嗯,用户让我帮忙总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”这样的开头。首先,我需要仔细阅读这篇文章,理解其主要内容和重点。 文章主要讨论了2025年下半年网络安全的威胁趋势。里面提到了勒索软件仍然流行,攻击者利用安全漏洞进入设备,甚至通过供应链攻击。恶意软件的传播方式也在变化,比如加载器和窃取器活动频繁。社会工程学仍然是主要的入侵手段,ClickFix技术让攻击者将执行步骤转移到用户身上。 此外,攻击者利用了各种文件格式和渠道来隐藏恶意行为,比如SVG钓鱼、QR码钓鱼等。AI在攻击中的应用也变得更加明显,虽然主要用于加速现有攻击手段,而不是完全自主的威胁。跨平台的攻击活动也很活跃,Linux和macOS系统都受到了不同程度的影响。 总结下来,文章强调了攻击者不断优化速度和规模的能力,通过快速入侵、隐藏自身以及通过盗窃、勒索或长期控制来获利。这些都是当前网络安全面临的主要挑战。 现在我需要把这些要点浓缩到100字以内,并且直接描述内容,不需要任何开头语。确保涵盖主要趋势、技术变化和社会工程学的应用。 </think> 2025年下半年网络安全威胁持续演变:勒索软件流行、供应链攻击频繁、恶意软件传播方式快速变化;社会工程学仍是主要入侵手段;AI加速攻击;跨平台攻击活跃;文件格式与渠道多样化隐藏恶意行为;技术与目标多样化推动威胁升级。 2026-3-27 08:25:20 Author: www.vmray.com(查看原文) 阅读量:18 收藏
/ / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / /
The second half of 2025 highlights a familiar pattern: ransomware remained a popular payload for attackers, while the paths into devices kept changing.
Public leak sites continued to grow, and break-ins often started with quickly abused security vulnerability, sometimes through supply chain attacks. At the same time, loader and stealer activity showed how fast delivery tools rotate: some stealers dropped sharply overall after a mid-year disruption through law enforcement, while others surged as a service to install ransomware and info-stealers.
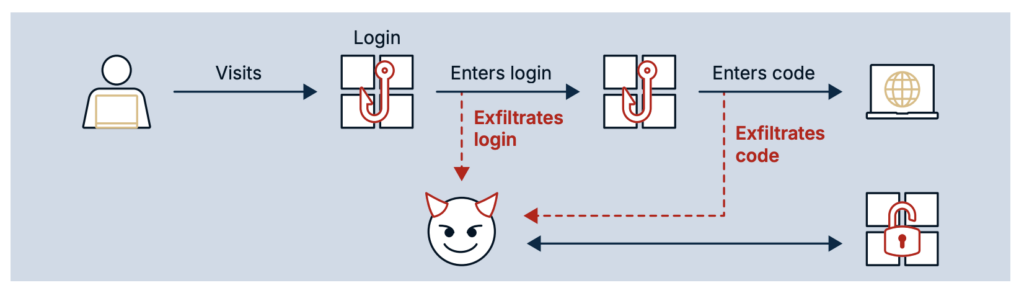
A major theme this period was social engineering that pushes the execution step onto the user. ClickFix keeps its position as a mainstream initial access method, with lures that look like normal troubleshooting or verification flows and end in copy/paste commands.
CAPTCHA use also changed shape: beyond blocking scanners with slider challenges or fake Cloudflare-style interstitials, attackers used CAPTCHA pages as part of the PasteJacking persuasion, guiding victims to run commands that trigger infection.
Attackers also leaned into file formats and channels that blend in. SVG-based phishing spiked as adversaries used SVG’s ability to carry scripts to turn “images” into a threat, while mail clients started to restrict some risky inline rendering paths.
QR phishing stayed high-volume and kept evolving: beyond standard QR redirects, attackers used tricks like ASCII “text QR codes” to dodge image scanning, and even treated QR images as containers for executable JavaScript in supply chain scenarios. SMS-based scams also grew, adding another fast, high-conversion route to push victims toward payment and credential theft.
AI-related abuse became more visible, but mostly as an accelerator rather than a fully autonomous threat: faster phishing, more believable text, and rapid code variation for obfuscation. At the sharper end, reporting described early operational uses of hosted AI services inside intrusion chains and higher-tempo workflows where AI agents handled many routine tasks under human direction.
On platforms beyond Windows, activity stayed practical and targeted. Linux incidents often centered on vulnerable edge and end-of-life devices (including routers and security appliances), plus high-impact enterprise software flaws used to plant backdoors; yet there were also more direct user-focused Linux lures such as malicious “.desktop” files delivered by email masquerading as PDF.
On macOS, campaigns increasingly relied on convincing websites, search results, and malvertising to steer users into running Terminal commands, delivering infostealers like AMOS and more advanced tooling in focused operations (including process injection and encrypted WebSocket control). Developers remained a high-value target across ecosystems: Xcode project infections, malicious IDE extensions, and large supply chain compromises in npm showed how one poisoned dependency, workflow, or marketplace upload can scale quickly into developer laptops, CI runners, and production code.
Combined with aggressive vulnerability exploitation (including high-impact server-side flaws) and continuing abuse of ads, extensions, and package repositories, the second half of 2025 showed attackers optimizing for speed and scale: get in faster, blend in better, and monetize access through theft, extortion, or long-term control.
Malware families to track
One of the foundational responsibilities of the VMRay Labs Threat Analysis team lies in the ongoing surveillance of cyber-security events in the world. This entails more than just tracking existing malware families and their evolving tactics, techniques, and procedures (TTPs) – it also requires the quick identification of newly emerging threats. Our goal is to remain a step ahead of cyber adversaries, enabling proactive defenses against both known and novel threats.
Beyond merely identifying new malware variants, security teams must maintain a real-time awareness of any shifts or changes within the larger threat landscape. This is crucial because the realm of cyber-security is continually shifting. New malware campaigns, vulnerabilities, and changes in attacker behavior are just a few of the variables that the teams need to closely monitor.
Most relevant malware families – 2025 H2
- XWorm
- FormBook
- Remcos
- AgentTesla
- StealCv2
- NjRat
- Gafgyt
- QuasarRAT
- Vidar
- GuLoader
The malware families observed most frequently in H2 2025 reflect a threat landscape shaped by accessibility and proven effectiveness. Remote access trojans and information stealers dominate — XWorm, Remcos, NjRat, and QuasarRAT enabling persistent attacker control, while FormBook, AgentTesla, StealC v2, and Vidar focus on credential and data extraction. GuLoader rounds out the list as one of the most active delivery mechanisms for secondary payloads.
