嗯,用户让我用中文总结一下这篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我需要通读文章,抓住主要信息。 文章讲的是Cisco Secure Firewall Management Center的一个严重漏洞,CVE-2026-20131。这是一个远程代码执行漏洞,CVSS评分是10.0,属于最高级别。攻击者无需认证就能利用这个漏洞执行任意代码,甚至以root权限运行。这个漏洞已经被用于实际攻击中,包括勒索软件活动。 接下来,技术细节部分提到漏洞是由于不安全的Java对象反序列化导致的。攻击者发送一个恶意的HTTP请求就能触发漏洞。此外,文章还提到了修复措施和时间线,比如Cisco已经发布了补丁,并且CISA将其加入已知被利用的漏洞目录。 用户可能需要的是一个简洁明了的摘要,用于快速了解问题。所以我要提炼出关键点:漏洞名称、类型、CVSS评分、影响范围、攻击方式、实际利用情况以及修复建议。 最后,确保语言简洁,在100字以内。可能的结构是:描述漏洞及其严重性、影响范围、攻击方式和实际利用情况、修复建议。 </think> Cisco Secure Firewall Management Center 存在严重反序列化漏洞(CVE-2026-20131),CVSS 评分为 10.0。该漏洞允许未认证攻击者通过恶意 Java 对象执行任意代码并获取 root 权限。已报告该漏洞被用于勒索软件攻击。 Cisco 已发布补丁修复此问题。 2026-3-31 18:5:5 Author: horizon3.ai(查看原文) 阅读量:17 收藏
Cisco Secure Firewall Management Center Insecure Deserialization Vulnerability
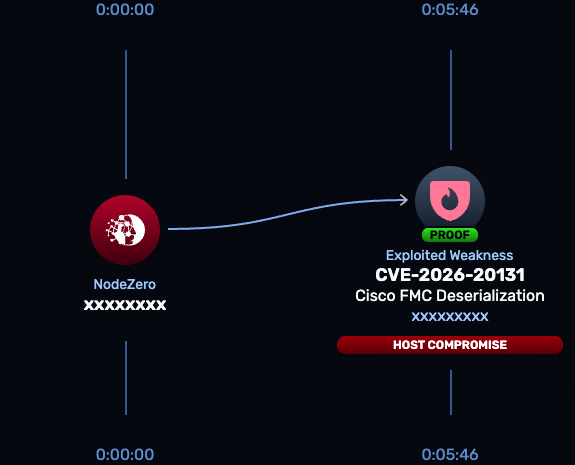
CVE-2026-20131 is a critical remote code execution vulnerability affecting Cisco Secure Firewall Management Center (FMC) Software and Cisco Security Cloud Control Firewall Management. Cisco assigns a CVSS v3.1 score of 10.0 and attributes the issue to insecure deserialization of user-supplied Java objects in the web-based management interface. An unauthenticated remote attacker can exploit this flaw to execute arbitrary code as root. Cisco and multiple security reports confirm that this vulnerability has been exploited in the wild, including in ransomware campaigns.
Technical Details
Cisco describes CVE-2026-20131 as a vulnerability in the web-based management interface caused by unsafe deserialization of user-controlled Java data.
The vulnerability does not require authentication or user interaction. An attacker can send a crafted HTTP request containing a malicious serialized Java object to the FMC interface. When processed, the application deserializes the object without proper validation, resulting in arbitrary Java code execution with root privileges.
The vulnerability affects Cisco Secure FMC Software and Cisco Security Cloud Control Firewall Management regardless of configuration. Cisco notes that limiting exposure of the management interface reduces attack surface but does not eliminate risk.
Because FMC serves as the centralized management plane for firewall policy and visibility, successful exploitation can allow attackers to execute commands as root and potentially impact firewall operations, configurations, and access control across the environment.
