
好的,用户让我帮忙总结一篇文章的内容,控制在100字以内,并且不需要特定的开头。首先,我需要通读整篇文章,抓住主要信息。 文章讲的是一个北卡罗来纳州的男子Cameron Curry,在担任Brightly Software的数据分析师期间,利用职务之便窃取公司敏感信息,然后进行敲诈。他索要250万美元赎金,并威胁泄露员工个人信息和向SEC举报。最终公司支付了7540美元比特币,FBI介入后逮捕了他。 接下来,我需要将这些信息浓缩到100字以内。重点包括:男子身份、公司名称、敲诈手段、金额、后果等。 可能的结构是:Cameron Curry在任职期间窃取信息,威胁泄露并索要赎金,最终被逮捕。 现在检查字数是否符合要求,并确保信息准确无误。 </think> 北卡罗来纳州男子Cameron Curry在担任Brightly Software数据分析师期间,利用职务之便窃取公司敏感信息并进行敲诈,索要250万美元赎金。他威胁泄露员工个人信息并举报公司未披露数据泄露事件。最终公司支付7540美元比特币赎金,FBI逮捕 Curry。 2026-3-20 07:2:27 Author: www.bleepingcomputer.com(查看原文) 阅读量:21 收藏

A North Carolina man was found guilty of extorting a D.C.-based technology company while still being employed as a data analyst contractor.
While a Justice Department press release published on Thursday doesn't name the victim, court documents reveal that he targeted Brightly Software, a Software-as-a-Service (SaaS) company previously known as SchoolDude, which Siemens acquired in August 2022.
Brightly has been in business for more than 20 years, employs over 700 people, and provides intelligent asset management and maintenance software to over 12,000 clients worldwide, mainly in the United States, Canada, the United Kingdom, and Australia.
As revealed in the indictment, 27-year-old Cameron Curry (also known as "Loot") took advantage of his access to Brightly's payroll information and corporate data to steal sensitive documents, which he used as leverage in an extortion scheme after learning that his six-month contract wouldn't be extended.
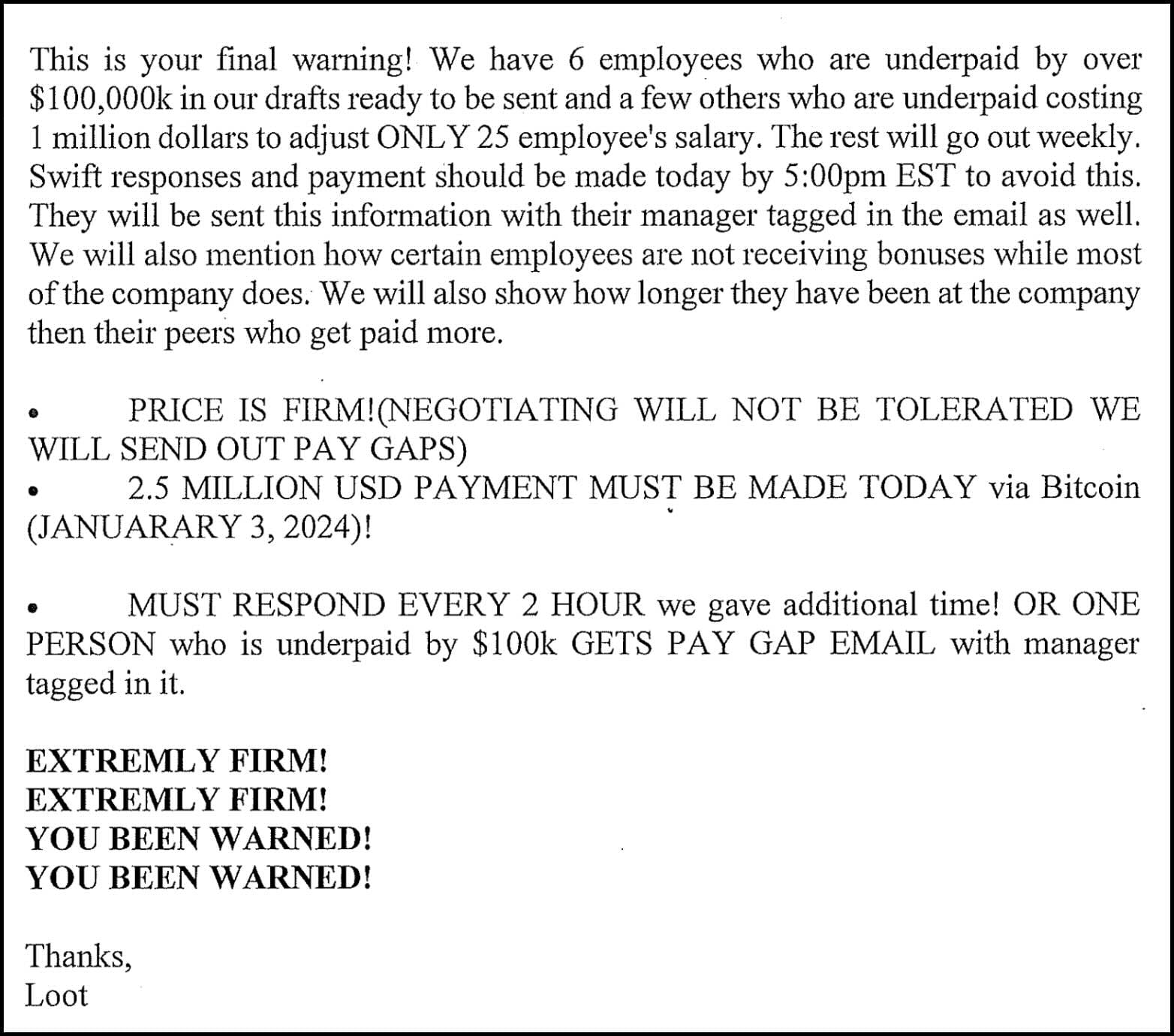
One day after his contract ended on December 10, Curry began sending over 60 extortion emails to Brightly employees using the [email protected] Microsoft email address and the Loot alias, threatening to leak sensitive information stolen between August and December 2023 unless he was paid a $2.5 million ransom.