Across the board, these are not novel threats, they are reliable, actively maintained tools that continue to circulate because they work. Security teams should treat sustained presence in this list as a signal that basic evasion and delivery techniques remain effective against a significant portion of defenses.
Across submitted sample types, URLs represent the dominant threat vector by a considerable margin, and their weight increases further when recursive analysis chains are taken into account, where URLs account for the majority of derived submissions.
Email is the second most common initial vector, consistent with phishing remaining the primary delivery mechanism for most malware. Windows executables follow, predominantly 32-bit — reflecting the continued prevalence of malware built to maximize compatibility across environments. PDF documents, HTML files, archives, and Linux ELF executables round out the picture. The distribution is telling: archives and PDFs appear disproportionately in recursive chains because phishing emails routinely deliver either a link or an attachment each of which expands into further analysis. The practical implication is that a single phishing email rarely represents a single sample.
The full delivery chain, followed to its end, is where the actual threat lives.
Sample types:
- URL
- Windows Exe (x86-32)
- Windows Exe (x86-64)
- HTML
- Archive
- Linux ELF Executable
- Other
/ / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / /
General trends
In 2025, ransomware were still popular among threat actors who quickly abused security weaknesses to break into organizations, sometimes through their supply chains. According to ESET, ransomware activity kept climbing throughout the year: Public leak sites listed 6,937 known victims in 2025, more than 1,700 higher than the year before.
The way malware was delivered also changed quickly. After a major global disruption in May, Lumma Stealer showed up again for short periods, but overall detections still dropped by 86% in the second half of 2025 compared to the first. At the same time, another malware family, GuLoader, became more popular, appearing almost thirty times more often in ESET’s tracking. Attackers used it heavily in malicious email campaigns, where it acted as a paid service to install other malware, including ransomware and data-stealing tools. For many defenders, this matched what they were seeing firsthand: tools and loaders change fast, but ransomware or data extortion tools in general are often still the final goal.
Generative AI also became more noticeable in everyday attacks, though mostly as a way to speed things up. Recorded Future found that most so-called AI malware is still in early stages, such as testing ideas or improving existing tools, rather than running fully on its own. Their research also notes that AI is mainly helping attackers do familiar things faster, like writing scripts or crafting phishing messages, rather than creating brand-new attack methods. There have been no confirmed real-world cases from actual threat actors of malware running its own full AI model directly on infected systems.
In practice, this means defenders are more likely to face quicker phishing campaigns, faster changes to scams, and more convincing messages sent at scale.
ESET reports similar findings, saying AI is mostly used for phishing and scams today, while also tracking early experiments like malware that uses hosted AI services to generate harmful scripts. A real-world example of where this is heading came late in the year, when Anthropic reported stopping a state-linked espionage effort that used their AI model to carry out many routine hacking tasks. The operation still needed human oversight and made mistakes, but it showed how AI can increase pace and scale.
Attack targets in 2025 were wide-ranging. Universities, large companies, media outlets, and critical public services were all affected. Public reports included Nissan customer data being exposed through a breach tied to Red Hat systems, several Harvard-related data breaches, including one linked to an Oracle zero-day flaw, and a confirmed cyberattack on email servers at France’s Interior Ministry. Media organizations were hit as well, such as a Washington Post breach that affected nearly 10,000 employees and contractors.
In the public sector, Denmark blamed Russia for destructive and disruptive cyberattacks, including one that impacted a water utility. These incidents show that attackers switch between making money, stealing information, and causing disruption, depending on who they are targeting and what access they gain.
As for delivery techniques, email remained a major way attackers got their foot in the door, but it was far from the only one. The APWG reported that SMS-based scams grew by about 35% in the third quarter of 2025. QR-code phishing also increased sharply, with Mimecast seeing an increase of 13% for QR codes used for phishing in just one quarter. Online ads continued to play a big role in scams as well. The following chapters will provide more in-depth information about these topics.
Linux malware
As Linux adoption as a desktop device still remains low, attacks on Linux devices often involved vulnerable embedded devices, sometimes those which are end-of-life (EoL) and thus no longer updated. That makes them easy targets: if attackers find one working flaw, they can reuse it across thousands of identical devices.
Recent incidents highlight this attack vector: After Fortinet disclosed two serious login bypass bugs in December 2025, attackers were seen breaking into FortiGate devices using fake SSO logins. Around the same time, another campaign took over thousands of end-of-life ASUS home routers and used them as part of a larger spying operation.
However, not all Linux attacks rely on exploitation or embedded devices. In a notable exception, one attacker targeted Linux users directly where malicious “.desktop” shortcut files were sent by email. These files allow the definition of commands which are executed when the file is double-clicked, similar to shortcuts on Windows. In this case, the file downloaded and ran malware on the victim’s system.
MacOS malware
Recent attacks aimed at macOS users show a move toward more convincing ways to reach victims, and methods that depend on people running the malware themselves, such as ClickFix.
Getting users to install malware themselves is still one effective method. macOS users are often lured through realistic websites and search results. In one campaign reported by LastPass, attackers pretended to offer popular software through fake GitHub pages. These fake apps delivered the Atomic (AMOS) infostealer using familiar “fix-it” style prompts. Search engine tricks helped push these pages high in Google and Bing results. Victims were told to copy and paste a command into the terminal, which then installed the malware. AMOS has since been updated to include a backdoor, allowing attackers to keep access to infected systems over time.
A similar approach shows up in other campaigns that use ads or fake help guides. CrowdStrike described cases where users searched for solutions to everyday problems, like printer issues. The instructions looked normal and told users to run commands in Terminal to fix the issue. Instead, those commands installed SHAMOS malware. This works well because running Terminal commands is framed as standard troubleshooting, not something suspicious.
One contrary example is MacSync Stealer. Early versions relied on the basic tricks outlined before, like telling users to copy and paste commands into the terminal. Newer versions look far more sophisticated, using properly packaged apps written in Swift and signed with developer certificates, raising fewer red flags.
