好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我得通读一下这篇文章,了解它的主要信息。 文章讲的是Sekoia Reveal这个产品,它帮助安全团队解决数据过多但缺乏上下文的问题。作者提到安全团队并不缺少数据,而是缺少将这些数据整合起来的上下文。Sekoia Reveal通过提供实时、统一的资产视图,帮助分析师更快地理解问题并采取行动。 接下来,我需要提取关键点:实时统一视图、整合资产、漏洞、行为信号、检测结果、减少盲点、提升效率。这些都是文章的核心内容。 然后,我要把这些信息浓缩成100字以内的描述。要确保语言简洁明了,直接传达产品的功能和优势。 最后,检查一下是否符合用户的要求:中文总结,100字以内,没有特定的开头。确保内容准确且完整。 </think> Sekoia Reveal 提供实时统一视图,整合资产、漏洞、行为信号和检测结果,帮助安全团队快速理解风险并采取行动。它通过减少盲点和提升上下文感知能力,助力SOC更高效地应对威胁。 2026-3-31 10:19:25 Author: blog.sekoia.io(查看原文) 阅读量:19 收藏
Security teams do not struggle with a lack of data. They struggle with a lack of context.
Alerts fire. Vulnerabilities pile up. Suspicious activity appears across endpoints, identities, cloud services, and SaaS applications. But when every signal lives in a different place, analysts are left stitching together the story by hand.
That is why we are launching Sekoia Reveal.
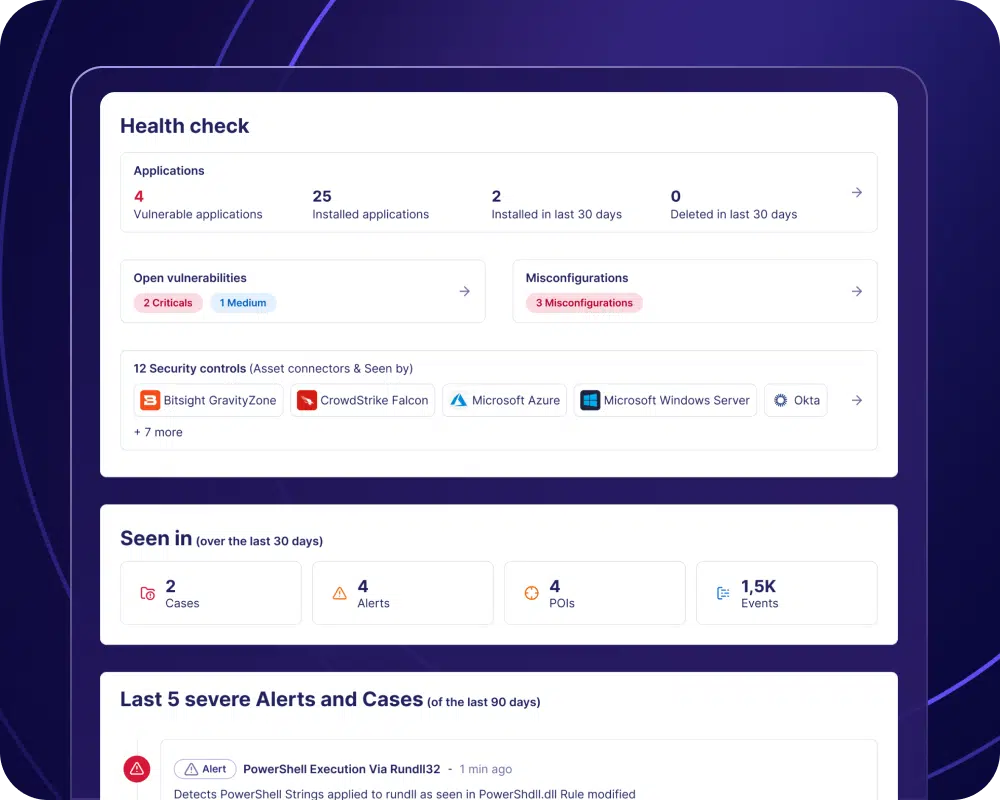
Sekoia Reveal brings asset intelligence into the SOC. It gives security teams a live, unified view of their assets, their exposures, their activity, and their security signals, so they can understand what matters faster and act sooner.