With the extortion messages, Curry also attached screenshots of spreadsheets listing the personal identification information (PII) of Brightly employees, including names, dates of birth, home addresses, and compensation information. He also threatened to report the company to the U.S. Securities and Exchange Commission (SEC) for failing to disclose the breach as required by law.
"We will commence the process of disseminating salary information starting January 1,2024 in phases to all employees and will report you to the SEC after for not reporting the breach," Curry threatened in one of the extortion emails.
"If you wish to reclaim your data, we recommend doing so promptly at 2.5 million USD in order to save your company and stocks, as each subsequent month will incur a $100,000 USD increase. Discrepancies in your books are currently over 16 million USD, posing a potential risk for retention issues, a hostile work environment, resentment, and more."
Following Curry's numerous extortion emails, Brightly paid $7,540 in Bitcoin, which was transferred to a cryptocurrency wallet controlled by Curry.
The FBI searched Curry's residence on January 24 after the company reported the incident and seized various electronic devices containing evidence of his extortion scheme.
Curry was released on bond in January 2024 and now faces up to 12 years in prison for six counts of transmitting or willfully causing interstate communications with the intent to extort a victim company.
Brightly also notified customers of a data breach unrelated to this case in May 2023 after attackers gained access to the database of its SchoolDude online platform and stole credentials and personal data (including names, email addresses, account passwords, phone numbers).
Information filed with the Office of the Maine Attorney General revealed that the intrusion was discovered 8 days after the attackers breached Brightly's systems on April 20, and that the data breach affected nearly 3 million SchoolDude customers and users.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
