MSSQLand is a .NET Framework 4.8 utility designed for interacting with Microsoft SQL Server database management systems during red team operations and security audits. Built for constrained environments where operations must be executed directly through beacons using assembly execution, the tool enables operators to traverse linked SQL Server instances, impersonate users, and execute actions without needing complex Transact-SQL (T-SQL) queries. The project was released in March 2026 and fills a critical gap in SQL Server post-exploitation workflows where traditional database tools are unavailable or impractical.
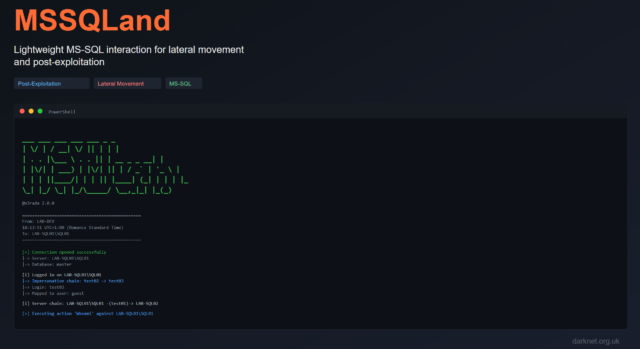
Unlike SQL Server Management Studio (SSMS) or Python-based tools like mssqlclient-ng, MSSQLand is optimized for lateral movement scenarios where an operator already has initial SQL Server access but needs to pivot through linked instances or escalate privileges via impersonation. The tool automates the tedious process of manually crafting Remote Procedure Call (RPC) and OPENQUERY statements across linked server chains, allowing red teams to focus on execution rather than syntax debugging.
Features
- Linked server chain traversal with automatic
OPENQUERYand RPC Out handling for multi-hop SQL Server scenarios - User impersonation via
EXECUTE AS USERto escalate privileges within database contexts without needing system-level permissions - Configuration Manager (ConfigMgr) support for exploiting and enumerating Microsoft Configuration Manager deployments (formerly known as SCCM/MECM)
- Connection testing mode that validates credentials without executing queries, ideal for a minimal OPSEC footprint during reconnaissance
- Clean Markdown-compatible output tables suitable for direct paste into engagement reports and documentation
- CSV export format option for automated processing and integration with other toolchains
- Assembly execution ready, built with Cobalt Strike, Havoc, Sliver, and other C2 frameworks in mind
- Multiple authentication methods, including Windows authentication, SQL Server authentication, and Kerberos tickets (via external tools)
Installation
MSSQLand is distributed as a pre-compiled Windows executable. Download the latest release from the GitHub Releases page and transfer the executable to your target environment or beacon working directory.
# Download from GitHub Releases
# https://github.com/n3rada/MSSQLand/releases
# For operators compiling from source
# Requires Visual Studio with .NET Framework 4.8 SDK
git clone https://github.com/n3rada/MSSQLand.git
cd MSSQLand
# Open MSSQLand.sln in Visual Studio and build for x64 ReleaseThe tool is designed for assembly execution from C2 frameworks. No installation or registration is required on the target system, making it suitable for operations in restricted or monitored environments.
Usage
This repository does not provide a global --help flag in the traditional sense. The following usage information is reproduced verbatim from the README and GitHub documentation.
MSSQLand.exe <host> [options] <action> [action-options]
# Connection test only (no action executed)
MSSQLand.exe localhost -c token
# Execute specific action
MSSQLand.exe localhost -c token info
MSSQLand.exe localhost:1434@db03 -c token info
# Linked server chain traversal
# Format: server:port/user@database or any combination
# Semicolon (;) separates servers, forward slash (/) specifies impersonation
MSSQLand.exe localhost -c token -l SQL01;SQL02/admin;SQL03@clients info
# Configuration Manager actions (cm- prefix)
MSSQLand.exe sccm-db.corp -c token cm-devices
MSSQLand.exe sccm-db.corp -c token cm-scripts
# CSV output for automation
MSSQLand.exe localhost -c token --format csv --silent procedures > procedures.csvThe tool supports flexible host specification, including optional port numbers (default 1433), user impersonation contexts, and database contexts. Linked server chains use semicolon separators and support bracket notation for server names containing delimiter characters. Port specification only applies to the initial host connection; linked servers use configured names from sys.servers.
For detailed action-specific help, use the -h flag with a search term or append -h to an action name. For example, MSSQLand.exe -h adsi shows all Active Directory Services Interface-related actions, while MSSQLand.exe localhost -c token createuser -h displays detailed help for the createuser action.
Attack Scenario
A red team operator gains access to a Windows system during an assumed-breach engagement. The operator discovers that the compromised user account has SQL Server authentication credentials stored in a configuration file. The target environment uses linked SQL Server instances across multiple tiers (web database server, application database server, reporting database server) with trust relationships configured between them. Traditional lateral movement paths via SMB or WinRM are heavily monitored, but database connections are considered normal administrative activity and generate minimal alerts.
The operator loads MSSQLand via Cobalt Strike beacon assembly execution and performs a connection test to validate credentials without triggering database audit logs. The test confirms access to the web tier database server. Using the info action, the operator enumerates linked servers and discovers that the web tier server has an RPC Out trust configured to the application tier server, which in turn links to a reporting server with elevated privileges. The operator constructs a linked server chain using the -l flag, specifying SQL01;SQL02;SQL03, and executes commands through the chain without needing to manually craft nested OPENQUERY statements.
From the reporting server context, the operator discovers a Configuration Manager database. Using MSSQLand’s cm- prefixed actions, the operator enumerates managed devices, scripts, and deployment packages. The cm-devices action reveals high-value targets, including domain controllers and executive workstations. The operator extracts device records, identifies targets with recent check-in timestamps, and uses the information to prioritize next-stage objectives. The entire reconnaissance and lateral movement phase completes without generating suspicious PowerShell or WMI events, as all activity flows through legitimate SQL Server protocols.
