好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住主要信息。 文章主要讲的是CISA命令美国政府机构修补三个iOS漏洞,这些漏洞被用于加密货币盗窃和网络间谍攻击,使用的是DarkSword工具包。DarkSword利用了六个漏洞,其中三个被CISA列为高危。这些漏洞已经被苹果修复,但旧版本的iOS设备仍受影响。攻击者使用这些漏洞进行数据窃取和间谍活动,并且涉及多个威胁组织。 接下来,我需要将这些信息浓缩到100字以内。要确保包含关键点:CISA的命令、漏洞数量、用途、DarkSword工具包、影响范围以及修复情况。 可能会这样组织句子:CISA要求美国政府机构修补三个iOS漏洞,这些漏洞被用于加密货币盗窃和网络间谍攻击。DarkSword工具包利用了六个漏洞中的三个,影响运行iOS 18.4至18.7的设备。苹果已修复这些漏洞,但旧版本仍受影响。 最后检查字数是否在限制内,并确保语句通顺。 </think> CISA要求美国政府机构修补三个iOS漏洞,这些漏洞被用于加密货币盗窃和网络间谍攻击。DarkSword工具包利用了六个漏洞中的三个,影响运行iOS 18.4至18.7的设备。苹果已修复这些漏洞,但旧版本仍受影响。 2026-3-23 08:45:15 Author: www.bleepingcomputer.com(查看原文) 阅读量:42 收藏

CISA ordered U.S. government agencies to patch three iOS vulnerabilities targeted in cryptocurrency theft and cyberespionage attacks using the DarkSword exploit kit.
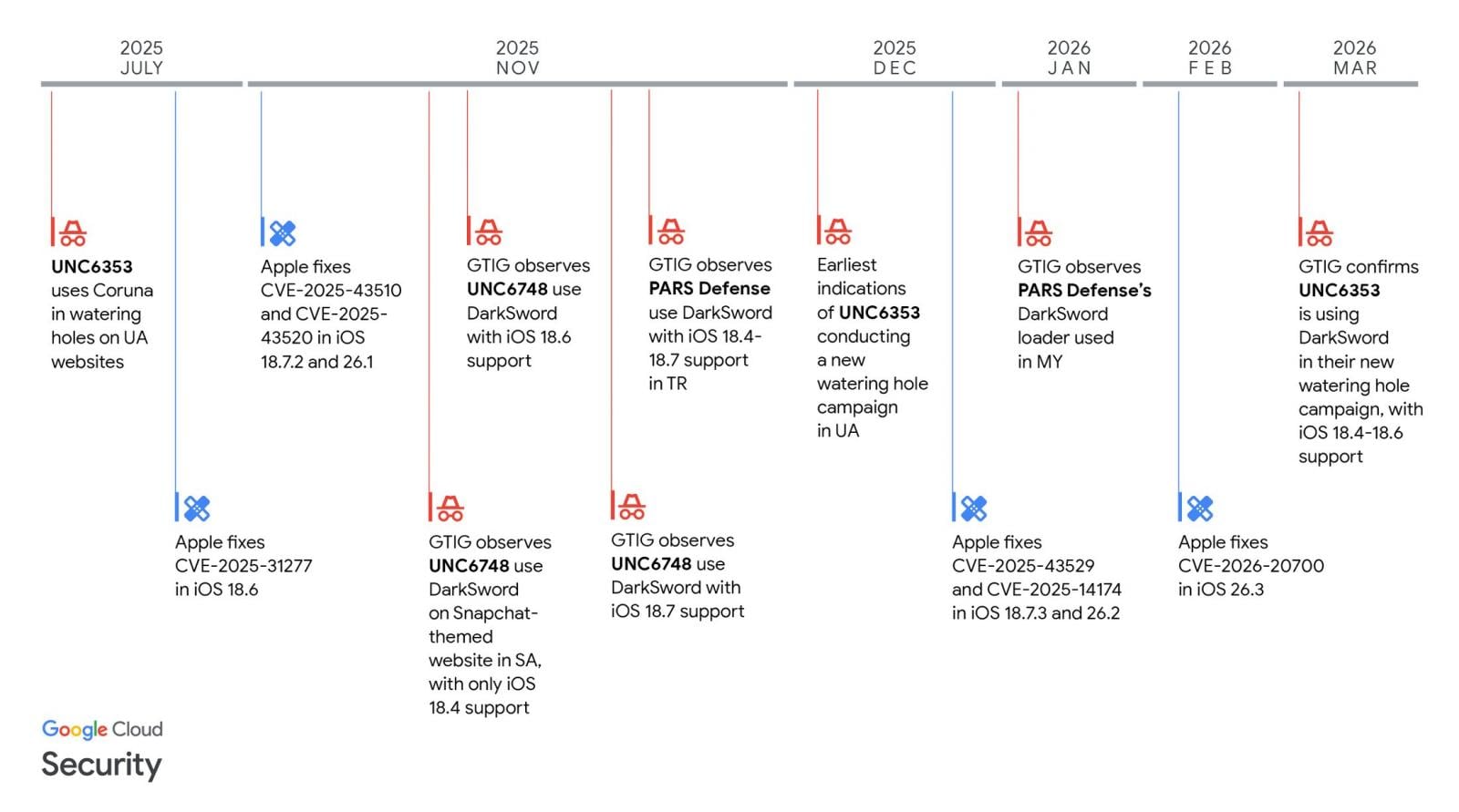
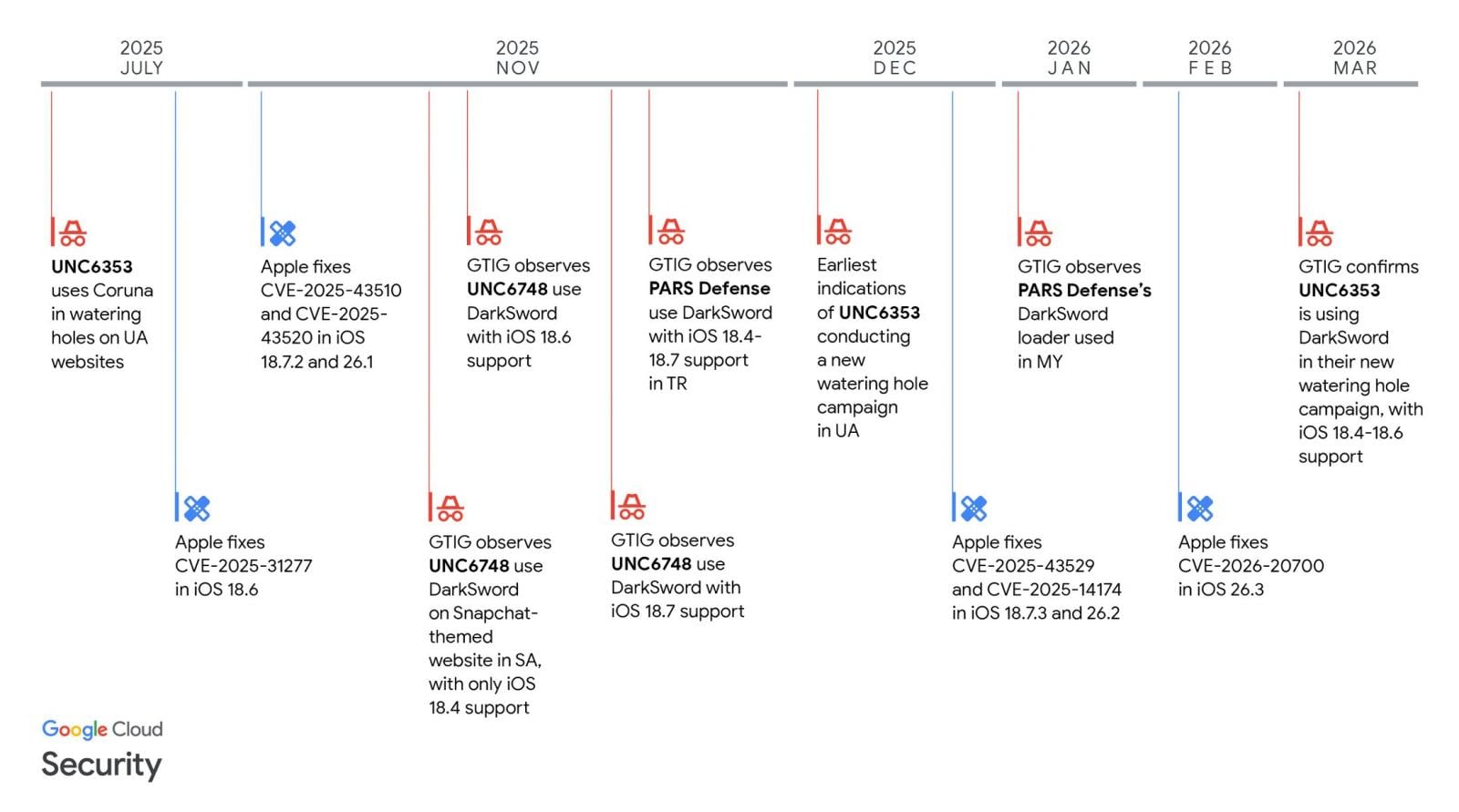
As Google Threat Intelligence Group (GTIG) and iVerify researchers revealed last week, the DarkSword delivery framework abuses a chain of six vulnerabilities tracked as CVE-2025-31277, CVE-2025-43529, CVE-2026-20700, CVE-2025-14174, CVE-2025-43510, and CVE-2025-43520.
These flaws enable attackers to escape sandboxes, escalate privileges, and gain remote code execution on unpatched iPhones, but have all been patched by Apple in the latest iOS releases and now only affect iPhones running iOS 18.4 through 18.7.
DarkSword was also linked by security researchers to multiple threat groups, including UNC6748, a customer of Turkish commercial surveillance vendor PARS Defense, and a suspected Russian espionage group tracked as UNC6353.
