
嗯,用户让我用中文总结一下这篇文章,控制在一百个字以内,而且不需要以“文章内容总结”或者“这篇文章”这样的开头,直接写描述。首先,我需要通读整篇文章,抓住主要信息。 文章主要讲的是朝鲜的 Lazarus Group 如何通过网络攻击加密货币平台,比如最近的 Bitrefill 事件。他们利用员工的失误和旧的凭证进入系统,然后窃取资金和客户数据。这显示了朝鲜如何将网络犯罪作为经济战的一部分。 接下来,我需要提炼这些信息到一百字以内。要包括攻击者、攻击手段、目标以及影响。可能还要提到防御措施的重要性。 然后,组织语言,确保简洁明了。比如:“朝鲜 Lazarus Group 利用员工错误和旧凭证攻击加密货币平台 Bitrefill,窃取资金和数据。此事件凸显网络犯罪在经济战中的作用。” 这样应该符合用户的要求了。 </think> 朝鲜 Lazarus Group 利用员工错误和旧凭证攻击加密货币平台 Bitrefill,窃取资金和数据。此事件凸显网络犯罪在经济战中的作用。 2026-3-20 12:33:0 Author: cyble.com(查看原文) 阅读量:21 收藏
North Korea’s Crypto Theft Operations: The Role of Lazarus Group in State-Sponsored Financial Warfare
Lazarus Group cyberattack on Bitrefill highlights how North Korean hackers exploit crypto platforms via credentials and human error for theft.
The latest Bitrefill cyberattack offers a revealing look into how state-sponsored cybercrime has evolved into a strategic financial weapon. The latest development revolves around the threat actor Lazarus Group, a hacking collective widely attributed to the DPRK (North Korea), whose operations have blurred the line between cyber espionage and economic warfare.
What makes this breach notable is not just the theft itself, but how methodically it reflects the broader pattern of Lazarus Group crypto attacks and the growing threat of North Korean hackers’ cryptocurrency operations. Bitrefill, a Sweden-based cryptocurrency gift card platform, disclosed that attackers had infiltrated its systems on March 1, 2026.
The breach led to drained crypto wallets and unauthorized access to approximately 18,500 customer purchase records.
A Breach That Started with a Laptop
The initial compromise did not rely on zero-day exploits or exotic vulnerabilities. Instead, it followed a pattern that has become almost characteristic of North Korean hackers’ cryptocurrency campaigns: exploiting human error.
According to Bitrefill’s internal investigation, attackers gained access through a compromised employee’s laptop. From there, they extracted a legacy credential, an overlooked but still valid key; that opened the door to a snapshot containing production secrets. This foothold allowed them to escalate privileges and move laterally across the company’s infrastructure.
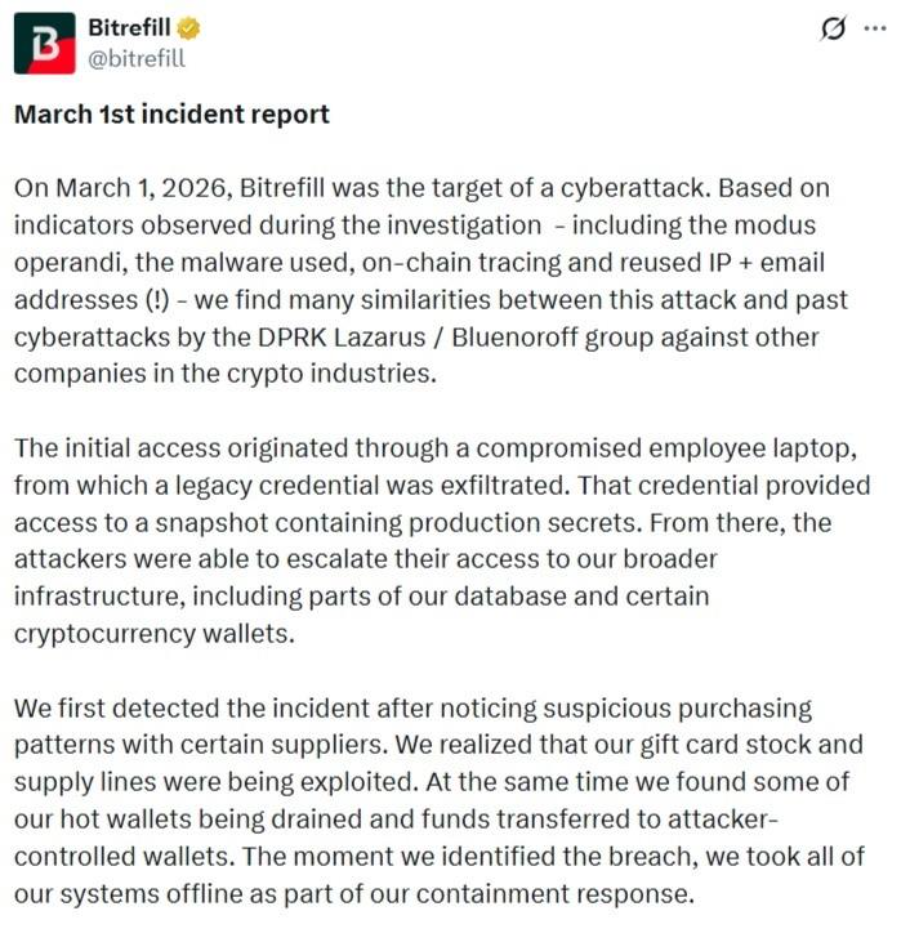
This method highlights a recurring truth in cybersecurity: attackers often prefer the simplest path. In the case of the Lazarus Group, social engineering and credential abuse consistently outperform more complex technical exploits.
