嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要理解文章的内容。文章讲的是一个叫做RoadK1ll的新恶意软件,它是一个Node.js植入程序,通过自定义的WebSocket协议进行通信,允许攻击者在受感染的主机上建立一个中继点,进而访问内部系统。 接下来,我需要提取关键信息:RoadK1ll的功能、发现者、工作原理、攻击手法以及缺乏持久性机制。然后,把这些信息浓缩成简短的句子,确保不超过100字。 可能会遇到的问题是如何在有限的字数内涵盖所有重要点。比如,RoadK1ll如何隐藏自己,攻击者如何利用它进行横向移动等。我需要选择最核心的信息来表达。 最后,检查总结是否符合用户的要求:直接描述内容,没有多余开头,并且控制在100字以内。确保语言简洁明了。 </think> 一种名为RoadK1ll的新恶意软件通过Node.js植入程序和自定义WebSocket协议,在受感染主机上建立中继点,使攻击者能够隐蔽地访问内部系统并扩展网络攻击范围。该恶意软件利用受感染设备的网络信任来绕过安全控制,并支持多连接同时通信。尽管缺乏传统持久性机制,但其灵活高效的隐蔽通信方式使其成为现代网络攻击中的有力工具。 2026-3-30 21:0:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:20 收藏

A newly identified malicious implant named RoadK1ll is enabling threat actors to quietly move from a compromised host to other systems on the network.
The malware is a Node.js implant that communicates over a custom WebSocket protocol to sustain ongoing attacker access and enable further operations.
RoadK1ll was discovered by managed detection and response (MDR) provider Blackpoint during an incident response engagement.
The researchers describe it as a lightweight reverse tunneling implant that blends into normal network activity and turns an infected machine into a relay point for the attacker.
"Its sole function is to convert a single compromised machine into a controllable relay point, an access amplifier, through which an operator can pivot to internal systems, services, and network segments that would otherwise be unreachable from outside the perimeter," Blackpoint says.
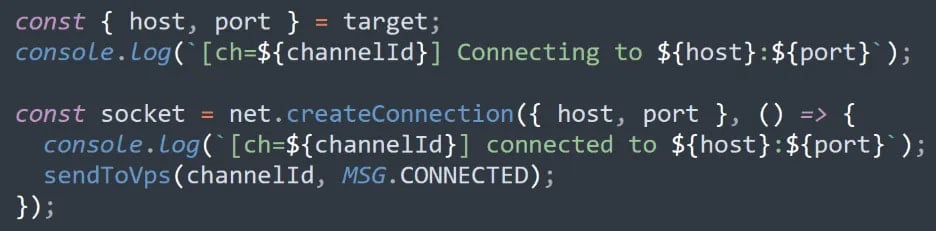
RoadK1ll does not rely on an inbound listener on the compromised host. It establishes an outbound WebSocket connection to attacker-controlled infrastructure, which is then used as a tunnel to relay TCP traffic on demand.
This approach allows the attacker to remain undetected for a longer period and forward traffic to internal systems through a single WebSocket tunnel.
“The attacker can instruct RoadK1ll to open connections to internal services, management interfaces, or other hosts that are not directly exposed externally,” Blackpoint says.
“Because these connections originate from the compromised machine, they inherit its network trust and positioning, effectively bypassing perimeter controls.”
Furthermore, RoadK1ll supports multiple concurrent connections over the same tunnel, allowing its operator to communicate with several destinations at once.
According to the researchers, the malware supports a small set of commands, which include:
- CONNECT – Instructs the implant to open a TCP connection to a specified host and port
- DATA – Forwards raw traffic through an active connection
- CONNECTED – Confirms that a requested connection was successfully established
- CLOSE – Terminates an active connection
- ERROR – Returns failure information to the operator
The CONNECT command triggers RoadK1ll’s primary function: initiating an outbound TCP connection to an adjacent target, extending the attacker’s reach into the compromised network.
Source: Blackpoint
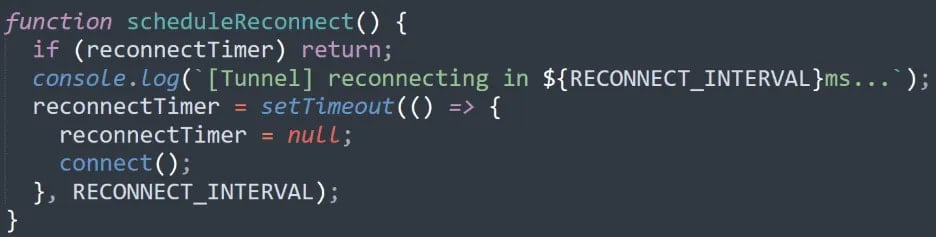
If the channel is interrupted, the tool attempts to restore the WebSocket tunnel using a re-connection mechanism, allowing the attackers to maintain persistent access without generating noise through manual intervention.
Source: Blackpoint
However, Blackpoint notes that RoadK1ll lacks a traditional persistence mechanism that uses registry keys, scheduled tasks, or services. Instead, it operates only as long as its process remains alive.
Despite this, the researchers say that the malware "shows a more modern and purpose-built implementation" of covert communication that makes it flexible, efficient, and easy to deploy.
It also allows the threat actor to move to internal systems and segments of the environment that are not reachable from outside the network.
Blackpoint provides a small set of host-based indicators of compromise that includes a hash for RoadK1ll and an IP address used by the threat actor for communication with the implant.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
