嗯,用户让我用中文帮他总结一下这篇文章,控制在一百个字以内,而且不需要以“文章内容总结”或者“这篇文章”这样的开头,直接写文章描述即可。好的,我先看看这篇文章讲的是什么。 文章主要讲的是一个叫做Silver Fox的网络入侵组织,他们来自中国。这个组织最初是为了财务动机进行攻击,比如窃取钱财或者数据。但自从2024年开始,他们逐渐转向更复杂的、类似高级持续性威胁(APT)的活动。这意味着他们的攻击变得更加隐蔽和有针对性,可能涉及到间谍活动或者长期潜伏。 文章还提到,Silver Fox使用了多种恶意软件工具,比如ValleyRAT和HoldingHands。这些工具帮助他们在目标系统中建立持久的访问权限,并进行数据窃取或其他恶意活动。此外,他们还利用了一些合法但配置错误的远程监控管理(RMM)工具来分发恶意软件,这使得他们的攻击更加难以被发现。 除了进行复杂的APT活动外,Silver Fox仍然进行一些传统的网络犯罪活动,比如针对南亚地区的金融诈骗。他们使用了一些在中国网络犯罪生态系统中常见的恶意软件,如Blackmoon。这些活动通常是大规模的、机会性的,并不特别针对某个特定的目标。 文章还提到,在2025年至2026年间,Silver Fox的攻击手法发生了变化。他们从使用ValleyRAT转向了滥用合法的RMM工具,并最终转向了基于Python的数据窃取器。这种转变显示了他们为了适应不同的目标和环境而不断调整其策略的能力。 最后,文章总结了Silver Fox的双重目标:一方面进行复杂的间谍活动和长期潜伏;另一方面继续进行传统的、以利润为导向的网络犯罪活动。这种双重策略使得他们在网络安全威胁领域显得更加复杂和难以应对。 总的来说,这篇文章详细描述了Silver Fox组织在2025年至2026年期间的攻击活动、使用的工具以及他们的双重目标。 </think> 这篇文章介绍了中国网络入侵组织Silver Fox近年来的行为变化。该组织最初以财务动机为主导展开攻击活动,但自2024年起逐渐转向更复杂的APT式操作,同时仍保持传统网络犯罪行为,形成双轨模式。文中详细分析了其使用的恶意软件工具、感染链演变以及针对南亚地区的最新攻击活动,揭示了其兼顾情报收集与经济利益的双重目标。 2026-3-24 08:18:21 Author: blog.sekoia.io(查看原文) 阅读量:34 收藏
Since early 2025, TDR has focused on tracking Silver Fox, a China-based intrusion set. Originally known for financially motivated attacks, the group has been shifting toward more sophisticated, APT-style operations since at least 2024. This dual focus reflects a broader trend observed throughout 2025, which is the increasingly blurred lines between financially motivated cybercrime operators and state-sponsored espionage.
Silver Fox relies on ValleyRAT (aka Winos), which can be considered as its primary modular backdoor. Despite the leak of ValleyRAT builder in March 2025, the intrusion set continued to use it, exploiting zero-day driver plugin and using kernel-mode rootkit likely for intelligence collection. In addition, Silver Fox relies on other malicious payloads like HoldingHands, which is a variant of Gh0st RAT. Rather than replacing ValleyRAT, it appears to be deployed alongside it to achieve specific operational goals.
In parallel with APT-like activities, Silver Fox still operates financially-motivated campaigns targeting less critical objectives. These operations typically leverage ubiquitous malware from the Chinese cybercrime ecosystem, such as Blackmoon.
TDR’s monitoring highlights an evolution throughout 2025 and 2026 in the group’s arsenal, transitioning from advanced backdoors like ValleyRAT to RMM tool, and more recently, to Python-based stealer. This observation confirms that despite its 2024 pivot toward APT-style operations, Silver Fox continues to conduct opportunistic, lucrative campaigns across South Asia.
This report presents findings on recent Silver Fox campaigns highlighting its dual objectives, with a specific focus on its arsenal and infrastructure.
Key Takeaways
> Silver Fox’s attack campaigns evolved between 2025 and 2026, transitioning from the ValleyRAT malware delivered via malicious PDF attachments to abusing a legitimate but misconfigured Chinese Remote Monitoring and Management (RMM) tool, and most recently, deploying a custom Python-based stealer disguised as a WhatsApp application.