Other attacks demonstrate that developers are still a key target. XCSSET is designed to slip into Xcode projects and run when the project is built. That means the malware runs as part of normal development work and can spread when infected projects are shared with others. A newer version of XCSSET adds several upgrades: it steals data from more browsers, watches the clipboard to silently swap the copied crypto wallet addresses with one controlled by the attacker, and hides its activity using stronger encryption and uses compiled AppleScripts that are harder to inspect. It now also pulls data from Firefox and adds another way to survive reboots by creating LaunchDaemon entries.
More focused attacks against macOS are also becoming more advanced. SentinelOne reported on an operation known as NimDoor, linked to North Korean threat actors targeting crypto and Web3 companies. These attacks used malware written in the Nim programming language and involved several attack paths. Two techniques stand out on macOS: injecting code into other running processes, and using encrypted WebSocket connections for remote control. These methods help attackers stay hidden while keeping steady access to infected systems.
Phishing
Captcha
To reduce automated analysis and scanning of malicious links, threat actors often place CAPTCHA challenges in front of phishing pages and malware delivery sites. The goal is simple: block security crawlers and sandbox systems long enough for the campaign to stay online and collect victims.
One new approach is the use of more complex CAPTCHAs. In one recently observed case, users must click and drag a slider to complete the challenge. Attackers assume that automated scanners will fail to interact correctly with this element, while human users can solve it without effort. Recent campaigns show that these slider-based CAPTCHAs are often custom-built rather than reused from legitimate providers, indicating active experimentation to slow down automated inspection tools.
Beyond functional CAPTCHAs, many phishing kits still rely on fake CAPTCHA pages. These are often designed to look similar to Cloudflare or other well-known protection services. The fake challenge acts as an interstitial page that loads before the actual phishing content. This technique is effective because the initial page contains no brand logos, so no obvious malicious elements. As a result, basic scans frequently see only a harmless-looking challenge page. According to Phish Report, phishing sites using this method can remain online and undetected for weeks after deployment.
In some cases, fake CAPTCHA pages are not just a defensive layer but an active part of the attack chain. Several campaigns use CAPTCHA prompts as a pretext to instruct users to perform manual actions, such as copying and executing commands. These so-called ClickFix attacks abuse the trust users place in security checks by framing the steps as part of a verification process. Trend Micro documented multiple cases where fake CAPTCHA pages were used to deliver infostealers and remote access trojans through multi-stage payloads, with the CAPTCHA serving as the social engineering hook.
One example of this tactic was reported in campaigns attributed to Russian threat actors. Victims were presented with an “I am not a robot” style CAPTCHA and instructed to execute a command as part of the verification step. Completing this action directly launched the NOROBOT malware on the system. This method is another form of a ClickFix attack, where the CAPTCHA is used to justify user-driven execution rather than automated exploitation.
Overall, CAPTCHA mechanisms have shifted from simple bot detection to a tool used to convince users to execute malicious code, which we go into more depth in the next chapter.
ClickFix innovation
ClickFix is a social engineering technique where the attacker shifts the “execution step” onto the victim by convincing them to run a command or script themselves (often via PowerShell, cmd.exe, or similar). According to Microsoft’s telemetry, this has moved from a niche trick to a mainstream initial access path: Microsoft Digital Defense Report 2025 states that ClickFix was the most common initial access method seen in Microsoft Defender Experts notifications, accounting for 47% of observed attacks.
A recurring pattern is using legitimate-looking “how to fix” instructions that end in copy/paste execution. Trend Micro even documented campaigns delivered through TikTok videos on mobile devices where the social engineering is embedded in the video itself: viewers are instructed to open PowerShell on their Desktop device and type a short command which pulls a remote script and starts the infection chain, often dropping Vidar or Stealc infostealer variants.
ClickFix lures are also getting more polished and tailored to the operating system the visitor is using. Push Security described a particularly advanced ClickFix page styled to resemble a Cloudflare bot-check even including a helpful video guide, contains a countdown timer, and a “users verified in the last hour” counter to build trust and urgency. In the same example, the page adapts instructions based on the visiting device, e.g. by serving Mac-specific steps, and automatically copies the malicious code to the clipboard via JavaScript.
ClickFix delivery can also lean on unusual protocols and command chains to fetch second-stage instructions. BleepingComputer reported on a finding by MalwareHunterTeam where a ClickFix attack was abusing the decades-old “Finger” protocol as a remote script delivery method: a batch file ran the finger command to retrieve instructions from a remote server and then executed them locally via cmd.exe.
In another instance, Expel described an evolution of the ClickFix formula using “cache smuggling” to reduce obvious download signals.
In this technique, the page and PowerShell content avoid triggering a user-facing downloading of malicious files; instead, the browser is made to cache a resource that presents as an image, but actually contains the next payload. The cached “image” can then be extracted and executed locally, allowing the payload to land on disk without making direct web requests for a file download.
Several newer techniques reuse the same core idea but change the execution surface to bypass defenses and user awareness training. Acronis documented one instance of a so-called “FileFix” attack being used in the wild.
FileFix is a technique where instead of asking the user to open a terminal or the Run dialog, the lure pushes the victim to paste a malicious command into the File Explorer address bar inside a file-upload window, which then executes locally. In the campaign documented by Acronis, steganography is being used to hide both a second-stage PowerShell script and encrypted executable payloads inside seemingly harmless JPG images; the initial stage downloads the images and parses them to extract and run the embedded content. The final stage unpacked the infostealer StealC.
Mr.d0x proposed an additional FileFix variation that targets Windows Mark of the Web (MoTW) assumptions by exploiting how browsers save webpages. In this approach, the attacker social-engineers the user into saving an HTML page with Ctrl+S which the researcher observed does not receive a Mark-of-the-Web tag; the user is asked to rename it to “.hta”, which means opening it runs embedded JScript immediately without security prompts.
SVG files
SVG (Scalable Vector Graphics) has become an attractive container for phishing because it is not just an image format but an XML-based file type that can embed JavaScript. This allows attackers to move directly from a user opening what looks like a harmless image to script execution in a browser context.
Data from LevelBlue SpiderLabs shows that SVG-based attacks have pivoted strongly toward phishing, with an increase of roughly 1800% in early 2025 compared to activity observed since April 2024. The rise accelerated in Q1 2025 driven in part by the spread of attack-in-the-middle phishing-as-a-service platforms such as Tycoon2FA.
A concrete example of this abuse was documented by VirusTotal in a campaign impersonating the Colombian justice system. In this case, the SVG executed embedded JavaScript on rendering, decoded a Base64-encoded HTML phishing page, and injected it to present a fake judicial portal. While the victim saw a simulated download progress bar, the script decoded a Base64 blob in the background and forced the download of the malicious payload. VirusTotal noted that this SVG-based chain initially evaded antivirus detection, showing how effective SVG can be as both a phishing lure and a delivery mechanism.
