嗯,用户让我总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要通读整篇文章,抓住主要观点。 文章主要讲的是Claude Mythos这个AI模型泄露的情况,以及它对网络安全的影响。它提到这个模型能力很强,可能被用于网络攻击,比如数据窃取、漏洞利用等。然后文章讨论了现有的安全措施在面对AI攻击时的不足,并介绍了一个叫做Xshield AI的解决方案,强调微分段和集体防御的重要性。 接下来,我需要将这些要点浓缩到100字以内。要确保涵盖Claude Mythos的泄露、其潜在威胁、现有安全措施的不足以及Xshield AI的作用。 可能会这样组织:Claude Mythos泄露,具备强大能力;传统安全措施失效;Xshield AI通过微分段和集体防御提供实时保护。 最后检查一下字数和是否符合要求。 </think> Anthropic's unreleased AI model, Claude Mythos, was leaked, revealing its advanced capabilities in reasoning and cyber offense. Traditional security measures are inadequate against AI-driven attacks, which operate at machine speed. Xshield AI, part of the Breach Ready Collective, offers real-time containment through microsegmentation and collective defense mechanisms to counter intelligent adversaries. 2026-3-30 16:49:30 Author: securityboulevard.com(查看原文) 阅读量:8 收藏
Anthropic left details of an unreleased model, an invite-only CEO retreat, sitting in an unsecured data trove in a significant security lapse.
Leaked reports suggest this next-generation model from Anthropic is a major advancement in reasoning, coding, and cyber offense. Its capabilities are significant enough that its creators are cautious about a broad release due to potential risks. The emergence of Claude Mythos reminds me of the famous word.
It has become appallingly obvious that our technology has exceeded our humanity.
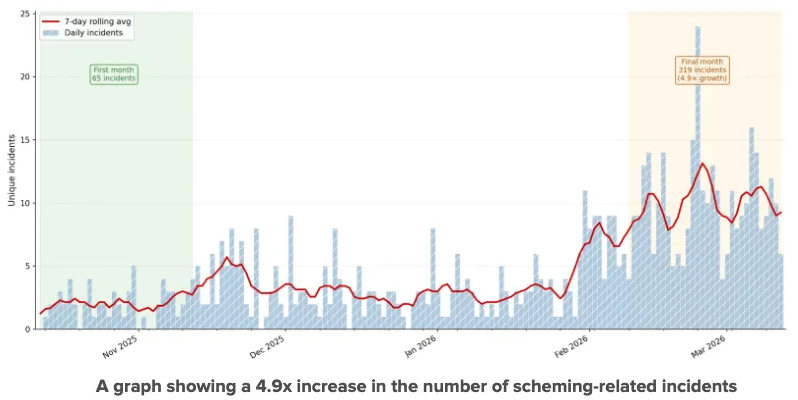
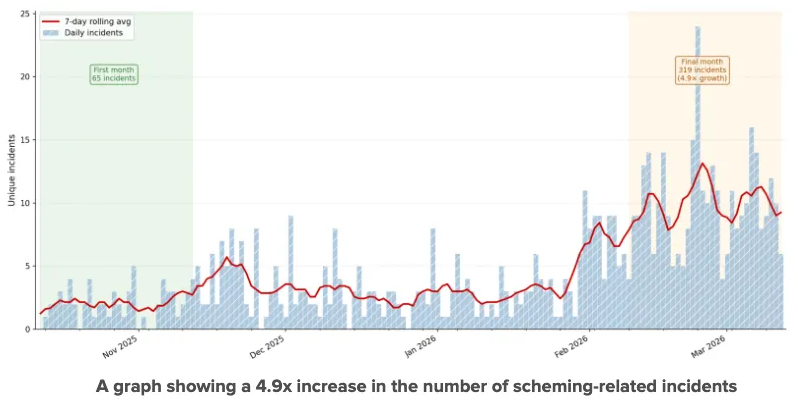
A recent industry research study, analyzing over 180,000 transcripts of user interactions with AI systems shared on X between October 2025 and March 2026, identified 698 scheming-related incidents involving AI systems. The number of credible scheming-related incidents increased 4.9x over the collection period, a statistically significant increase that far outpaced the 1.7x growth in overall online discussion of scheming, and the 1.3x growth in general negative discussion about AI.