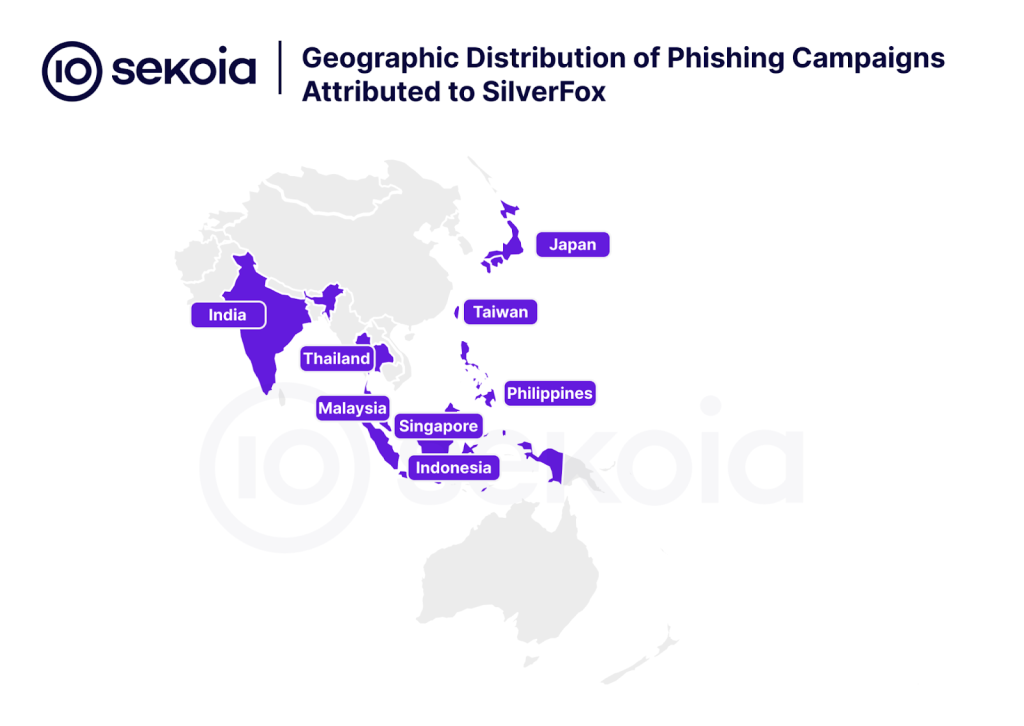
> The threat actor consistently uses culturally relevant lures that impersonate national taxation authorities or payroll documents to gain initial access. The campaign broadened its scope to target entities across a wide range of South Asian countries, including Taiwan, Japan, Malaysia, India, Indonesia, Singapore, Thailand, and the Philippines.
> While recent reports highlight Silver Fox’s transition toward APT-style operations using the modular ValleyRAT and HoldingHands frameworks, TDR observes a persistent commitment to traditional cybercrime. The group maintains a dual-track model, running broad, opportunistic campaigns alongside its more sophisticated operations by continuously evolving its tooling.
Intrusion Set Profile
Silver Fox (aka Void Arachne) is a China-based intrusion set active since at least 2022. It started by conducting financially-motivated campaigns before switching toward both lucrative and espionage operations in 2024.
Silver Fox has primarily conducted mass infection, likely impacting opportunistically individuals in China and South Asia. It delivered ValleyRAT (aka Winos) using SEO poisoning via gaming or AI-related applications, or fake VPN software, which are popular among individuals looking to evade online censorship enforced by the Great Firewall. The way the threat actor ends up generating profit remains unknown, as ValleyRAT enables a large panel of actions, from keystroke logging, to security bypass, remote system control, and data exfiltration.
By November 2024, Silver Fox was reported targeting Chinese and Vietnamese-speaking users through infected MSI installers. The evolution of its arsenal, including CleverSoar installer and Nidhogg rootkit, suggested this intrusion set engaged in a more advanced post-exploitation toolkit likely to conduct espionage along with lucrative campaigns.
