Modern organizations use cloud platforms and remote work which helps improve productivity but it also increases cybersecurity risks and a single security solution is no longer enough to protect sensitive systems and data.
To reduce risk businesses now use a layered security stack that protects identities networks and devices and this approach creates many security layers so if one control fails other layers continue to protect the system.
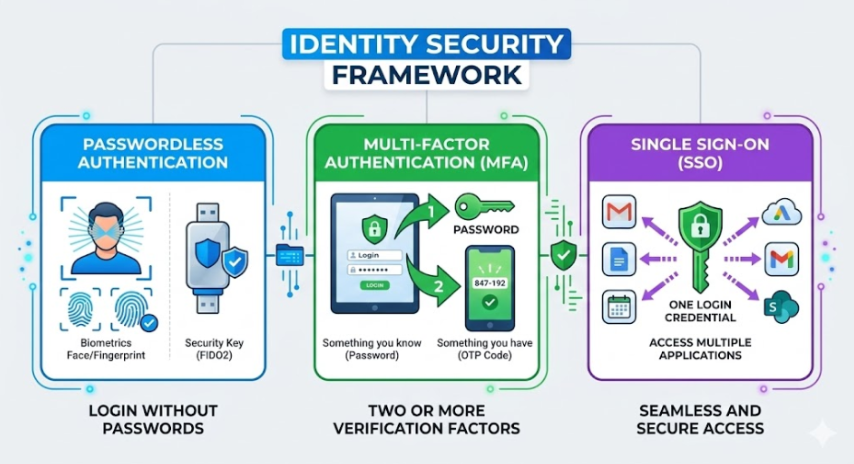
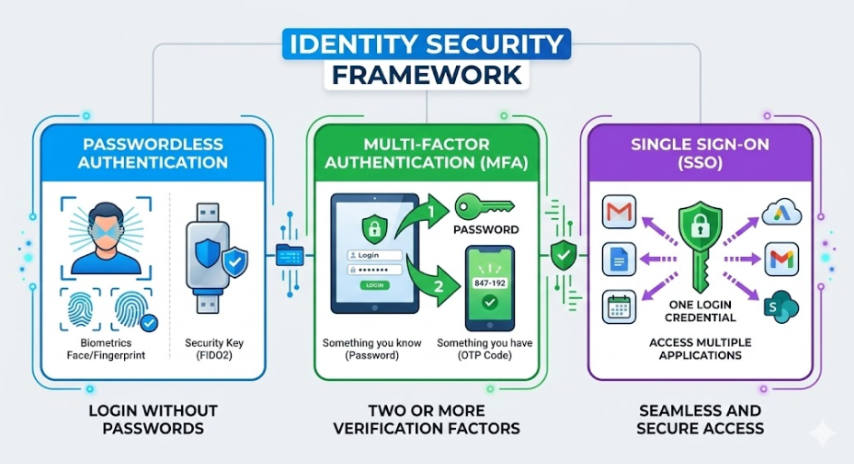
Identity security is the first line of defense in modern cybersecurity and many cyberattacks start with stolen or compromised login details and stronger authentication helps make sure that only authorized users can access company resources.
Passwordless Authentication
Traditional passwords are often weak and easy targets for phishing attacks and passwordless authentication replaces passwords with stronger ways of verification.
Common passwordless authentication methods include:
- Biometric authentication
- Hardware security keys
- Authentication apps
- One time login codes
By removing passwords organizations reduce the risk of credential theft and also make the login process easier for users.
MFA
Multi Factor Authentication ( MFA ) adds an extra verification step during login and even if attackers get a password they cannot access the system without the second authentication step.
Common MFA verification methods include:
- Password or PIN
- One time codes sent to mobile devices
- Authentication apps
- Biometric verification
Using MFA greatly reduces the chance of unauthorized access.
SSO
Single Sign On ( SSO ) allows users to log in once and access many applications without entering login details again and this makes authentication easier and reduces password fatigue.
Key benefits of SSO include:
- Simplified login experience
- Centralized authentication management
- Improved employee productivity
- Stronger access control policies
When SSO is used with MFA it gives both convenience and stronger identity security.