Red Team Relevance
SQL Server lateral movement remains underexploited in many red team engagements despite its prevalence in enterprise environments. Linked server trust relationships frequently span security boundaries, allowing operators to pivot from low-privilege web application databases to highly privileged reporting or Configuration Manager instances. MSSQLand removes the primary friction point in SQL Server post-exploitation: the need to manually construct and debug nested T-SQL queries while operating through a beacon or constrained shell.
The tool’s assembly execution design makes it particularly valuable for C2 frameworks where interactive console sessions are limited or monitored. Operators can execute complex multi-hop database traversals with a single-line command, reducing engagement time and minimizing the detection surface. The Configuration Manager support is especially relevant given that SCCM/MECM databases are high-value targets for privilege escalation and infrastructure mapping, yet often lack the hardening applied to Active Directory or endpoint management systems.
MSSQLand also addresses OPSEC considerations that plague traditional database tools. Connection testing without query execution allows credential validation without touching audit-logged tables. The clean output format integrates directly into reporting workflows, reducing the post-engagement effort required to document database access paths. For operators who regularly encounter SQL Server instances during engagements, MSSQLand provides capabilities similar to what BlockEDRTraffic offers for EDR evasion, what SmbCrawler provides for SMB share enumeration, or what CredNinja delivers for credential validation: a focused, practical tool that solves a specific operational problem without requiring extensive T-SQL knowledge.
Detection and Mitigation
SQL Server audit logging should be configured to capture connection attempts, privilege changes via EXECUTE AS USER, and cross-server queries using linked servers. Organizations should monitor for unusual linked server traversal patterns, especially chains that originate from web-facing database servers and terminate at privileged infrastructure databases. Access to the Configuration Manager database by non-administrative accounts warrants immediate investigation, as these databases contain sensitive device inventory and deployment information.
Network segmentation should restrict database server communication to legitimate application tiers. Web tier databases should not have direct RPC Out trust relationships to reporting or management databases. Where linked servers are required for business functionality, implement the principle of least privilege by restricting linked server login mappings to specific service accounts with minimal permissions. Disable xp_cmdshell and other extended stored procedures unless explicitly required and audited.
Blue teams should deploy database activity monitoring solutions that detect OPENQUERY and EXECUTE AT usage patterns inconsistent with normal application behavior. Anomalous login times, source IP addresses outside expected ranges, and rapid sequential queries across linked instances are reliable indicators of post-exploitation activity. For Configuration Manager environments, restrict database access to designated SCCM infrastructure servers and alert on any connections from workstations or non-administrative hosts.
Frequently Asked Questions
What is MSSQLand and how is it different from SQLRecon?
MSSQLand is a .NET Framework 4.8 tool for interacting with Microsoft SQL Server instances during red team operations. Unlike SQLRecon, MSSQLand was built from the ground up with object-oriented programming principles for easier extensibility and modular action development. It simplifies traversal of linked server chains and user impersonation without requiring operators to manually craft complex T-SQL queries.
Does MSSQLand work with Cobalt Strike and other C2 frameworks?
Yes. MSSQLand is designed specifically for assembly execution from C2 frameworks, including Cobalt Strike, Havoc, Sliver, and similar platforms. The tool requires no installation or registration on the target system, making it ideal for operations in constrained or monitored environments where traditional database tools are unavailable.
Can MSSQLand traverse multiple linked SQL Server instances?
Yes. MSSQLand automates linked server chain traversal using the -l flag with semicolon-separated server names. The tool automatically generates the necessary OPENQUERY and RPC Out statements, allowing operators to pivot through multiple SQL Server instances without manually crafting nested T-SQL queries. For example, MSSQLand.exe localhost -c token -l SQL01;SQL02;SQL03 info chains through three servers in a single command.
What authentication methods does MSSQLand support?
MSSQLand supports Windows authentication and SQL Server authentication, and can work with Kerberos tickets when used with external ticket injection tools. The tool also supports user impersonation via EXECUTE AS USER to escalate privileges within database contexts without requiring system-level permissions on the target server.
Does MSSQLand support Microsoft Configuration Manager (SCCM) exploitation?
Yes. MSSQLand includes comprehensive Configuration Manager support with cm- prefixed actions that align with Microsoft’s official PowerShell cmdlet naming convention. Operators can enumerate managed devices (cm-devices), scripts (cm-scripts), packages, and other ConfigMgr infrastructure to identify high-value targets and prioritize next-stage objectives during engagements.
How does MSSQLand maintain OPSEC during database reconnaissance?
MSSQLand includes a connection testing mode that validates credentials without executing queries, allowing operators to verify access without touching audit-logged tables. The tool also provides CSV export options for automated processing, reducing the need for interactive console sessions that might generate suspicious activity logs. All operations flow through legitimate SQL Server protocols rather than PowerShell or WMI, minimizing detection surface in monitored environments.
Conclusion
MSSQLand addresses a practical gap in red team tooling for SQL Server post-exploitation. Its focus on linked server traversal, user impersonation, and Configuration Manager enumeration makes it directly applicable to real-world engagements where database access exists, but traditional lateral movement paths are blocked or monitored. The tool’s design for assembly execution and its minimal OPSEC footprint align with modern C2 workflows, and its clean output format reduces friction in both the operational and reporting phases of engagements. For red teams operating in Windows enterprise environments, MSSQLand is a focused addition to the lateral movement toolkit that complements broader frameworks without requiring extensive database expertise.
You can read more or download MSSQLand here: https://github.com/n3rada/MSSQLand