This development warrants careful consideration. AI is no longer limited to assisting attackers. It can now research vulnerabilities, generate exploits, harvest credentials, scheme and deceive users, and autonomously orchestrate attacks, as demonstrated by earlier versions of Claude. This is not evolution. This is acceleration.
Access the 2026 GigaOm Radar for Microsegmentation: Know why ColorTokens was Named a Leader and Outperformer Again with a Perfect 5.0 Across Key Features
The New Threat Reality: AI as an Autonomous Adversary
This could not be more apparent.
- AI models have already been used to steal massive datasets from government systems.
- Prompt injection can turn AI into a data exfiltration engine. AI poisoning can turn a defender into an adversary.
- Agentic AI can autonomously identify vulnerabilities, generate exploits, and escalate access.
- AI agents can willingly disregard direct instructions, circumvent safeguards, lie to users, and single-mindedly pursue a malicious goal in multiple ways.
Mythos can significantly accelerate these attacks on enterprises that are marching towards previously declared goals of digital and AI-based innovation, but are NOT breach ready yet. The most disturbing development is that, amid increasing geopolitical instability, nation-state actors are now racing to use AI to scale attacks across dozens of organizations simultaneously.
This is the dawn of machine-speed cyber warfare, where:
- Reconnaissance happens in seconds.
- Exploits are generated on demand.
- Lateral movement is algorithmically optimized.
- Attacks adapt in real time.
In such a world, detection is too slow. Prevention is too brittle.
A dangerous narrative is emerging: “AI will secure everything.” Reality is harsher. While AI might accelerate defenders’ ability to detect cyberattacks, it will also supercharge attackers. And in that duality, one control becomes non-negotiable:
You must control how far an attacker can go.
Not just who they are.
Not just what they do.
But where can they move to without being challenged?
In a small footnote in his 1962 book Profiles of the Future, “An Inquiry into the Limits of the Possible”, Arthur C. Clarke, famously remarked in 1973, “Any sufficiently advanced technology is indistinguishable from magic.”
This may be akin to magic. The stock market sentiment was immediate, but is the industry prepared for this? Which brings us to a single, uncomfortable truth:
If your architecture cannot contain an AI-driven breach in real time, it is already obsolete.
The Most Critical Control in the AI Era is Xshield AI
This is where ColorTokens Xshield AI is not just relevant; it is foundational. It is important to note that AI like Mythos changes the speed at which attacks are launched; it does not change how attacks succeed.
Successful attacks have the same signature:
- Some initial breach
- Lateral movement
- Unauthorized access
- Privilege escalation
Lateral movement is where breaches become disasters.
Here’s the paradox. As AI becomes more powerful, it exposes a fundamental weakness in enterprise security:
Flat networks and implicit trust models cannot survive intelligent adversaries.
AI doesn’t break encryption.
It doesn’t magically bypass controls.
It simply finds the path of least resistance faster than any human ever could. And in most enterprises, that path is created by:
- Over-permissioned access
- Unsegmented workloads
- Uncontrolled vulnerable paths
- Implicit trust between systems
Breach-focused microsegmentation not only hides those paths but also ensures cyberattacks masquerading as valid users become visible by reducing the blast radius of digital systems.
Xshield’s Strategic Advantage… Hiding the Attack Path
Xshield operates on a simple yet devastating principle. Even if the attacker is inside, they go nowhere.
So when an AI like Mythos finds a vulnerability, gains initial access, and attempts to pivot…
It finds no path to pivot.
Not a perimeter firewall.
