It’s only on rare occasions that anyone pays attention to the acknowledgment section of a vulnerability disclosure.
But for the person who found the bug, it’s often the conclusion of hours of work, trial and error, searching for recognition, and finally seeing the vulnerability get patched. Bug hunters are doing us all a huge favor when they responsibly disclose a vulnerability to the vendor.
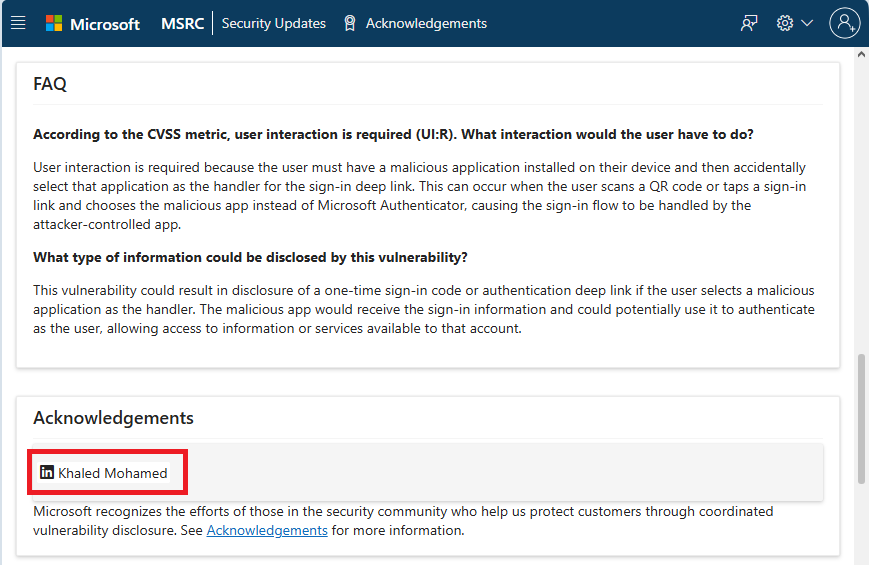
This week we talked to Khaled Mohamed, the bug bounty hunter who found CVE-2026-26123, a flaw in Microsoft Authenticator for both iOS and Android, where, in some cases, another app on your phone could steal or misuse your sign‑in codes.
Q: Tell us a little bit about yourself. How did you end up in cybersecurity?

A: I’m Khaled Mohamed, a 23-year-old security engineer and the founder of SecBound—a cybersecurity startup specializing in penetration testing. Our goal at SecBound is to provide convenient, agile, and affordable testing services that address the security issues that truly matter to our clients.
Besides running SecBound, I work full-time as a Security Engineer and I’m also an active bug bounty hunter. I’ve been listed in the Halls of Fame of several major companies, including Google, GitHub, LinkedIn, Mastercard, Starbucks, and Vimeo. I find it incredibly rewarding to identify significant security issues for some of the most renowned organizations in the world. There’s an amazing feeling that comes with fixing a vulnerability that could have seriously impacted countless users.
My journey into cybersecurity started in a tough and unconventional way.
I was that kid who loved to explore and break things. Eventually, I became a “script kiddie.” I still remember the thrill of knocking my neighbor’s Wi-Fi offline with a simple script and thinking I ruled the world.
From there, I began learning about cybersecurity, especially web security—how websites can be broken, and how to secure them.
When I was 15, I got my first freelance project: web application penetration testing. I completely failed to find any real vulnerabilities, but that experience was a turning point. It pushed me to discover the real science behind cybersecurity. I went on to pursue a degree in Computer Science, and I’m still learning every day. There’s truly no end to it.
I think many people in this field share a similar story. At its core, curiosity is what keeps us moving forward.
Q: Did you set out to find a vulnerability in Authenticator, or did something unusual catch your attention?
A: As I mentioned earlier, I’m a bug bounty hunter, though I wasn’t specifically targeting Microsoft Authenticator at the time. I just happened to notice something unusual in the way the app handled deep links and sign-in flows on mobile devices. When you tap a sign-in link or scan a QR code, the operating system prompts you to “Open Link.”
That made me curious. What would happen if a different app intercepted that action? The more I investigated and experimented, the clearer it became that there was a genuine security issue. Pulling at that thread eventually led me to discover and report CVE-2026-26123.
Q: What surprised you the most about the Authenticator vulnerability?
A: CVE-2026-26123 could lead to a full account takeover in a surprisingly simple way. If a malicious application was installed on the device, and the user scanned a sign-in QR code using the phone’s built-in scanner, their account could effectively be taken over. Even advanced protections such as two-factor authentication (2FA) could be bypassed, leaving all associated Microsoft accounts completely compromised.
The potential real-world impact on multi-factor authentication and passwordless sign-in flows was significant, and that genuinely surprised me.
Q: What advice would you give to aspiring bug hunters or anyone starting out in cybersecurity?
A: Always think like an attacker and train your mindset to identify the potential impact behind every action. Your technical knowledge is just a tool: use it to achieve the impact you’ve envisioned.
Test everything yourself. Don’t assume something is secure just because others have tested it before. Think deeply about how things might still be vulnerable, then work to prove or disprove your assumptions through hands-on testing.
Q: What do you think is the most common mistake made in cybersecurity?
A: One of the most common—and most dangerous—mistakes in cybersecurity is underestimating the real threat level. Many organizations still believe that cyberattacks are rare events or that attackers primarily target large, well-known corporations. In reality, every company, regardless of size or reputation, can become a target.
A: I want people to know that responsible disclosure works. Microsoft responded through their Coordinated Vulnerability Disclosure program, and the patch was released as part of the March 10, 2026 security update, meaning users are now protected.
This process—a researcher discovers an issue, reports it responsibly, and the vendor fixes it—is what keeps the entire ecosystem safer over time. If you find a vulnerability, report it. Don’t sit on it.
We’d like to thank Khaled Mohamed for his time and wish him all the best in his future endeavors.
We don’t just report on phone security—we provide it
Cybersecurity risks should never spread beyond a headline. Keep threats off your mobile devices by downloading Malwarebytes for iOS, and Malwarebytes for Android today.
