嗯,用户让我总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头。直接写描述就行。好的,首先我需要通读一下这篇文章,理解它的主要观点。 文章讲的是Handala生态系统,它被描述为一个网络行动者,但实际上更像是一个叙事放大引擎。也就是说,它主要通过放大有限的访问权限、真实事件和未经验证的声明来制造心理和媒体效果。文章提到Handala与伊朗相关的网络集群有关联,但其技术能力并不持续或复杂,而是依赖于战略性的叙事放大。 Handala的运作模式是将网络活动作为叙事生产的原材料,而不是最终目标。他们通过钓鱼、社会工程等手段获取凭证,然后夸大成系统性入侵或破坏能力。这种模式下,技术现实和公众认知之间的差距是故意的,以达到最大的影响。 文章还举了Kash Patel事件的例子,说明即使是一个个人账户的入侵也能引起媒体和公众的广泛关注。Handala通过这种方式将每个事件转化为影响力倍增器。此外,Handala还利用模糊性来维持媒体兴趣和延长事件生命周期。 总的来说,Handala的成功在于信息环境的利用,而不是持续的技术入侵。他们的影响力主要来自于如何将活动转化为关注和心理影响。 现在我需要把这些要点浓缩到100字以内。要抓住Handala作为叙事放大引擎的特点,他们的运作模式依赖于有限的技术能力和战略性的放大策略。还要提到他们利用模糊性和媒体周期来扩大影响。 可能的总结结构:Handala作为一个网络行动者,主要通过有限的技术能力和战略性的叙事放大来制造影响力。他们利用钓鱼、社会工程等手段获取凭证,并夸大成系统性入侵或破坏能力。通过模糊性和媒体周期扩大影响。 检查一下字数是否在100字以内,并且直接描述内容。 </think> Handala 是一个以叙事放大为核心的网络行动者,主要通过有限的技术能力和战略性的信息传播制造影响力。其运作依赖于钓鱼、社会工程等手段获取凭证,并夸大成系统性入侵或破坏能力。通过模糊性和媒体周期扩大影响,在心理和声誉层面施加压力而非持续技术入侵。 2026-3-30 16:15:39 Author: krypt3ia.wordpress.com(查看原文) 阅读量:22 收藏
Operational Overview
The Handala ecosystem presents itself as a capable cyber actor, but the available evidence indicates it functions more accurately as a narrative amplification engine effectively a hype machine operating under the guise of cyber operations. While the group, variously linked in open-source reporting to Iranian state-aligned clusters such as MuddyWater (Seedworm / MERCURY / Static Kitten / Mango Sandstorm / MOIST GRASSHOPPER) and broader MOIS-associated activity, does demonstrate episodic technical capability, its operational model does not rely on sustained or sophisticated intrusion. Instead, it depends on the strategic amplification of limited access, selectively real events, and often unverified claims into outsized psychological and media effects.
In this model, cyber activity serves primarily as raw material for narrative production, not as the end objective. Individual compromises frequently enabled through credential theft, phishing, or social engineering are elevated into claims of systemic breach, strategic penetration, or destructive capability. The gap between technical reality and public perception is not incidental; it is central to the group’s effectiveness. Handala’s operations consistently demonstrate that perceived access is operationally sufficient, even when underlying evidence is minimal or absent.
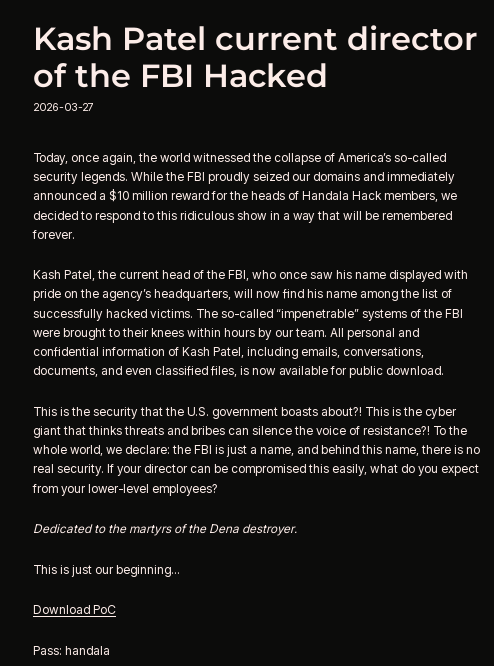
The response cycle surrounding the breach of Kash Patel illustrates this dynamic with particular clarity. The compromise itself was limited to a personal account and contained no classified material, yet the incident generated disproportionate attention across media, government, and public discourse. This amplification effect was not accidental. It reflects a deliberate reliance on the modern news and social media cycle as an extension of the operation itself. By releasing material in a way that guarantees coverage, Handala effectively outsources the scaling of its influence to journalists, analysts, and online platforms, turning each incident into a multiplier event.
This pattern is consistent across the broader campaign. Claims tied to individuals such as Sima Shine or Eran Ortal are framed in maximalist terms large-scale email leaks, strategic document exposure yet rarely produce verifiable downstream consequences beyond reputational pressure. Even in cases where real disruption occurs, such as the incident involving Stryker Corporation, the rarity of such events reinforces the broader pattern: technical impact is the exception, while narrative amplification is the rule.
The group’s persistent use of ambiguity further supports this assessment. By avoiding detailed technical disclosure, Handala ensures that claims cannot be easily falsified, while still compelling investigation and response. This ambiguity sustains media interest and prolongs the lifecycle of each incident, effectively stretching limited technical activity into extended influence operations. In practice, the group is not maximizing technical penetration it is maximizing attention, uncertainty, and perceived reach.
