March was a packed month for ANY.RUN. We rolled out major product improvements that help security teams investigate phishing inside encrypted traffic, expand cross-platform analysis with macOS, and bring Windows Server into the sandbox workflow.
At the same time, our detection team continued to strengthen threat coverage with new behavior signatures, Suricata rules, and fresh threat intelligence reports focused on active malware and attack techniques.
Here’s a closer look at what’s new.
Product Updates
This month’s updates are all about helping security teams see more and investigate with less friction. We improved phishing detection inside encrypted traffic, expanded sandbox coverage to macOS, and added Windows Server analysis so teams can work across more of the environments they protect every day.
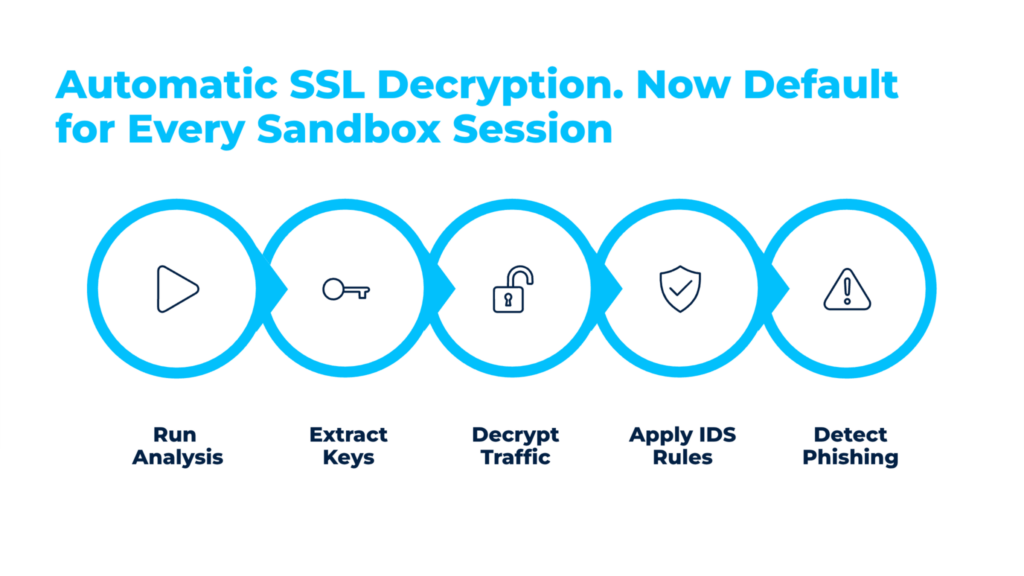
Automatic SSL Decryption for Stronger Phishing Detection
Encrypted HTTPS traffic remains one of the main reasons phishing is harder to confirm quickly. It hides credential theft, redirect chains, and token-based attacks inside traffic that often appears legitimate, forcing teams to spend more time on validation and increasing the chance of missed compromise.
In March, ANY.RUN introduced automatic SSL decryption in the Interactive Sandbox across all subscription tiers. By extracting encryption keys directly from process memory, the sandbox can now inspect decrypted traffic during analysis and apply Suricata rules, detection signatures, and IOC extraction immediately.
Check real-world example: Detecting Salty2FA phishing campaign with SSL decryption
This significantly expands phishing visibility across every sandbox session. After implementing the technology, ANY.RUN saw a 5x increase in SSL-decrypted phishing detection and added 60,000 more confirmed malicious URLs to TI Lookup each month.
For your SOC, this means:
- Higher detection rate: Analysts can now identify phishing activity that would otherwise stay hidden inside encrypted traffic.
- Faster MTTD and MTTR: Teams confirm malicious behavior earlier and respond before phishing causes broader damage.
- Reduced Tier 1-to-Tier 2 escalation volume: Tier 1 can close more cases independently and escalate only the incidents that truly need deeper investigation.
