好的,我现在需要帮用户总结一篇文章,控制在100字以内。用户已经提供了文章内容,我先快速浏览一下。 文章主要讲俄罗斯相关的行为者通过钓鱼攻击针对WhatsApp和Signal的用户,特别是政府官员和记者。他们利用钓鱼邮件获取账户访问权限,读取信息、联系人,甚至进一步攻击。 接下来,我需要提取关键信息:俄罗斯关联的威胁行为者、目标是高价值账户、使用钓鱼手段、影响Signal和WhatsApp用户,导致账户被接管。 然后,按照用户的要求,用中文简洁地总结,不使用“文章内容总结”之类的开头。确保在100字以内。 最后,检查一下是否涵盖了所有重要点,并且语言流畅自然。 </think> 俄罗斯相关威胁行为者通过钓鱼攻击针对WhatsApp和Signal的高价值账户,包括政府官员、军事人员、政治人物和记者。攻击者利用钓鱼手段获取账户访问权限,读取消息、联系人并进一步发起攻击。 2026-3-22 19:21:15 Author: securityaffairs.com(查看原文) 阅读量:19 收藏
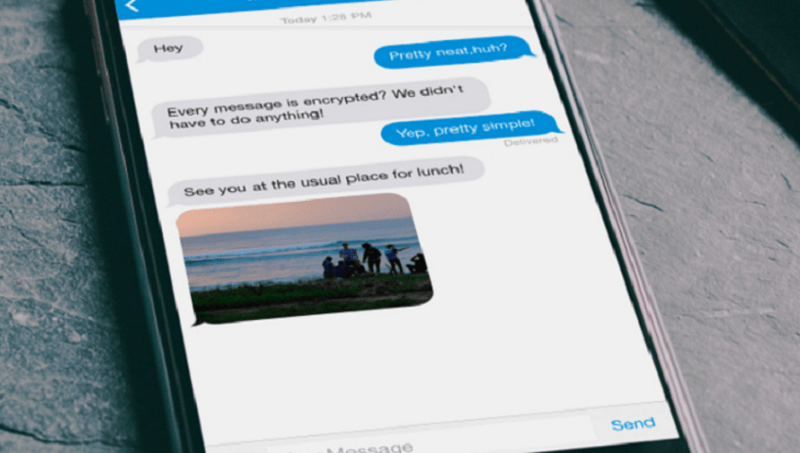
Russia-linked actors target WhatsApp and Signal in phishing campaign

Russia-linked actors target WhatsApp and Signal accounts of officials and journalists via phishing, gaining access to messages and contacts.
Threat actors linked to Russian Intelligence Services are running phishing campaigns to hijack high-value accounts on messaging apps like WhatsApp and Signal, the FBI warns.
“The FBI has identified cyber actors associated with Russian Intelligence Services targeting users of commercial messaging applications, including Signal.” FBI Director Kash Patel wrote on X. “The campaign targets individuals of high intelligence value, including current and former U.S. government officials, military personnel, political figures, and journalists.”
— FBI Director Kash Patel (@FBIDirectorKash) March 20, 2026The @FBI has identified cyber actors associated with Russian Intelligence Services targeting users of commercial messaging applications, including Signal.
The campaign targets individuals of high intelligence value, including current and former U.S. government officials,…
Targets include government officials, military personnel, politicians, and journalists. The attackers do not break app encryption but instead use phishing to gain account access. The attacks have already compromised thousands of accounts worldwide. Once inside, attackers can read messages, access contacts, impersonate victims, and launch further phishing using trusted identities.
Attackers especially target Signal but use similar tactics across other platforms. Users who strengthen their security and stay alert to social engineering attempts can reduce the risk and limit the impact of these attacks.
Russia-linked actors pose as messaging app support accounts and send phishing messages tailored to trick targets. They push users to click links or share verification codes or PINs. When victims comply, attackers gain access by linking their own device or taking over the account entirely. As the campaign evolves, they may also deploy malware to further compromise victims.
“If the user performs any of the requested actions, they unwittingly provide the actors with unauthorized access to their account either by adding the attacker’s device as a linked device or through a full account takeover.” reads a joint Public Service Announcement (PSA) published by CISA and the Federal Bureau of Investigation. “As the campaign evolves, actors may use additional techniques, such as malware to infect the victim.”
Phishing remains a simple but highly effective way to compromise accounts, bypassing protections like end-to-end encryption by targeting users directly. Attackers trick victims into sharing codes or clicking malicious links, gaining full account access.
Users should stay alert: pause if something feels off, never share PINs or 2FA codes, and treat unexpected messages with suspicion, even from known contacts. Always check links before clicking, verify group members, and use built-in security features.
Report suspicious activity quickly to security teams or authorities. Remember, legitimate app support will never ask for codes or send links to “verify” accounts, always use official channels.
Recently, Dutch intelligence agencies (MIVD and AIVD) also warned of a global campaign by Russia-linked threat actors aiming to compromise Signal and WhatsApp accounts. The operation targets government officials, civil servants, and military personnel, highlighting growing cyber risks to sensitive communications among national security actors.
Russian cyber spies are tricking users into revealing verification codes to hijack Signal and WhatsApp accounts. They impersonate Signal Support or exploit the “linked devices” feature, gaining access to messages and chat groups, potentially exposing sensitive information from government and military targets.
Dutch intelligence warned that Russia targets Signal for its strong end-to-end encryption, aiming to access sensitive government communications. Officials stressed that apps like Signal and WhatsApp should not be used for classified or confidential information.
The government experts pointed out that attackers don’t exploit app vulnerabilities but abuse legitimate features of Signal and WhatsApp. Only individual accounts are targeted, not the platforms themselves, officials say.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, WhatsApp, Signal)
如有侵权请联系:admin#unsafe.sh

