好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读用户提供的文章内容。 文章主要讲的是GitGuardian团队参加了RWC 2026会议,他们在会上展示了关于私钥泄露的研究,涉及94万多个泄露的私钥。此外,会议还讨论了密码学的几个关键主题,比如后量子算法、形式验证、隐私保护技术和PKI基础设施的脆弱性。还有一些演讲提到了密码管理器的安全漏洞和可信执行环境的潜在威胁。 接下来,我需要将这些信息浓缩到100字以内。重点包括会议名称、GitGuardian的研究成果、会议讨论的主题以及关键演讲内容。同时要确保语言简洁明了,不使用复杂的术语。 可能的结构是:会议名称、时间地点、GitGuardian的研究发现、讨论的主题以及演讲亮点。这样既涵盖了主要信息,又控制在字数限制内。 最后,检查一下是否符合用户的要求,没有使用“文章内容总结”等开头,并且信息准确全面。 </think> GitGuardian团队在RWC 2026会议上展示了关于94万多个泄露私钥的研究,并探讨了后量子算法、隐私保护技术及PKI基础设施等主题。会议还揭示了密码管理器和可信执行环境的安全漏洞。 2026-4-1 15:49:2 Author: securityboulevard.com(查看原文) 阅读量:3 收藏
In early March, the GitGuardian cybersecurity research team joined several hundred cryptographers, security engineers, and practitioners in Taipei for the tenth edition of the Real World Cryptography Symposium (RWC 2026). Held from March 9 to 11, the conference lived up to its name: three dense days of talks grounded in the reality of production-deployed crypto-systems.
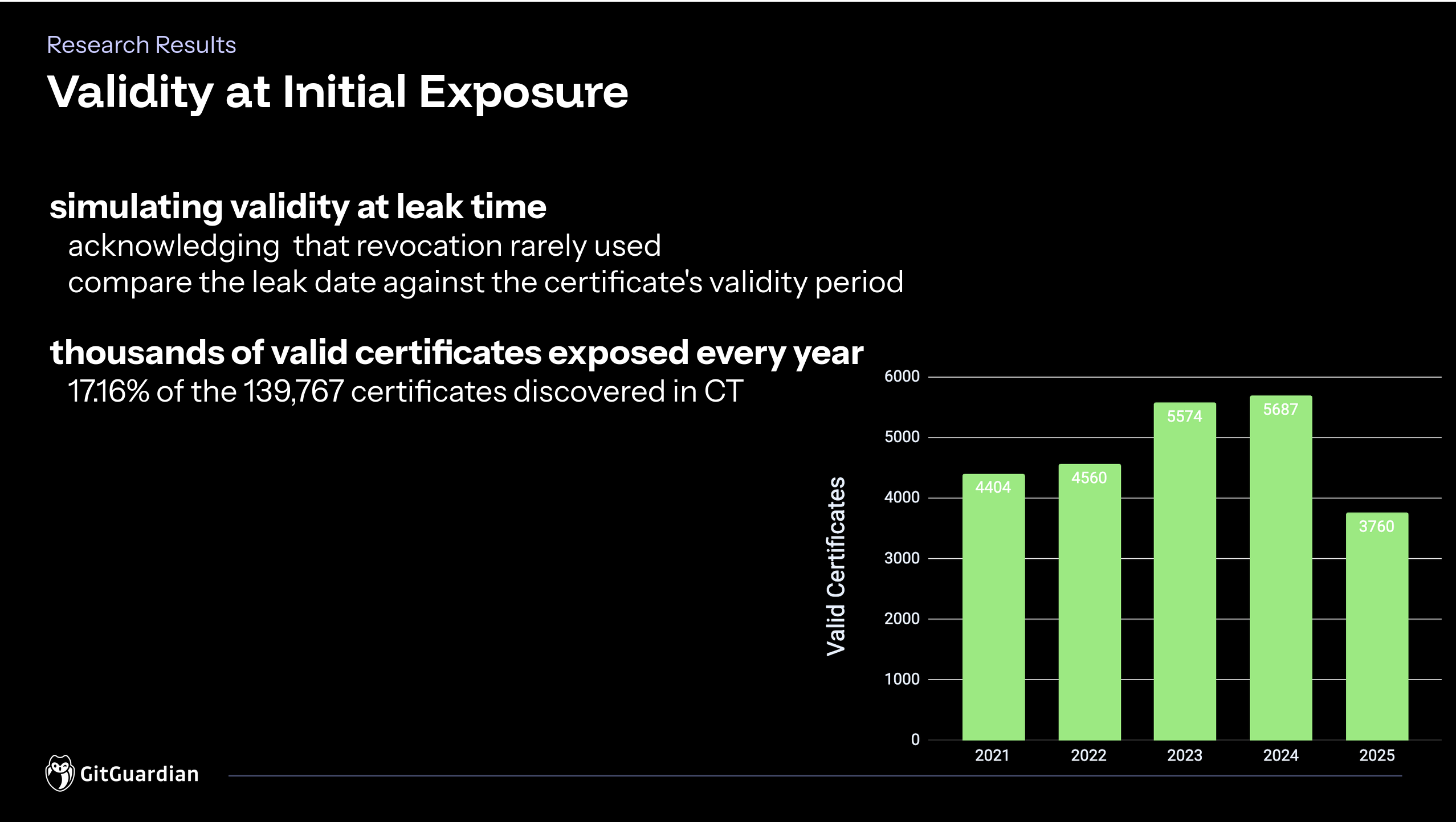
Beyond oolong drinking and the night markets, Taipei had more serious business to offer: GitGuardian was there to present our own research. We took the stage on Day 3 to share the findings behind "Private Key Leaks in the Wild", mapping 945,560 leaked private keys to 139,767 certificates through Certificate Transparency logs, evidence that key material escaping into the wild is not a niche incident but a systemic problem.