Email clients are starting to react to this threat model. According to heise online, Microsoft has stopped displaying inline SVG images in Outlook for Web and the new Outlook for Windows, replacing them with blank placeholders. The change targets the risk that SVG content can execute scripts when rendered inline. SVG files sent as regular attachments are still supported, which means the format remains usable for attackers, but one high-risk rendering path in email has been reduced.
QR codes
Quishing, the use of QR codes in phishing attacks, remains a clear and ongoing issue in 2025. Attackers continue to rely on QR codes to move victims away from traditional email links and toward mobile devices.
Telemetry from Mimecast shows a sustained increase in malicious QR code activity. During Q3 2025, they detected 700k unique malicious QR codes used for phishing, representing a 13% increase compared to the quarter before. These figures highlight that QR-based phishing is not a niche technique but a widely adopted delivery method.
Attackers are also refining how QR codes are constructed to evade detection. One such case is highlighted by Checkpoint which showed the use of ASCII-based QR codes, where the visual structure of a QR code is recreated using text characters instead of a standard image. The primary goal of this technique is to bypass optical character recognition (OCR) and image-based scanning engines commonly used in email security products. Because these QR codes are technically plain text, they can slip through controls that only analyze embedded images.
QR codes are no longer limited to classic phishing scenarios. In one case documented by Socket, QR codes were used as a covert container for malicious JavaScript code rather than as a redirection mechanism. A malicious npm package named fezbox used an unusual steganographic approach: when the library was imported, it fetched a QR code from a remote server and then decoded and executed the JavaScript code represented by that QR image. This technique allowed the attacker to hide executable logic in an unexpected format, complicating static analysis and code review processes.
Complex chains
Phishing attacks have become harder to spot over time as putting a simple link in an email is often avoided nowadays. Instead, attackers attach documents that lead the reader to a website. We also see them using link shorteners, open redirects, and several jumps between websites to hide where the link really ends up. While this is nothing new, one recent phishing attempt we investigated highlighted the complexity these chains have reached.
The attack started with an email claiming there were changes to an employee’s compensation which also included a PDF file as an attachment. The file was locked with a password which had to be extracted from the email. This extra step is likely meant to deter automated security tools that scan attachments individually without seeing or understanding the full context, i.e., the email content containing the password.
After opening the PDF with the password, the reader is shown a shortened link. Clicking it sends them to a page protected by a Cloudflare CAPTCHA to stop bots and security scanners. Behind the scenes, the page also checks whether the visitor is using a VPN, another way to spot and block automated scanners and security systems.
Only after getting past all of these steps does the fake Microsoft login page finally appear. By building these long chains, attackers hope that security tools will miss or fail at one of the steps and never reach the final page, making the attack harder to detect and classify as such.
(Ab)use of AI
Clearly AI-written malicious scripts used to be a novelty in 2024: when we saw code patterns that strongly suggested generative AI output, it stood out. By 2025, those indicators showed up far more often, and in day-to-day triage it became almost routine.
This shift is not limited to malware code. Microsoft Threat Intelligence reported a credential-phishing campaign where the attacker likely used AI-generated code to hide the phishing payload and reduce the chance of being caught by detection systems. AI-assisted obfuscation can quickly produce many code variants, which makes simple signature-based blocking less reliable.
A second trend is the growth of “malicious LLMs” sold specifically for crime. Unit 42 tested black-market tools including WormGPT 4 and KawaiiGPT and concluded that these models are already being used by attackers. In their testing, these tools could generate convincing phishing and spear-phishing emails with fewer of the language mistakes that defenders often see in the wild.
They were also marketed and used as malware helpers: Unit 42 showed examples where the model produced working attacks, including a PowerShell routine that encrypts PDF files using AES-256 and optional components for data exfiltration via Tor. The same tools could also draft ransom notes and even assemble a full extortion flow (encryption message through cryptocurrency payment instructions), lowering the skill needed to run a ransomware-style operation. Unit 42 also noted the size of the surrounding ecosystem, with Telegram channels in the hundreds of subscribers for these tools.
So far, we still see fewer real-world malware families that run AI at runtime on victim machines. When runtime AI does appear, it is often tied to research or to narrow experiments rather than being used by threat actors. One notable operational case was described by Microsoft: the SesameOp backdoor used the OpenAI Assistants API for command-and-control, effectively treating a legitimate AI service as part of its control channel.
Google Threat Intelligence Group (GTIG) also summarized several ways threat actors are experimenting with AI tools in operations, including malware that is explicitly written to interact with AI systems. In their reporting, FRUITSHELL included hard-coded prompts aimed at bypassing detection or analysis by security tooling that uses LLMs, PROMPTSTEAL used the Hugging Face API to query Qwen2.5 and generate one-line Windows commands, and QUIETVAULT used prompts plus on-host AI CLI tooling to search for additional secrets on an infected system and then exfiltrate the results.
These examples point to a practical direction: attackers are not only using AI to write better emails or scripts before deployment, but are also starting to wire AI services and AI-facing tricks into the intrusion chain itself. However, at the same time, public reporting suggests it is easy to overstate how common “AI malware” really is today. Recorded Future argued that most observed cases were teams experimenting and researching rather than running fully autonomous campaigns, meaning many widely shared examples are narrow PoCs with unclear real impact, and there are no confirmed public cases of malware with embedded local models running on victim devices.
AI-assisted operations, however, have been observed in the wild. Anthropic provided a concrete example of what an AI-assisted operations can look like when a capable actor builds a workflow around an AI coding agent. In its report on disrupting an espionage campaign, Anthropic stated that a state-linked threat actor (believed to be Chinese state-sponsored) used Claude Code to automate much of the operation against roughly 30 targets, with successful compromise in a small number of cases. Anthropic described a framework where humans chose targets and guided the overall plan, while the AI tool handled many routine steps: fast reconnaissance to find high-value data, researching and testing vulnerabilities, writing exploit code, identifying high-privilege accounts, creating backdoors, and supporting data theft. Anthropic estimated AI covered about 80-90% of the work, but also noted reliability issues, such as the model hallucinating credentials or overstating what it had accessed.
Other malware delivery methods
While phishing is still a popular delivery method, threat actors also push and pivot to other delivery methods for malware.