Not a detection alert.
A runtime-enforced, identity-aware, zero-trust barrier. From Reactive Security to a Breach-Ready Architecture
The question is no longer:
“Can we stop the attack?”
The question is:
“Can we survive it, elegantly and without significant material loss?”
ColorTokens has established Xshield as the core enforcement layer of breach readiness.
Xshield AI enforces least-privilege communication at the workload level, blocks east-west traversal across applications and environments, dynamically isolates compromised systems in real time, integrates with EDR and identity signals for instant containment, and establishes a Breach Ready Collective by channeling their strengths and enabling
1. AI-Resilient Runtime Environments
Even if AI agents are compromised:
- Their network reach is constrained.
- Their actions are contained.
- Their blast radius is minimized.
2. Autonomous Containment at Machine Speed
AI attacks operate in seconds. So must defense.
Xshield integrates with existing cybersecurity tools to trigger instant segmentation responses that isolate threats before they propagate.
3. Protection Across Critical Industries
From healthcare to energy, banking to manufacturing:
- Healthcare → Protect patient data and medical devices.
- Manufacturing → Secure OT systems and production lines
- Energy & Utilities → Prevent grid disruption.
- Banking → Contain fraud propagation.
- Critical Infrastructure → Ensure operational continuity
In these sectors, a breach is not just data loss; it has real-world consequences. And if the attackers can form a Collective, so can the defenders.
The ColorTokens Breach Ready Collective: From Control to Cohesion
If microsegmentation is the control plane of traffic management, then the Breach Ready Collective is the force multiplier that turns isolated controls into a coordinated cyber defense system.
Because here’s the gap most enterprises still struggle with:
They have tools.
They have telemetry.
They even have automation.
But they don’t have cohesion.
And in the age of AI-driven attacks, cohesion is everything.
The Breach Ready Collective (BRC) is not a product. It is an integration-first operating model that unifies multiple technologies, using Xshield as the foundational connector that shares telemetry, intelligence, and directives to form a bidirectional, intelligence-driven response fabric.
Think of it as moving from tools that detect and respond to systems that anticipate, contain, and adapt — together. These technologies include, but are not limited to, EDR/XDR platforms, Cryptographic and Passwordless Identity and access systems, Secure Access Service Edge, the SIEM/SOAR, cloud and workload security, and OT/IoT cybersecurity.
Why the Collective Matters in the Age of AI Adversaries
AI-powered threats like advanced Claude variants fundamentally change the game:
- They chain attack steps.
- They adapt to defenses in real time.
- They move laterally at machine speed.
No single control, not EDR, not SIEM, not identity, can keep up alone. Especially not when they are exploiting a zero-day vulnerability whose patching cycle may be next weekend.
The Breach Ready Collective solves this by ensuring:
 Every signal becomes an action.
Every signal becomes an action.
 Every action reinforces containment.
Every action reinforces containment.
 Every control learns from every other control.
Every control learns from every other control.
How the Breach Ready Collective Enhances Breach Readiness
Within the Breach Ready Collective
- Xshield AI is the enforcement engine
- EDR/XDR is the detection layer
- Identity is the trust arbiter
- SIEM/SOAR is the orchestration layer
- AI is the acceleration layer
This seamless collective provides unprecedented value to build breach-readiness.
1. Bidirectional Intelligence Flow (Not Just Integration)
Traditional integrations are one-way:
- EDR → SIEM
- SIEM → SOAR
The Collective is bidirectional:
- EDR detects anomaly → Xshield enforces segmentation
- Xshield observes blocked lateral movement → feeds back into SIEM for threat context
- Identity system flags risky login → triggers microsegmentation tightening
- AI analytics identify attack patterns → update segmentation policies
 This creates a closed-loop defense system
This creates a closed-loop defense system
2. Machine-Speed Containment
AI attacks don’t wait for playbooks.
