
嗯,用户让我帮忙总结一篇文章,控制在一百个字以内。首先,我需要仔细阅读文章内容,抓住主要信息。文章讲的是一个叫Jonathan Spalletta的人,他两次入侵Uranium Finance加密交易所,窃取了超过5300万美元的加密货币,并通过加密货币混合器洗钱。然后他用这些钱买了各种收藏品,最后被执法部门逮捕,面临最高20年的监禁。 接下来,我要确定用户的需求是什么。用户可能是一个需要快速了解新闻内容的人,比如记者或者学生。他们可能希望得到一个简洁明了的摘要,不需要复杂的结构或过多的细节。 然后,我需要将这些信息浓缩到100字以内。要确保包含关键点:嫌疑人是谁,做了什么(入侵交易所、窃取金额、洗钱)、结果(交易所关闭)、他的花费以及被捕和可能的刑罚。 最后,检查语言是否流畅自然,避免使用过于正式或复杂的词汇。确保摘要准确传达文章的核心内容。 </think> 一名男子因两次入侵Uranium Finance加密交易所窃取超5300万美元并洗钱被捕。他利用智能合约漏洞非法提款,并用赃款购买高价收藏品。检方指控其破坏交易所运营并造成重大损失。 2026-3-31 09:30:18 Author: www.bleepingcomputer.com(查看原文) 阅读量:15 收藏

U.S. prosecutors have charged a Maryland man with stealing more than $53 million after hacking the Uranium Finance crypto exchange twice and laundering the proceeds through a cryptocurrency mixer.
36-year-old Jonathan Spalletta (known online as "Cthulhon" and "Jspalletta") appeared in court before U.S. Magistrate Judge Ona T. Wang after surrendering to law enforcement on Monday.
Spalletta hacked the decentralized cryptocurrency exchange Uranium (which operated as an automated market maker similar to Uniswap) in April 2021, forcing the company to shut down due to a lack of funds after stealing approximately $53.3 million worth of cryptocurrency.
"As alleged, Jonathan Spalletta repeatedly hacked smart contracts to steal millions of dollars' worth of other people's money for himself, and destroyed a cryptocurrency exchange in the process," said U.S. Attorney Jay Clayton.
"In describing his alleged 'heist,' Spalletta told another individual' Crypto is just fake internet money anyway.' Stealing from a crypto exchange is stealing—the claim that 'crypto is different' does not change that. For the victims, there is nothing different about having your money taken. Spalletta cost real victims real losses of tens of millions of dollars, and now he's under real arrest."
According to the unsealed indictment, the defendant carried out two separate attacks. During the first breach, on April 8, Spalletta exploited a flaw in Uranium's smart contract code, abusing the AmountWithBonus variable to issue zero-token withdrawal commands that forced the exchange to pay rewards he was not entitled to receive, draining the liquidity pool of approximately $1.4 million.
Spalletta then extorted Uranium into assigning nearly $386,000 of the stolen funds as a sham "bug bounty" in exchange for returning the remainder to the crypto-exchange.