In January 2025, Silver Fox leveraged tax-themed phishing content by impersonating national taxation authorities and lure its victims into opening a malicious PDF. The document then delivered ValleyRAT using DLL side-loading. According to Fortinet, this campaign, which first impacted entities based in China and Taiwan, extended to target professionals also in Japan and Malaysia.
A hypothesis is that Silver Fox conducts both massive, less sophisticated operations for financial gain, as well as strategic campaigns for intelligence collection or to maintain a foothold in the systems of specific targets. This type of activity can likely be attributed to cybercrime operators selling access to state-sponsored groups or to a private actor outsourcing initial access capabilities to a State while operating moonlighting activities.
Arsenal evolution
ValleyRAT, which was characteristic of Silver Fox’s infection chain, had its builder leaked in March 2025. After the leak, this intrusion set continued to deliver ValleyRAT and exploited its modular plugin-based architecture to develop sophisticated additional plugins likely to evade detection and ensure persistent access. For instance, in August 2025, CheckPoint identified the abuse of a Microsoft-signed driver, amsdk.sys, to bypass Microsoft Vulnerable Driver Blocklist and detection by community projects.
By October 2025, Silver Fox campaigns also started to leverage HoldingHands, which is a variant of Gh0st RAT, a well-known malware family used in the Chinese cybercrime ecosystem. HoldingHands does not seem to replace ValleyRAT, which continues to be associated with recent Silver Fox’s campaigns. However, it is likely that HoldingHands is used as a more “premium” tool for specific, high-value espionage operations.
Consequently, the modular nature of Silver Fox’s arsenal enables the group to rapidly adapt its infection chains, maintaining a low profile while ensuring long-term access. This agility allows Silver Fox to execute advanced operations in tandem with more traditional, profit-driven cybercrime.
Latest campaigns features
Despite some variants, Silver Fox infection chain and infrastructure remain quite the same since 2023. However, the increasing use of stealthy techniques, like kernel-mode rootkit, confirmed the trend observed since at least 2024, hinting at more complex motivations. Silver Fox likely pursues its dual objectives, conducting APT-like operations along with lucrative campaigns.
Of note, Silver Fox latest reported campaigns continued to feature:
- Lures that impersonate national taxation authorities and corporations to deliver ValleyRAT, using both malicious files embedded in emails and fake applications;
- SEO poisoning to drive traffic from malicious payloads to C2 servers, using malicious ads and Telegram.
- Blurred objectives with infection chains that can likely align with intelligence collection purposes, as well as financial gain.
Silver Fox Campaigns: a Three Waves Evolution
Between 2025 and 2026, TDR monitored a malicious campaign impersonating national taxation authorities to infect victims in South Asia. While maintaining a consistent infrastructure, the campaign underwent several updates, evolving in both its victimology and infection methods. To date, the TDR team identified three different waves in Silver Fox recent campaigns.
This section highlights an early investigation in Taiwan during heightened geopolitical tensions and examines the group’s technical shift from abusing misconfigured RMM tools to a Python-based stealer.
Given Silver Fox’s dual motivations, the initial campaign targeting Taiwan during the national tax audit window suggests a strategic alignment with APT-style operations. However, the discrepancies identified in the phishing lures indicate a degree of opportunistic targeting rather than a surgical espionage operation. The subsequent two waves, being more widespread and geographically diverse, appear to align with traditional profit-driven cybercrime.
First wave: Focus on Taiwanese entities
Since at least January 2025, Silver Fox conducted a campaign impersonating national taxation authorities for initial access. It focused on Taiwanese entities and exploited a national tax audit selection to lure victims into opening a malicious PDF file sent by email, which was used to deploy ValleyRAT.
Background and context
At the 2025 Shangri-La Dialogue Security Summit, US Defense Secretary Pete Hegseth warned that a Chinese invasion of Taiwan “could be imminent,” following Beijing’s reaffirmed resolve to defend its sovereignty. These tensions underscore a growing crisis as the CIA previously indicated that President Xi aims for readiness by 2027, a claim supported by intensifying military drills and the discovery of mock-up Taiwanese government districts in Inner Mongolia.
In this tense geopolitical context, Taiwan faces a surge in Chinese offensive cyber operations, notably marked by state-sponsored operations attributed to Salt Typhoon and APT10, likely directed to intelligence collection and critical infrastructure prepositioning.