App Stores, add-ons, plugins and extensions
Attackers like app stores and extension marketplaces because they solve two problems at once: distribution and trust.
A malicious upload can reach the same audience that would normally install legitimate tooling, and it runs in a context users often treat as “part of the product” (editor, browser, package manager). Recent cases show that this is not limited to consumer browsers; developer ecosystems are a prime target as well.
Multiple investigations show that VS Code extensions are being used as a delivery channel for malware, often by pretending to be harmless themes, formatters, or developer tools. In several cases, extensions executed code immediately after installation and deployed infostealers that captured screens, stole credentials, clipboard data, or browser sessions.
Researchers have also found extensions hiding malicious payloads inside files that looked like static assets. One campaign documented by ReversingLabs embedded archives and droppers inside fake image files, which unpacked and ran binaries using built-in Windows tools.
Abuse is not limited to Microsoft’s marketplace. Open VSX has repeatedly hosted malicious extensions that remained available even after being removed from the VS Code Marketplace. Threat groups tracked by different researchers uploaded dozens of extensions across both platforms, using multi-stage payloads, backdoors, crypto miners, and repeated re-uploads to maintain reach across VS Code-compatible IDEs.
Some incidents had direct financial impact. Annex analyzed a fake Solidity extension installed into Cursor that provided no real functionality and instead downloaded and executed remote code, leading to the theft of roughly $500,000 in crypto assets. Secure Annex reported a similar Solidity-themed extension that deployed a remote access trojan with command-and-control tied to an Ethereum smart contract.
Developers and power users are also targeted through public package repositories where “install” and “build” steps execute code on the endpoint. Sonatype documented an npm worm campaign dubbed IndonesianFoods that self-propagates every seven seconds and scaled to more than 100,000 packages associated with the activity. The report frames the campaign as using scale to disrupt the ecosystem rather than focusing on credential theft or classic host infection.
On the Linux side, Arch Linux’s AUR (Arch User Repository) saw malicious packages used to install CHAOS RAT. BleepingComputer reported that three AUR packages pulled code from an attacker-controlled GitHub repository and were removed roughly two days after upload once community members flagged them. CHAOS RAT was described as an open-source remote access trojan for Windows and Linux, supporting file upload/download, command execution, and reverse shell capability.
This distribution method is not limited to code-centric ecosystems. BleepingComputer reported a campaign delivering StealC V2 via malicious Blender .blend model files uploaded to 3D model marketplaces. Blender projects can embed Python scripts; when Blender’s Auto Run option is enabled, a rig can automatically execute embedded code. In the observed chain, embedded Python fetched a loader, which then pulled additional scripts and payloads and established persistence, ultimately deploying Stealc alongside an additional Python stealer.
Browser add-ons remain one of the most effective channels. Some campaigns hide malicious logic inside files users do not expect to be executable. Koi’s GhostPoster write-up describes a Firefox extension (“Free VPN Forever”) that reads its own logo.png, searches for a marker after the end of the real image data, and extracts JavaScript embedded in the PNG bytes. The report links this to a broader campaign spanning multiple Firefox extensions and describes capabilities including extensive browsing monitoring and a backdoor for remote code execution.
Other campaigns focus on patience and supply-chain style updates. Koi reported ShadyPanda as a seven-year operation that reached millions of Chrome and Edge users. In mid-2024, several extensions (including ones labeled “Featured” and “Verified”) were weaponized after years of legitimate operation, with behavior described as periodic remote code execution by downloading arbitrary JavaScript, plus browsing monitoring, fingerprint collection, and data exfiltration.
Finally, some groups combine extensions with phishing and malware distribution. Koi’s GreedyBear report describes an operation with 150+ weaponized Firefox extensions impersonating popular cryptocurrency wallets, paired with hundreds of malicious executables and scam sites. The report also describes “extension hollowing” (building a benign-looking reputation, then swapping code later), and links associated binaries to stealer families such as LummaStealer and variants described as Luca Stealer, with user reports indicating substantial financial losses.
Text message
SMS remains a popular alternative to email-based phishing. This is reflected in the APWG report which shows that SMS-based fraud (also called “smishing”) rose by nearly 35% in Q3 2025 compared to the quarter before, but noting that the increase was driven in part by improved detection and reporting rather than purely attacker growth.
A large share of current SMS phishing activity is built around simple but effective social engineering, commonly pushing recipients to click a link and resolve an alleged problem immediately. Unit 42 attributes an ongoing global campaign using fraudulent toll-violation and package-misdelivery lures to a threat actor cluster widely tracked as the “Smishing Triad”. The campaign relies on urgency to shorten the victim’s decision time and move them straight from reading the SMS to entering data or making a payment on a phishing site. From an infrastructure perspective, Unit 42 describes the operation as highly decentralized, without a single control point, and supported by a very large and diverse pool of domains and hosting providers, linked to approximately 194,000 malicious domains since the beginning of 2024, which illustrates the scale and the rapid domain churn used to reduce takedown impact and blocklist effectiveness.
Beyond message content and domain churn, recent reporting also shows how attackers can operationalize smishing by abusing network-edge devices that are exposed on the internet. Sekoia observed suspicious traces in honeypots and assessed that a cellular router API had been exploited to send malicious SMS messages containing phishing URLs. In this activity, Belgium was singled out frequently, with phishing URLs impersonating local services such as CSAM and Ebox; Sekoia also noted instances targeting France. The same investigation identified more than 18,000 routers of the affected type reachable from the public internet, and at least 572 that were potentially vulnerable. Sekoia reports active exploitation for smishing distribution dating back to at least February 2022, indicating long-lived operational use rather than a short campaign spike.
Malvertising
Malvertising uses paid advertisements to pull victims toward attacker-controlled infrastructure, often by abusing the trust users place in search results and well-known brands. In the second half of 2025, this remained a reliable delivery path because ads can be placed at scale, tuned to high-intent keywords, and quickly rotated when domains get taken down. Multiple incident reports from 2025 show the same pattern: an ad or promoted result acts as the first redirector, and the payload is delivered from a lookalike site or a staged infection flow.
A key driver is the size of the ad ecosystem itself, including the amount of fraud that can be monetized before enforcement catches up. Reuters reported that internal Meta documents projected around $16 billion (roughly 10% of 2024 revenue) coming from ads tied to scams and banned goods, and that Meta internally estimated users were shown billions of higher-risk scam ads per day. Even if not all of that activity is malware delivery, this scale makes advertising channels attractive for criminals because it provides reach, targeting, and measurable conversion funnels.
