嗯,用户让我总结这篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要快速浏览文章内容,抓住主要信息。 文章讲的是一个与中国有关的网络攻击组织Red Menshen,他们利用一种叫做BPFDoor的恶意软件,针对电信网络进行间谍活动。攻击目标主要是中东和亚洲的政府机构。BPFDoor隐藏得很深,难以被发现,可以在网络中长期潜伏。 接下来,我需要将这些关键点浓缩成一句话。要包括攻击组织、使用的工具、目标以及影响。确保不超过100字。 最后,检查一下是否符合要求,没有使用特定的开头,并且信息准确。 </think> 中国关联的Red Menshen组织利用BPFDoor恶意软件潜入电信网络,在中东和亚洲进行长期间谍活动,针对政府目标实施隐蔽监控。 2026-3-27 06:16:10 Author: securityaffairs.com(查看原文) 阅读量:45 收藏
China-linked Red Menshen APT deploys stealthy BPFDoor implants in telecom networks

China-linked Red Menshen APT group used stealthy BPFDoor implants in telecom networks to spy on government targets.
Rapid7 Labs uncovered a China-linked threat group known as Red Menshen has been running a long-term espionage campaign by infiltrating telecom networks, mainly in the Middle East and Asia. Active since at least 2021, the group uses highly stealthy BPFDoor implants to maintain hidden access inside critical infrastructure.
This strategic positioning allows attackers to quietly monitor and potentially spy on government communications. Researchers describe these implants as extremely hard to detect, acting like “digital sleeper cells” embedded deep within telecom environments for prolonged surveillance.
Compromised telecoms threaten entire populations, not just individual companies, as they carry critical communications and digital identities. Over the past decade, similar state-backed intrusions have targeted multiple countries, exposing call records, sensitive communications, and trusted operator links, revealing a worrying global pattern.
Investigations reveal a structured, long-term campaign by a China-linked threat actor targeting telecommunications infrastructure. Rather than short-term intrusions, the operation plants “sleeper cells”, dormant footholds embedded deep within networks to maintain persistent access over extended periods. Recurring tools in the attackers’ arsenal include kernel-level implants, passive backdoors, credential-harvesting utilities, and cross-platform command frameworks, forming a layered, stealthy access model. Experts highlighted the central role of BPFdoor, a Linux backdoor operating within the kernel that activates only when triggered by specially crafted packets, without exposing ports or command-and-control channels. By positioning below traditional visibility layers, this approach complicates detection and demonstrates a shift toward deep, covert tradecraft. BPFdoor is not an isolated tool but part of a broader, scalable intrusion model targeting telecom environments at high stealth.
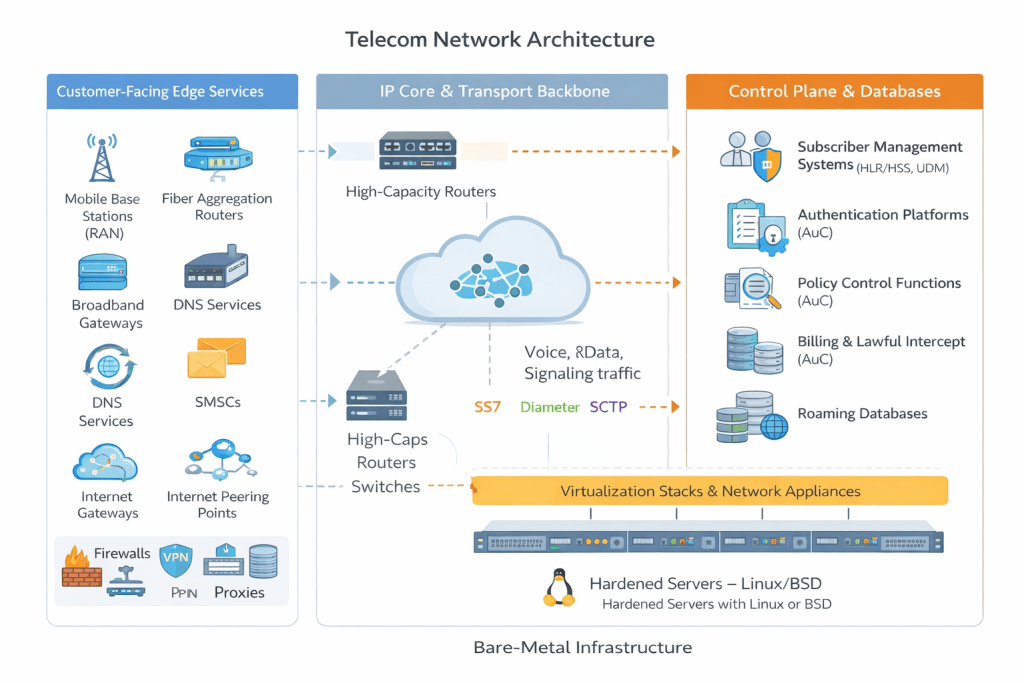
Modern telecom networks are built in layers, making them highly valuable targets. At the edge are customer-facing systems like base stations, routers, VPNs, and firewalls, which connect to the core backbone that carries massive volumes of global traffic.