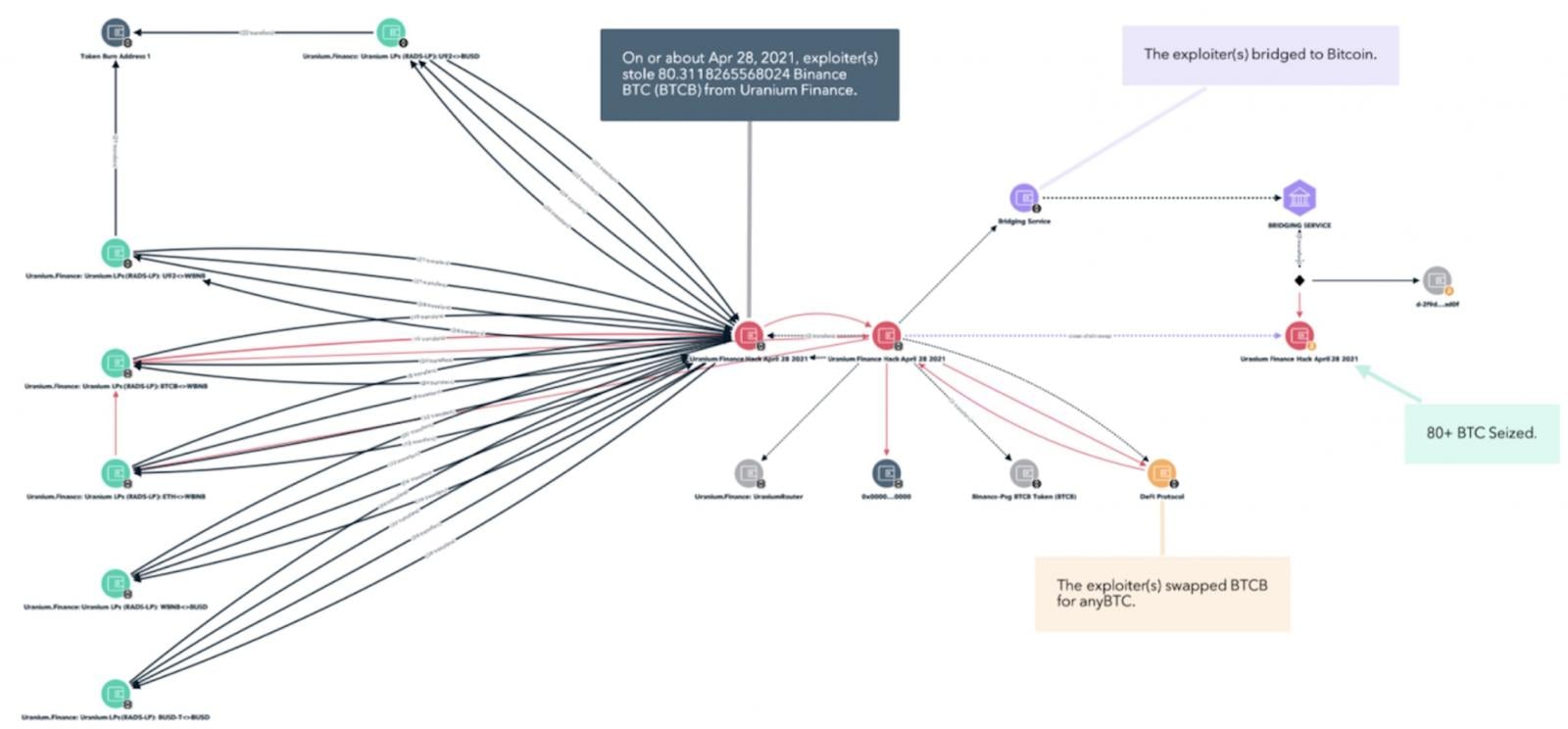
Three weeks later, on April 28, he struck again, exploiting a separate single-character coding error that caused Uranium's transaction-verification logic to use 1,000 instead of 10,000.
This allowed Spalletta to withdraw nearly 90% of the assets held across 26 separate liquidity pools while depositing effectively zero tokens, netting him approximately $53.3 million (the overwhelming majority of Uranium's holdings) and forcing the crypto exchange to shut down immediately.
Spalletta laundered the stolen crypto assets across multiple decentralized exchanges through the Tornado Cash cryptocurrency mixer and spent the proceeds on a wide range of items, including a "Black Lotus" Magic: The Gathering card for approximately $500,000, 18 sealed packs of Alpha Booster Magic cards for around $1.5 million, a first-edition complete Pokémon base set for roughly $750,000, and an ancient Roman coin commemorating Julius Caesar's assassination for over $601,000.
In February 2025, law enforcement seized the collectibles from his residence under a court-authorized search warrant and recovered approximately $31 million in cryptocurrency from wallets linked to Spalletta.
Spalletta now faces up to 10 years in prison on a computer fraud count and up to 20 years if found guilty of money laundering.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
