
嗯,用户让我总结一篇文章,控制在100字以内,而且不需要特定的开头。我先看看文章内容。文章讲的是一个名为Coruna的漏洞工具包,它是之前Operation Triangulation活动使用的框架的演变。Coruna针对的是iPhone,特别是使用A17和M3芯片的设备,以及iOS 17.2及以下版本的操作系统。 文章提到Coruna包含五个完整的iOS漏洞链,利用了23个漏洞,其中两个CVE编号在之前的活动中也被使用过。Kaspersky的研究人员分析后发现,Coruna使用的漏洞是之前活动的升级版,并且代码相似,说明它是之前的恶意框架的继任者。 攻击过程是从Safari开始的,通过一个加载器来识别设备信息,选择合适的远程代码执行和PAC漏洞,然后下载加密的元数据。有效载荷会下载加密组件,使用ChaCha20解密,LZMA解压缩,并解析自定义容器格式来获取包信息。根据设备架构和iOS版本选择合适的内核漏洞、Mach-O加载器和启动器来部署间谍软件植入。 此外,Coruna还支持ARM64和ARM64E架构,并且可以针对不同版本的iOS进行攻击。研究人员发现Coruna已经被用于金融动机的活动,比如通过虚假交易所网站窃取加密货币。 苹果公司已经发布了安全更新来修复这些漏洞。 总结一下:Coruna是一个针对iPhone的新漏洞工具包,利用多个零日漏洞攻击现代硬件和操作系统版本,并且是之前Operation Triangulation活动的升级版。它支持最新的芯片和多个iOS版本,并被用于间谍活动和金融犯罪。 </think> 文章介绍了名为Coruna的iPhone漏洞工具包,其基于2019年Operation Triangulation活动使用的框架开发,并针对A17、M3等现代芯片及iOS 17.2以下系统设计。该工具包包含五个完整的iOS漏洞链,利用23个漏洞(包括CVE-2023-32434和CVE-2023-38606),并支持ARM64/ARM64E架构及多种iOS版本。Kaspersky分析显示其为Operation Triangulation框架的升级版,并已被用于间谍活动及金融犯罪。 2026-3-26 13:15:13 Author: www.bleepingcomputer.com(查看原文) 阅读量:25 收藏

The Coruna exploit kit is an evolution of the framework used in the Operation Triangulation espionage campaign, which in 2023 targeted iPhones via zero-click iMessage exploits.
The software has been expanded to target modern hardware, specifically including Apple's A17 and M3 chips, as well as operating systems up to iOS 17.2.
Coruna contains five full iOS exploit chains leveraging 23 vulnerabilities, among them CVE-2023-32434 and CVE-2023-38606 also used in Operation Triangulation.
After analyzing the exploit code for the two security issues, Kaspersky researchers determined that Coruna ran an updated version of the exploit used in Operation Triangulation that had started since 2019.
Additional code similarities led to the conclusion that the kit is the successor to the malicious framework leveraged in the Triangulation campaign that also targeted iPhones on Kaspersky's network.
“During our analysis we’ve discovered that the kernel exploit for CVE-2023-32434 and CVE-2023-38606 vulnerabilities used in Coruna, in fact, is an updated version of the same exploit that was used in Operation Triangulation,” the researchers say in a report today.