Seasonal shopping periods continue to amplify malvertising and ad-driven malware because users are primed to click on deals, discount extensions, and brand impersonation. Malwarebytes research published in November 2025 highlighted “ad-related malware” as a recurring holiday threat and pointed to a “Walmart gift card” lure that functioned as a data-harvesting trap. In the same research, Malwarebytes reported high exposure rates: for malvertising specifically, 40% reported being targeted and 11% reported falling victim.
A common technical implementation is SEO poisoning paired with sponsored ads that push trojanized installers for popular enterprise software. Blackpoint described a campaign that abused malvertising to distribute a fake Microsoft Teams installer, offering a malicious “MSTeamsSetup.exe” via a spoofed download site reached from a sponsored search result.
Exploiting Vulnerabilities
Threat actors continued to raise the bar in 2025 by chaining and scaling the abuse of security flaws to gain access, drop malware, and run ransomware operations.
Recorded Future identified 161 distinct vulnerabilities that were actively exploited in H1 2025, with nearly half of that activity tied to malware. Over the same period, the total number of disclosed CVEs increased by 16% year over year. Targeting was not confined to obscure software however: Microsoft products and edge security appliances drew attention, with Microsoft responsible for 28 actively exploited CVEs, including 20 affecting Windows. That total was more than three times higher than the next most targeted vendor in the dataset, Apple, which had eight vulnerabilities. Speed and repeatability were central factors, as 42% of exploited flaws had publicly available proof-of-concept exploits, reducing the effort required to deploy them at scale. When attribution was possible, more than half of the observed exploitation activity was linked to suspected state-sponsored actors.
The same pattern appears in breach reporting. Verizon found that the use of vulnerability exploitation as an initial access vector in data breaches increased by 34% year over year and represented 20% of all breaches, with part of the rise tied to zero-day attacks against embedded network devices and VPNs. The report also noted that median ransomware payments declined in the prior year and that 64% of victim organizations chose not to pay.
Microsoft incident response data helps tie vulnerability abuse to other entry points. In Microsoft investigations, 28% of breaches began with phishing or social engineering. Among incidents where motivation was known, most were financially driven through extortion, theft, or ransom, while only 4% were driven only by espionage.
To highlight one important security vulnerability that was widely exploited: ToolShell affected on-premises SharePoint servers and permitted unauthenticated users to remotely execute code and allowed broad access to SharePoint data and underlying file systems. It also illustrates how quickly attackers can act once a high-impact flaw becomes public, as China-based actors reportedly used it to breach a telecommunications provider in the Middle East shortly after the issue was disclosed and patched in July 2025. Organizations across multiple continents were impacted, which is consistent with fast scanning and exploitation of internet-facing SharePoint deployments.
Another highlight is React2Shell, which refers to a set of maximum-severity remote code execution flaws affecting server-side use of React Server Components and related frameworks, including Next.js. These issues carried a reported severity of 10.0 and allowed unauthenticated RCE with a single request. Reporting shows rapid uptake across attacker groups: within hours of disclosure, nation-state operators were exploiting the flaws for cyberespionage or to deploy malware such as EtherRAT, while criminal actors used them for cryptocurrency mining and ransomware.
Public reports also document ongoing exploitation of widely used web platforms, particularly WordPress plugins. Across multiple incidents, attackers abused flaws such as a critical issue in an Elementor add-on, a Post SMTP plugin bug used to hijack or take over administrator accounts, authentication bypasses in the JobMonster and Service Finder themes, active exploitation of a critical RCE in the Alone theme, exposure of private data through a security plugin, and large-scale campaigns targeting outdated plugins.
Finally, embedded and end-of-life devices remained attractive targets, especially when positioned at the edge between internal networks and the internet. SecurityScorecard described “Operation WrtHug” as a coordinated espionage-focused campaign that compromised thousands of ASUS routers worldwide, turning home and small-office devices into active threats. The operation reportedly relied on multiple flaws, including OS command injection, arbitrary command execution, and improper authentication, with AiCloud identified as the initial access vector. In total, at least six vulnerabilities were used to gain initial access in the campaign.
Supply Chain Attacks
Supply chain attacks remain one of the most efficient ways to reach a large number of victims in a single operation: if an attacker can tamper with a widely used dependency, the normal update path can push malicious code into developer laptops, CI runners, and production builds at scale.
A clear example from 2025 is the Shai-Hulud campaign, which evolved in multiple waves and focused heavily on the JavaScript ecosystem. In the first wave, Socket reported that a malicious release of @ctrl/tinycolor (around 2.2 million weekly downloads at the time) appeared on npm, but that it was part of a bigger compromise that hit more than 40 packages across different maintainers. What made this incident particularly dangerous is the automation built into the injected code: Socket described a function that programmatically pulls a package tarball, drops a malicious script, repackages and republishes the archive. This effectively turns the victim package into a “trojanizer” that can poison downstream packages without manual republishing for each target.
In the later Shai-Hulud 2.0 wave, the impact shifted from poisoning packages to large-scale credential exposure. Wiz documented that, compared to earlier npm worms such as Shai-Hulud 1.0 and s1ngularity, Shai-Hulud 2.0 stayed active longer and continued generating new compromised repositories days after disclosure, including renewed spikes. The same Wiz analysis reported that attacker-collected data included a very large set of leaked secrets: up to about 400,000 unique secret values were present in their dataset (with a smaller verified subset).
More broadly, npm has remained a frequent target, and credential theft (often via phishing) is a common entry point. Socket described an expanding campaign where attackers obtained maintainer access and published malicious versions of widely used developer tooling packages, including “eslint-config-prettier”, “eslint-plugin-prettier”, and others, distributing them through standard dependency resolution into developer machines and CI pipelines. In a similar cluster of activity, Socket reported the hijack of the popular “is” package (around 2.8 million weekly downloads), noting that its malicious variants were designed to run across platforms under Node 12+ (macOS, Linux, Windows). Socket’s write-up details how the payload contained heavily obfuscated JavaScript, collected host and environment details, and established a control channel where received messages could be executed as code, effectively enabling remote code execution within any process that imported the dependency.
