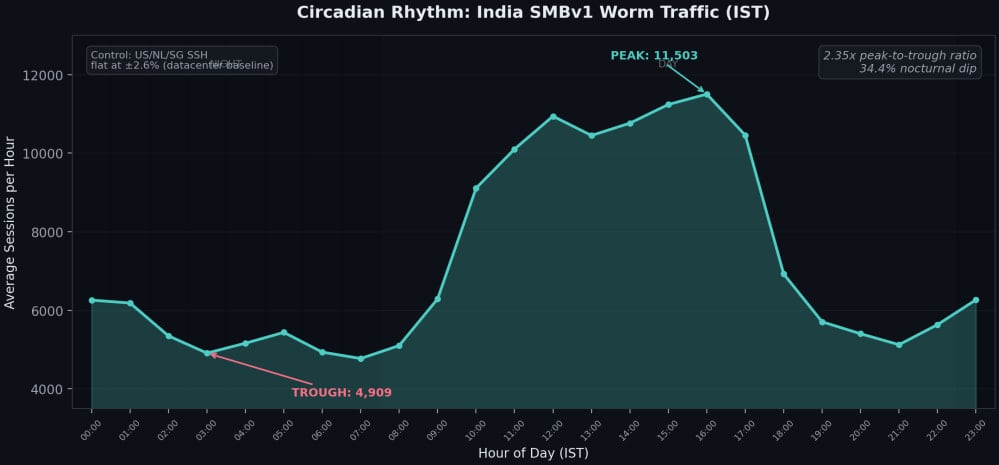
Source: GreyNoise
The researchers report that residential proxy traffic is generated by two distinct, non-overlapping ecosystems: IoT botnets and infected computers.
In cases involving the latter, the proxies come from SDKs in free VPNs, ad blockers, and similar apps, which enroll user devices in bandwidth-selling schemes.
GreyNoise has also highlighted the resilience of these networks using the example of IPIDEA, one of the world’s largest residential proxy networks, which was recently disrupted by Google Threat Intelligence Group (GTIG) and partners.
The disruption reduced its proxy pool by roughly 40%, but in the period that followed, datacenter traffic increased, indicating that demand can be absorbed by others when needed and that lost capacity is quickly replaced.
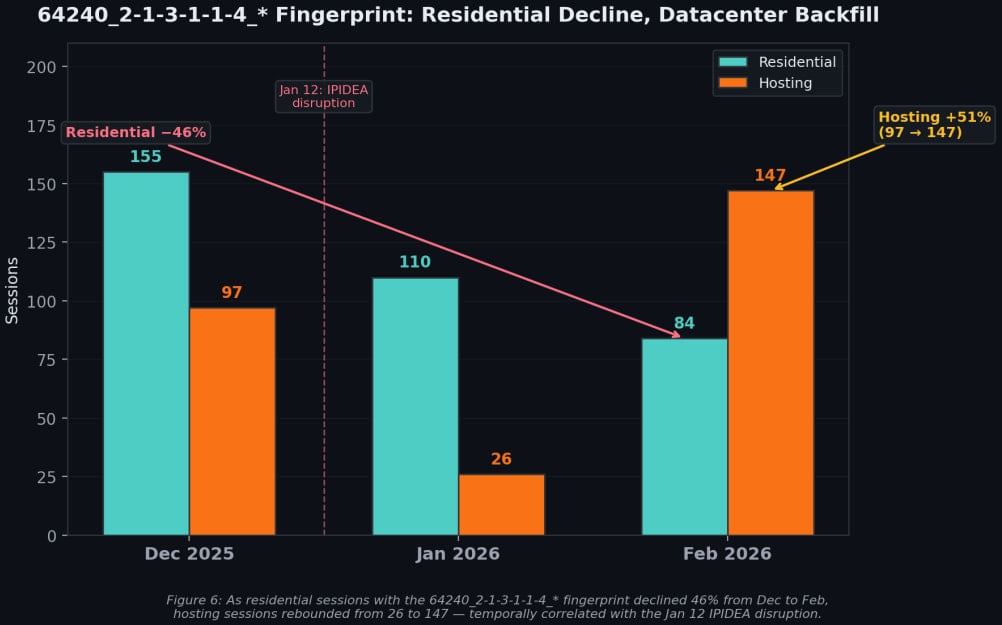
Source: GreyNoise
GreyNoise says residential proxying evasion tactics require abandoning IP reputation as a primary signal and focusing instead on behavior.
The researchers suggest detecting sequential probing from rotating residential IPs, blocking clearly illegitimate protocols like SMB from ISP space, and tracking device fingerprints that survive IP rotation.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