This is not just another asset inventory.
Too many solutions in the market stop at visibility. They can tell you what exists, but not what matters. They can list assets, but not explain the risk around them. They can surface findings, but leave analysts to do the hard work of connecting the dots.
We know that is a problem, because SOC teams do not need more lists. They need operational context.
Reveal is built for exactly that. It helps analysts investigate faster, detect weak signals earlier, prioritize risk with confidence, and eliminate the blind spots attackers count on.
Why we built Reveal
Modern attack surfaces change constantly.
Endpoints come and go. Identities multiply. Cloud resources spin up and disappear. Shadow IT creeps in quietly. Traditional inventories cannot keep up, and disconnected security tools only show fragments of the bigger picture.
The result is familiar to every SOC: too many alerts, not enough context, and too much time spent pivoting between tools.
Reveal changes that.
It connects asset discovery, vulnerabilities, behavioral signals, and detections into one operational view, so analysts can immediately see what an asset is, how risky it is, what is happening around it, and why it matters.
Because that is the real gap in most environments today: not the absence of security data, but the absence of security data that is usable in the moment.
What Reveal helps you do
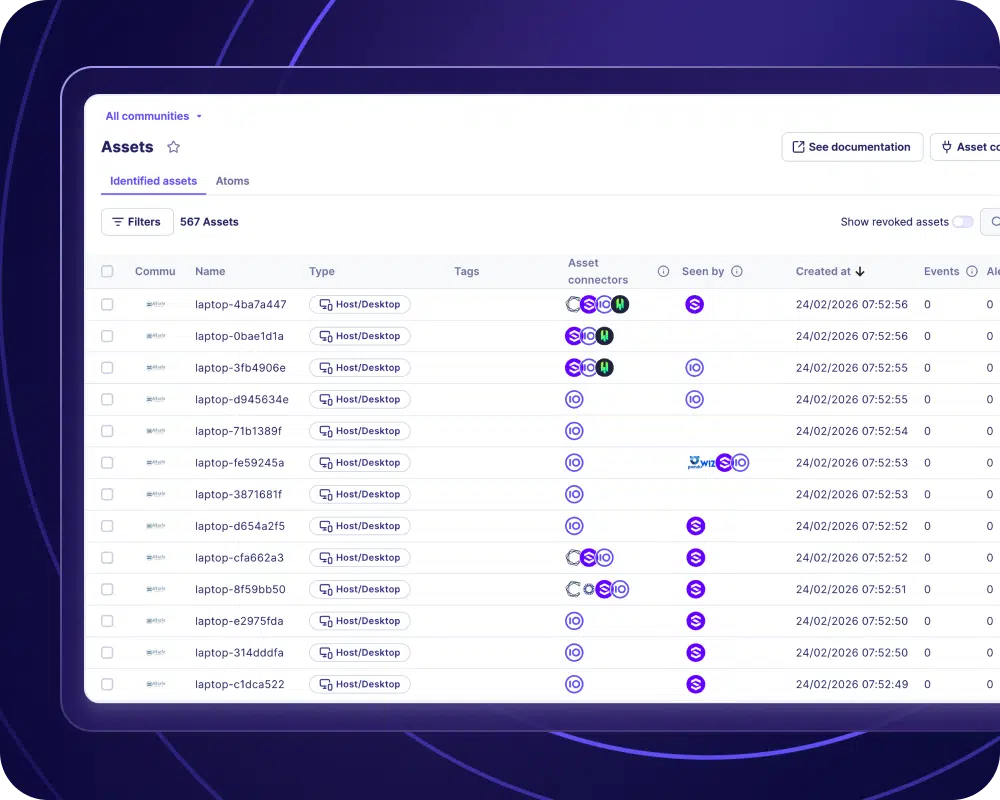