Across the three days, recurring themes emerged: the industry-wide migration toward post-quantum algorithms and its hard engineering trade-offs; formal verification maturing into a practical tool; privacy-enhancing technologies finding their way into production systems; and secure channels and PKI infrastructure proving more fragile than assumed. All talks are worth a read or a replay, and the recordings are already available online.
This article, however, focuses on what resonated most with GitGuardian.
When secret managers fail: a cryptography nightmare
Matteo Scarlata and Giovanni Torrisi represented their team of four researchers in this presentation about password managers' security. Their talk was titled Zero Knowledge (About) Encryption, a pointed jab at the "zero-knowledge" marketing promise that cloud-based password managers like Bitwarden, LastPass, and Dashlane use to sell themselves: the claim that the provider never sees your plaintext secrets. This is usually the definition of what is called end-to-end encryption (E2E).
This research focused on studying the security of four cloud-based password managers under the E2E encryption hypothesis, especially in a malicious server attack model. Matteo Scarlata et al demonstrated serious attacks against all four password managers. 27 attacks in total. Most issues stem from a weak cryptography protocol, especially related to “advanced” features:
- Key recovery
- Partial vault synchronization
- Secret sharing
- Backward compatibility
Notable attacks included:
- BitWarden’s server being able to enforce the key recovery for any client, recovering a master decryption key.
- Servers acting as a public key server for password sharing, where they can provide malicious keys to recover shared passwords.
- Password leak through favicon resolution resulting from field-level encryption and no key separation (LastPass, Bitwarden).
The full paper backing this research is available online and is a must-read.
Password-based authentication has been an open problem for decades now, and this research shows that this is still the case, despite the existing vaults and other storage solutions. The whole industry has been pushing toward vaults and password managers to manage authentication secrets, which makes sense considering the state of authentication. That said, this research reminds us that the threat model of a compromised vault is important to consider.
Under the assumption of a compromised secret vault, having a good understanding of one’s own secret landscape is paramount, a situation where NHI governance and secrets observability can help.
Should you trust your trusted execution environment?
Somehow on the same line, Christina Garman and Daniel Genkin presented their talk “TEE.fail: Breaking Trusted Execution Environments via Memory Bus Interposition”, where they also found and exploited vulnerabilities in a technology everyone would deem the state-of-the-art of security: trusted execution environments. They targeted both AMD and Intel’s latest TEE technologies, which shifted significantly in how they are implemented. Especially, both now rely on AES-XTS for memory encryption, which offers no integrity protection.
Through a brilliant live demonstration, Christina and her team showed how, using hobbyist-level hardware, it is possible to set up an interposition attack on a server’s physical memory. They later used this setup to recover private keys from the TEE in an otherwise simple attack.
Although the threat model for this attack is quite convoluted, making it difficult to perform outside a state-sponsored operation, and, more specifically, an adversarial law enforcement situation, this talk puts some perspective on best-of-breed security mechanisms. As showcased with the password safes example above, even the best-protected secrets can leak, and we should keep that in mind when designing our risk analysis.
In one rather interesting talk, Yubiko’s Christopher Harrell explored a fundamentally interesting question: how did we get from a mostly-unencrypted internet to 95% of Chrome page loads being HTTPS? His main point is that it did not occur in a blast after a single breakthrough: the cryptography to make it happen has been as old as the internet itself. However, real adoption stemmed from a mix of policies, standards evolution, or accessible infrastructure (Let’s Encrypt in that case).
Harrell then traced the same pattern through human identities and authentication, with the example of passkeys and FIDO. Human authentication has gone through three recognizable phases:
- Shared secrets (passwords)
- Second factors (mostly TOTP and SMS OTP)
- Device-bound phishing-resistant credentials (Passkeys, FIDO)
Similar to the encryption on the Internet, while the technology required for secure human authentication exists, the adoption is not there yet.
What resonated particularly with GitGuardian’s activities is how we can parallel human authentication evolutions to the Non-Human Identities world. Non-human identities (the API keys, service account passwords, and OAuth tokens that machine-to-machine communication relies on) are still largely stuck in phase one. Long-lived API keys are, functionally, passwords: static, shareable, leak-prone, and with no equivalent of origin binding. OAuth tokens represent an improvement analogous to MFA, but they remain stealable and, in many configurations, reusable beyond their intended context.
The FIDO moment for non-human identities has not arrived yet, and the scale of the problem is already visible in the data. As showcased in the State of Secret Sprawl report, the number of leaked secrets, largely linked to NHIs, has never been higher. While the technology evolves, hopefully, before we get locked in the insecure defaults, you’d better be equipped with a good secret security solution.

Until next time
There is so much more that could be told about the content that was presented at RWC 2026, and so many more presentations are worth watching – just like Nadia Heninger’s talk about the encryption technologies used in space and technical debt, a topic that could very much find parallels in the NHIs world. If you want to know more, the slides of all the presentations are available on the conference website. Video recordings should also be made available soon.
We can only hope GitGuardian’s research team will be able to attend Real World Crypto again in the future. Presenting at such a conference is an honor, and we need to thank the organizers and chairmen for allowing us to promote our work there this year.
Until next time, if you want to have a peek at GitGuardian research topics and results, now is the perfect time to have a look at our fresh release of the State of Secret Sprawl report.
*** This is a Security Bloggers Network syndicated blog from GitGuardian Blog - Take Control of Your Secrets Security authored by Gaëtan Ferry. Read the original post at: https://blog.gitguardian.com/highlights-from-rwc-2026/
如有侵权请联系:admin#unsafe.sh