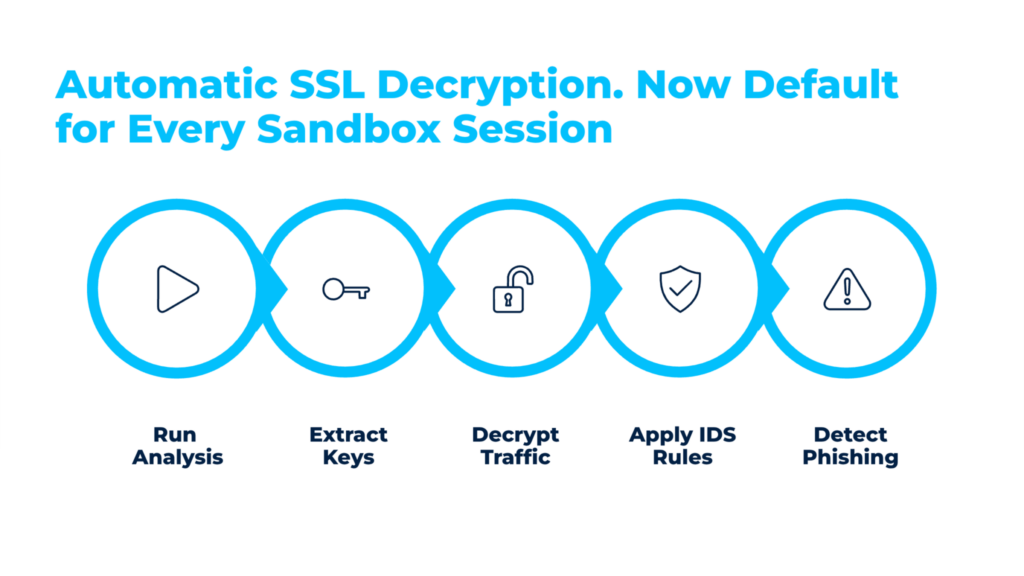
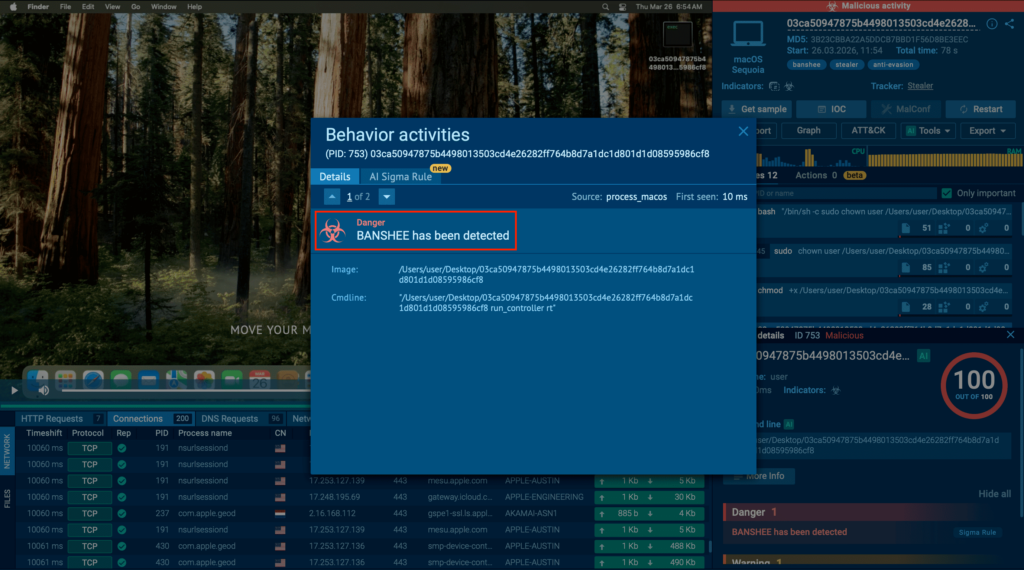
Expanding Your SOC’s Cross-Platform Analysis with macOS
As enterprise environments grow more complex, SOC teams are expected to investigate threats across multiple operating systems without slowing down triage. But when analysis is split across separate tools and environments, investigations take longer, alert backlogs grow, and the risk of delayed or missed detection increases.
To help solve this, ANY.RUN expanded its sandbox OS coverage with macOS virtual machine, now available in beta for Enterprise Suite users. This gives teams one environment to investigate threats across Windows, Linux, Android, and now macOS.