At the same time, cybercrime operators have targeted Taiwanese entities to make profit, such as CrazyHunter ransomware operators or Silver Fox. This type of threat, not formerly attributed to China and more opportunistic than cyberespionage operations, comes on top of those already hanging over the island. These campaigns notably rely on trusted relationships with partners or the administration to entice the targeted entity to download or click on a link in order to deploy the malicious payload.
In the case of this campaign, malicious operators took advantage of a communication dating back to January 8th, 2025 of the Taiwanese Ministry of Finance indicating that the audit selection for profit-seeking enterprises will soon begin. Indeed, operators crafted a PDF document mimicking the announcement by the Ministry of Finance of the list of enterprises selected for the audit. It entices the reader to click on PDF, which enables the deployment of the malicious payload.
Delivery method and initial access
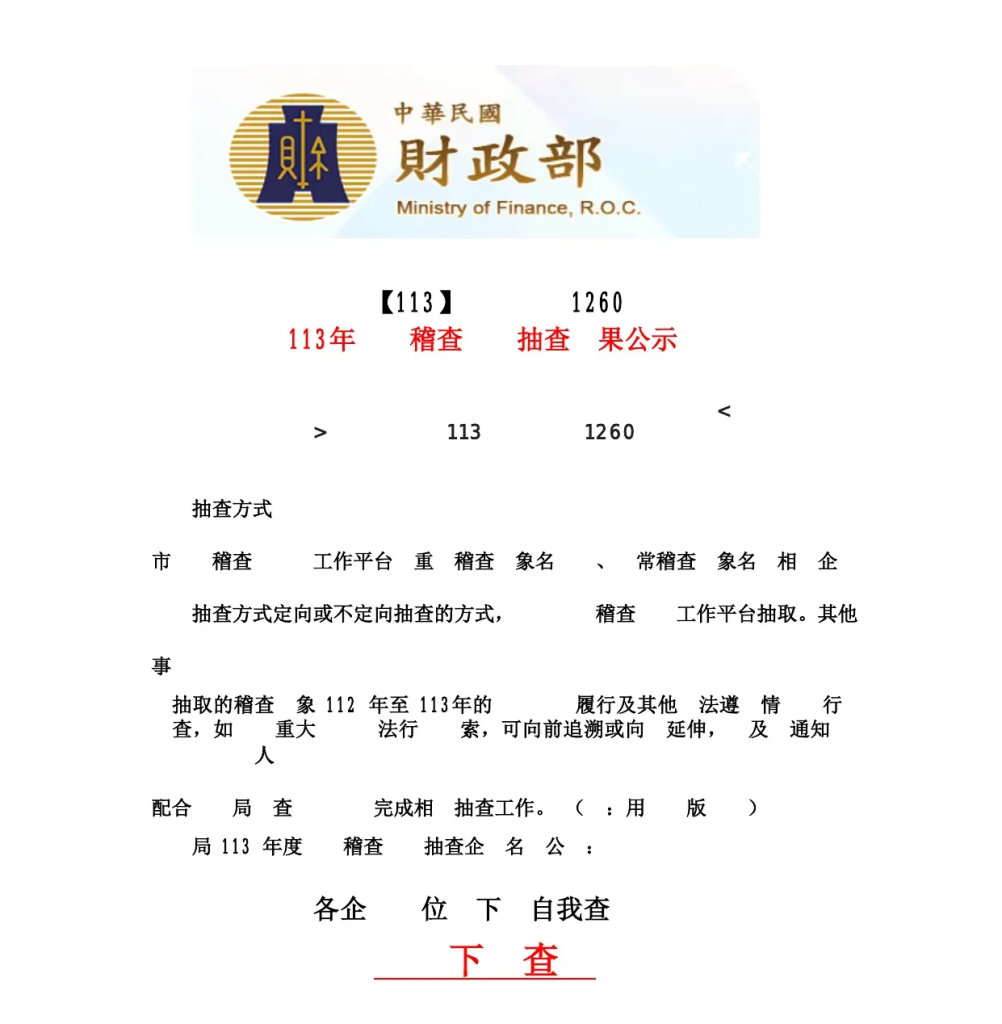
This campaign started by a short phishing email impersonating the tax authorities of Taiwan. The email contained a PDF in attachment. Once victims get lured by the Tax theme of the email and open the PDF file the execution of malicious payload begins. The infection chain was as follow:
- Phishing email ;
- PDF with a
/Annoton the all file to be hidden behind a clickable area in the PDF that triggers a second stage (ZIP) download from myqcloud infrastructure (kind of bucket) ; - The ZIP contains two files
python311.dlland查看10.exe; - Python311.dll act as a shellcode to execute the last stage ;
- Execute ValleyRAT whose configuration is downloaded in the public directory:
c:\users\public\download\bb.jpg
See below the Indicators of Compromise for this infection:
- PDF: e2b75baeb7ed21fb8f27984f941286770d1c3c0b60fce8d7fa5b167bd24ba6dc
- Bucket addresses:
https://6-1321729461.cos.ap-guangzhou.myqcloud[.]com/lnstaller.msihttps://00-1321729461.cos.ap-guangzhou.myqcloud[.]com/2024.7z
- C2:
9010.360sdgg[.]com
Lure Themes and Messaging
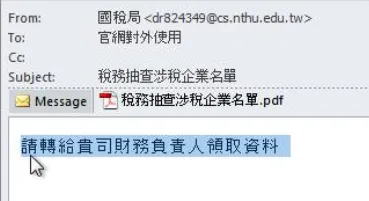
The email came from a legitimate looking address, which seems to belong to the National Tsing Hua University of Hsinchu in Taiwan. However, a quick check on the Have I Been Pwned database revealed that the address was part of a leak, which suggests it may be hijacked.
The translation of the different elements of the mail is:
- From: “National Tax Administration”
- To: “Official Website External Use”
