
嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要快速浏览文章内容,抓住主要信息。 文章主要介绍Tenable Cloud Security的最新更新,包括自定义策略自动化、AWS ABAC支持、漏洞保护等。这些功能旨在减少MTTR,同时不影响DevOps流程。 接下来,我得提取关键点:自动化治理、研究驱动的情报、最小权限、漏洞修补。这些都是文章的核心内容。 然后,我要确保总结简洁明了,不超过100字。可能需要合并一些信息,避免重复。 最后,检查语言是否流畅自然,确保用户能快速理解主要内容。 </think> Tenable Cloud Security最新更新通过自定义策略自动化、AWS ABAC支持和研究驱动的漏洞保护,帮助用户减少平均修复时间(MTTR),同时优化多云环境的安全管理。 2026-3-31 13:0:0 Author: www.tenable.com(查看原文) 阅读量:11 收藏
Stop the noise and scale your cloud security. Our latest updates introduce custom policy automation via Explorer, AWS ABAC support for true least privilege, and research-backed protection against critical vulnerabilities, all designed to slash MTTR without disrupting your DevOps workflows.
Key takeaways
- Automated governance via Explorer: Harness the power of Tenable’s unified data model, transforming any query into a permanent security policy or a scheduled report across all entities, such as resources, findings and vulnerabilities, with custom interval scheduling.
- Research-driven intelligence: New insights from Tenable Research feature the discovery of novel critical vulnerabilities in Google Looker Studio and Google Looker, and a deep-dive into a recently identified malicious third-party npm package.
- True least privilege via ABAC: Support for AWS ABAC ensures precision in permission evaluations — a critical requirement for securing the 18% of organizations with overprivileged IAM roles that AWS AI services can instantly assume.
- Streamlined vulnerability patching: Tenable's unique plugin name and ID information is now integrated into vulnerability and workload profiles, eliminating manual research for DevOps teams.
Cloud security often generates more “noise" than insight. The goal for the security team is to close the gap between discovery of vulnerabilities/misconfigurations and their actual remediation — all without disrupting DevOps workflows.
The latest updates to Tenable Cloud Security are focused on that exact mission: providing the precision needed to silence the noise and the automation required to scale – and quickly. From flexible custom policies and query-based reporting to granular IAM visibility, we’re making it easier to manage your cloud security posture across complex, multi-cloud environments.
Using Tenable advances your maturity by shifting the focus from managing individual findings to understanding functional resilience.
Governance and automation: The power of our Explorer
We have enhanced the recently introduced Explorer capability to allow you to turn multi-cloud risk analysis insights into automated governance and scheduled intelligence.
Custom policy creation from queries
Use the Explorer query builder to create custom policies, baking your internal business logic directly into the platform. If you can query it, you can police it—for example, tracking publicly exposed EC2 instances with a "Sensitive" tag. You can set findings at your preferred severity level, ensuring your dashboard reflects your organization's actual risk priorities. Additionally, you can now add free-text remediation instructions to any policy to align with your organization’s specific practices.
Bottom line: Effortlessly transform ad-hoc searches into permanent, automated security monitoring that triggers exactly when and how you need it.
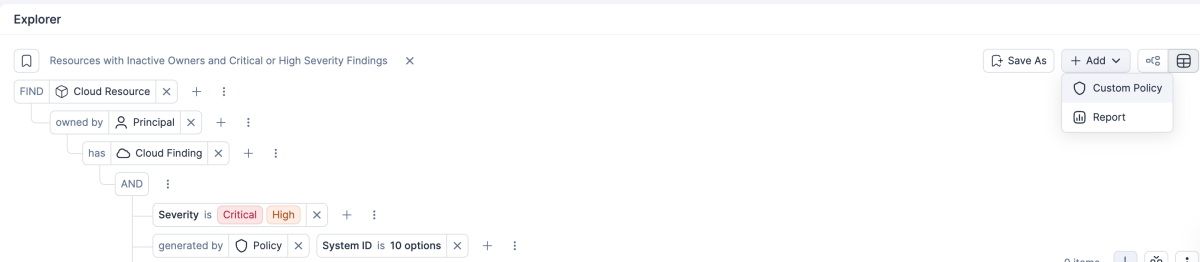
Transform queries into standing custom policies in one click using the Explorer query builder and customize the remediation steps for improved governance
Automated reports from queries
Explorer, based on our unified data model, generates reports based on queries of all entities, including cloud resources, finding types, and vulnerability instances. You can use a redesigned, full-screen reporting experience with live data previews and local time zone support. New custom-interval scheduling gives you total control, such as scheduling a report for every Monday and Wednesday at 9:00 AM.
Bottom line: Provides a consistent, automated pulse on your cloud security posture, delivering tailored insights to stakeholders on a regular cadence via our report delivery method.

Generate reports based on detailed Explorer queries, and schedule them for delivery at customized intervals
Research spotlight: Protection against emerging cloud threats
A cloud security platform is only as good as its intelligence. Tenable Research continues to lead the industry in identifying critical cloud service and supply chain vulnerabilities.