Deeper inside sits the control plane, where critical systems manage subscribers, authentication, billing, and signaling using protocols like SS7 and Diameter. Much of this infrastructure runs on Linux or BSD systems, meaning a kernel-level backdoor can place attackers close to sensitive data and communication flows.
Attacks usually begin at the network edge by exploiting exposed services or valid accounts on devices like VPNs, firewalls, and virtualization hosts. Once inside, attackers deploy tools such as CrossC2 for command execution, TinyShell for stealthy persistence, and keyloggers or brute-force tools to steal credentials and move laterally toward core systems.
A key tool is BPFdoor, a stealthy Linux backdoor that hides in the kernel and activates only when it receives a specially crafted “magic” packet.
“BPFdoor first came to broader public attention around 2021, when researchers uncovered a stealthy Linux backdoor used in long-running espionage campaigns targeting telecommunications and government networks. The BPFDoor source code reportedly leaked online in 2022, making the previously specialized Linux backdoor more accessible to other threat actors.” reads the report published by Rapid7. “Normally, BPF is used by tools like tcpdump or libpcap to capture specific network traffic, such as filtering for TCP port 443. It operates partly in kernel space, meaning it processes packets before they reach user-space applications. BPFdoor abuses this capability. Rather than binding to a visible listening port, the implant installs a custom BPF filter inside the kernel that inspects incoming packets for a specific pattern, a predefined sequence of bytes often referred to as a “magic packet” or “magic byte.” “
Like a hidden lock that opens with the right code, it leaves no visible trace, making detection extremely difficult while enabling long-term, covert access across telecom environments.
Rapid7 Labs hunted BPFdoor variants by analyzing ELF samples and grouping them by code similarity, revealing both recurring clusters and outliers. Using custom tools, they discovered new features, including a variant “F” with a 26-instruction BPF filter and updated magic packets. Some samples inspect SCTP traffic, giving attackers access to telecom signaling, subscriber data, and location tracking. Other tactics include mimicking bare-metal servers like HPE ProLiant or container services such as Docker to blend into telecom hardware and 5G core environments. These strategies allow implants to remain hidden while embedding directly into the backbone, turning persistence into deep visibility across critical networks.
According to Rapid7, recent BPFdoor variants show significant evolution in stealth and control. Instead of simple magic packets, triggers are now hidden inside legitimate HTTPS traffic, passing through proxies, load balancers, and firewalls.
A clever padding mechanism, called the 26- or 40-byte “magic ruler,” ensures the activation marker lands at a fixed offset, surviving header changes. The malware also uses lightweight RC4-MD5 encryption for fast command execution and reuses proven routines from prior Chinese-linked malware. ICMP packets are used as a small control channel between infected systems. A special marker (0xFFFFFFFF) tells the receiving host to execute commands, letting attackers manage multiple compromised servers quietly across telecom and enterprise networks.
“BPFdoor and new eBPF malware families like Symbiote demonstrate how kernel packet filtering can be abused for stealth persistence. As defenders improve visibility at higher layers, adversaries are increasingly shifting implants deeper into the operating system.” concludes the report that provides Indicators of Compromise (IoCs).
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, telecom)
如有侵权请联系:admin#unsafe.sh