In these attacks, GTIG observed three separate information-theft malware families dropped on victims' devices: a very aggressive JavaScript infostealer named GhostBlade, the GhostKnife backdoor that can exfiltrate large swaths of data, and the GhostSaber JavaScript that executes code and also steals victims' data.
Of the three, UNC6353 deployed both the DarkSword and Coruna iOS exploit kits in watering-hole attacks targeting iPhone users visiting compromised Ukrainian websites of e-commerce, industrial equipment, and local services organizations.
Notably, DarkSword wipes temporary files and exits after stealing data from infected devices, indicating that it was designed for short-term surveillance operations designed to evade detection.
Mobile security company Lookout, which discovered DarkSword while investigating infrastructure used in the Coruna attacks, believes that DarkSword is used in cyber-espionage campaigns aligned with Russian intelligence requirements and by a Russian threat actor with financial objectives.
On Friday, CISA added three of the 6 DarkSword vulnerabilities (CVE-2025-31277, CVE-2025-43510, and CVE-2025-43520) to its catalog of actively exploited security flaws, ordering Federal Civilian Executive Branch (FCEB) agencies to secure their devices within two weeks by April 3, as mandated by Binding Operational Directive (BOD) 22-01.
"Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable," CISA warned.
"These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise."
Although BOD 22-01 applies only to federal agencies, CISA urged all defenders, including those working for private sector companies, to prioritize securing their organizations' devices against these flaws as soon as possible.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