See what is really in your environment
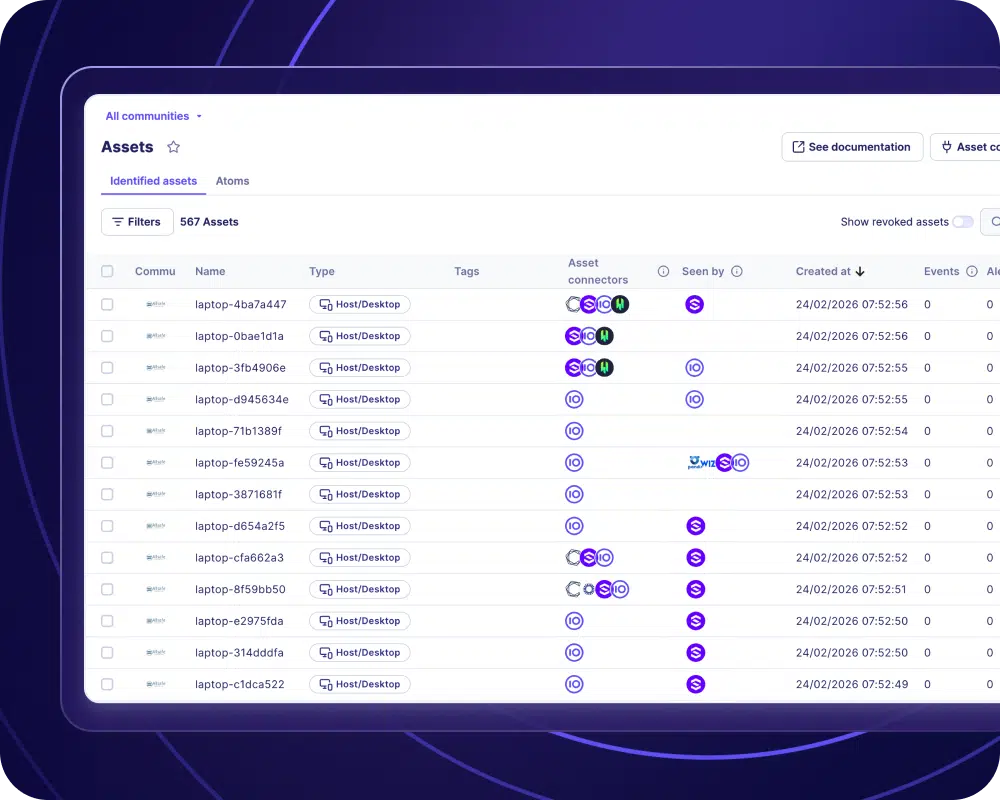
Reveal gives you a unified view of the assets that matter across your environment, including endpoints, identities, cloud resources, and connected services.
That means fewer unknowns, fewer unmanaged assets, and far less time spent figuring out whether a system is even visible to the SOC.
Many tools claim visibility, but visibility alone is not enough. Static inventories go out of date quickly, and isolated asset views rarely reflect what security teams are actually defending day to day.
Reveal is different because it is built for live security operations. It does not just show you assets. It helps you understand which ones matter, which ones are exposed, and which ones deserve attention now.
Catch weak signals earlier
Not every attack starts with a critical alert.
Some start with subtle anomalies, unusual behavior, or small signs of exposure that are easy to miss in isolation. Reveal helps surface these early indicators so your team can spot emerging risk before it becomes a full-blown incident.
This is another place where many approaches fall short. They are designed to highlight confirmed issues, not ambiguous signals that need context to become meaningful.
But defenders know weak signals matter. The problem is that most tools force analysts to find them manually across disconnected datasets.
Reveal is designed to bring those signals together early, while there is still time to act.