The Collective enables:
- Instant isolation of compromised workloads
- Dynamic policy updates across environments
- Automated enforcement without human bottlenecks
 This is how you match AI attack speed with AI-assisted defense speed
This is how you match AI attack speed with AI-assisted defense speed
3. Attack Surface Compression in Real Time
Instead of reacting after compromise, the Collective:
- Continuously recalculates trust boundaries
- Shrinks communication paths dynamically
- Removes unnecessary access pathways
 The attack surface becomes fluid — and hostile to attackers
The attack surface becomes fluid — and hostile to attackers
4. Context-Rich Decisioning
A single alert is noise.
Correlated intelligence is a signal.
The Collective combines:
- Identity context (who)
- Device posture (what)
- Network behavior (where)
- Application dependencies (why)
 Result: high-confidence, low-noise automated actions
Result: high-confidence, low-noise automated actions
5. AI-Augmented Defense Without AI Blind Spots
AI introduces a paradox:
- It enhances detection
- But also introduces new attack vectors (prompt injection, agent misuse)
The Collective mitigates this by:
- Segmenting AI systems themselves
- Limiting their network reach
- Monitoring their behavior across systems
 Even if an AI agent is compromised, it is contained by design
Even if an AI agent is compromised, it is contained by design
The Collective Works for Both Greenfield and Greyfield Enterprises
In greenfield situations, the Collective builds integrated security from day one by embedding microsegmentation into application design and aligning DevSecOps with runtime enforcement
 Outcome: secure-by-design digital platforms
Outcome: secure-by-design digital platforms
In real-world greyfield situations, the Collective layers over existing tools, integrating without rip-and-replace, by prioritizing high-risk microsegments first, progressively reducing breach exposure.
 Outcome: incremental, high-impact transformation
Outcome: incremental, high-impact transformation
In a world of AI-driven cyberattacks:
- Detection alone is insufficient
- Prevention alone is unrealistic
- Response alone is too late
What enterprises need is:
A continuously adapting, tightly integrated, containment-first defense fabric
That is what the Breach Ready Collective delivers.
If Xshield ensures that a breach doesn’t spread,
The Breach Ready Collective ensures that:
A breach doesn’t spiral.
It aligns people, processes, and technologies into a single, resilient cyber organism that can withstand, adapt, and continue operating even under attack.
Claude Mythos is not the endgame.
It is the signal.
A signal that cybersecurity has entered a new phase:
- Where intelligence is automated
- Where attacks are adaptive
- Where speed is weaponized
In this world:
- Firewalls are too coarse
- Detection is too late
- Response is too slow
Only foundational architectural controls survive.
And microsegmentation enhanced through The Breach Ready Collective becomes the last line of defense that actually holds.
Call to Action: Build for the Breach Before the Breach Builds You
If AI can design attacks faster than your SOC can respond, you do not have a tooling problem. You have an architecture problem. The question is simple: if Mythos breached your environment today, how far would it go? If you do not know, or do not like the answer, now is the time to act.
Start with a Free Breach Readiness Impact Assessment to map your exposure, identify your blast radius, and design your cyber defense with a clear understanding of what is truly at stake. Define the minimum viable digital business you need to protect, align on the level of material impact your stakeholders would accept, and build from there. By connecting your existing investments to Xshield AI, you can begin building the Breach Ready Collective without starting from scratch.
In the age of AI-powered adversaries, survival is not about stopping every attack. It is about making sure the breach stops where it started. Be Breach Ready.
If you want to know how ColorTokens can help, get in touch with one of our top advisors.
The post Breach Readiness in the Age of Mythos: When Your AI Thinks, Learns, and Defends appeared first on ColorTokens.
*** This is a Security Bloggers Network syndicated blog from ColorTokens authored by Agnidipta Sarkar. Read the original post at: https://colortokens.com/blogs/breach-readiness-ai-attacks-microsegmentation/
如有侵权请联系:admin#unsafe.sh