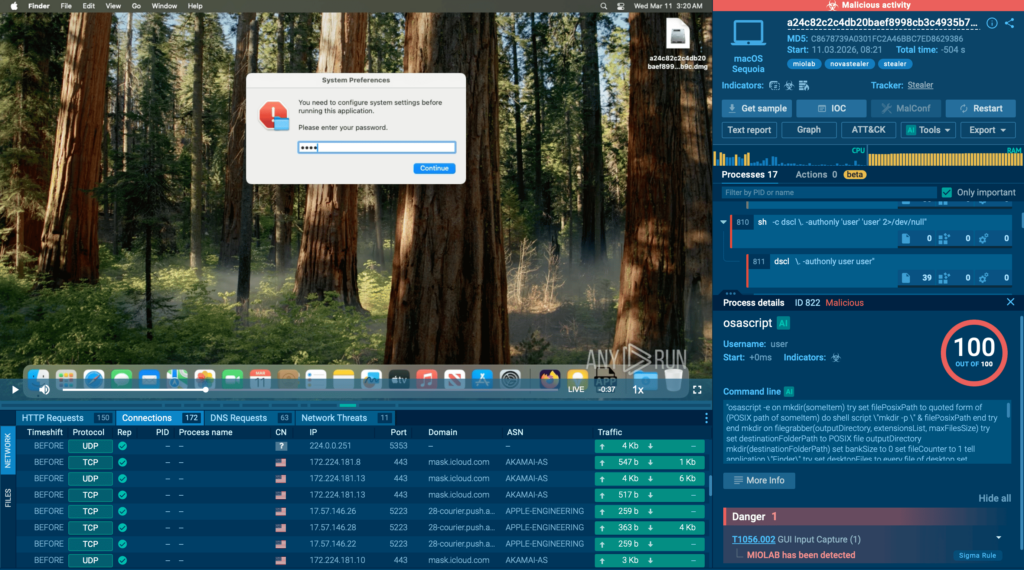
Bringing interactive macOS analysis into the workflow is especially important for threats that stay dormant until a user enters a password, approves a system dialog, or triggers another action. By allowing real user interaction during detonation, the sandbox can expose behaviors that automated analysis often misses, including fake authentication prompts, staged execution chains, file collection, and post-authentication data exfiltration.
This operational improvement leads to measurable outcomes:
- Faster validation of suspicious files and URLs: Teams can confirm malicious behavior in minutes through behavior-based analysis during triage.
- Shorter investigation cycles: Analysts can observe full execution behavior in one environment without manually piecing evidence together across multiple tools.
- Improved cross-platform detection coverage: Security teams can investigate platform-specific threats across macOS, Windows, Linux, and Android in a consistent workflow.
- Higher productivity during triage: Less context switching helps analysts process more alerts per shift.
- Reduced alert backlog during peak activity: Faster decisions help SOC teams keep queues under control during phishing waves and malware outbreaks.
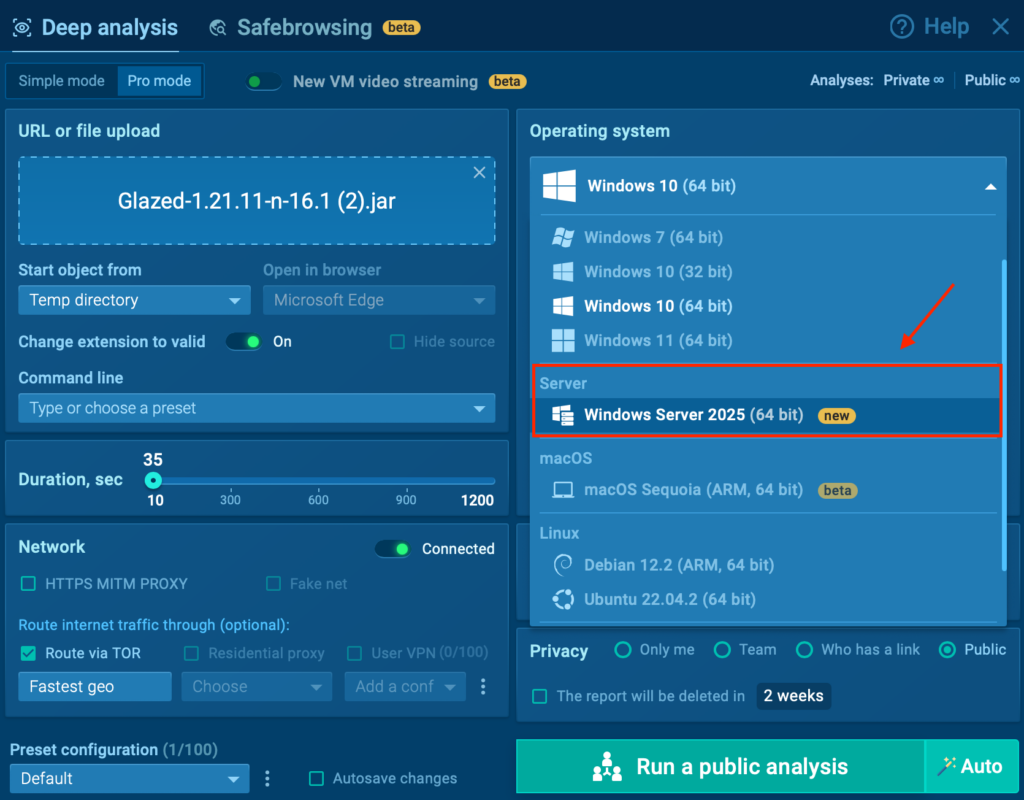
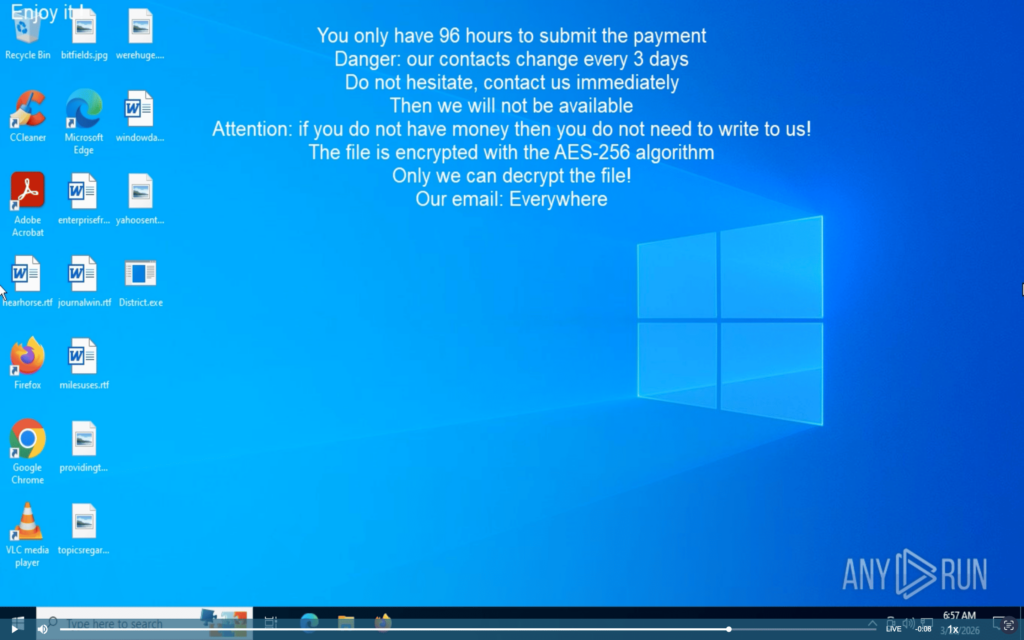
Advancing Server-Side Threat Analysis with Windows Server
For many enterprise teams, critical infrastructure runs on Windows Server, from domain services and file storage to business applications and backups. But malware that targets server environments often behaves differently from threats launched on standard Windows systems, making it harder to assess risk accurately in a desktop-focused setup.
To close that gap, ANY.RUN Sandbox now supports analysis in a Windows Server environment. This gives security teams a way to observe attack behavior in a server OS and investigate techniques tied to infrastructure, including changes to domain accounts, security policies, and the use of administrative tools.
This addition helps teams strengthen infrastructure-focused triage and response:
- Better visibility into server-specific techniques: Teams can analyze behavior tied to domains, policies, and administrative utilities in a more relevant environment.
- Stronger investigation confidence for infrastructure threats: Analysts can validate whether a sample affects server-side services or critical business systems before escalating.
- More effective detection and response preparation: Security teams can collect artifacts, refine detections, and improve incident playbooks for Windows Server scenarios.
Threat Coverage Updates
In March, our detection team continued to expand coverage across phishing, credential theft, backdoors, miners, stealers, loaders, and evasive system abuse.
This month’s updates include:
- 91 new behavior signatures
- 1,293 new Suricata rules
These additions give security teams better visibility into modern attack chains, from OAuth phishing and Telegram-based credential theft to backdoor communication, loader behavior, and suspicious use of built-in system tools.
New Behavior Signatures
In March, we added 91 new behavior signatures to strengthen detection across malware families, Android threats, stealers, loaders, RATs, ransomware, and suspicious system-level activity.