NodeZero® Proactive Security Platform — Rapid Response
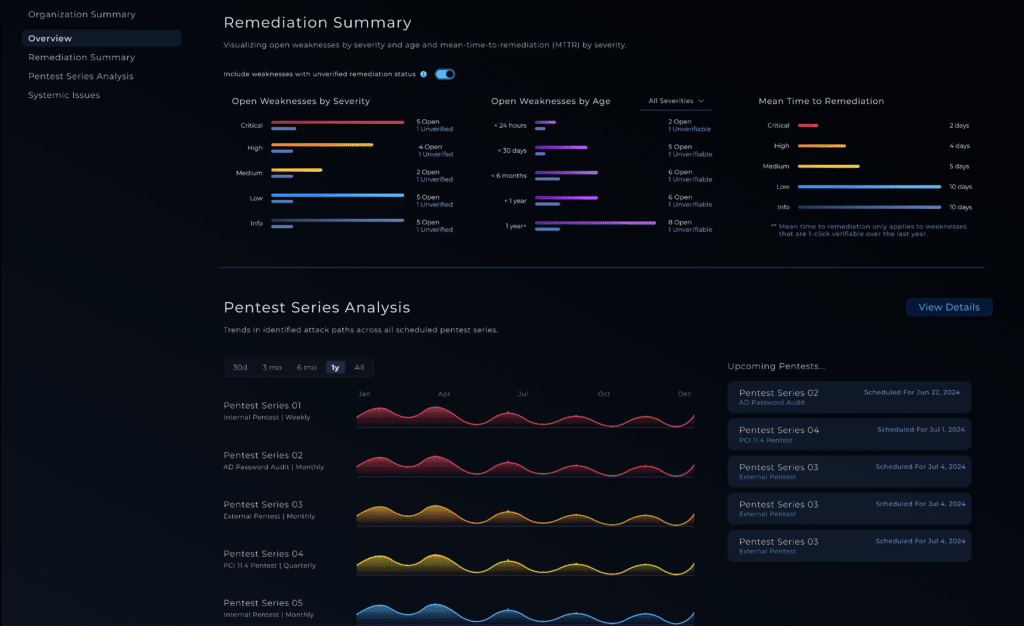
The Rapid Response test in NodeZero is designed to help security teams answer the question that matters most: is this actually exploitable in our environment? For CVE-2026-20131, the test can be used to validate exposure before remediation and confirm the issue is no longer exploitable after the fix is applied.
- Run the Rapid Response test
Use NodeZero to verify whether Cisco FMC instances are susceptible to unauthenticated remote code execution. - Patch immediately
Cisco has released software updates to address this vulnerability. Organizations should upgrade to the fixed versions identified in Cisco’s advisory. Cisco states that no workarounds are available. - Re-run the Rapid Response test
After patching, re-test to confirm the vulnerability is no longer exploitable and that remediation was effective.
Indicators of Compromise
Cisco has not published a detailed list of indicators such as attacker IP addresses, file hashes, or filenames for CVE-2026-20131.
However, based on observed exploitation and reported attack activity, defenders should monitor for:
- Unexpected or suspicious HTTP requests to the FMC web interface, particularly those containing serialized payloads
- Outbound connections initiated from the FMC appliance to unknown or untrusted external systems
- Execution of unexpected processes or commands on the FMC system
- Unexplained changes to firewall configurations, policies, or administrative settings
- Evidence of persistence mechanisms or unauthorized access originating from the FMC host
- Public reporting linked exploitation of this vulnerability to ransomware campaigns, indicating that attackers may use initial access to establish persistence and move laterally.
Affected versions & patch
Affected:
- Cisco Secure Firewall Management Center (FMC) Software
- Cisco Security Cloud Control Firewall Management
Patch:
Cisco has released software updates to remediate this vulnerability. Customers should use Cisco’s Software Checker and advisory to identify the appropriate fixed release for their deployment.
Cisco states that there are no workarounds available for this vulnerability.
For Cisco Security Cloud Control Firewall Management, updates are applied by Cisco as part of standard SaaS maintenance.
Timeline
- March 4, 2026: Cisco published its security advisory and released patches for CVE-2026-20131.
- March 18, 2026: AWS threat intelligence reported exploitation of CVE-2026-20131 in ransomware activity.
- March 19, 2026: Cisco updated its advisory to include evidence of in-the-wild exploitation.
- March 19, 2026: CISA added CVE-2026-20131 to the Known Exploited Vulnerabilities (KEV) catalog.
- March 22, 2026: Deadline issued for U.S. federal agencies to remediate or discontinue use of affected systems.
References
- Cisco Security Advisory — Cisco Secure Firewall Management Center Software Remote Code Execution Vulnerability
- CVE Record — CVE-2026-20131
- CISA KEV Catalog — Known Exploited Vulnerabilities Catalog
- AWS Security Blog — Interlock ransomware campaign targeting enterprise firewalls
- SecurityWeek — Cisco Firewall Vulnerability Exploited as Zero-Day in Interlock Ransomware Attacks
- BleepingComputer — CISA orders feds to patch max-severity Cisco flaw by Sunday
Read about other CVEs
NodeZero® Platform
Implement a continuous find, fix, and verify loop with NodeZero
The NodeZero® platform empowers your organization to reduce your security risks by autonomously finding exploitable weaknesses in your network, giving you detailed guidance around how to priortize and fix them, and having you immediately verify that your fixes are effective.
Recognized By
如有侵权请联系:admin#unsafe.sh