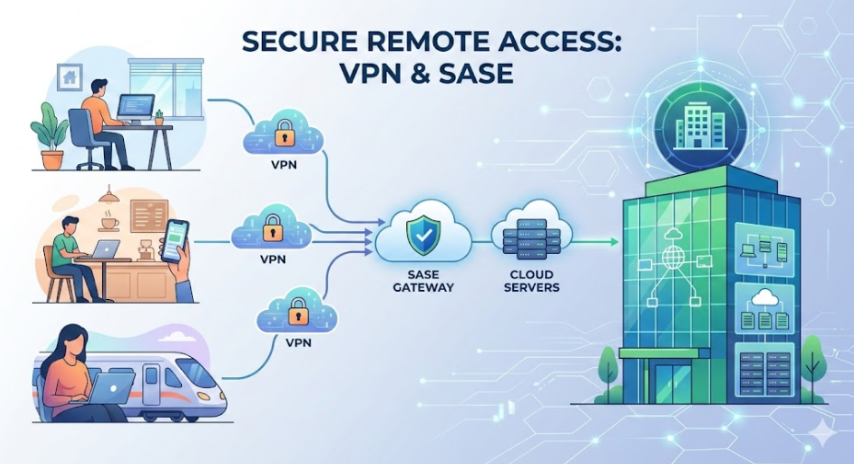
Network security protects the data that moves between users devices and applications and as organizations depend more on remote work and cloud systems securing network access becomes very important.
Network layer protection usually includes VPN platforms and secure web gateways and SASE solutions and teams that research options often look at providers and review platforms such as Cisco AnyConnect Palo Alto GlobalProtect Zscaler as part of their evaluation process.
VPN Platforms
Tested Virtual Private Networks ( VPNs ) create encrypted tunnels between users and company networks and this encryption keeps sensitive data safe from being intercepted when employees access systems remotely.
Key advantages of VPN platforms include:
- Encrypted communication channels
- Secure remote access for employees
- Protection when using public Wi Fi
- Increased data privacy
VPNs remain an essential tool for remote workforce security.
Secure Web Gateways
Secure Web Gateways ( SWGs ) monitor and filter internet traffic to protect users from malicious websites and unsafe downloads.
Common capabilities include:
- URL filtering and website blocking
- Malware detection and prevention
- Phishing protection
- Web traffic monitoring
These tools help organizations enforce safe browsing policies and reduce exposure to online threats.
SASE
Secure Access Service Edge ( SASE ) combines networking and security services into one cloud based platform and this setup helps organizations manage security better in distributed environments.
SASE platforms typically integrate:
- Secure web gateways
- Firewall as a service
- Cloud access security brokers
- Zero Trust access controls
This allows companies to apply consistent security policies regardless of user location.
ZTNA
Zero Trust Network Access ZTNA follows the rule never trust always verify and instead of giving full network access users are checked every time they try to access an application.
ZTNA systems evaluate factors such as:
- User identity
- Device security status
- Location of the request
- Access permissions
This approach limits access to only the resources users need and reducing the risk of internal attacks.
Devices like laptops and smartphones and tablets often act as entry points to company systems and protecting these endpoints is an important part of a layered security strategy.
Endpoint Detection and Response ( EDR )
Endpoint Detection and Response tools watch device activity to find suspicious behavior or possible threats.
Key EDR features include:
- Continuous threat monitoring
- Malware detection
- Automated incident response
- Security alerts for IT teams
These tools help security teams detect and stop threats before they spread.
Mobile Device Management ( MDM )
Mobile Device Management solutions let organizations manage and keep mobile devices used for work secure.
Capabilities include:
- Device encryption enforcement
- Remote wipe for lost or stolen devices
- App installation controls
- Security configuration management
This ensures that company data remains protected on employee devices.
Patch and Update Management
Old software often has weaknesses that attackers can use and patch management systems make sure devices get updates and security fixes on time.
Patch management typically includes:
- Automatic operating system updates
- Application security patches
- Vulnerability monitoring
- Scheduled update deployment
Keeping software updated helps reduce security risks across the organization.
Building a layered security system is important for protecting modern digital environments and by combining identity security and network protection and device safeguards organizations can reduce cybersecurity risks significantly.
Technologies like passwordless authentication ,MFA, VPNs, SASE and endpoint protection work together to protect users and sensitive data and make security stronger across systems devices and networks
*** This is a Security Bloggers Network syndicated blog from MojoAuth Blog - Passwordless Authentication & Identity Solutions authored by MojoAuth Blog - Passwordless Authentication & Identity Solutions. Read the original post at: https://mojoauth.com/blog/layered-security-stack-strategy