Inside the Bitrefill Cyberattack
Once inside, the attackers started understanding the operational model. Rather than immediately exfiltrating large datasets, they probed the environment carefully. Logs indicate they executed a limited number of database queries, likely to identify high-value assets such as cryptocurrency wallets and gift card inventory.
The breach was ultimately detected through anomalies in purchasing behavior. Suspicious transactions involving suppliers revealed that the attackers were exploiting Bitrefill’s gift card supply chain while simultaneously draining funds from its hot wallets, cryptocurrency wallets connected to the internet for active transactions.
Bitrefill responded by taking its entire system offline, a move that, while disruptive, likely prevented further losses. Given the company’s global footprint, spanning multiple suppliers, products, and payment systems, this shutdown was far from trivial.
Data Exposure: Limited but Significant
Although the attackers did not extract the full database, they accessed around 18,500 purchase records. These included email addresses, crypto payment addresses, and metadata such as IP addresses.
For roughly 1,000 transactions, encrypted customer names were also at risk. Bitrefill acknowledged that if encryption keys were compromised, this data could potentially be exposed. The affected users were notified directly.
Importantly, Bitrefill emphasized that customer data was not the primary target. The attackers’ behavior suggests a focus on financial gain rather than large-scale data harvesting, a hallmark of Lazarus Group crypto attacks.
Attribution to Lazarus Group and DPRK
Bitrefill attributed the attack to actors linked to the Lazarus Group, citing multiple indicators: malware similarities, reused IP addresses, email patterns, and blockchain tracing. These elements closely match previous campaigns associated with both Lazarus and its financially motivated subgroup, Bluenoroff.
This attribution aligns with broader intelligence assessments. The DPRK has relied on cyber operations to generate revenue, particularly in response to international sanctions. Cryptocurrency platforms have become prime targets due to their liquidity and relative anonymity.
In 2025 alone, blockchain analysis firms estimated that North Korea-linked actors stole approximately $2.02 billion in cryptocurrency, accounting for a big portion of global crypto theft. This includes high-profile incidents such as the $1.5 billion Bybit exchange hack, also attributed to the Lazarus Group.
Cyble’s Tracking of Lazarus Group and DPRK Cyber Operations
Cyble has long tracked the Lazarus Group, identifying it as one of the most persistent state-sponsored threat actors operating under the umbrella of the DPRK (North Korea). Their assessment frames the group not as a single unit, but as a distributed ecosystem of sub-clusters that carry out financially motivated and espionage-driven operations.
The group has accumulated a wide range of aliases over the years, including APT-C-26, Hidden Cobra, TraderTraitor, and Diamond Sleet. The geographic breadth of North Korean hackers’ cryptocurrency operations spanned countries such as the United States, Japan, India, Germany, South Korea, and Australia, alongside sectors like banking, aerospace, healthcare, energy, and telecommunications. However, in recent years, the financial and crypto sectors have become disproportionately affected due to their high liquidity and cross-border transaction flows.
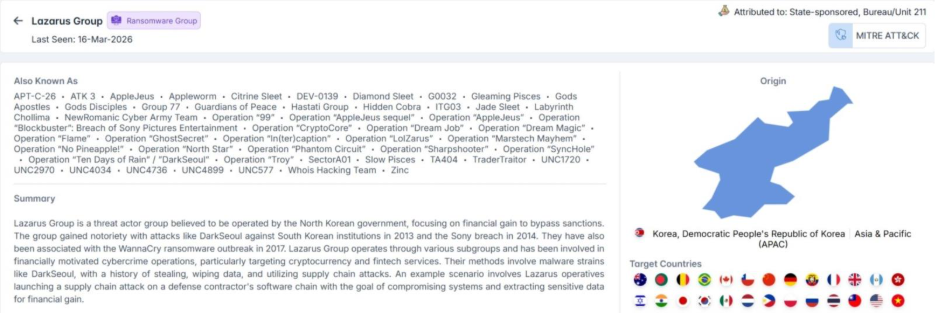
From a tactical standpoint, Cyble’s mapping of Lazarus Group crypto attacks shows a consistent reliance on multi-stage intrusion chains. These often begin with spearphishing campaigns, move into malware deployment, and end with long-term persistence inside compromised networks.