Uncovering vulnerabilities in Google Looker Studio and Google Looker
Our researchers recently discovered and responsibly disclosed significant novel vulnerabilities in both Google Looker Studio and Google Looker. The “LeakerLooker” discovery identified nine cross-tenant vulnerabilities that could have let attackers exfiltrate or modify data across Google services. The “LookOut” discovery identified remote code execution (RCE) and unauthorized internal access risks that could have allowed an attacker to completely compromise a Looker instance. These discoveries reflect how, working behind the scenes, Tenable offers proactive protection to help secure an organization’s broader cloud ecosystem.
Neutralizing supply chain attacks
The threat often enters through the code itself. Tenable Research recently provided a deep-dive analysis of "ambar-src," a malicious npm package designed to mimic popular legitimate libraries to infect developer systems. This is critical as research shows 86% of organizations host third-party code packages with critical-severity vulnerabilities.
Bottom line: When you use Tenable Cloud Security, you are backed by the same elite research team that discovered these Looker and npm threats, ensuring protection against modern, sophisticated attack vectors.
Workload protection (CWPP): Slashing mean-time-to-remediation
The gap between security and DevOps is often manual research. When security tools lack clear fixes, remediation stalls, and the risk window stays open. In fact, we recently found that 82% of organizations run cloud workloads with known, exploited, critical CVEs – leaving environments highly vulnerable to automated exploitation – a growing threat in this AI era.
Remediation patches and Tenable plugin IDs
To bridge this divide we integrated Tenable plugin IDs directly into vulnerability tables and workload profiles – that is, the remediation workflow. With vulnerabilities now mapped to specific plugin names and IDs, teams can instantly identify the exact software versions required to resolve security gaps across VMs and container images. Integrated metadata, including Vulnerability Priority Ratings (VPR) and discovery timestamps, allows teams to move past "severity" and focus on the actual risk impact to the business. DevOps get the exact patch name they need, removing manual research and "back-and-forth" communication between security and engineering.
Bottom line: Greatly reduces mean-time-to-remediation (MTTR) by providing actionable data at the point of discovery, aligning security goals with developer velocity.
Cloud identity and entitlement management (CIEM): Achieving least privilege with permissions granularity
Identity is the new perimeter, but managing it at scale is difficult. Indeed our recent risk report found this is becoming increasingly critical for AI-related identities, with 18% of organizations having overprivileged IAM roles that AWS AI services can instantly assume.
AWS ABAC support and granular visibility
We’ve upgraded permission evaluations to support AWS attribute-based access control (ABAC) and added a dedicated access level section to resource profiles. This replaces generic summaries with a detailed breakdown of permission categories, providing a highly accurate view of your identity landscape.
Bottom line: Achieve true least privilege by accounting for attribute-based access, ensuring your permission recommendations are as precise as your AWS environment.
Strategic operations: Scale and precision
Data security: Precision classification
Enhance data discovery by using Regex to exclude known or irrelevant values. This ensures data security findings focus on the specific sensitive information while filtering out irrelevant data matches.
Bottom line: Ensures your team only spends time on genuine data exposure risks, increasing operational efficiency.
GraphQL API and centralized exclusions
Manage high-volume environments programmatically with new GraphQL API support for Projects, allowing you to create or modify role assignments directly within your DevOps workflows. Our new centralized exclusions framework allows you to define business scenarios to ignore non-actionable findings using flexible tags, creating a single, auditable source of truth for all exceptions.
Bottom line: Streamlines security governance for large-scale environments by automating project management and centralizing risk handling.
Frequently Asked Questions
Q: How do custom policies differ from the built-in policies in Tenable Cloud Security?
A: While built-in policies cover industry standards, custom policies allow you to use the Explorer query builder to create rules specific to your environment and assign the severity levels that reflect your organization’s risk appetite.
Q: Why is the support for AWS ABAC a significant update for identity security?
A: Most tools evaluate only static IAM policies, but modern permissions are often granted based on attributes (tags). We support AWS ABAC to provide the precision needed for true least privilege without disrupting developer workflows.
Q: Why is using the Tenable One Exposure Management Platform important for my cloud strategy?
A: It shifts the focus from "finding bugs" to "managing risk" in full context across your hybrid environment. Tenable One’s cloud security capabilities integrate vulnerabilities, identities, network, and data into a single view, allowing you to see how an attacker could move through your environment.
Learn more:

Yoel Calderon
Senior Director, Product Management
Yoel Calderon, Senior Director of Product Management at Tenable, leads the Tenable Cloud Security Product Management group. He is a cybersecurity product veteran with 18+ years of experience in designing and delivering enterprise software. Before joining Tenable, Yoel led the Cloud Security product portfolio at Proofpoint and played a key role in building VMware’s cloud services platform and shifting the company toward SaaS products. He holds an MBA (magna cum laude) from Tel Aviv University and is a co-inventor on several patents in cloud storage and data protection.
如有侵权请联系:admin#unsafe.sh