Prioritize the risks that actually matter
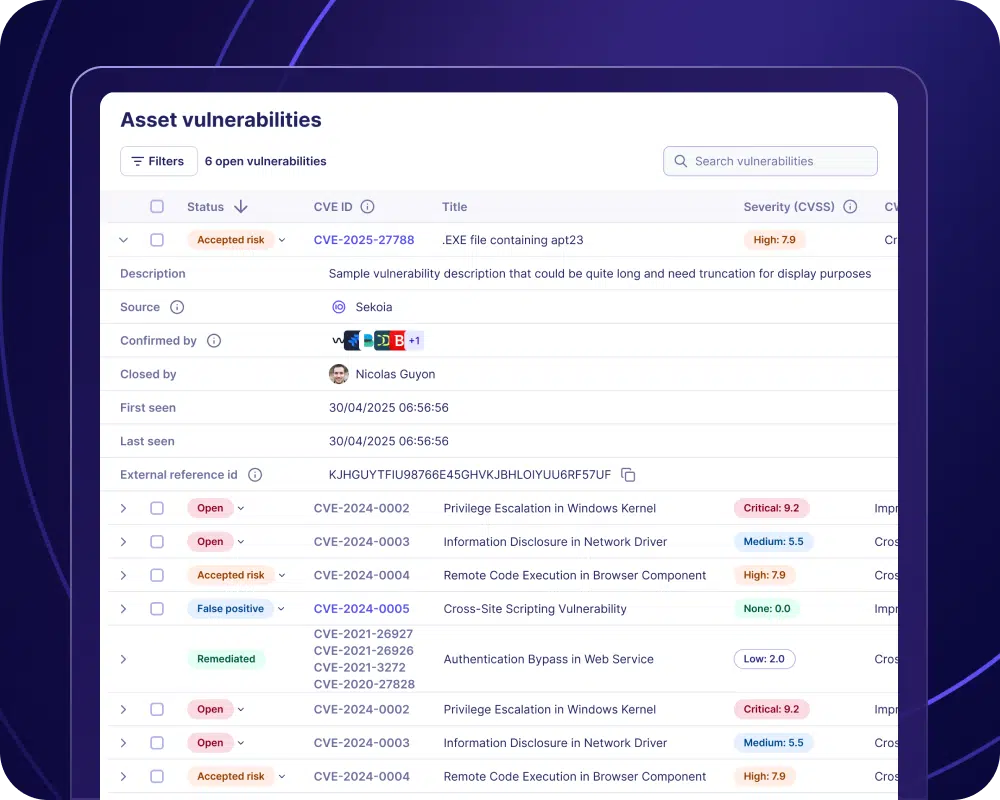
A vulnerability score alone does not tell you what to do first.
Reveal helps analysts prioritize by combining asset criticality, exposure, behavior, and detections in one place. Instead of treating every signal the same, teams can focus on the assets and events that create real business risk.
That matters because too many products still prioritize in silos. Vulnerability tools rank findings by severity. Detection tools rank alerts by confidence. Asset tools rank systems by ownership or type. But the SOC has to make decisions across all of these dimensions at once.
We built Reveal to solve that operational reality. It gives teams a way to prioritize risk in context, not in isolation.