Another high-impact npm incident in 2025 showed how supply chain compromise can jump from developer tooling into end-user transaction theft. Aikido reported that attackers hijacked 18 very popular JavaScript packages with a combined download volume of more than 2 billion per week. The injected code was designed to run in web client contexts and hook into crypto/web3 activity in the browser, altering wallet interactions and rewriting payment destinations so that approvals or transfers could be redirected to attacker-controlled addresses without obvious user-facing signals.
Python’s ecosystem has faced similar pressure, with account takeover attempts used as a stepping stone toward package compromise. PyPI itself repeatedly warned maintainers and users about ongoing phishing campaigns that impersonate PyPI and attempt to capture credentials. In one campaign, PyPI described emails that claimed “account maintenance” or email verification requirements and tried to lure recipients to a non-PyPI domain; PyPI explicitly stated the message was fraudulent.
Supply chain activity is not limited to package repositories; it also targets the automation and tooling that surrounds builds. GitGuardian reported the GhostAction campaign, where attackers injected malicious GitHub Actions workflows across 817 repositories tied to 327 GitHub users, exfiltrating 3,325 secrets (including PyPI, npm, and DockerHub tokens). This is a useful reminder that “dependency trust” also includes CI configuration, reusable workflows, and repository-level automation.
Developer environments beyond package managers have also become a target. Koi described GlassWorm as a self-propagating worm aimed at VS Code extensions. A key technique highlighted by Koi is the use of invisible Unicode characters that make parts of the malicious code effectively disappear in editors, reducing the chance of detection during review. Koi also described resilient control mechanisms, including blockchain-based command-and-control and the use of Google Calendar as a backup command channel.
Finally, supply chain compromise is not limited to developer tools and libraries. BleepingComputer reported a consumer-facing case where the SmartTube YouTube client for Android TV was breached after an attacker gained access to the developer’s signing keys, allowing a malicious update to be distributed to users. In that incident, the compromise was only noticed when Google Play Protect began blocking the app, and analysis of the affected build identified a native library that was not present in the public source tree.
/ / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / /
In the second half of 2025, attackers continued to refine how they gain access, stay hidden, and scale their operations. Ransomware activity kept rising even as delivery tooling shifted rapidly, with some loaders surging as paid services while others disappeared just as quickly. This reinforced a familiar pattern: tools change fast, but extortion, data theft, and long-term access remain the primary objectives.
Social engineering remained a popular entry point. Email was still heavily abused, but it was increasingly combined with QR codes, fake CAPTCHAs, and long redirect chains designed to frustrate automated detection. ClickFix techniques stood out as a key trend, with attackers pushing execution onto victims by convincing them to run commands themselves, often through highly polished and device-specific instructions.
Attackers also focused on stealth and persistence across platforms. Linux campaigns targeted embedded and end-of-life devices, while macOS attacks leaned on user-driven execution and developer workflows. At the same time, supply chain compromise expanded across package repositories, extensions, CI systems, and update channels, allowing a single breach to spread widely through trusted ecosystems.
Exploitation of vulnerabilities accelerated in parallel, with threat actors rapidly weaponizing newly disclosed flaws in internet-facing services, frameworks, and edge devices. AI played a growing supporting role by speeding up phishing, scripting, and reconnaissance, and in some cases by being wired directly into attack workflows. Many of these techniques are built to defeat static inspection, highlighting the need for dynamic analysis methods like evasion-resistant sandboxes to gain more in-depth insights into the malicious nature of the techniques.
/ / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / / /
- https://www.recordedfuture.com/blog/ai-malware-hype-vs-reality
- https://www.bleepingcomputer.com/news/security/nissan-says-thousands-of-customers-exposed-in-red-hat-breach/
- https://www.bleepingcomputer.com/news/security/harvard-university-discloses-data-breach-affecting-alumni-donors/
- https://www.bleepingcomputer.com/news/security/france-interior-ministry-confirms-cyberattack-on-email-servers/
- https://www.bleepingcomputer.com/news/security/washington-post-data-breach-impacts-nearly-10k-employees-contractors/
- https://www.theguardian.com/world/2025/dec/18/denmark-says-russia-was-behind-two-destructive-and-disruptive-cyber-attacks
- https://docs.apwg.org/reports/apwg_trends_report_q3_2025.pdf (PDF)
- https://www.reuters.com/investigations/meta-is-earning-fortune-deluge-fraudulent-ads-documents-show-2025-11-06/
- https://www.anthropic.com/news/disrupting-AI-espionage
- https://arcticwolf.com/resources/blog/arctic-wolf-observes-malicious-sso-logins-following-disclosure-cve-2025-59718-cve-2025-59719/
- https://securityscorecard.com/blog/operation-wrthug-the-global-espionage-campaign-hiding-in-your-home-router/
- https://www.cyfirma.com/research/apt36-targets-indian-boss-linux-systems-with-weaponized-autostart-files/
- https://www.darktrace.com/blog/auto-color-backdoor-how-darktrace-thwarted-a-stealthy-linux-intrusion
- https://www.jamf.com/blog/macsync-stealer-evolution-code-signed-swift-malware-analysis/
- https://www.microsoft.com/en-us/security/blog/2025/09/25/xcsset-evolves-again-analyzing-the-latest-updates-to-xcssets-inventory/
- https://blog.lastpass.com/posts/attack-targeting-macs-via-github-pages
- https://moonlock.com/amos-backdoor-persistent-access/
- https://www.bleepingcomputer.com/news/security/decades-old-finger-protocol-abused-in-clickfix-malware-attacks/