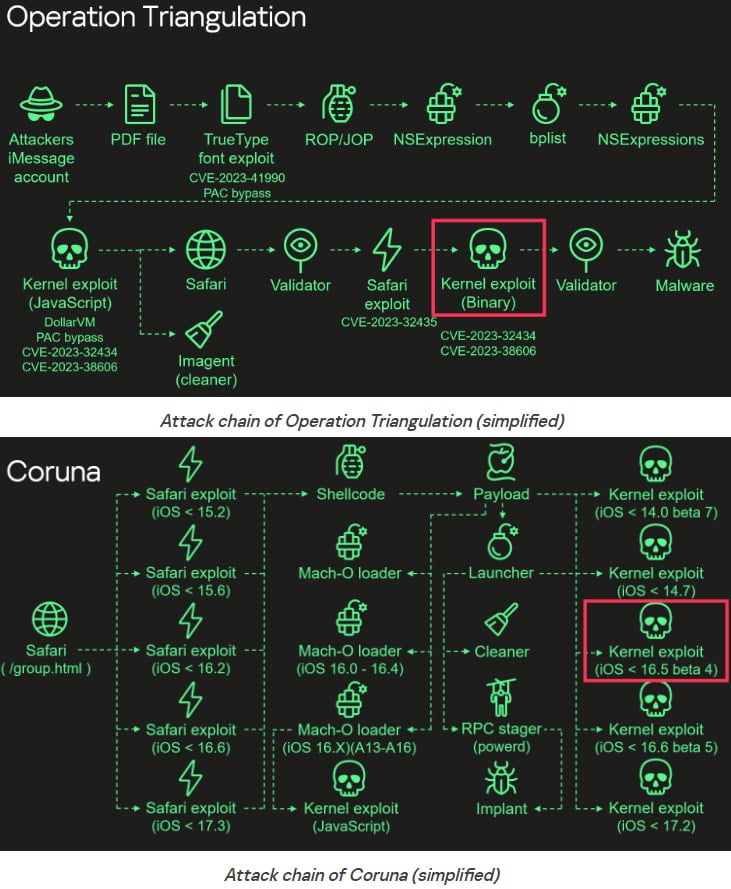
Kaspersky's analysis shows that the attack begins in Safari with a stager that fingerprints the device, selects suitable RCE and PAC exploits, and then retrieves encrypted metadata for subsequent stages.
The payload downloads additional encrypted components, decrypts them using ChaCha20, decompresses them with LZMA, and parses custom container formats to obtain package information.
Based on the device’s architecture and iOS version, it selects and executes the appropriate kernel exploit, Mach-O loader, and launcher to deploy the spyware implant.
Kaspersky’s findings indicate that the payloads support targeting ARM64 and ARM64E architectures, with explicit checks for A17, M3, M3 Pro, and M3 Max chips.
Also, the package IDs and system checks indicate that the exploits can target:
- iOS < 14.0 beta 7
- iOS < 14.7
- iOS < 16.5 beta 4
- iOS < 16.6 beta 5
- iOS < 17.2
Boris Larin, principal security researcher at Kaspersky Global Research and Analysis Team (GReAT), says the connection with Triangulation became evident after analyzing Coruna's binaries.
"Coruna is not a patchwork of public exploits; it is a continuously maintained evolution of the original Operation Triangulation framework."
Additionally, the developers continued to update the framework by including checks for newer processors (e.g., M3) and iOS builds.
Since Coruna has also been used in financially-motivated campaigns aiming to steal cryptocurrency via fake exchange websites, Larin notes that "what began as a precision espionage tool is now deployed indiscriminately."
Operation Triangulation was a highly sophisticated iOS espionage campaign that used multiple zero-day exploits to silently infect iPhones and deploy spyware implants.
It was discovered by Kaspersky during internal WiFi network monitoring in June 2023, though the campaign had started four years earlier.
In late 2023, the same researchers found that these attacks leveraged undocumented features in Apple chips to bypass hardware-based security protections.
Another exploit kit, dubbed DarkSword, was disclosed earlier this month by researchers at mobile security companies Lookout and iVerify, and Google.
Like Coruna, DarkSword is being used by multiple threat actors, but all appear to be leveraging it for espionage operations. It should be noted that DarkSword is now publicly available, which increases the risk of cybercriminals starting to leverage it against unpatched iPhones.
Apple has published a bulletin to address all these recently uncovered exploit kits, noting that fixes for all flaws have been made available via security updates for the latest, as well as earlier, iOS versions.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