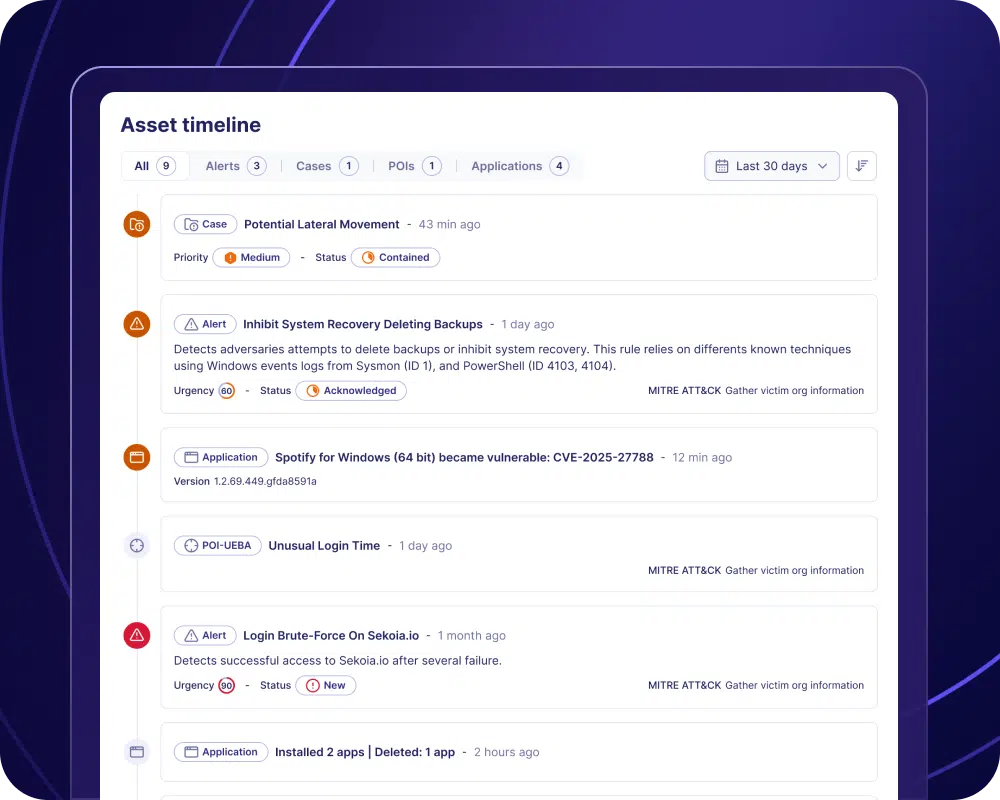
Investigate faster
Analysts should not have to open five tools to understand one alert.
Reveal puts asset context directly into investigations, so teams can move from detection to understanding much faster. When an alert fires, analysts can immediately see the asset involved, its risk profile, its history, and related signals without losing time on manual enrichment.
This is where many platforms still create friction. They may integrate data, but they do not operationalize it. Analysts still have to pivot between screens, rebuild timelines, and manually enrich alerts before they can make a decision.
We know that delay is costly. It slows triage, increases fatigue, and makes real threats easier to miss.
Reveal is built to remove that friction by making asset intelligence available where investigations actually happen.
Expose your coverage gaps
Attackers thrive in blind spots.
Reveal helps teams identify unmanaged systems, poorly monitored assets, and gaps in defensive coverage across the environment. That makes it easier to spot weak points early and improve visibility before they are exploited.
This is a critical weakness in many environments. Security teams often assume coverage because they have tools deployed, but deployed does not mean visible, monitored, or usable in practice.
Reveal helps close that gap. Instead of giving a false sense of completeness, it helps teams see where coverage is thin, where assets are slipping through, and where defensive visibility needs to improve.
Built for security operations, not just visibility
Reveal is designed to make asset intelligence usable inside the day-to-day workflow of the SOC.
It continuously brings together data from across the environment, enriches each asset with relevant security context, highlights what needs attention, and helps teams take action earlier.
That distinction matters.
There is no shortage of tools that collect data. The challenge is turning that data into something a SOC can use under pressure.
Reveal is built to do exactly that.
In practice, that means security teams can:
- understand their environment faster,
- detect risk earlier,
- investigate with better context,
- and make smarter prioritization decisions under pressure.
A better way to operate the SOC
The goal of Reveal is simple: help security teams spend less time chasing disconnected signals and more time focusing on what matters.
With Sekoia Reveal, your SOC can move from fragmented visibility to real operational clarity.
You see the assets.
You understand the risk.
You catch the weak signals.
You investigate faster.
You close the gaps before they become incidents.
That is the promise of Sekoia Reveal.
And that is why we built it the way we did: not to add another layer of data, but to solve the context problem that keeps slowing security teams down.
See it in action
For a full, self-guided demo, visit our dedicated Reveal page here.
如有侵权请联系:admin#unsafe.sh