- Subject: “List of Companies Suspected in Tax Audit”
- Attachment filename: “List of Companies Involved in Tax Inspection.pdf”
And the body of the message is: “Please forward this to your company’s finance officer to collect the documents.”
The email was brief and designed to incite either fear or curiosity in the recipient. However, several discrepancies were observed. While the content impersonated the national taxation authority, the sender’s address was linked to a Taiwanese university. This mismatch between a government lure and an academic sender, combined with a message directed at the private sector, suggests that the campaign was likely opportunistic or, at least, with a broad targeting.
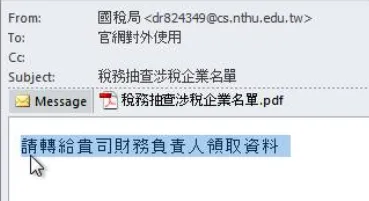
The PDF was an announcement from the Ministry of Finance (Taiwan, ROC) regarding the tax audit selection results for Year 113 (2024 in the Gregorian calendar). It explained the methods of selection and emphasised that the audit indicators are based on previous years’ data, including legal violations. Enterprises were encouraged to conduct internal reviews and self-checks to prepare for potential audits.
NB: A translated version of the PDF is provided in Annex 1.
In April 2025, Fortinet identified an expansion of this campaign targeting also Japanese entities.
Second wave: the RMM shift
In mid-December 2025, a new Silver Fox operation was identified by TDR and other cybersecurity editors. It was characterised by a broader targeting, including entities in Malaysia, the Philippines, Thailand, Indonesia, Singapore and India. This new version likely aligns with more typical profit-driven operations.
In comparison to the first campaign, Silver Fox leveraged part of its existing infrastructure, with several known domains, to execute a broader phishing campaign. Based on these IoCs, it was possible to pivot on a new infrastructure. The latest was reviewed and simplified regarding server hosting. The threat actor retains several old registered domains to continue delivering its malware, notable domains include: googlevip[.]icu, oytdwzz[.]shop andyvxyngw[.]cn.
The initial access was made using a phishing email that fits the tax organisation’s communication style of the targeted victims’ countries. Contrary to the initial campaign, which leveraged PDF files directly included in the email, this new version embedded the link to the fake Tax phishing website in the mail body. The content of the mail was crafted to encourage the victim to visit the website and download a file.