- https://www.trendmicro.com/en_us/research/25/e/tiktok-videos-infostealers.html
- https://pushsecurity.com/blog/the-most-advanced-clickfix-yet/
- https://www.acronis.com/en/tru/posts/filefix-in-the-wild-new-filefix-campaign-goes-beyond-poc-and-leverages-steganography/
- https://www.crowdstrike.com/en-us/blog/falcon-prevents-cookie-spider-shamos-delivery-macos/
- https://www.sentinelone.com/labs/macos-nimdoor-dprk-threat-actors-target-web3-and-crypto-platforms-with-nim-based-malware/
- https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/msc/documents/presentations/CSR/Microsoft-Digital-Defense-Report-2025.pdf (PDF)
- https://assets.recordedfuture.com/insikt-report-pdfs/2025/cta-2025-0828.pdf (PDF)
- https://mrd0x.com/filefix-part-2/
- https://expel.com/blog/cache-smuggling-when-a-picture-isnt-a-thousand-words/
- https://levelblue.com/blogs/spiderlabs-blog/pixel-perfect-trap-the-surge-of-svg-borne-phishing-attacks
- https://blog.virustotal.com/2025/09/uncovering-colombian-malware-campaign.html
- https://www.heise.de/en/news/Microsoft-Outlook-No-more-SVG-display-for-security-reasons-10731394.html
- https://x.com/MsftSecIntel/status/1995649242329677996
- https://phish.report/blog/fake-cloudflare-interstitials
- https://www.trendmicro.com/en_us/research/25/e/unmasking-fake-captcha-cases.html
- https://www.bleepingcomputer.com/news/security/russian-hackers-evolve-malware-pushed-in-i-am-not-a-robot-clickfix-attacks/
- https://blog.checkpoint.com/harmony-email/the-evolution-of-qr-code-phishing-ascii-based-qr-codes/
- https://socket.dev/blog/malicious-fezbox-npm-package-steals-browser-passwords-from-cookies-via-innovative-qr-code
- https://www.koi.ai/blog/the-vs-code-malware-that-captures-your-screen
- https://www.reversinglabs.com/blog/malicious-vs-code-fake-image
- https://secureannex.com/blog/sleepyduck-malware/
- https://www.koi.ai/blog/tiger-jack-malicious-vscode-extensions-stealing-code
- https://www.koi.ai/blog/whitecobra-vscode-cursor-extensions-malware
- https://securelist.com/open-source-package-for-cursor-ai-turned-into-a-crypto-heist/116908/
- https://www.sonatype.com/blog/unprecedented-automation-indonesianfoods-pits-open-source-against-itself
- https://github.com/6mile/Indonesian-Foods-Worm
- https://www.bleepingcomputer.com/news/security/arch-linux-pulls-aur-packages-that-installed-chaos-rat-malware/
- https://www.bleepingcomputer.com/news/security/malicious-blender-model-files-deliver-stealc-infostealing-malware/
- https://www.koi.ai/blog/inside-ghostposter-how-a-png-icon-infected-50-000-firefox-browser-users
- https://www.koi.ai/blog/4-million-browsers-infected-inside-shadypanda-7-year-malware-campaign
- https://socket.dev/blog/malicious-chrome-extensions-phantom-shuttle
- https://www.koi.ai/blog/greedybear-650-attack-tools-one-coordinated-campaign
- https://www.koi.ai/blog/google-and-microsoft-trusted-them-2-3-million-users-installed-them-they-were-malware
- https://assets.recordedfuture.com/insikt-report-pdfs/2025/cta-2025-0828.pdf (PDF)
- https://its.ny.gov/system/files/documents/2025/06/maguire-verizon.pdf (PDF)
- https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/msc/documents/presentations/CSR/Microsoft-Digital-Defense-Report-2025.pdf (PDF)
- https://www.security.com/blog-post/toolshell-china-zingdoor
- https://www.bleepingcomputer.com/news/security/critical-react2shell-flaw-exploited-in-ransomware-attacks/
- https://www.s-rminform.com/latest-thinking/react2shell-used-as-initial-access-vector-for-weaxor-ransomware-deployment
- https://www.sysdig.com/blog/etherrat-dprk-uses-novel-ethereum-implant-in-react2shell-attacks
- https://www.cloudsek.com/blog/rondodox-botnet-weaponizes-react2shell
- https://www.anthropic.com/news/disrupting-AI-espionage
- https://www.recordedfuture.com/blog/ai-malware-hype-vs-reality
- https://www.malwarebytes.com/press/2025/11/20/daily-scams-hit-27-of-people-on-social-media-and-15-on-marketplaces
- https://blackpointcyber.com/blog/malicious-teams-installers-drop-oyster-malware/
- https://www.bleepingcomputer.com/news/security/critical-flaw-in-wordpress-add-on-for-elementor-exploited-in-attacks/
- https://www.bleepingcomputer.com/news/security/hackers-exploit-wordpress-plugin-post-smtp-to-hijack-admin-accounts/
- https://www.bleepingcomputer.com/news/security/hackers-exploit-critical-auth-bypass-flaw-in-jobmonster-wordpress-theme/
- https://www.bleepingcomputer.com/news/security/hackers-exploit-auth-bypass-in-service-finder-wordpress-theme/
- https://www.bleepingcomputer.com/news/security/wordpress-security-plugin-exposes-private-data-to-site-subscribers/
- https://www.bleepingcomputer.com/news/security/hackers-launch-mass-attacks-exploiting-outdated-wordpress-plugins/
- https://www.bleepingcomputer.com/news/security/hackers-actively-exploit-critical-rce-in-wordpress-alone-theme/
- https://www.bleepingcomputer.com/news/security/post-smtp-plugin-flaw-exposes-200k-wordpress-sites-to-hijacking-attacks/
- https://securityscorecard.com/blog/operation-wrthug-the-global-espionage-campaign-hiding-in-your-home-router/
- https://socket.dev/blog/tinycolor-supply-chain-attack-affects-40-packages
- https://www.wiz.io/blog/shai-hulud-2-0-aftermath-ongoing-supply-chain-attack
- https://socket.dev/blog/npm-is-package-hijacked-in-expanding-supply-chain-attack
- https://www.aikido.dev/blog/npm-debug-and-chalk-packages-compromised
- https://www.bleepingcomputer.com/news/security/pypi-urges-users-to-reset-credentials-after-new-phishing-attacks/
- https://blog.pypi.org/posts/2025-09-23-plenty-of-phish-in-the-sea/
- https://blog.gitguardian.com/ghostaction-campaign-3-325-secrets-stolen/
- https://www.koi.ai/incident/live-updates-glassworm-first-self-propagating-worm-using-invisible-code-hits-openvsx-and-vscode-marketplaces
- https://secureannex.com/blog/glassworm-continued/
- https://www.bleepingcomputer.com/news/security/smarttube-youtube-app-for-android-tv-breached-to-push-malicious-update/
- https://www.microsoft.com/en-us/security/blog/2025/09/24/ai-vs-ai-detecting-an-ai-obfuscated-phishing-campaign/
- https://unit42.paloaltonetworks.com/dilemma-of-ai-malicious-llms/
- https://www.microsoft.com/en-us/security/blog/2025/11/03/sesameop-novel-backdoor-uses-openai-assistants-api-for-command-and-control/
- https://cloud.google.com/blog/topics/threat-intelligence/threat-actor-usage-of-ai-tools
如有侵权请联系:admin#unsafe.sh