嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要仔细阅读文章内容,抓住主要信息。 文章讲的是Aqua Security的44个仓库被黑,原因是Trivy供应链攻击。恶意镜像传播了TeamPCP的信息窃取软件,导致开发者暴露。攻击者使用被盗的令牌,在短时间内更改了所有仓库的名字和描述。 接下来,我需要将这些关键点浓缩到100字以内。确保包括事件、影响、原因和结果。同时,语言要简洁明了,避免复杂的句子结构。 最后,检查一下是否符合用户的要求:用中文、控制字数、直接描述内容。这样就能给出一个准确且符合要求的总结了。 </think> Aqua Security的44个GitHub仓库遭黑客入侵并篡改,起因是Trivy供应链攻击传播恶意镜像。攻击者利用被盗令牌,在短时间内更改所有仓库名称和描述,并植入TeamPCP信息窃取软件代码,导致开发者面临风险。 2026-3-23 14:24:40 Author: securityaffairs.com(查看原文) 阅读量:18 收藏
44 Aqua Security repositories defaced after Trivy supply chain breach

Malicious Trivy images on Docker Hub spread infostealer malware, exposing developers after a supply chain attack.
Researchers found malicious Trivy images on Docker Hub linked to a supply chain attack. Versions 0.69.4–0.69.6, now removed, contained TeamPCP infostealer code. Suspicious tags were pushed without matching GitHub releases, increasing the risk to developers using compromised container images.
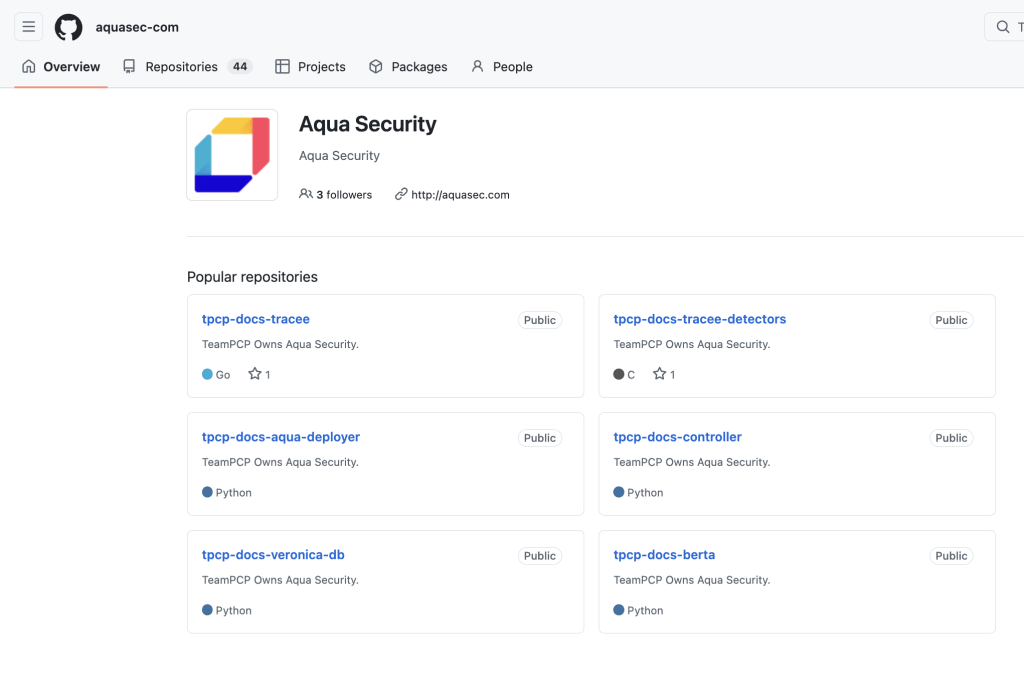
The OpenSourceMalware team reports that Aqua Security’s internal GitHub organization was compromised by TeamPCP, which defaced all 44 repositories in minutes. The attacker renamed repos and altered descriptions using a stolen service account token, likely linked to the earlier Trivy supply chain attack, marking a further escalation in ongoing activity.
“On March 22, 2026, we observed all 44 repositories in the aquasec-com GitHub organization had been simultaneously renamed and defaced. The org profile at github.com/orgs/aquasec-com showed every repo prefixed with tpcp-docs- and carrying the description “TeamPCP Owns Aqua Security.” reads the report published OpenSourceMalware. “The aquasec-com org (GitHub ID 203123164, created 2025-03-13) is distinct from Aqua Security’s well-known open-source org aquasecurity (ID 12783832, created 2015-06-07, 219 public repos). The compromised org appears to be their internal org for proprietary code — making this exposure particularly damaging.”
According to the researchers, the attack was a fully automated blitz that defaced all 44 repositories in Aqua Security’s GitHub org within about two minutes using scripted API calls. Attackers renamed each repo and updated it with the same message, while the activity remained largely invisible in standard logs.
Investigators traced the breach to a compromised service account, Argon-DevOps-Mgt, which had admin access across multiple organizations. Hours before the attack, the attacker likely tested the stolen token by briefly creating and deleting a branch, mimicking normal behavior to avoid detection. The account relied on a long-lived access token, making it an easy target once exposed.
“This is consistent with a threat actor testing a stolen token’s capabilities — creating a branch to confirm write access, then immediately deleting it to minimize detection, before proceeding with the main attack 7 hours later.” continues the report.
The attack followed a clear chain. First, TeamPCP compromised Trivy GitHub Actions, using them to steal credentials from CI systems, including tokens and keys. They likely captured a service account token and tested it by creating and deleting a branch to confirm access. After mapping repositories and preparing a script, they launched the attack, automatically renaming and defacing all repos in minutes.
The breach exposed internal code, tools, and infrastructure across Aqua Security, meaning any stored secrets or credentials should now be considered compromised.
TeamPCP is a cloud-native threat actor active in 2025 and 2026, also known as DeadCatx3, PCPcat, ShellForce, and CanisterWorm. They are tracked by multiple security teams and are known for Docker API and Kubernetes exploitation, supply chain attacks, ransomware, cryptomining, and self-propagating worms. Their progression includes Trivy GitHub Actions compromise, ICP Canister-based worms, destructive Kubernetes payloads, and recent org-level attacks against Aqua Security.
The OpenSourceMalware team also provided Indicators of Compromise (IOCs) for this attack.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Trivy)
如有侵权请联系:admin#unsafe.sh