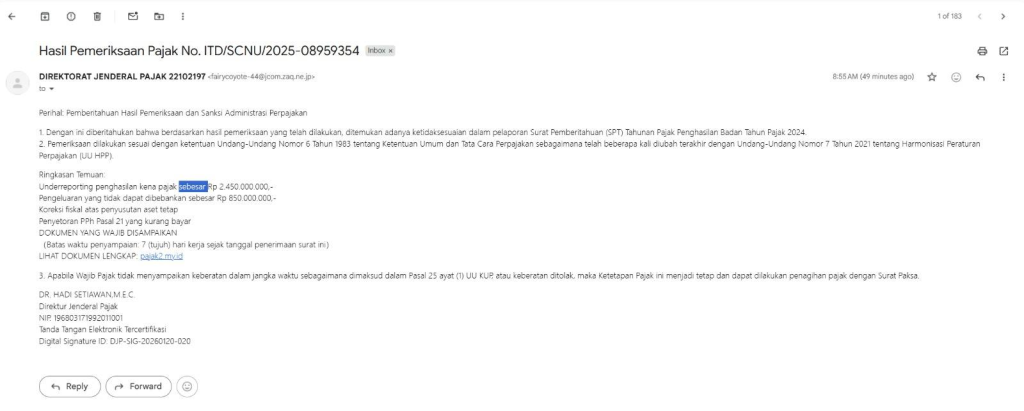
Since 2026, the file has been an archive, either a ZIP or a RAR file. The archive contains one PE32+ executable file.
The executable file is a legitimate Chinese RMM tool, as highlighted in the eSentire report. The binary was digitally signed by the “SyncFutureTec Company Limited”. By pivoting on the PE signature thumbprint signature:F9EAAB0F05BD38A251427A05F95386CA7CEDDCE8 on VirusTotal and filtering on parent process being a compressed file, other samples can be identified. The list of hashes related to the compressed file dropping the RMM tool can be found in the section Indicator of Compromise.
The RMM files follow a specific name format: “[ipv4] + ClientSetup.exe”. In this case, the IPv4 string acts as the C2 address. The threat actor exploited a configuration handling misconfiguration in the legitimate RMM tool to pass the C2 parameters directly via the filename, thereby avoiding any alteration to the file signature.
TDR also identified the filename: 45.119.55.]66ClientSetup.exe. Based on this naming convention, additional C2 were uncovered, with a complete list of associated IPv4 addresses provided in Annex 2. These indicators should be used for hunting or retro-hunting. Indeed, there is no sufficient evidence regarding the origins and the related infection chains to validate whether these C2s remain operational or if they were exclusively used by the Silver Fox operators.
Third wave: Python stealer to target Malaysia
In February 2026, the downloaded payload from the phishing website was replaced. The threat actor stopped using the RMM tool and switched to a compiled Python stealer.
In this new campaign, the website identified delivering the payload was in Malay, indicating the targeting of Malaysia. However, based on previous campaigns, it is likely that Silver Fox continues to operate more broadly against entities in South Asia.
The deployment of this custom Python stealer opens the door to various malicious activities. Beyond potential espionage, the compromised credentials facilitate financial operations including Business Email Compromise (BEC), data resale, etc.
The executable runs a Python stealer that mimicates a WhatsApp application. The code is straightforward as it collects multiple artefact of interest on the infected device and uploads them to its C2 that is xqwmwru[.]top. This domain points to an IP address in the same CIDR as the phishing website.
In this version, the phishing website is hosted at 154.201.87[.]75 and the fake WhatsApp C2 is in the same address block: 154.201.87[.]124.
A similarity with previously observed Silver Fox campaigns is the use of custom User-Agent with a version 1.0. Here, the User-Agent: WhatsAppBackup/1.0. is used.
Even the C2 server attempts to look like a legitimate WhatsApp web server.

The executable leaves some singular artefacts on compromised host, such as:
C:\\WhatsAppBackup\\WhatsAppData.zip%TEMP%\\whatsapp_backup.lock
The contacted URLs by the stealer are:
https://xqwmwru[.]top/upload_large.phphttps://xqwmwru[.]top/upload_status.php
The second and third campaigns leaning on the RMM tool and Python stealer appear to align more closely with opportunistic cybercrime than APT operations. This hypothesis is supported by the broader targeting, the absence of the modular ValleyRAT backdoor and the less sophisticated delivery mechanisms.
Furthermore, the payloads of an abused commercial RMM tool and a custom Python-based stealer designed to collect credentials are general-purpose tools favored in the cybercrime ecosystem, while the use of tax-themed phishing lures serves as a sector-agnostic method for initial access, further better aligned with a profit-driven objective.
