
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解其主要内容。 文章主要讲的是Fortinet的FortiClient EMS平台存在一个严重的SQL注入漏洞(CVE-2026-21643),攻击者正在积极利用这个漏洞。这个漏洞允许未经身份验证的攻击者通过恶意HTTP请求执行任意代码或命令。虽然CISA和其他已知被利用的漏洞列表中尚未标记此漏洞为已被利用,但根据Defused的数据,攻击已经在四天前开始了。 接下来,我需要提取关键信息:漏洞名称、影响版本、攻击方式、暴露数量以及修复建议。然后将这些信息浓缩成一句话,确保不超过100字。 可能的结构是:FortiClient EMS平台存在SQL注入漏洞,允许攻击者执行任意代码;已有千余实例暴露在线;建议升级到7.4.5或更高版本修复。 现在检查字数是否在限制内,并确保信息准确无误。 </think> FortiClient EMS平台存在SQL注入漏洞(CVE-2026-21643),允许攻击者通过恶意HTTP请求执行任意代码;已有千余实例暴露在线;建议升级到7.4.5或更高版本修复。 2026-3-30 08:1:16 Author: www.bleepingcomputer.com(查看原文) 阅读量:28 收藏

Attackers are now actively exploiting a critical vulnerability in Fortinet's FortiClient EMS platform, according to threat intelligence company Defused.
Tracked as CVE-2026-21643, this SQL injection vulnerability allows unauthenticated threat actors to execute arbitrary code or commands on unpatched systems through low-complexity attacks targeting the FortiClientEMS GUI (web interface) via maliciously crafted HTTP requests.
"Fortinet Forticlient EMS CVE-2026-21643 - currently marked as not exploited on CISA and other Known Exploited Vulnerabilities (KEV) lists - has seen first exploitation already 4 days ago according to our data," Defused warned over the weekend.
"Attackers can smuggle SQL statements through the 'Site'-header inside an HTTP request. According to Shodan, close to 1000 instances of Forticlient EMS are publicly exposed."
The vulnerability, discovered internally by Gwendal Guégniaud of the Fortinet Product Security team, affects FortiClient EMS version 7.4.4 and can be patched by upgrading to version 7.4.5 or later.
Fortinet has yet to update its security advisory and flag the vulnerability as exploited in the wild. BleepingComputer reached out to a Fortinet spokesperson to confirm reports of active exploitation, but a response was not immediately available.
Internet security watchdog group Shadowserver is currently tracking over 2,000 FortiClient EMS instances with their web interfaces exposed online, with more than 1,400 IPs in the United States and in Europe.
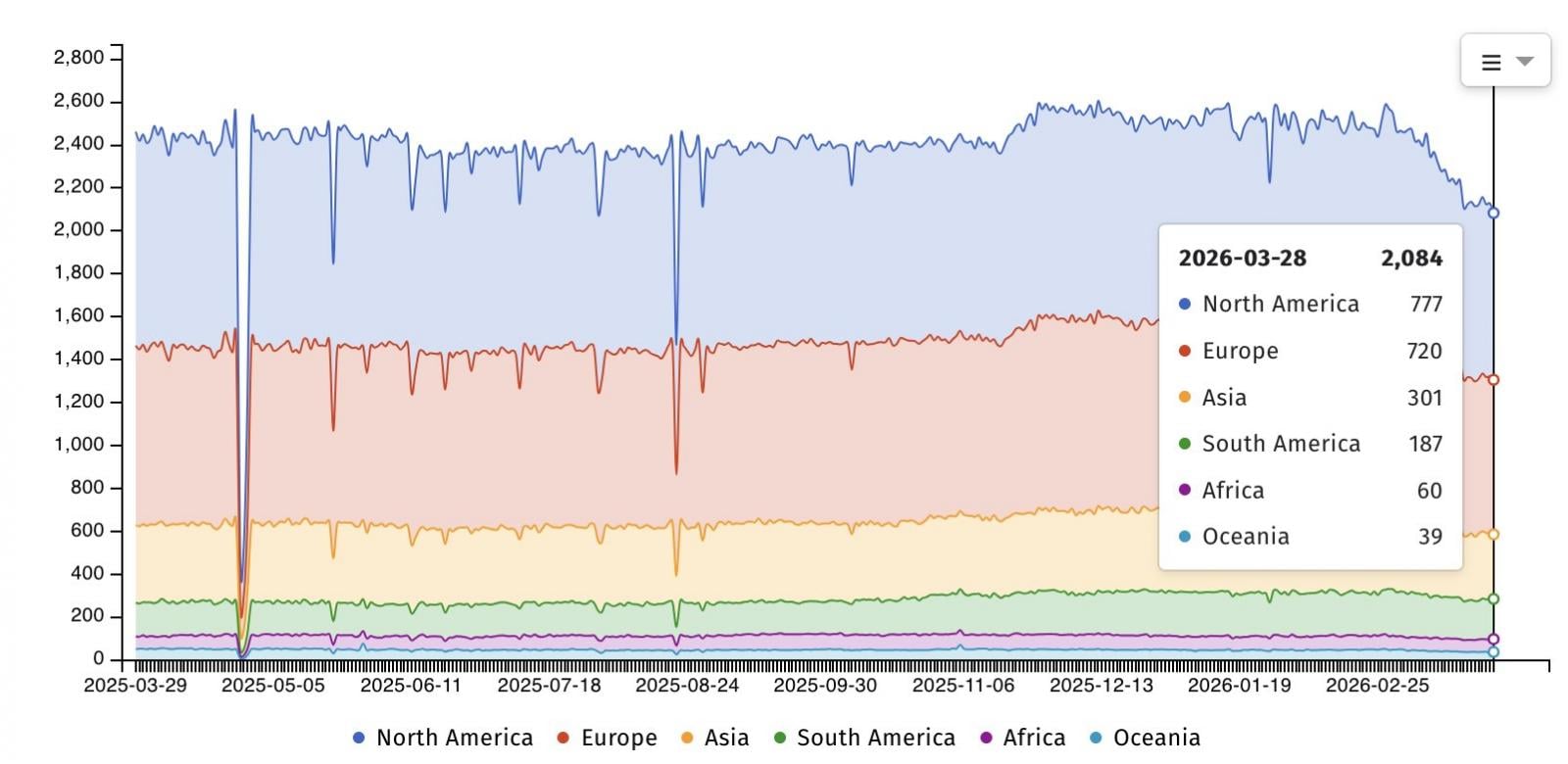
A separate Shodan search shows more than FortiClient EMS, with most exposed instances in the United States.
Fortinet vulnerabilities are frequently exploited to breach corporate networks in ransomware attacks and cyber espionage campaigns (often as zero-day bugs while patches are still pending).
Most recently, Fortinet mitigated CVE-2026-24858 zero-day attacks by blocking FortiCloud SSO connections from devices running vulnerable firmware versions.
Two years ago, in March 2024, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) ordered federal agencies to patch another FortiClient EMS SQL injection vulnerability that had been exploited in ransomware attacks and by Salt Typhoon, a Chinese state-sponsored hacking group, to breach telecommunications service providers.
In total, CISA has flagged 24 Citrix vulnerabilities as actively exploited, 13 of which were used in ransomware attacks.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