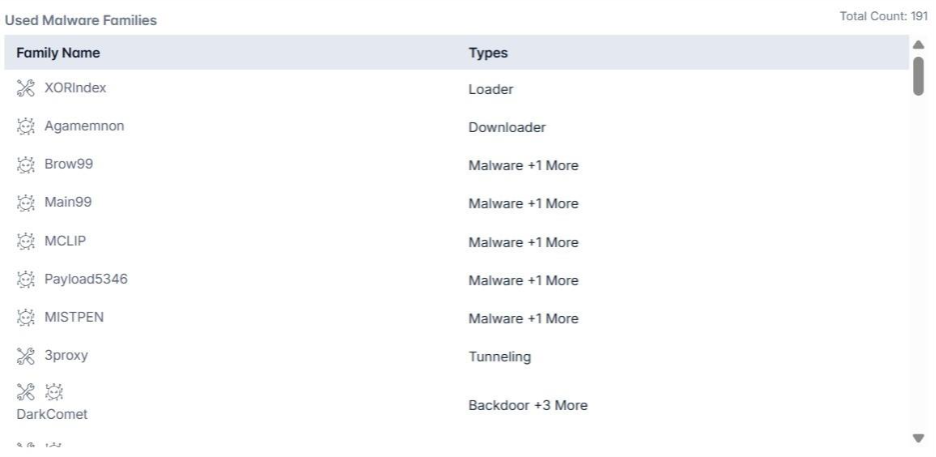
Tools such as credential stealers (for example, Mimikatz), remote access trojans, and custom loaders frequently appear across campaigns.
One of the key observations is that Lazarus operations are rarely purely opportunistic. Instead, they are structured, iterative, and adaptive. The group refines its intrusion methods based on defensive responses observed in earlier campaigns, often reusing infrastructure components such as IP ranges, email patterns, and malware variants with slight modifications to avoid detection.
Why Cryptocurrency Platforms Are Prime Targets
The Bitrefill cyberattack reinforces a larger trend: cryptocurrency ecosystems are uniquely vulnerable to state-sponsored exploitation.
Unlike traditional financial systems, crypto platforms often prioritize speed and accessibility, sometimes at the expense of layered security controls. Hot wallets, in particular, present an attractive target because they maintain immediate liquidity.
Additionally, services like Bitrefill introduce hybrid use cases, bridging crypto with real-world spending through gift cards and digital purchases. This creates new attack surfaces, especially within supply chains that were not originally designed with adversarial threat models in mind.
The Playbook of Lazarus Group
The tactics observed in this breach are consistent with the broader operational playbook of the Lazarus Group:
- Spearphishing and social engineering: Often using fake job offers or professional outreach on platforms like LinkedIn
- Credential theft and reuse: Leveraging weak or outdated authentication practices
- Living-off-the-land techniques: Using legitimate system tools to avoid detection
- Custom malware deployment: Including backdoors, loaders, and credential stealers
- Persistence mechanisms: Such as scheduled tasks and renamed administrative accounts
Their malware arsenal is extensive, ranging from tools like Mimikatz for credential extraction to destructive wipers like Destover. This versatility allows them to pivot between espionage, disruption, and financial theft depending on mission objectives.
Response and Recovery
Bitrefill has stated that it will absorb the financial losses through its operational capital. The company also engaged multiple cybersecurity firms and law enforcement agencies to investigate the breach and strengthen its defenses.
Post-incident measures include:
- Enhanced access controls
- Expanded logging and monitoring capabilities
- Ongoing penetration testing
- Improved incident response procedures
Notably, the platform’s design, minimizing stored personal data and avoiding mandatory KYC, helped limit the potential impact on users.
By March 5, the company had restored its systems, with payments, inventory, and user accounts returning to normal operation.
Conclusion
The Bitrefill cyberattack shows how Lazarus Group, DPRK, and North Korean hackers’ cryptocurrency operations exploit human error, legacy credentials, and limited visibility to access systems and drain assets. The incident highlights that defending against Lazarus Group crypto attacks depends on strict credential hygiene, behavioral monitoring, and rapid anomaly detection rather than perimeter defenses alone.
It also reinforces that limiting data exposure and access scope reduces breach impact. Intelligence-led platforms like Cyble provide real-time threat intelligence and visibility to detect and respond to such intrusions faster. Organizations looking to strengthen resilience against North Korean hackers’ cryptocurrency threats can schedule a demo with Cyble to see how AI-native threat intelligence and real-time detection can help identify and stop attacks before they escalate.
References:
如有侵权请联系:admin#unsafe.sh
