Cybersecurity researchers have flagged a new malware dubbed Speagle that hijacks the functionality and infrastructure of a legitimate program called Cobra DocGuard.
"Speagle is designed to surreptitiously harvest sensitive information from infected computers and transmit it to a Cobra DocGuard server that has been compromised by the attackers, masking the data exfiltration process as legitimate communications between client and server," Symantec and Carbon Black researchers said in a report published today.
Cobra DocGuard is a document security and encryption platform developed by EsafeNet. The abuse of this software in real-world attacks has been publicly recorded twice to date. In January 2023, ESET documented an intrusion where a gambling company in Hong Kong was compromised in September 2022 via a malicious update pushed by the software.
Later that August, Symantec highlighted the activity of a new threat cluster codenamed Carderbee, which was found using a trojanized version of the program to deploy PlugX, a backdoor widely used by Chinese hacking groups like Mustang Panda. The attacks targeted multiple organizations in Hong Kong and other Asian countries.
Speagle remains unattributed to date. But what makes the malware noteworthy is that it's designed to gather and exfiltrate data from only those systems that have the Cobra DocGuard data protection software installed. The activity is being tracked under the moniker Runningcrab.
"This indicates deliberate targeting, possibly to facilitate intelligence collection or industrial espionage," the Broadcom-owned threat hunting teams said. "At present, we believe the most likely hypotheses are that it is either the work of a state-sponsored actor or the work of a private contractor available for hire."
Exactly how the malware is delivered to victims is unknown, although it's suspected that it may have been done via a supply chain attack, as evidenced by the two aforementioned cases.
In addition, the central role played by the security software and its infrastructure deserves a mention. Not only does Speagle use a legitimate Cobra DocGuard server for command-and-control (C2) and as a data exfiltration point, it also invokes a driver associated with the program to delete itself from the compromised host.
The 32-bit .NET executable, once launched, first checks the installation folder of Cobra DocGuard and then proceeds to harvest and transmit data from the infected machine in phases. This includes details about the system and files located in specific folders, such as those that contain web browser history and autofill data.
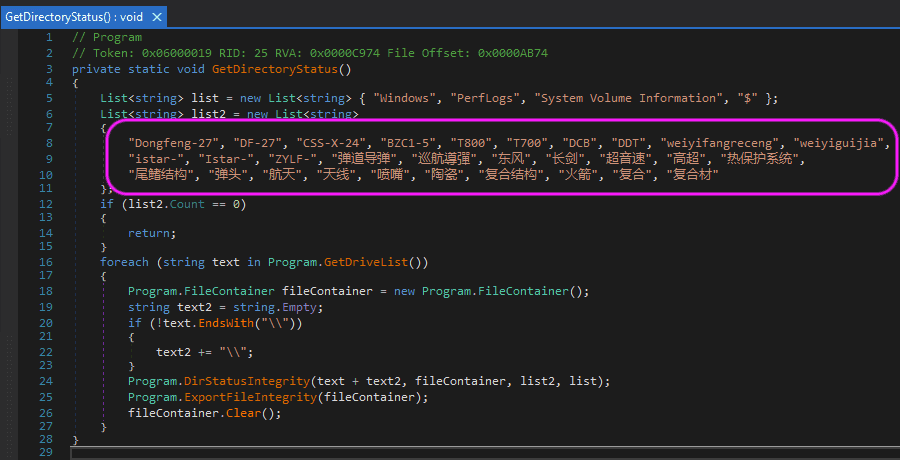
What's more, one variant of Speagle has been found to incorporate additional functionality to turn on/off certain types of data collection, as well as search for files related to Chinese ballistic missiles like Dongfeng-27 (aka DF-27).
"Speagle is a novel, parasitic threat that cleverly makes use of Cobra DocGuard's client to mask its malicious activity and its infrastructure to hide exfiltration traffic," researchers said. "Its developer no doubt took notice of previous supply chain attacks using the software and may have selected it both for its perceived vulnerability and its high rate of use among targeted organizations."
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.