Victimology
These three 2025-2026 Silver Fox campaigns targeted entities in South Asia. It started impacting mainland China and Taiwan, and followed with the targeting of Japan, Malaysia, the Philippines, Thailand, Indonesia, Singapore and India.
Initial TDR investigation from early 2025 suggested Silver Fox synchronized its delivery phase with a national tax audit window in Taiwan to maximise lure efficacy. However, subsequent iterations of the campaign drifted from specific policy-driven timelines.
We assess that the threat actor shifted toward a more generalised ‘financial-thematic’ approach, leveraging tax and accounting lures as a sector-agnostic baseline for maintaining a persistent initial access method and potentially making financial gain.
Conclusion
While Silver Fox relies on the ValleyRAT modular backdoor likely for advanced operations, TDR assesses this threat actor continues to conduct profit-driven campaigns in South Asia, adapting its arsenal and delivery methods.
Despite this dual motivation, the core TTPs of Silver Fox remain consistent, using culturally relevant tax/finance lures to gain initial access, maintaining a versatile malware ecosystem, and rapidly adapting infrastructure and evasion techniques.
The recent shift to using an RMM tool for delivery and a custom stealer indicates Silver Fox’s continuous effort to maintain a low profile and avoid detection while pursuing both lucrative and strategic goals across South Asia.
External References
- Rapid7 -New “CleverSoar” Installer Targets Chinese and Vietnamese Users
- Trend Micro – Behind the Great Wall Void Arachne targets Chinese-speaking users
- eSentire – Winos4.0 “Online Module” Staging Component Used in CleverSoar Campaign
- eSentire – Weaponized in China, Deployed in India: The SyncFuture Espionage Targeted Campaign
- Fortinet -Winos 4.0 Spreads via Impersonation of Official Email to Target Users in Taiwan
- Fortinet – Tracking Malware and Attack Expansion: A Hacker Group’s Journey across Asia
- Fortinet – Winos 4.0 Spreads via Impersonation of Official Email to Target Users in Taiwan
- Check Point – Chasing the Silver Fox: Cat & Mouse in Kernel Shadows
- The Economist – There is an “imminent” threat to Taiwan, America warns
- Ministry of Foreign Affairs of the People’s Republic of China – Foreign Ministry Spokesperson Lin Jian’s Regular Press Conference on May 30, 2025
- Reuters – CIA chief warns against underestimating Xi’s ambitions toward Taiwan
- France 24 – Taipei replica in remote Chinese province fans Taiwan invasion fears
- Ministry of Finance, R.O.C. (Taiwan) – Profit-seeking enterprises CFC audit selection will soon begin. Please pay attention to the four main audit points.
Annex
Annex 1 – Translation of the PDF
Ministry of Finance, R.O.C.
【Year 113】1260
Year 113 Tax Audit Random Selection Results Announcement
Audit Method:
The tax audit will be conducted through the Tax Audit Work Platform using both focused and regular audit indicators.
The selection method is either directed or random, using the Tax Audit Work Platform and other methods.
Matters:
The selected audit indicators are based on situations from Year 112 to Year 113, including suspected legal violations or irregularities.
For serious legal cases, investigations may be extended retroactively and relevant parties will be notified.