Ultimately, Handala’s effectiveness is less a function of cyber capability than of information environment exploitation. Its operations are designed to intersect with and depend upon the rhythms of the media cycle. The Patel incident demonstrates that even a relatively minor compromise can achieve strategic effect when amplified through news coverage and public discourse. In this sense, Handala operates not just as a cyber actor, but as a producer of narrative events, calibrated to trigger and exploit the feedback loops of modern information ecosystems.
The result is a campaign in which the true center of gravity is not network access or persistence, but visibility and amplification. Cyber activity provides the pretext, but the outcome is driven by how effectively that activity is translated into attention. Handala’s success, therefore, lies not in what it can consistently hack, but in how effectively it can make the world believe that it has.
Technical Effectiveness (Selective but Credible)
At the technical level, Handala exhibits uneven but meaningful capability. The attack against Stryker Corporation represents a confirmed high-impact operation, involving disruption to manufacturing, logistics, and enterprise systems, as well as large-scale device wiping. This incident establishes that the group can, under certain conditions, execute destructive or disruptive cyber operations against enterprise environments.
However, such cases are infrequent. The majority of claimed operations lack independent verification of comparable impact. As a result, technical effectiveness should be assessed as episodic rather than systemic, serving primarily to establish credibility rather than define the campaign’s core capability.
Exposure and Reputational Impact
The most consistent and reliable dimension of Handala’s effectiveness lies in exposure-driven operations. The compromise and publication of personal data associated with Kash Patel demonstrates how relatively limited access can produce significant reputational and counterintelligence consequences. Similarly, repeated targeting of individuals such as Sima Shine, Ilan Steiner, Deborah Oppenheimer, and Eran Ortal reflects a deliberate strategy of elite-focused hack-and-leak operations.
In these cases, the impact is not operational disruption but reputational degradation and perception management. The framing of large-scale email leaks whether fully substantiated or not—serves to project institutional vulnerability and undermine confidence in leadership and security structures.
Underlying Causes and Access Mechanisms

The effectiveness of these operations is closely tied to their underlying causes. Across the dataset, the dominant access vector is credential compromise at the identity layer, achieved through phishing, credential harvesting, password reuse, and OTP interception. These methods exploit human behavior rather than technical vulnerabilities, making them both scalable and difficult to fully mitigate.
Social engineering plays a central role, particularly when combined with geopolitical context that increases urgency and emotional susceptibility. High-value targets often operate across personal and professional digital environments with inconsistent security controls, creating exploitable gaps. In this model, the success of operations is driven less by advanced exploitation and more by systematic exploitation of identity-layer weaknesses and human factors.

Strategic Assessment
Handala’s effectiveness is best understood as the interaction of three core elements:
- Selective technical capability providing occasional high-impact events
- Consistent exposure operations driven by identity compromise and social engineering
- Narrative amplification and ambiguity transforming events into sustained influence operations
This combination produces a campaign that is resilient, scalable, and capable of imposing costs without requiring continuous technical success.
Conclusions
Handala is best understood as an effective cyber-enabled influence actor with selective disruptive capability. Its strength does not lie in consistent technical sophistication, but in its ability to exploit human vulnerability, leverage ambiguity, and control narrative dissemination at scale.
The campaign diverges from traditional cyber threat models. Rather than sustained, high-end intrusions, Handala employs a hybrid approach in which limited or episodic access is amplified through disciplined messaging, targeted victimology, and multi-platform distribution. As a result, effectiveness is measured less by depth of compromise and more by psychological, reputational, and strategic impact.
Technically, the group demonstrates credible but uneven capability. The attack against Stryker Corporation shows it can conduct disruptive operations against enterprise environments. However, such events are rare. Most activity lacks independently verified operational impact, indicating that technical success functions primarily as a credibility anchor rather than a consistent capability.
Handala’s core effectiveness lies in exposure operations. Incidents involving Kash Patel and Israeli intelligence figures illustrate how limited access can produce disproportionate reputational and psychological effects. These operations are typically enabled by credential compromise and social engineering, exploiting identity-layer weaknesses rather than network-level vulnerabilities.
The campaign scales further through targeting of civilian and dissident networks, such as VahidOnline, where data exposure becomes a tool of intimidation. This expands impact from individuals to communities, reinforcing a coercive dimension without requiring advanced technical tradecraft.
A defining feature of Handala’s effectiveness is its use of ambiguity. Most claims are not supported by verifiable artifacts, yet still compel investigation, media coverage, and defensive response. In practice, the possibility of compromise often produces the same effect as confirmed compromise, allowing the group to achieve disproportionate influence with limited technical input.
This extends into strategic signaling. Claims of access to critical infrastructure whether substantiated or not function as deterrence messaging, shaping perception and introducing uncertainty into decision-making processes. In this model, psychological operations can substitute for technical capability.
The campaign’s resilience is reinforced by its architecture. Disposable domains such as handala-team and handala-hack variants act as narrative anchors, while Telegram and X provide amplification. Even when infrastructure is disrupted, the narrative persists through consistent branding and rapid reconstitution.
Overall, Handala’s effectiveness is driven by the interaction of three elements: selective technical capability, consistent exposure operations enabled by identity compromise, and narrative amplification through ambiguity. This combination allows the group to impose real costs operational, reputational, and cognitive without requiring sustained technical success.
如有侵权请联系:admin#unsafe.sh