These updates improve visibility into behaviors often seen in real attacks, including persistence, self-deletion, loader activity, shell delivery, registry tampering, PowerShell abuse, and virtual machine checks used to evade analysis.
Highlighted families and detections include:
New behavior-based detections also cover:
- PhantomCore
- Delivers shell command via nslookup
Together, these additions give security teams broader behavioral coverage across both established malware families and attacker techniques that commonly appear in multi-stage intrusions.
New Suricata Rules
In March, we added 1,293 new Suricata rules to strengthen detection of credential theft, phishing activity, and malicious command-and-control traffic.
Key highlights include:
- Credential theft via Telegram API (sid: 84001778): Tracks adversary attempts to exfiltrate victim’s email & password via Telegram Bot API
- MS OAuth Device Code phish / EvilTokens activity (sid: 84001845): Identifies usage of emerged attack technique that exploits legitimate OAuth 2.0 device authorization flows to gain control over victims’ Microsoft 365 accounts
- DinDoor backdoor HTTP activity (sid: 85006556): Detects Iran-linked MuddyWater (TA450) actor’s new backdoor attempts to establish C2 communication via HTTP
Threat Intelligence Reports
In March, our team published new Threat Intelligence Reports on emerging malware, banking trojans, ransomware, backdoors, and stealthy delivery techniques.
Available as part of ANY.RUN’s TI Lookup Premium plan, these reports help security teams better understand active threats and investigate them with stronger context.
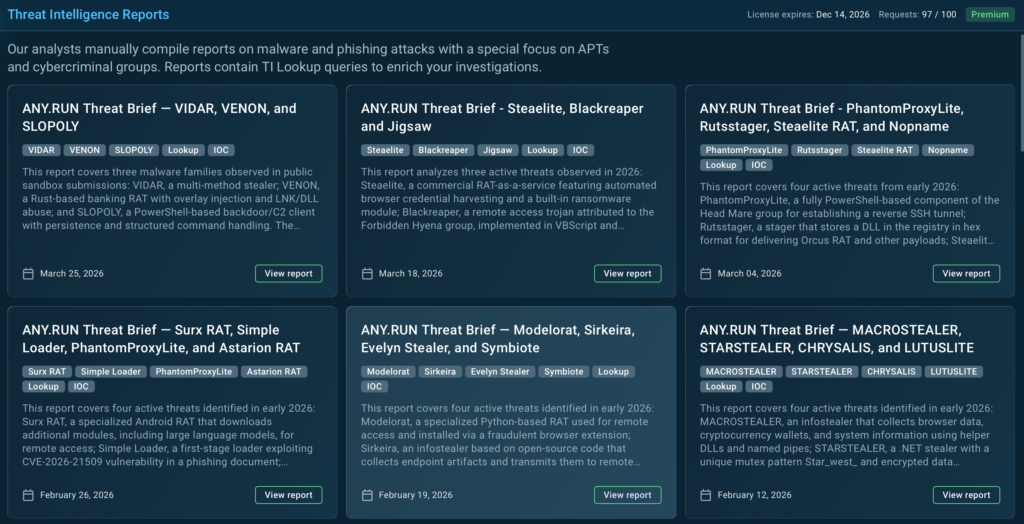
- VIDAR, VENON, and SLOPOLY: This report covers a polymorphic stealer, a Rust-based banking RAT, and a PowerShell backdoor tied to the Hive0163 ecosystem, with a focus on their behavior, artifacts, and detection opportunities.
- Steaelite, BlackReaper, and Jigsaw: This brief looks at three threats combining credential theft, remote access, persistence, and ransomware behavior, including Telegram-based control and file encryption activity.
- PhantomProxyLite, Rutsstager, Steaelite RAT, and Nopname: This report explores tunneling, registry-based staging, data theft, and ransomware, showing how these threats mix stealth techniques with clear forensic traces.
About ANY.RUN
ANY.RUN provides interactive malware analysis and threat intelligence solutions built to support modern security operations.
By combining Interactive Sandbox, Threat Intelligence Lookup, and Threat Intelligence Feeds, ANY.RUN helps SOC and MSSP teams accelerate threat analysis, investigate incidents with greater clarity, and detect emerging attacks earlier.
Used by more than 15,000 organizations and over 600,000 security professionals worldwide, including 74% of Fortune 100 companies, ANY.RUN is focused on helping teams improve detection and response while meeting the data protection, compliance, and workflow demands of real-world security operation
Integrate ANY.RUN’s solution for Tier 1/2/3 in your organization →