Tax authorities will cooperate to complete related audit tasks. (For official use)
The list of enterprises selected for tax audit in Year 113 is announced as follows:
All enterprises are advised to conduct self-checks
Self-Check
Annex 2 – RMM tool filename IPv4 address
115[.]187.17.212
112[.]121.183.102
156[.]251.18.45
206[.]238.178.116
112[.]213.120.164
47[.]85.99.19
216[.]250.104.166
45[.]119.55.66
69[.]30.250.99
103[.]228.12.151
103[.]97.128.142
156[.]254.5.118
156[.]251.18.238
112[.]121.183.106
45[.]119.55.112
115[.]187.17.68
103[.]231.12.45
103[.]97.128.103
45[.]194.37.147
220[.]167.103.145
103[.]97.128.109
130[.]250.191.46
103[.]203.48.174
154[.]91.84.3
93[.]127.142.77
220[.]167.103.160
154[.]12.87.28
150[.]109.79.82
220[.]167.103.158
170[.]205.54.88
116[.]213.43.23
103[.]231.12.23
222[.]186.190.138
103[.]70.76.130
154[.]44.28.175Indicator of Compromise
Phishing websites used by Silver Fox
ksdfuefagfrukayhfka[.]eu[.]cc
rdhrse[.]qpon
googlevip[.]icu
oytdwzz[.]shop
cocdex[.]cn
nao[.]nnnwin[.]vip
googlehfgj[.]cyou
fhauifhyileydhfl[.]com
megamovielord[.]com
fzdoor[.]vip
amvcoins[.]vip
peyvz[.]com
sdyteq[.]shop
ksudeu[.]nanguanglu[.]com
domainct[.]com
host-hunter[.]com
domainca[.]top
fghs[.]shlowcarbon[.]com
jinmai[.]vip
opkllasyy[.]shop
fdfhddfss[.]top
udste[.]xidyuyedg[.]qpon
swy[.]juanseguros[.]com
primetechstocks[.]com
juanseguros[.]com
mohaazon[.]com
fkfjrvfa[.]cn
zibenbang[.]vip
zptsgryw[.]cn
betooo[.]vip
czxfdz[.]com
sgeshex[.]vip
eaxwwyr[.]cn
wwfygid[.]biz[.]id
sgegdvip[.]vip
morecoworking[.]com
gov[.]incometax[.]click
yigushengjin[.]com
gofjasj[.]help
isyraw[.]quidoaehse[.]icu
xueshirencai[.]com
wgooglegoogle[.]com
gfmqvip[.]vipPython Stealer Ioc
https://xqwmwru[.]top/upload_large.php# data exfiltrationhttps://xqwmwru[.]top/upload_status.php# data exfiltrationhttps://xqwmwru[.]top/admin/login.php# login panel
Archive dropping RMM tool
055c3fff8f1f58a41e7571b9bd7ebf4b1b10ba5231f1ffbcb47e0307d7ff6072
06ecf34ecf1f3f56a1760b8757b978d6bd859adcf699af4adfbeb0982e41282a
18cb036bcc7aacf7393575ddf15133e24d3a22cc92a4b14e8595686e4bf80629
249d2d1d6cfcf34d48ac0465ede688759a3c90b7412723373ea5a434d6d64c9c
2a4eab726a878a74dcad41d090681a7fa78d9247b1812e5c3066d7a1aa0413b1
316cbc90ad71a421e571b529af2dee40f901b15b4bc549836c25f1be35597249
36e0368dd4c3c9c70a78050618797705cda87a017e41777968c6b4b9173f553f
3f8e2ef8a5e7b8f8d14e43032ad2b18f0a4fb168609494fd346dcdfe1127a5cd
616be8ba3383909b2b04c87bcb9ca0707f5a19a8eaa6fc1e552181baa4e3e0aa
75bf89f0369b6eef1e2931e6da67a9d4f3095b9a623e6e8fdddf7fee66cc7cc0
80f7f10bcddafaec497a2de78dd3d2a53b72f27bb72e7939443539115f7e2168
8c54e6d91d95885beae125b30ab9096bd341e12be08dec3aeb859e539dc77d47
98be97a6f4663d04cf5382f4ed046b479af1dd300d0ab3fa7a399ab15078d7a0
a6fd51bf2da2c2544ff78ef1824c30d4feef9a77c824f36d9afd2c6093c9b6ae
a8d193e49e6c9c6d7c32ea807d22311bd1b110f2326b8a96c67978ecc6862ee6
a8edb8fb1cf83031a454b5f39ffab0b1d93448cb3b9794246507e35ba0036801
ae243178e201c6ee475e4498cade0d21ef22b8a6923322576115b0888e189013
aed5ce23aa11f28e063c8b1b0836d3dbd059d93867e8e828a8356770ee185d1b
d49bd211364594c671c4e34a31afb75becc69b32b45b140ed0d200f4b05868c6
d91ea2ec158e871408229ec2f7a8fe78a8d30ed0db42f73fe9e31875b30b17c2
eb4a53145734d1ef612897337b1fc3375209598c427590731bb87de3bd8f9bb0
fc43d1640d94ef621c82a4d3a0406df3443b39043c4ddef0a23608c186c307e8如有侵权请联系:admin#unsafe.sh